Featured News
-

 317News
317NewsKuwait’ Ministry of Internal Affairs Website Hacked, hacker demands interference in Syria
The official website belonging to the Ministry of Internal Affairs of Kuwait was hacked and defaced on 26th March, 2014 by unknown...
-
 284Data Security
284Data SecurityMicrosoft Warning: MS Word Has Been Hacked, Do not open ‘.RTF’ Files
Microsoft has issued a warning about a possible hacking attempt through an RTF exploit code, according to its official blog. The latest...
-
 131News
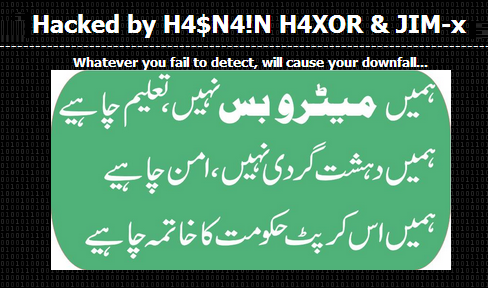
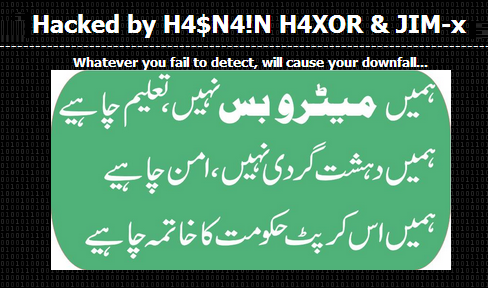
131NewsPakistani Consulate in Jeddah Website Hacked against Corrupt Government
A Pakistani hacker going with the handle Hasnain Haxor from Pakistan Haxor Crew has hacked and defaced the official website of Pakistani consulate in...
-

 202Data Security
202Data SecuritySpammers using “No War on Syria” petitions to steal personal information
Spammers are taking advantage of the various online petitions against the recent news about the alleged arming of the Syrian rebels by...
-

 172News
172NewsAnonymous Ecuador Hacks Official Twitter Account of Ecuador President
The official Twitter account of Ecuadoran president Rafael Correa was hacked last Thursday with several anti-government tweets spammed over the social media. The hacked Twitter...
-
 265News
265NewsIsraeli Ministry of Agriculture and Rural Development Domain Hacked by AnonGhost
The pro-Palestinian hacktivist AnonGhost has hacked and defaced the official website of Israeli Agricultural Research Organization, which is ran by Israeli Ministry of...
-

 320How To
320How To5 Tips for protecting Windows XP machines after April 8, 2014
Microsoft will cease providing security updates for the Windows XP operating system on April 8, 2014. If you cannot get away from...
-

 511Cyber Crime
511Cyber CrimeThe Internet of Things isn’t a malware‑laced game of cyber‑Cluedo… yet
Will the future be a murderous game of 'smart device' Cluedo, where Colonel Mustard meets his death at the hands of a...
-

 78Cyber Crime
78Cyber CrimeChannel Cybercrime: Bug allows hackers to hijack screen of Philips TVs
Hackers could take control of Philips ‘smart TVs’ and broadcast their own ‘shows’ to watching famlies, thanks to a ‘fixed’ password which...
-

 192Cyber Events
192Cyber EventsAnonymous threatens cyberattack on Albuquerque Police Department for shooting and killing homeless man
Anonymous threatens cyberattack on Albuquerque Police Department for shooting and killing mentally ill homeless man James M. Boyd. File photo of mentally ill...
-
 305Data Security
305Data SecurityHackers Target Monster Jobs Website with Gameover Zeus malware
A security firm has revealed that hackers are targeting companies utilizing services of Monster Jobs, a well-known job portal, through a new...
-

 482Privacy
482PrivacyPRISM‑proof system could turn servers into spook‑proof fortresses
A young MIT student has invented a new system for storing data which could offer protection against unscrupulous colleagues - and even...
-
 215News
215NewsFamous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data
Famous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data. A hacker going with the handle of ‘Seo’...
-
 384Windows
384WindowsTime to Move On From Windows XP
Windows XP comes to an end of sorts on April 8, 2014. After this, Microsoft will cease providing security updates or support...
-
 287Opinion
287OpinionBetter Mac Testing: Static versus Dynamic Testing
Dynamic or on-access Mac testing of AV products is problematical with samples for which Apple has implemented signature detection.
-
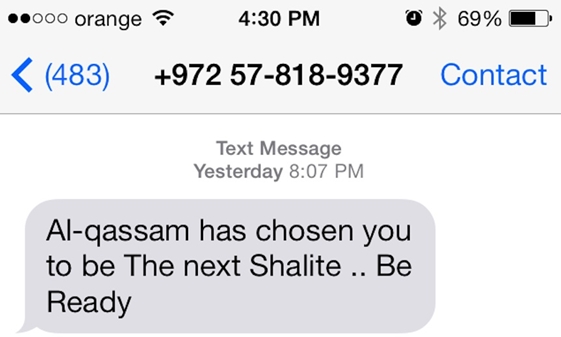
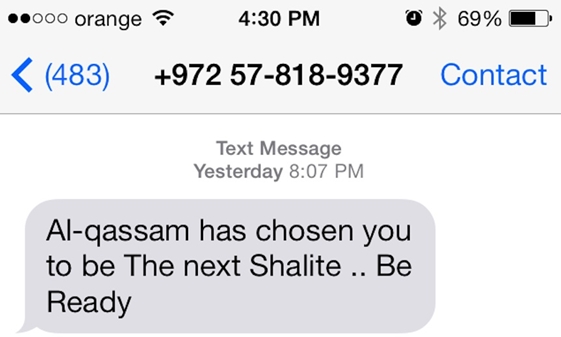 245News
245NewsHackers Breached Israeli Defence Forum, gathered info, sent threatening SMS to Israeli journalists
A possibility that Muslim hackers could have compromised the IsraelDefense magazine (www.israeldefense.com) database and its website, to launch the recent SMS attack on...
-

 222Surveillance
222SurveillanceJimmy Carter Believes the NSA Spies on Him
In an exclusive interview with NBC, the ex-American president Mr. Jimmy Carter expressed his views on the NSA; according to which Mr. Carter believes...
-
 409Password
409PasswordMark Zuckerberg invests in CAPTCHA‑crushing AI which “thinks like a human”
Mark Zuckerberg, Paypal founder Elon Musk and Ashton Kutcher have invested $40 million in an artificial-intelligence start-up, Vicarious, which can already 'read'...
-

 247News
247NewsDocuments Leaked by Snowden show NSA Spied on Chinese Government and Huawei Telecom
NSA hacked into servers of Huawei Technologies, a Chinese network manufacturer, and collected information to plant ‘backdoors’ on their equipment, according to...
-

 74Cyber Crime
74Cyber CrimeBitcoin fixes Mt Gox theft bug – as exchange staff find 200,000 BTC in ‘forgotten’ wallet
Bitcoin’s developers have released a new version of the software, which includes a long-awaited fix for the “transaction malleability” bug which is...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




