Featured News
-

 102Password
102PasswordNew iPad could be latest to add fingerprint security
New evidence has emerged that the new iPad will have fingerprint security built in, as found on the Apple iPhone 5S.
-

 243Cyber Crime
243Cyber CrimeEdward Snowden’s Leaks Helped Terrorists: Hillary Clinton
Hillary Clinton, former Secretary of State, a Senator and the First Lady, is not yet convinced that Snowden leaked the classified documents...
-

 210News
210NewsOfficial Website of City of Westminster, California hacked by Saudi Hackers
Two Saudi Arabian hackers going with the handle of NeT-DeViL and Dr-TaiGaR from Group Hp-Hack have hacked and defaced the official website...
-

 281Surveillance
281SurveillanceInternet is a CIA project, be careful before making Google searches: Putin
Russian president Vladimir Putin has said that Internet is a CIA project and Russians should be careful while making Google searches. While...
-

 247News
247NewsSyrian hacker hacks and defaces UNICEF New Zealand Official blog for Free Syria
A Syrian hacker going with the handle of Dr.SHA6H has hacked and defaced the official blog of The United Nations Children’s Fund (UNICEF) designated for...
-

 284Cyber Events
284Cyber EventsSnowden Delivers his Maiden Speech as Glasgow University Rector
The whistleblower kept the students glued as he addressed them via a video link from Russia stressing on “speaking out” for human...
-

 296Cyber Crime
296Cyber CrimeThe perfect job? Dream on! Five signs a job offer is a scam
Job scams are a permanent fixture in cyberspace. Anyone who has posted their resume online has offered cyber gangs two crucial pieces...
-

 75Cyber Crime
75Cyber CrimeBad business: ALL major companies are hosting malware – Cisco
Every single one of 30 major companies tested by Cisco over the course of 2013 had malicious traffic on their networks, according...
-

 98Privacy
98PrivacyYoung people fear internet of things will give away their secrets
Young people are seriously worrried about connected gadgets when it comes to privacy - worrying that 'connected' gadgets such as Smart TVs...
-

 211Cyber Events
211Cyber EventsAnonymous Exposes How Rothschild Family Profited from missing Malaysian Airliner MH 370
A couple of weeks ago, a video was uploaded on YouTube by online hacktivist group Anonymous. In the video anonymous gives an depth...
-

 240Data Security
240Data SecurityAndroid Trojan Virus: iBanking Malware ‘Qadars’ Targets Facebook Users via Webinjects
Cyber criminals have targeted millions of Facebook users through a sophisticated Android Trojan app that can bypass the two-factor authentication shield used...
-

 74Cyber Crime
74Cyber CrimeGoogle offers refunds for buyers of fake Virus Shield app
Google is offering full refunds to buyers of the Virus Shield app which briefly topped the Android charts last week - but...
-

 74Cyber Crime
74Cyber CrimeLack of cyber risk insurance could lead to “global financial shock”
The financial damage caused by a large data breach or malicious employee activity can be enormous, but the lack of financial protection...
-

 101Kids Online
101Kids OnlineHow do you know if your child’s ID has been stolen?
When it comes to identity theft, the most successful attack is on the person least likely to be aware of activity being...
-

 128Privacy
128PrivacyCybercrime evolves as criminal gangs join forces with spies – report
Hackers targeting sensitive information or stealing from retailers work at such speed that customers often notice data breaches first - and for...
-
 106Malware
106MalwareFake Facebook app attack can lead to your Android being spied upon, and your bank account being hacked
Hackers are using a notorious banking Trojan horse to display a bogus message from Facebook, in an aggressive attempt to infect Android...
-
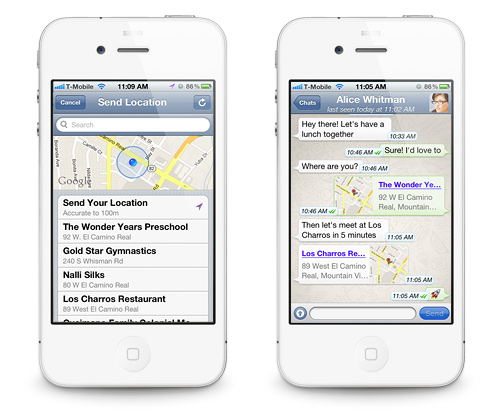
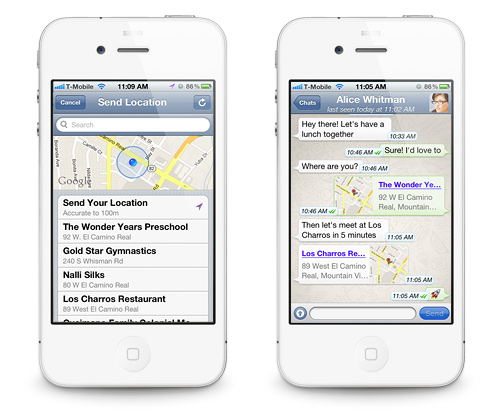 179Data Security
179Data SecurityWhatsApp Flaw leaves User Location Vulnerable to Hackers and Spies.
Researchers warn that the highly popular mobile application WhatsApp cannot be trusted blindly. WhatsApp has been one of the most popular mobile...
-

 150Surveillance
150SurveillanceNo Room for Privacy: Facebook Launches Friend-Spying Feature ‘Nearby Friends’
A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has...
-

 246News
246NewsOfficial website of Bangalore City Police hacked by Pakistani hacker
A Pakistani hacker going with the handle of H4x0r10ux m1nd has hacked and defaced the official website of Bangalore City Police India, yesterday....
-

 229How To
229How ToHow to run Kali on your Android device
This tutorial mainly created for Linux fans. Follow the given steps below to install Kali Linux on your Android phone. Step 1:...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




