Featured News
-
 407Password
407PasswordMark Zuckerberg invests in CAPTCHA‑crushing AI which “thinks like a human”
Mark Zuckerberg, Paypal founder Elon Musk and Ashton Kutcher have invested $40 million in an artificial-intelligence start-up, Vicarious, which can already 'read'...
-

 245News
245NewsDocuments Leaked by Snowden show NSA Spied on Chinese Government and Huawei Telecom
NSA hacked into servers of Huawei Technologies, a Chinese network manufacturer, and collected information to plant ‘backdoors’ on their equipment, according to...
-

 73Cyber Crime
73Cyber CrimeBitcoin fixes Mt Gox theft bug – as exchange staff find 200,000 BTC in ‘forgotten’ wallet
Bitcoin’s developers have released a new version of the software, which includes a long-awaited fix for the “transaction malleability” bug which is...
-
 237News
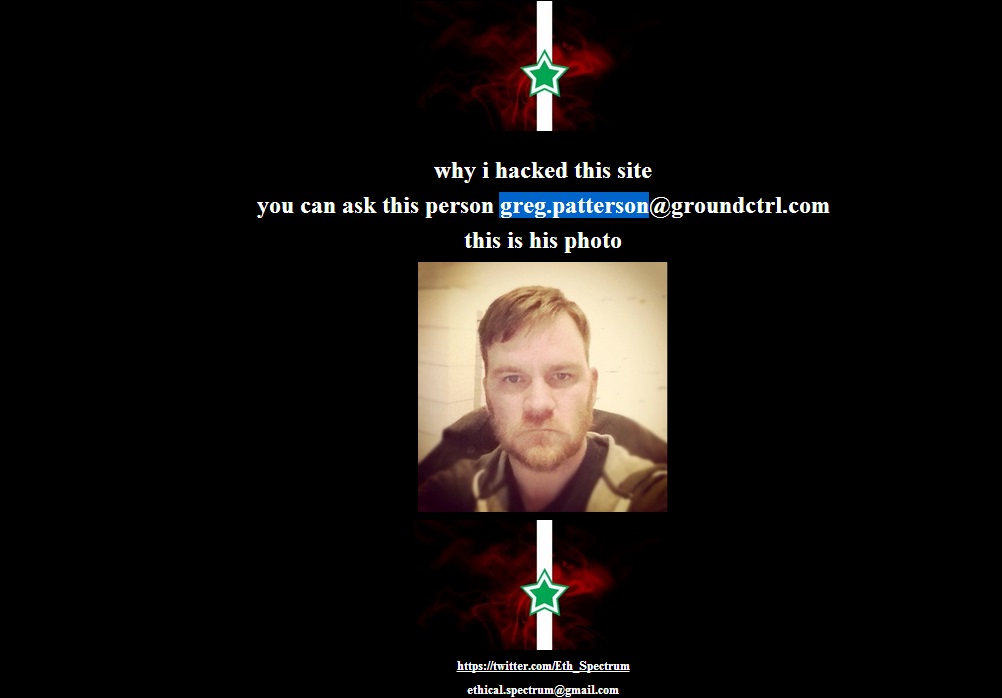
237NewsOfficial website of Miley Cyrus, Taylor Swift, Britney Spears, Selena Gomez and Nicki Minaj Hacked
A hacker going with the handle of Eth_Spectrum had hacked and defaced the official websites of top Hollywood celebrities including Miley Cyrus, Taylor Swift,...
-
 121News
121NewsHacked Emails Show How Much Microsoft Charges FBI for Selling Your Personal Data
According to documents leaked by the Syrian Electronic Army, Microsoft have been charging the FBI with millions of Dollars a year for giving them...
-

 121Privacy
121PrivacyGoogle encrypts ALL Gmail to keep snoopers out
Starting today, Gmail will use an encrypted HTTPS connection to check or send email, regardless of what platform users employ to access...
-

 227Surveillance
227SurveillanceWhy The NSA is Trying to Keep Its Water Usage a Secret?
The list of secrets held by the NSA is a never-ending one. Latest in the list includes its refusal to disclose the amount...
-

 151Malware
151Malware10 years of Mac OS X malware
The malware problem on Mac OS X is nothing like as bad as it is on Windows, but that doesn't mean it...
-

 96How To
96How ToMaster of Mavericks: How to secure your Mac using Apple’s latest update
Apple’s Mavericks update was the first free update to Mac OS X – itself a big step forward for security, as all...
-
 205Android
205AndroidStealth malware sneaks onto Android phones, then “turns evil” when OS upgrades
A new form of Android malware could bypass one of the main warning systems built into Google’s smartphone and tablet OS -...
-

 102Cyber Crime
102Cyber CrimeTarget breach optioned as Sony feature film
The Target breach, and in particular the role of respected security blogger Brian Krebs in breaking the story, has been optioned as...
-
 178Geek
178GeekAlert: Tor Browser app in the Apple Store is fake, spreading Malwares and Spywares! Do not download!
Tor Browser app in the Apple app store is fake and have been found spreading adware and spywares. According to the official website...
-

 503Privacy
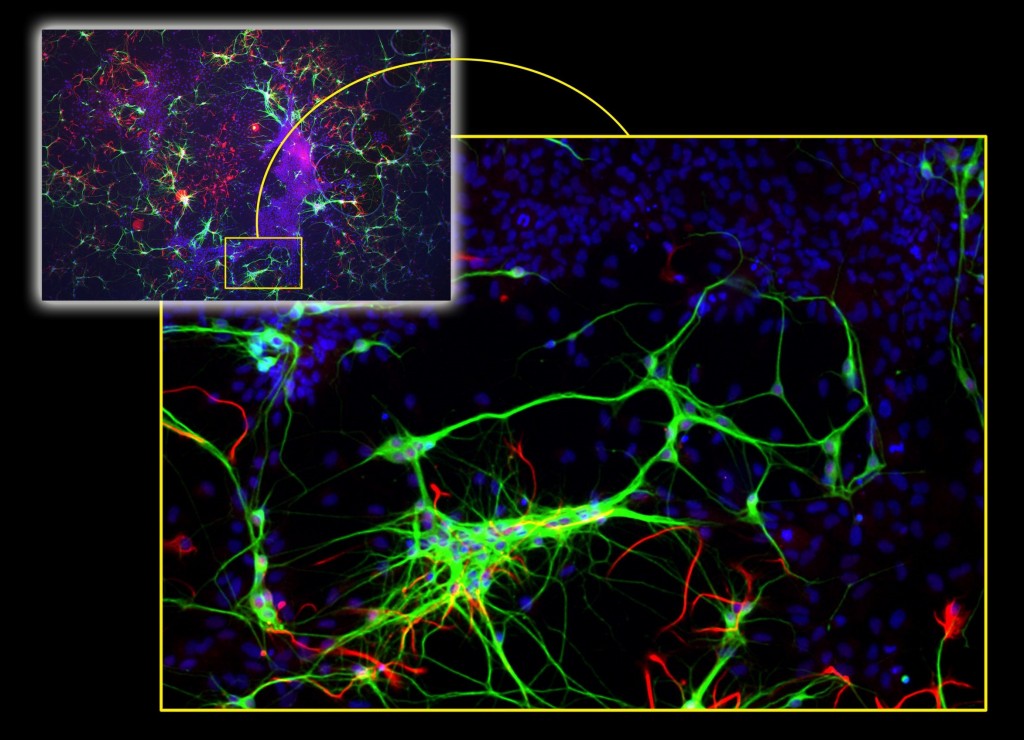
503PrivacyFacebook’s ‘Deepface’ photo‑matching is nearly as good as human brains
Facebook’s ‘Deepface’ photo-matching software can now ‘recognize’ human faces with an accuracy just a fraction of a percentage point behind human beings...
-

 91Malware
91MalwareGoogle Glass spyware lets snoopers “see through wearer’s eyes”
Spyware which stealthily takes photographs using Google Glass’s built-in camera and uploads them to a remote server without the user being aware...
-

 139Opinion
139OpinionBetter Mac Testing? How OS security can make AV testing harder
As Mac malware increases in prevalence, testing security software that supplements OS X internal security gets more important and more difficult.
-

 196Geek
196GeekPalestinian activists all set to release boycott Israel app for smartphone
Boycott Israel through Smartphones, a higher level of anti-Israel campaign launched by pro-Palestinian activists from Boycott, Divestment and Sanctions movement (BDS). The Boycott...
-
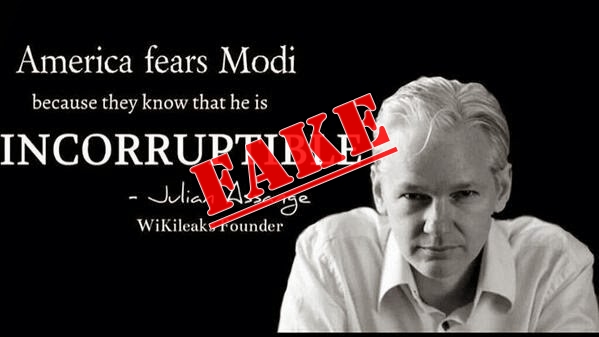
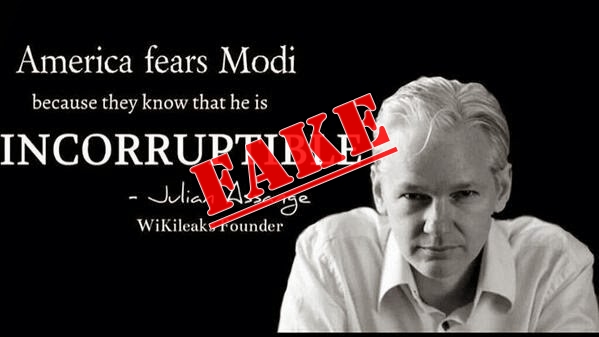 202News
202NewsIndian politician faking WikiLeaks’ Julian Assange words to gain popularity
Indian politicians have taken social media to its greatest height during the coming 16th Lok Sabha elections. A politician’s strength and mass following...
-
 68Cyber Crime
68Cyber CrimeOver 500,000 PCs attacked every day after 25,000 UNIX servers hijacked by Operation Windigo
Malware researchers at ESET have uncovered a widespread cybercriminal operation that has seized control of tens of thousands of Unix servers. Learn...
-

 500Malware
500MalwareOperation Windigo – the vivisection of a large Linux server‑side credential‑stealing malware campaign
Our report titled “Operation Windigo – the vivisection of a large Linux server-side credential-stealing malware campaign" details our analysis of a set...
-

 75Cyber Crime
75Cyber CrimeMore than 80% of business leaders feel “unprepared” for cyber incidents
More than 80% of business leaders do not feel fully prepared for the effects of a major cyber incident, according to a...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




