Featured News
-

 239Data Security
239Data SecurityAndroid Trojan Virus: iBanking Malware ‘Qadars’ Targets Facebook Users via Webinjects
Cyber criminals have targeted millions of Facebook users through a sophisticated Android Trojan app that can bypass the two-factor authentication shield used...
-

 73Cyber Crime
73Cyber CrimeGoogle offers refunds for buyers of fake Virus Shield app
Google is offering full refunds to buyers of the Virus Shield app which briefly topped the Android charts last week - but...
-

 74Cyber Crime
74Cyber CrimeLack of cyber risk insurance could lead to “global financial shock”
The financial damage caused by a large data breach or malicious employee activity can be enormous, but the lack of financial protection...
-

 100Kids Online
100Kids OnlineHow do you know if your child’s ID has been stolen?
When it comes to identity theft, the most successful attack is on the person least likely to be aware of activity being...
-

 127Privacy
127PrivacyCybercrime evolves as criminal gangs join forces with spies – report
Hackers targeting sensitive information or stealing from retailers work at such speed that customers often notice data breaches first - and for...
-
 105Malware
105MalwareFake Facebook app attack can lead to your Android being spied upon, and your bank account being hacked
Hackers are using a notorious banking Trojan horse to display a bogus message from Facebook, in an aggressive attempt to infect Android...
-
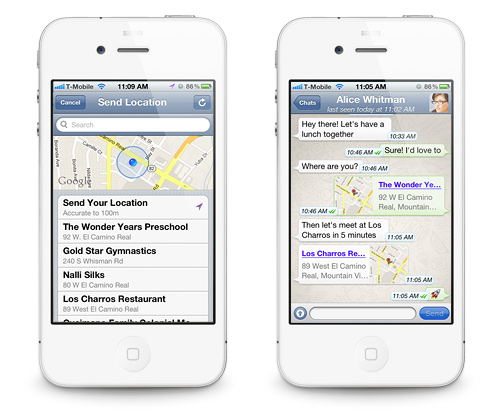
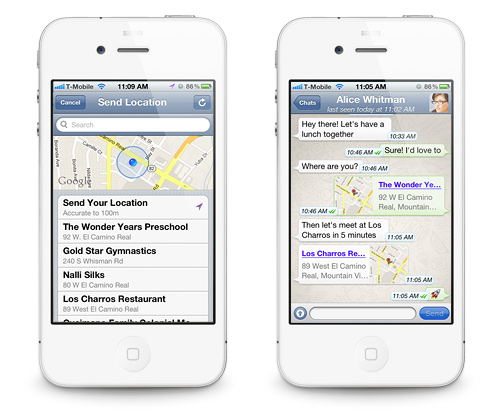 178Data Security
178Data SecurityWhatsApp Flaw leaves User Location Vulnerable to Hackers and Spies.
Researchers warn that the highly popular mobile application WhatsApp cannot be trusted blindly. WhatsApp has been one of the most popular mobile...
-

 149Surveillance
149SurveillanceNo Room for Privacy: Facebook Launches Friend-Spying Feature ‘Nearby Friends’
A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has...
-

 245News
245NewsOfficial website of Bangalore City Police hacked by Pakistani hacker
A Pakistani hacker going with the handle of H4x0r10ux m1nd has hacked and defaced the official website of Bangalore City Police India, yesterday....
-

 227How To
227How ToHow to run Kali on your Android device
This tutorial mainly created for Linux fans. Follow the given steps below to install Kali Linux on your Android phone. Step 1:...
-

 73Cyber Crime
73Cyber CrimeHacking predictions gone wild from the ‘internet of things’
A new, terrifying weapon is in the hands of hackers - the ability to stop a toilet flush working. We look at...
-

 95Password
95PasswordGoogle Chromebook passwords could soon just be the wave of an Android
Google’s popular Chromebook laptops could soon do away with passwords entirely with a new system where simply bringing a phone near the...
-

 193Cyber Crime
193Cyber CrimeCanadian teenager is first to be arrrested for Heartbleed bug attack
A 19-year-old teenager in London, Ontario, Canada has become the first criminal to be arrested for exploiting the ‘Heartbleed’ bug to steal...
-

 85Cyber Crime
85Cyber CrimeLaCie breach leaks passwords and emails – for a whole YEAR
Hard drive specialist LaCie has admitted a data breach that exposed customer emails and passwords - and the attack went undetected for...
-

 327Surveillance
327SurveillanceGoogle admits it’s reading your emails, tells court Gmail users should not expect privacy
Google’s latest update on Monday only highlights how apathetic they are to the privacy of their users and consider every bit of...
-

 84Cyber Crime
84Cyber CrimeSamsung Galaxy S5 is vulnerable to crude “fake fingerprint” hack
A crude fake fingerprint molded using wood glue, and based on a photo taken by a smartphone was enough to fool the...
-

 204Malware
204Malware‘Heartbleed thingumajig’ man suffers heartbleed hackers revenge
Man challenges hackers to break into accounts after complaining Heartbleed was “overhyped” – and has online life destroyed in minutes.
-

 89Malware
89MalwareFacebook Webinject Leads to iBanking Mobile Bot
iBanking is a malicious Android application that when installed on a mobile phone is able to spy on its user’s communications. This...
-

 415Opinion
415OpinionXP‑diency: beyond the end of the line
Can't yet upgrade from XP? Recommendations are being made by Gartner and others for staying (relatively) safe.
-

 174Cyber Crime
174Cyber CrimeHeartbleed claims British mums and Canadian tax payers as victims
The critical security vulnerability in OpenSSL known commonly as “Heartbleed” continues to raise alarms, with websites now warning that hackers have breached...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




