Featured News
-

 200News
200NewsIndian hacker Takes Down Official website of terrorist organization Tehreek e Taliban Pakistan
The official website of terrorist organization Tehreek e Taliban Pakistan (TTP) (http://www.umarmedia.com/) has been targeted and successfully taken down by famous Indian hacker Godzilla. Godzilla hacker...
-

 79Cyber Crime
79Cyber CrimeSwooping robot attack which felled triathlete “may be work of hackers”
A competitor in an Australian triathlon was hospitalized with injuries and “pieces of propeller in her head” after a drone plunged from...
-

 356Cyber Crime
356Cyber Crime“Virus Shield” app is top‑selling hit – but does absolutely nothing
Armed with an impressive-looking shield logo, security app Virus Shield shot to the top of the sales charts on Android last week....
-

 437Password
437PasswordTwo‑thirds of parents spy “regularly” on children’s social media accounts
Two-thirds of the respondents to the survey admitted to using various methods to check on children “without their knowledge" - and one-fifth...
-

 359Password
359PasswordThe future of security: Microsoft rewards 5‑year‑old who found critical password flaw
Most five year olds can write their own name - but few have a job title to put after it. A young...
-

 196How To
196How ToMake Your Computer Work Faster In 10 Easy Steps
We all know that sinking feeling when your computer decides to slow down and barely function for no real reason. Why is...
-

 372Malware
372MalwareMicrosoft to fix zero‑day flaw that meant just previewing an Outlook email could infect your computer
It's one thing to have a security hole that relies upon users visiting an infected website, or opening a dodgy attachment -...
-

 343Surveillance
343SurveillanceNSA conducted warrantless searches of Americans’ calls and Emails! Report
One of the top intelligence officials in the Obama administration has confirmed National Security Agency (NSA) spying on the Americans’ communication using...
-

 85Cyber Crime
85Cyber CrimeWhat is EMV, and why is it such a hot topic?
You may know it by one of many names: EMV, Integrated Chip Cards, or more simply Chip & Pin or Smart Cards…...
-

 88Cyber Crime
88Cyber Crime“Domestic spyware” apps increasingly precursor to violence – or murder
Apps designed to ‘report’ on handset users’ communications while remaining undetected have increasingly become a factor in cases of domestic violence and...
-

 77Cyber Crime
77Cyber CrimeSurveillance cameras hijacked to mine Bitcoin while watching you
Malware written specifically for DVR recorders used for the output of surveillance cameras has forced some machines to mine Bitcoin - although...
-

 219News
219NewsGerman Town bans parents from calling their child ‘Wikileaks’
A couple in Southern German Town has been banned from naming their child ‘’WikiLeaks’’, claiming that it may put baby’s life in...
-
 282Malware
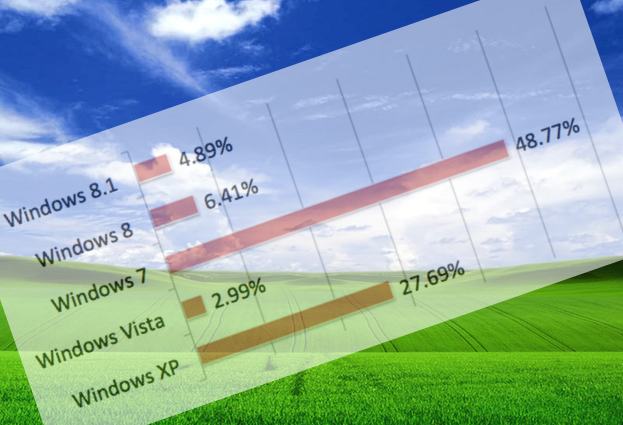
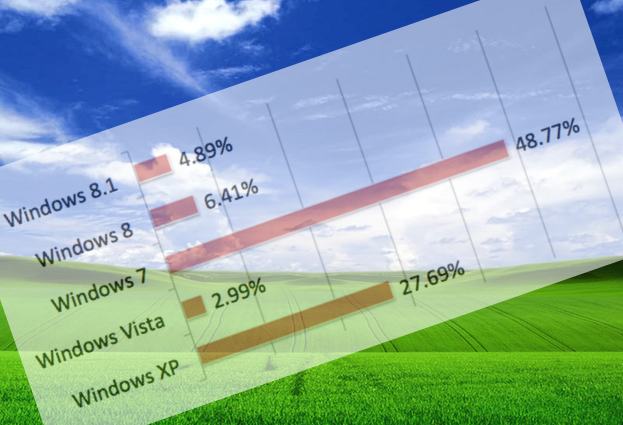
282MalwareWith just days to go, just how many PCs are still running Windows XP?
If computers continue to run Windows XP, and don't receive any more security patches. they are not just putting themselves and the...
-

 89Cyber Crime
89Cyber CrimeAttack on Samsung’s Boxee TV service leaks 158,000 passwords and emails
An attack on the forums for the Boxee internet-TV service has yielded 158,000 customer passwords - and what appears to be email...
-
 228Surveillance
228SurveillanceHow ANGRY BIRDS Game App is Sharing Your Personal Data with NSA: Proved by Researchers
Mobile applications collecting personal data of users in one form or the other is no more a stunning news. The Snowden documents...
-

 257News
257NewsEgyptian Armed Forces Training Authority Website Hacked and Defaced
On 31st March, 2014, a hacker going with the handle of ”YMH” hacked and defaced the official website of Egyptian Armed Forces Training Authority....
-

 192Malware
192MalwareWin32/Sality newest component: a router’s primary DNS changer named Win32/RBrute
DNS hijacking is still going strong and the Win32/Sality operators have added this technique to their long-lasting botnet. This blog post describes...
-

 222Privacy
222PrivacyNew Harris poll shows NSA revelations impact online shopping, banking, and more
A new Harris poll shows that revelations about the National Security Agency’s digital surveillance activities are changing online behavior for many Americans...
-

 471Password
471PasswordCredit cards are dead, long live fingerprints? Samsung S5 first of ‘many’ scan‑to‑pay phones
Samsung's Galaxy S5 offers a cutting-edge component that will change m-commerce forever - a fingerprint-scanner which offers instant authentication with one finger-swipe...
-
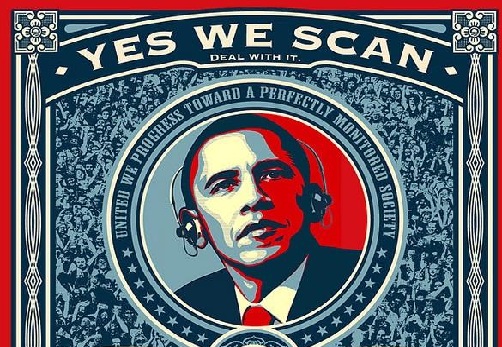
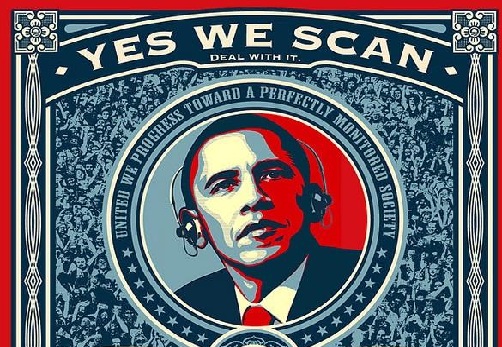 307News
307NewsSnowden Document Reveals NSA spied on 122 world leaders
Documents leaked by the ex-NSA contractor and the whistleblower, Edward Snowden, indicate GCHQ and NSA along with the US government were hand...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




