Featured News
-

 89Malware
89MalwareIf you love someone, upgrade them from XP
It is us, the nerdy geeks who are into computers, who have a moral right to help the great unwashed, and lead...
-

 262Surveillance
262SurveillanceEdward Snowden and journalist Laura Poitras Win Truth-Telling Award
Both were key players in exposing the US government surveillance program that has outraged the national and international communities alike. Laura Poitras...
-

 329Surveillance
329SurveillanceFinFisher Surveillance Challenged in Pakistani Court
A human right organization has challenged the setting up of the FinFisher surveillance technology in Pakistan, according to media reports. Bytes For...
-

 197News
197NewsIndian hacker Takes Down Official website of terrorist organization Tehreek e Taliban Pakistan
The official website of terrorist organization Tehreek e Taliban Pakistan (TTP) (http://www.umarmedia.com/) has been targeted and successfully taken down by famous Indian hacker Godzilla. Godzilla hacker...
-

 78Cyber Crime
78Cyber CrimeSwooping robot attack which felled triathlete “may be work of hackers”
A competitor in an Australian triathlon was hospitalized with injuries and “pieces of propeller in her head” after a drone plunged from...
-

 354Cyber Crime
354Cyber Crime“Virus Shield” app is top‑selling hit – but does absolutely nothing
Armed with an impressive-looking shield logo, security app Virus Shield shot to the top of the sales charts on Android last week....
-

 436Password
436PasswordTwo‑thirds of parents spy “regularly” on children’s social media accounts
Two-thirds of the respondents to the survey admitted to using various methods to check on children “without their knowledge" - and one-fifth...
-

 358Password
358PasswordThe future of security: Microsoft rewards 5‑year‑old who found critical password flaw
Most five year olds can write their own name - but few have a job title to put after it. A young...
-

 194How To
194How ToMake Your Computer Work Faster In 10 Easy Steps
We all know that sinking feeling when your computer decides to slow down and barely function for no real reason. Why is...
-

 370Malware
370MalwareMicrosoft to fix zero‑day flaw that meant just previewing an Outlook email could infect your computer
It's one thing to have a security hole that relies upon users visiting an infected website, or opening a dodgy attachment -...
-

 342Surveillance
342SurveillanceNSA conducted warrantless searches of Americans’ calls and Emails! Report
One of the top intelligence officials in the Obama administration has confirmed National Security Agency (NSA) spying on the Americans’ communication using...
-

 85Cyber Crime
85Cyber CrimeWhat is EMV, and why is it such a hot topic?
You may know it by one of many names: EMV, Integrated Chip Cards, or more simply Chip & Pin or Smart Cards…...
-

 88Cyber Crime
88Cyber Crime“Domestic spyware” apps increasingly precursor to violence – or murder
Apps designed to ‘report’ on handset users’ communications while remaining undetected have increasingly become a factor in cases of domestic violence and...
-

 76Cyber Crime
76Cyber CrimeSurveillance cameras hijacked to mine Bitcoin while watching you
Malware written specifically for DVR recorders used for the output of surveillance cameras has forced some machines to mine Bitcoin - although...
-

 218News
218NewsGerman Town bans parents from calling their child ‘Wikileaks’
A couple in Southern German Town has been banned from naming their child ‘’WikiLeaks’’, claiming that it may put baby’s life in...
-
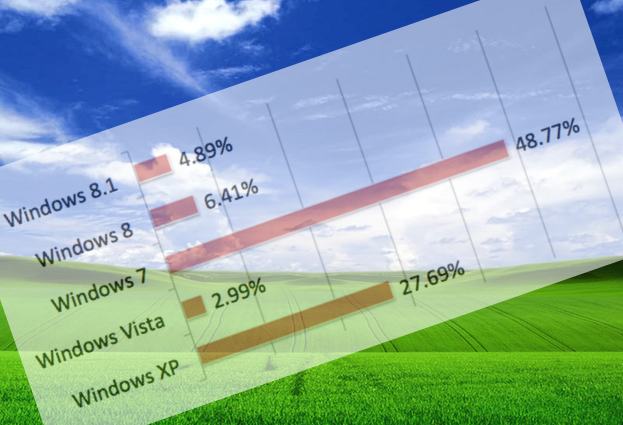
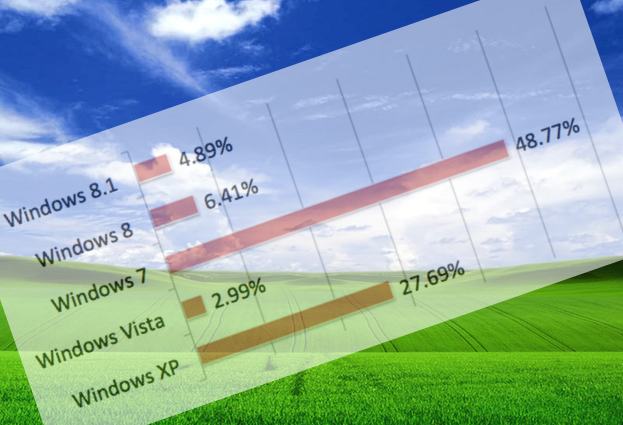 281Malware
281MalwareWith just days to go, just how many PCs are still running Windows XP?
If computers continue to run Windows XP, and don't receive any more security patches. they are not just putting themselves and the...
-

 88Cyber Crime
88Cyber CrimeAttack on Samsung’s Boxee TV service leaks 158,000 passwords and emails
An attack on the forums for the Boxee internet-TV service has yielded 158,000 customer passwords - and what appears to be email...
-
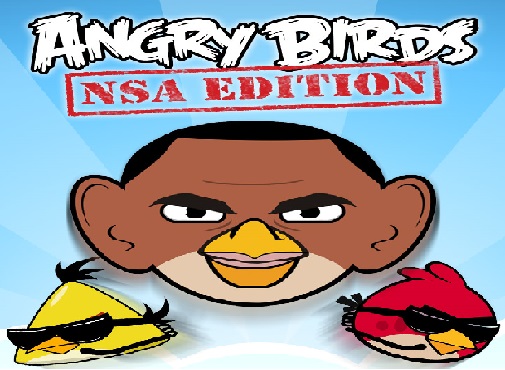
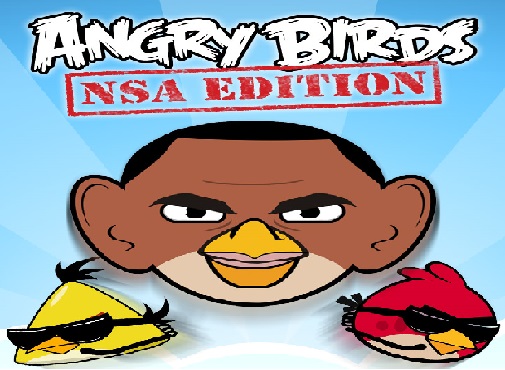 226Surveillance
226SurveillanceHow ANGRY BIRDS Game App is Sharing Your Personal Data with NSA: Proved by Researchers
Mobile applications collecting personal data of users in one form or the other is no more a stunning news. The Snowden documents...
-

 256News
256NewsEgyptian Armed Forces Training Authority Website Hacked and Defaced
On 31st March, 2014, a hacker going with the handle of ”YMH” hacked and defaced the official website of Egyptian Armed Forces Training Authority....
-

 191Malware
191MalwareWin32/Sality newest component: a router’s primary DNS changer named Win32/RBrute
DNS hijacking is still going strong and the Win32/Sality operators have added this technique to their long-lasting botnet. This blog post describes...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




