Featured News
-
 268Geek
268GeekThe Major Cyber Events You Might Have Missed
The most happening events in cyber world that makes every web savvy thrilled and compel to think ahead of cyber crime are...
-

 283Privacy
283Privacy“I am responsible”: Heartbleed developer breaks silence
The source of the bug, which has affected at least 500,000 sites and millions of users, was a small programming error made...
-

 479Privacy
479PrivacyPrivacy, Social Media, and the Younger Generation
When parents post photographs and information about their children to social media, what are the privacy implications for those children when they're...
-

 251Android
251AndroidAndroid malware? Google will be watching your every move
Google is to boost security on its Android devices, by continuously checking apps to see that they haven’t mutated into malicious Android...
-

 125Malware
125MalwareWindigo not Windigone: Linux/Ebury updated
There have been some interesting new developments since we published our report on Operation Windigo. In this blog post you will read...
-
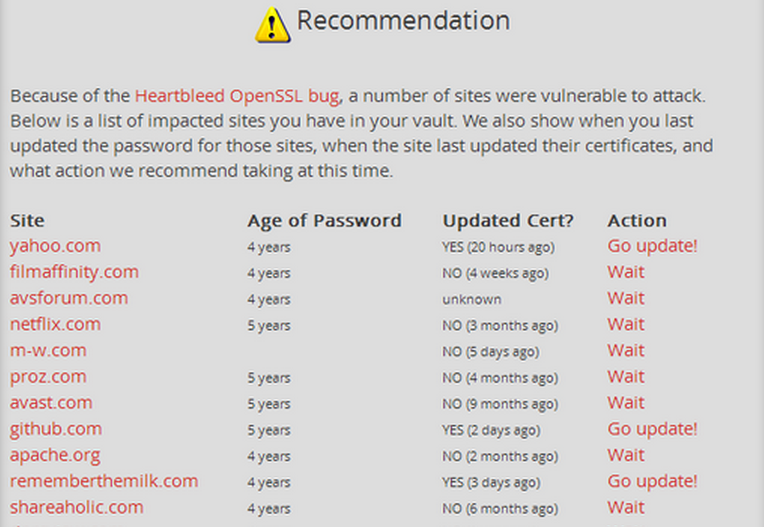
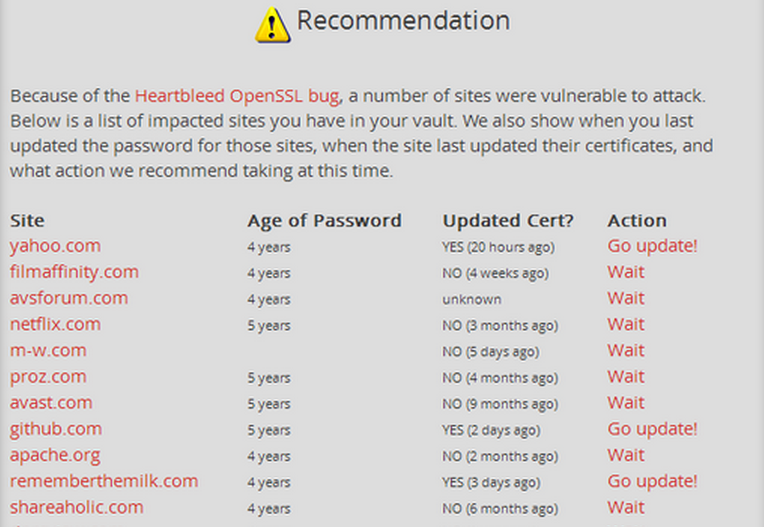 321Data Security
321Data SecurityUse LastPass checker to find sites vulnerable to ‘Heartbleed’ and if you’ve to change your password
The password manager, LastPass, allows you to check if the saved sites are affected by the bug through its ‘LastPass Heratbleed Checker. LastPass’s Security...
-

 198Data Security
198Data SecurityYour email Password, Credit Card at Risk—Web Encryption Compromised by ‘Heart Bleed’ Bug
The new bug allows attackers to gain sensitive information protected by the SSL/TLS encryption. A new exploit in the open SSL, the...
-

 248Privacy
248PrivacyNSA revelations shake faith in U.S. tech firms as Harris poll shows public conflicted
The National Security Agency (NSA) surveillance activities revealed by former CIA contractor Edward Snowden appear to be taking a serious toll on...
-

 247Geek
247GeekFacebook could be developing Anonymous app that will force users to confess their secrets: Report
The Secret app showcases startling confessions about what a person really thinks but isn’t willing to share on sites like Facebook Reports suggest Zuckerberg has had...
-

 186Cyber Crime
186Cyber CrimeHeartbleed encryption flaw leaves millions of sites at risk
The Heartbleed bug – a flaw in an encryption technology used to protect major websites including Yahoo – has left a huge amount...
-

 66Cyber Crime
66Cyber Crime“New weapon” against malware intrusion designed by American student
A new technique for spotting cyber attacks has been designed by a young American student - and could prevent attacks against planes...
-

 227How To
227How ToHow to Record Skype Video and Audio calls for Windows and Mac
Pamela [Win] It is free to download and allows you to record calls you make using Skype. It works on Windows devices...
-
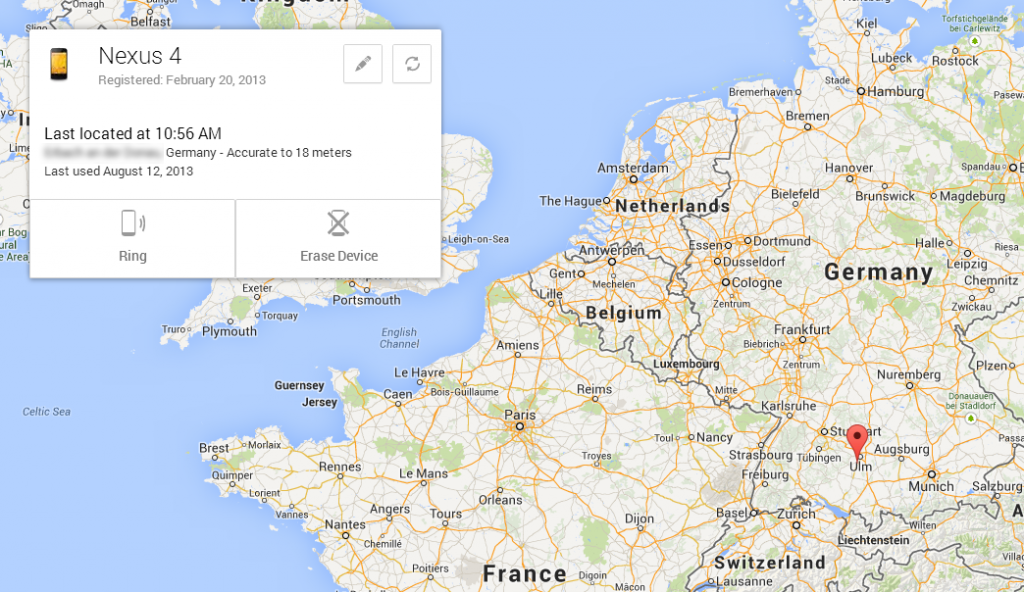
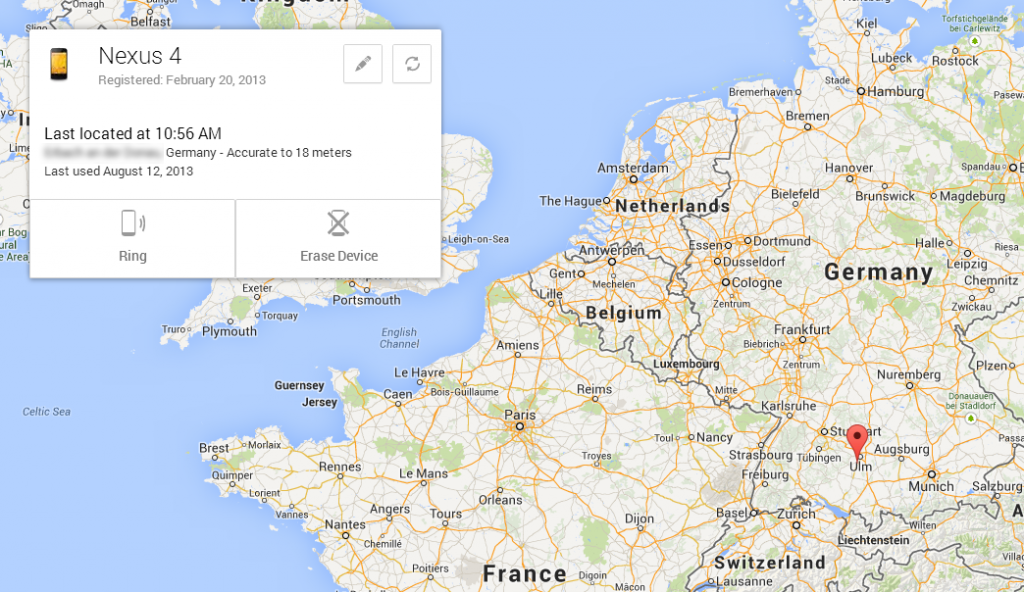 199How To
199How ToHow to Locate Your Lost Android Device Easily
Lost you android phone ..? Feeling to sad .. ? Dont worry Now we came with another Application which sorts out...
-

 147Opinion
147OpinionGoodbye, Windows XP!
This patch Tuesday, April 8, 2014, sees the last updates to be released to the public for Windows XP and Office 2003....
-

 107Privacy
107PrivacySamsung smartphones are security favourite – for adulterers
Samsung is the most popular brand of smartphone among a large portion of the adult population - adulterers, with the Korean handsets...
-

 139How To
139How ToPorts That Are Commonly Targeted By Hackers
Common ports, such as TCP port 80 (HTTP), may be locked down — but other ports may get overlooked and be vulnerable...
-

 258News
258News#OpIsrael: Israeli Ministry of Agriculture Domain Hacked, 100+ other crushed down by Anonymous
Year 2014 begin with a warning from online hacktivists Anonymous in which it warned Israel to get ready for a massive cyber...
-

 91Malware
91MalwareIf you love someone, upgrade them from XP
It is us, the nerdy geeks who are into computers, who have a moral right to help the great unwashed, and lead...
-

 264Surveillance
264SurveillanceEdward Snowden and journalist Laura Poitras Win Truth-Telling Award
Both were key players in exposing the US government surveillance program that has outraged the national and international communities alike. Laura Poitras...
-

 330Surveillance
330SurveillanceFinFisher Surveillance Challenged in Pakistani Court
A human right organization has challenged the setting up of the FinFisher surveillance technology in Pakistan, according to media reports. Bytes For...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




