Featured News
-

 477Privacy
477PrivacyPrivacy, Social Media, and the Younger Generation
When parents post photographs and information about their children to social media, what are the privacy implications for those children when they're...
-

 249Android
249AndroidAndroid malware? Google will be watching your every move
Google is to boost security on its Android devices, by continuously checking apps to see that they haven’t mutated into malicious Android...
-

 122Malware
122MalwareWindigo not Windigone: Linux/Ebury updated
There have been some interesting new developments since we published our report on Operation Windigo. In this blog post you will read...
-
 316Data Security
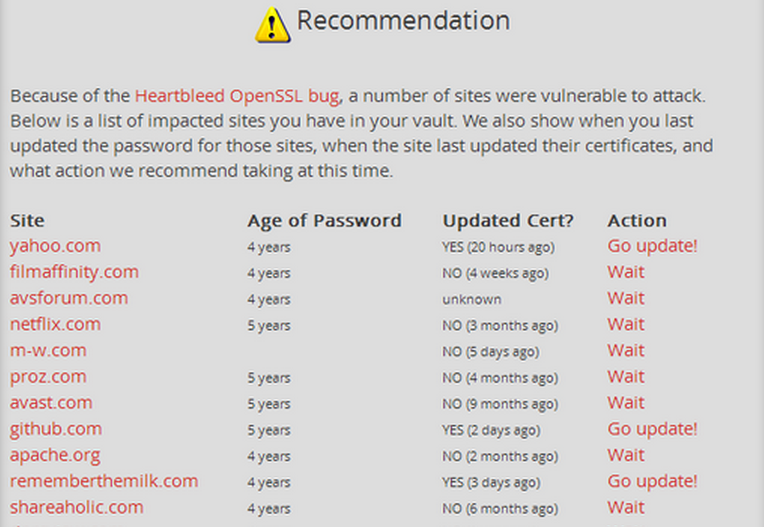
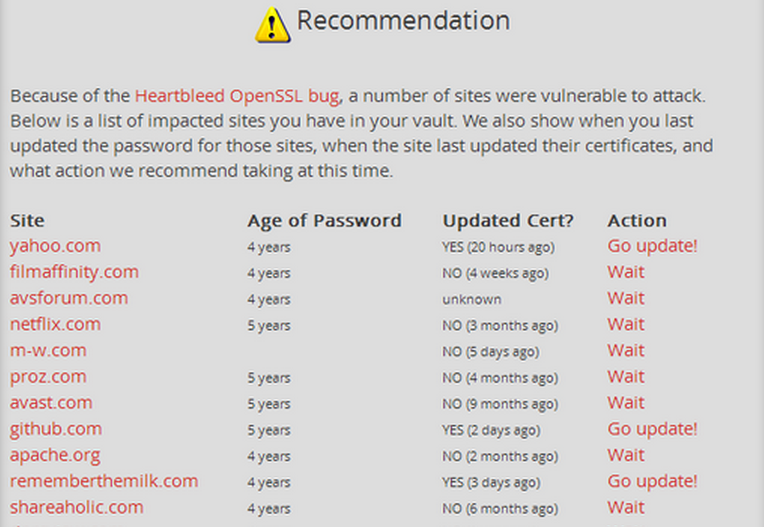
316Data SecurityUse LastPass checker to find sites vulnerable to ‘Heartbleed’ and if you’ve to change your password
The password manager, LastPass, allows you to check if the saved sites are affected by the bug through its ‘LastPass Heratbleed Checker. LastPass’s Security...
-

 197Data Security
197Data SecurityYour email Password, Credit Card at Risk—Web Encryption Compromised by ‘Heart Bleed’ Bug
The new bug allows attackers to gain sensitive information protected by the SSL/TLS encryption. A new exploit in the open SSL, the...
-

 246Privacy
246PrivacyNSA revelations shake faith in U.S. tech firms as Harris poll shows public conflicted
The National Security Agency (NSA) surveillance activities revealed by former CIA contractor Edward Snowden appear to be taking a serious toll on...
-

 244Geek
244GeekFacebook could be developing Anonymous app that will force users to confess their secrets: Report
The Secret app showcases startling confessions about what a person really thinks but isn’t willing to share on sites like Facebook Reports suggest Zuckerberg has had...
-

 183Cyber Crime
183Cyber CrimeHeartbleed encryption flaw leaves millions of sites at risk
The Heartbleed bug – a flaw in an encryption technology used to protect major websites including Yahoo – has left a huge amount...
-

 65Cyber Crime
65Cyber Crime“New weapon” against malware intrusion designed by American student
A new technique for spotting cyber attacks has been designed by a young American student - and could prevent attacks against planes...
-

 224How To
224How ToHow to Record Skype Video and Audio calls for Windows and Mac
Pamela [Win] It is free to download and allows you to record calls you make using Skype. It works on Windows devices...
-
 195How To
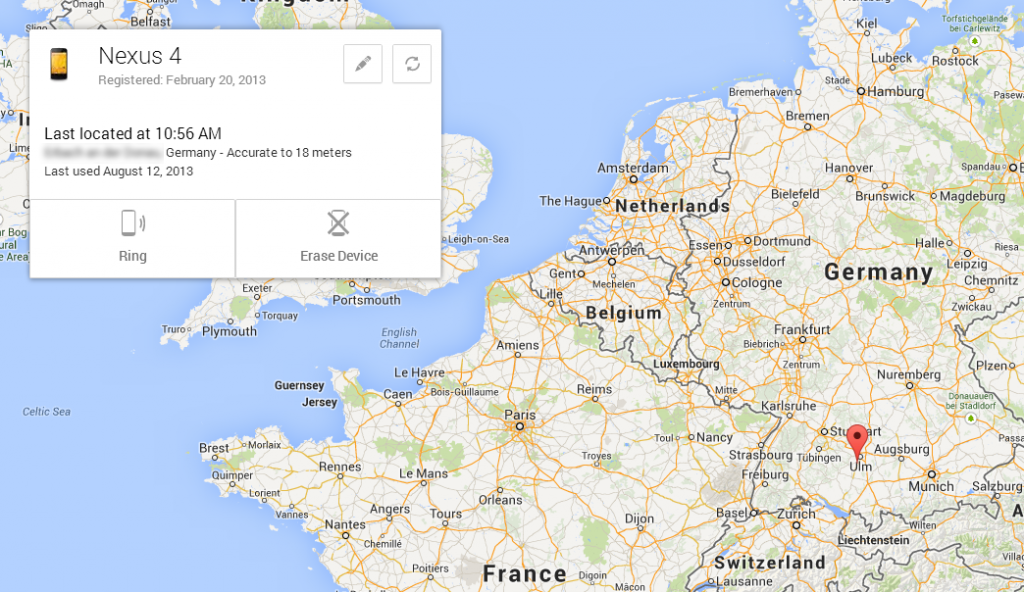
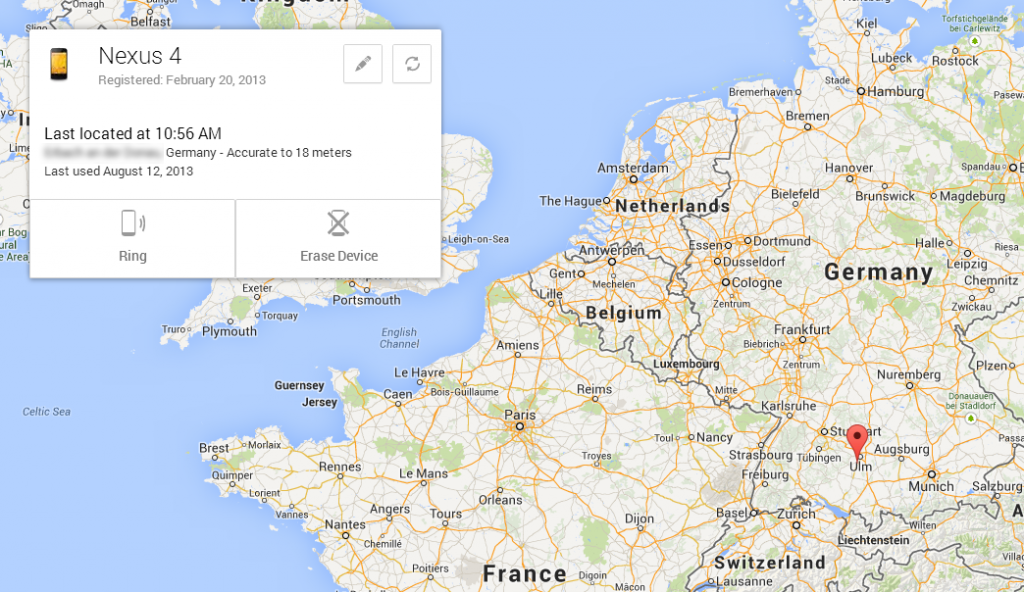
195How ToHow to Locate Your Lost Android Device Easily
Lost you android phone ..? Feeling to sad .. ? Dont worry Now we came with another Application which sorts out...
-

 146Opinion
146OpinionGoodbye, Windows XP!
This patch Tuesday, April 8, 2014, sees the last updates to be released to the public for Windows XP and Office 2003....
-

 105Privacy
105PrivacySamsung smartphones are security favourite – for adulterers
Samsung is the most popular brand of smartphone among a large portion of the adult population - adulterers, with the Korean handsets...
-

 137How To
137How ToPorts That Are Commonly Targeted By Hackers
Common ports, such as TCP port 80 (HTTP), may be locked down — but other ports may get overlooked and be vulnerable...
-

 256News
256News#OpIsrael: Israeli Ministry of Agriculture Domain Hacked, 100+ other crushed down by Anonymous
Year 2014 begin with a warning from online hacktivists Anonymous in which it warned Israel to get ready for a massive cyber...
-

 89Malware
89MalwareIf you love someone, upgrade them from XP
It is us, the nerdy geeks who are into computers, who have a moral right to help the great unwashed, and lead...
-

 260Surveillance
260SurveillanceEdward Snowden and journalist Laura Poitras Win Truth-Telling Award
Both were key players in exposing the US government surveillance program that has outraged the national and international communities alike. Laura Poitras...
-

 328Surveillance
328SurveillanceFinFisher Surveillance Challenged in Pakistani Court
A human right organization has challenged the setting up of the FinFisher surveillance technology in Pakistan, according to media reports. Bytes For...
-

 197News
197NewsIndian hacker Takes Down Official website of terrorist organization Tehreek e Taliban Pakistan
The official website of terrorist organization Tehreek e Taliban Pakistan (TTP) (http://www.umarmedia.com/) has been targeted and successfully taken down by famous Indian hacker Godzilla. Godzilla hacker...
-

 78Cyber Crime
78Cyber CrimeSwooping robot attack which felled triathlete “may be work of hackers”
A competitor in an Australian triathlon was hospitalized with injuries and “pieces of propeller in her head” after a drone plunged from...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




