Featured News
-

 251Privacy
251PrivacyNSA revelations shake faith in U.S. tech firms as Harris poll shows public conflicted
The National Security Agency (NSA) surveillance activities revealed by former CIA contractor Edward Snowden appear to be taking a serious toll on...
-

 249Geek
249GeekFacebook could be developing Anonymous app that will force users to confess their secrets: Report
The Secret app showcases startling confessions about what a person really thinks but isn’t willing to share on sites like Facebook Reports suggest Zuckerberg has had...
-

 194Cyber Crime
194Cyber CrimeHeartbleed encryption flaw leaves millions of sites at risk
The Heartbleed bug – a flaw in an encryption technology used to protect major websites including Yahoo – has left a huge amount...
-

 68Cyber Crime
68Cyber Crime“New weapon” against malware intrusion designed by American student
A new technique for spotting cyber attacks has been designed by a young American student - and could prevent attacks against planes...
-

 230How To
230How ToHow to Record Skype Video and Audio calls for Windows and Mac
Pamela [Win] It is free to download and allows you to record calls you make using Skype. It works on Windows devices...
-
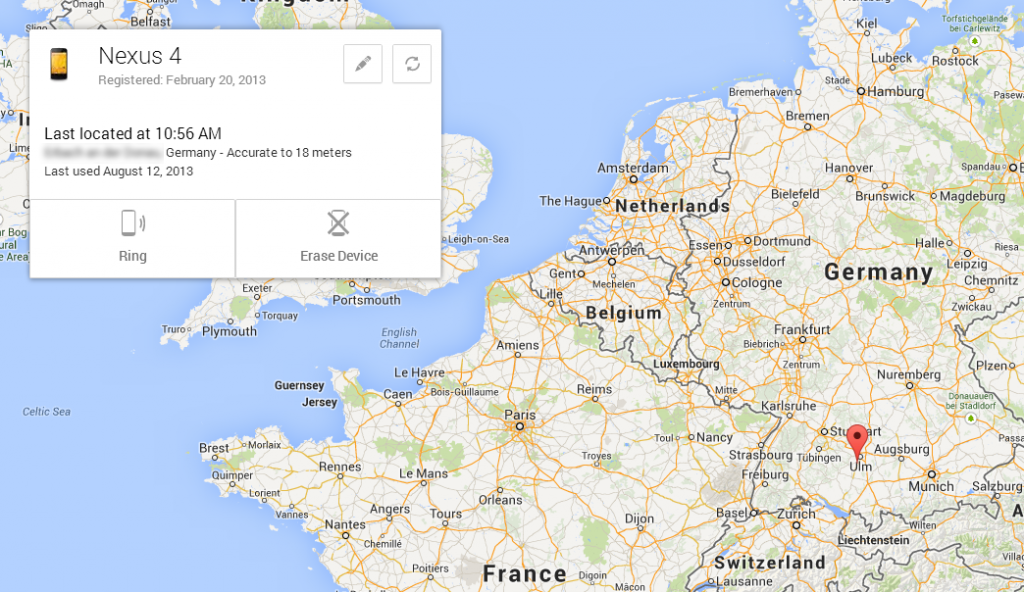
 200How To
200How ToHow to Locate Your Lost Android Device Easily
Lost you android phone ..? Feeling to sad .. ? Dont worry Now we came with another Application which sorts out...
-

 152Opinion
152OpinionGoodbye, Windows XP!
This patch Tuesday, April 8, 2014, sees the last updates to be released to the public for Windows XP and Office 2003....
-

 114Privacy
114PrivacySamsung smartphones are security favourite – for adulterers
Samsung is the most popular brand of smartphone among a large portion of the adult population - adulterers, with the Korean handsets...
-

 143How To
143How ToPorts That Are Commonly Targeted By Hackers
Common ports, such as TCP port 80 (HTTP), may be locked down — but other ports may get overlooked and be vulnerable...
-

 261News
261News#OpIsrael: Israeli Ministry of Agriculture Domain Hacked, 100+ other crushed down by Anonymous
Year 2014 begin with a warning from online hacktivists Anonymous in which it warned Israel to get ready for a massive cyber...
-

 94Malware
94MalwareIf you love someone, upgrade them from XP
It is us, the nerdy geeks who are into computers, who have a moral right to help the great unwashed, and lead...
-

 269Surveillance
269SurveillanceEdward Snowden and journalist Laura Poitras Win Truth-Telling Award
Both were key players in exposing the US government surveillance program that has outraged the national and international communities alike. Laura Poitras...
-

 334Surveillance
334SurveillanceFinFisher Surveillance Challenged in Pakistani Court
A human right organization has challenged the setting up of the FinFisher surveillance technology in Pakistan, according to media reports. Bytes For...
-

 203News
203NewsIndian hacker Takes Down Official website of terrorist organization Tehreek e Taliban Pakistan
The official website of terrorist organization Tehreek e Taliban Pakistan (TTP) (http://www.umarmedia.com/) has been targeted and successfully taken down by famous Indian hacker Godzilla. Godzilla hacker...
-

 83Cyber Crime
83Cyber CrimeSwooping robot attack which felled triathlete “may be work of hackers”
A competitor in an Australian triathlon was hospitalized with injuries and “pieces of propeller in her head” after a drone plunged from...
-

 362Cyber Crime
362Cyber Crime“Virus Shield” app is top‑selling hit – but does absolutely nothing
Armed with an impressive-looking shield logo, security app Virus Shield shot to the top of the sales charts on Android last week....
-

 440Password
440PasswordTwo‑thirds of parents spy “regularly” on children’s social media accounts
Two-thirds of the respondents to the survey admitted to using various methods to check on children “without their knowledge" - and one-fifth...
-

 363Password
363PasswordThe future of security: Microsoft rewards 5‑year‑old who found critical password flaw
Most five year olds can write their own name - but few have a job title to put after it. A young...
-

 199How To
199How ToMake Your Computer Work Faster In 10 Easy Steps
We all know that sinking feeling when your computer decides to slow down and barely function for no real reason. Why is...
-

 377Malware
377MalwareMicrosoft to fix zero‑day flaw that meant just previewing an Outlook email could infect your computer
It's one thing to have a security hole that relies upon users visiting an infected website, or opening a dodgy attachment -...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




