Featured News
-

 221Privacy
221PrivacyNew Harris poll shows NSA revelations impact online shopping, banking, and more
A new Harris poll shows that revelations about the National Security Agency’s digital surveillance activities are changing online behavior for many Americans...
-

 470Password
470PasswordCredit cards are dead, long live fingerprints? Samsung S5 first of ‘many’ scan‑to‑pay phones
Samsung's Galaxy S5 offers a cutting-edge component that will change m-commerce forever - a fingerprint-scanner which offers instant authentication with one finger-swipe...
-
 305News
305NewsSnowden Document Reveals NSA spied on 122 world leaders
Documents leaked by the ex-NSA contractor and the whistleblower, Edward Snowden, indicate GCHQ and NSA along with the US government were hand...
-

 316News
316NewsKuwait’ Ministry of Internal Affairs Website Hacked, hacker demands interference in Syria
The official website belonging to the Ministry of Internal Affairs of Kuwait was hacked and defaced on 26th March, 2014 by unknown...
-
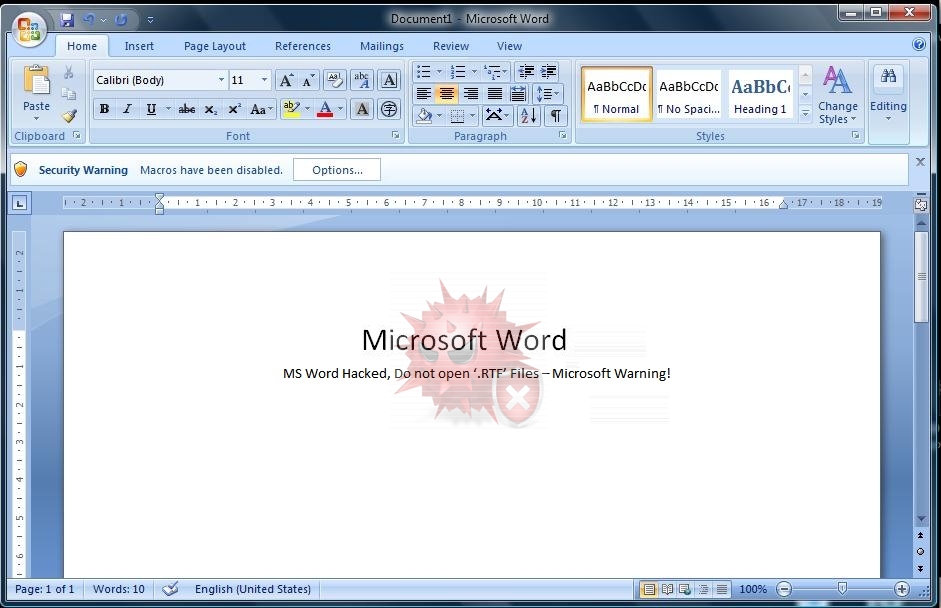
 283Data Security
283Data SecurityMicrosoft Warning: MS Word Has Been Hacked, Do not open ‘.RTF’ Files
Microsoft has issued a warning about a possible hacking attempt through an RTF exploit code, according to its official blog. The latest...
-
 130News
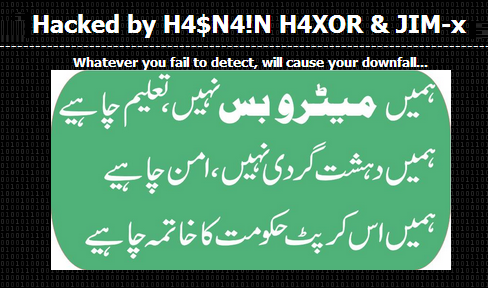
130NewsPakistani Consulate in Jeddah Website Hacked against Corrupt Government
A Pakistani hacker going with the handle Hasnain Haxor from Pakistan Haxor Crew has hacked and defaced the official website of Pakistani consulate in...
-

 200Data Security
200Data SecuritySpammers using “No War on Syria” petitions to steal personal information
Spammers are taking advantage of the various online petitions against the recent news about the alleged arming of the Syrian rebels by...
-

 171News
171NewsAnonymous Ecuador Hacks Official Twitter Account of Ecuador President
The official Twitter account of Ecuadoran president Rafael Correa was hacked last Thursday with several anti-government tweets spammed over the social media. The hacked Twitter...
-
 264News
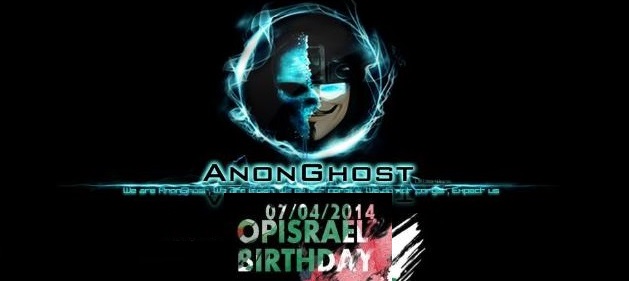
264NewsIsraeli Ministry of Agriculture and Rural Development Domain Hacked by AnonGhost
The pro-Palestinian hacktivist AnonGhost has hacked and defaced the official website of Israeli Agricultural Research Organization, which is ran by Israeli Ministry of...
-

 319How To
319How To5 Tips for protecting Windows XP machines after April 8, 2014
Microsoft will cease providing security updates for the Windows XP operating system on April 8, 2014. If you cannot get away from...
-

 509Cyber Crime
509Cyber CrimeThe Internet of Things isn’t a malware‑laced game of cyber‑Cluedo… yet
Will the future be a murderous game of 'smart device' Cluedo, where Colonel Mustard meets his death at the hands of a...
-

 78Cyber Crime
78Cyber CrimeChannel Cybercrime: Bug allows hackers to hijack screen of Philips TVs
Hackers could take control of Philips ‘smart TVs’ and broadcast their own ‘shows’ to watching famlies, thanks to a ‘fixed’ password which...
-

 191Cyber Events
191Cyber EventsAnonymous threatens cyberattack on Albuquerque Police Department for shooting and killing homeless man
Anonymous threatens cyberattack on Albuquerque Police Department for shooting and killing mentally ill homeless man James M. Boyd. File photo of mentally ill...
-
 304Data Security
304Data SecurityHackers Target Monster Jobs Website with Gameover Zeus malware
A security firm has revealed that hackers are targeting companies utilizing services of Monster Jobs, a well-known job portal, through a new...
-

 480Privacy
480PrivacyPRISM‑proof system could turn servers into spook‑proof fortresses
A young MIT student has invented a new system for storing data which could offer protection against unscrupulous colleagues - and even...
-
 214News
214NewsFamous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data
Famous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data. A hacker going with the handle of ‘Seo’...
-
 383Windows
383WindowsTime to Move On From Windows XP
Windows XP comes to an end of sorts on April 8, 2014. After this, Microsoft will cease providing security updates or support...
-
 286Opinion
286OpinionBetter Mac Testing: Static versus Dynamic Testing
Dynamic or on-access Mac testing of AV products is problematical with samples for which Apple has implemented signature detection.
-
 243News
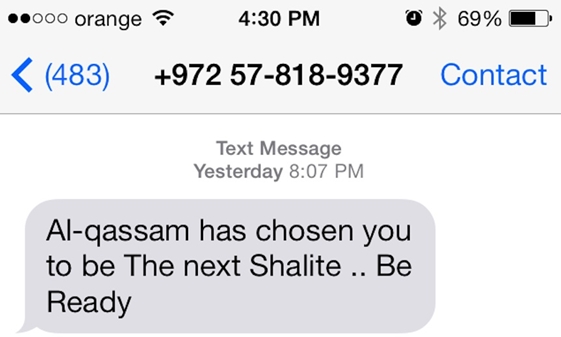
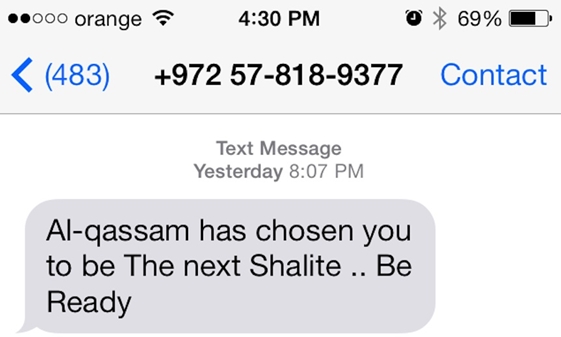
243NewsHackers Breached Israeli Defence Forum, gathered info, sent threatening SMS to Israeli journalists
A possibility that Muslim hackers could have compromised the IsraelDefense magazine (www.israeldefense.com) database and its website, to launch the recent SMS attack on...
-

 222Surveillance
222SurveillanceJimmy Carter Believes the NSA Spies on Him
In an exclusive interview with NBC, the ex-American president Mr. Jimmy Carter expressed his views on the NSA; according to which Mr. Carter believes...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




