Featured News
-

 350Surveillance
350SurveillanceNSA conducted warrantless searches of Americans’ calls and Emails! Report
One of the top intelligence officials in the Obama administration has confirmed National Security Agency (NSA) spying on the Americans’ communication using...
-

 90Cyber Crime
90Cyber CrimeWhat is EMV, and why is it such a hot topic?
You may know it by one of many names: EMV, Integrated Chip Cards, or more simply Chip & Pin or Smart Cards…...
-

 93Cyber Crime
93Cyber Crime“Domestic spyware” apps increasingly precursor to violence – or murder
Apps designed to ‘report’ on handset users’ communications while remaining undetected have increasingly become a factor in cases of domestic violence and...
-

 79Cyber Crime
79Cyber CrimeSurveillance cameras hijacked to mine Bitcoin while watching you
Malware written specifically for DVR recorders used for the output of surveillance cameras has forced some machines to mine Bitcoin - although...
-

 226News
226NewsGerman Town bans parents from calling their child ‘Wikileaks’
A couple in Southern German Town has been banned from naming their child ‘’WikiLeaks’’, claiming that it may put baby’s life in...
-
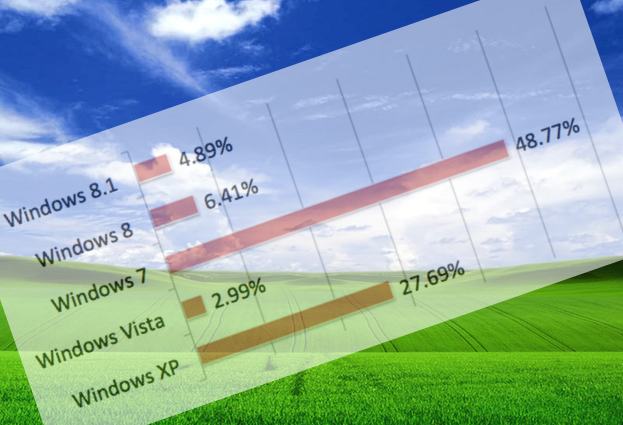
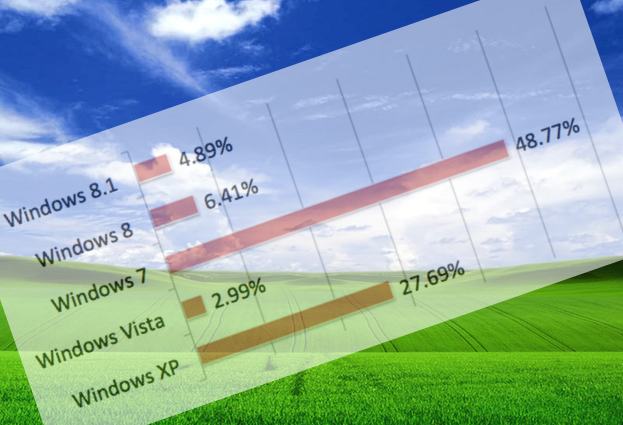 287Malware
287MalwareWith just days to go, just how many PCs are still running Windows XP?
If computers continue to run Windows XP, and don't receive any more security patches. they are not just putting themselves and the...
-

 93Cyber Crime
93Cyber CrimeAttack on Samsung’s Boxee TV service leaks 158,000 passwords and emails
An attack on the forums for the Boxee internet-TV service has yielded 158,000 customer passwords - and what appears to be email...
-
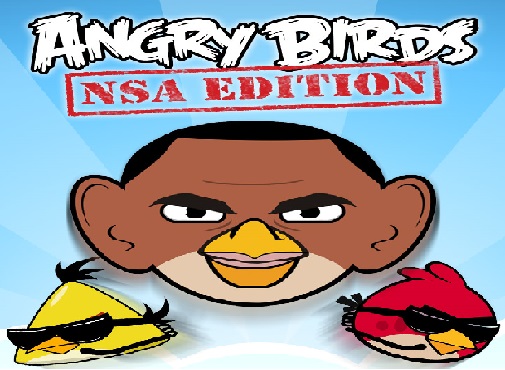
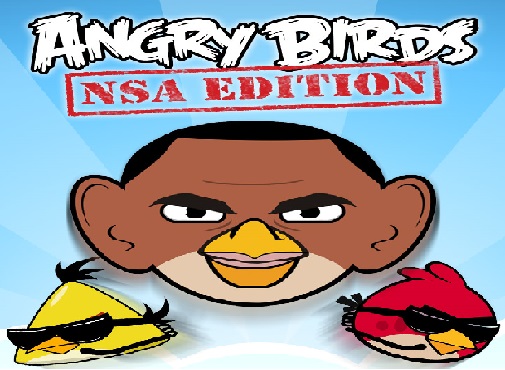 230Surveillance
230SurveillanceHow ANGRY BIRDS Game App is Sharing Your Personal Data with NSA: Proved by Researchers
Mobile applications collecting personal data of users in one form or the other is no more a stunning news. The Snowden documents...
-

 261News
261NewsEgyptian Armed Forces Training Authority Website Hacked and Defaced
On 31st March, 2014, a hacker going with the handle of ”YMH” hacked and defaced the official website of Egyptian Armed Forces Training Authority....
-

 194Malware
194MalwareWin32/Sality newest component: a router’s primary DNS changer named Win32/RBrute
DNS hijacking is still going strong and the Win32/Sality operators have added this technique to their long-lasting botnet. This blog post describes...
-

 226Privacy
226PrivacyNew Harris poll shows NSA revelations impact online shopping, banking, and more
A new Harris poll shows that revelations about the National Security Agency’s digital surveillance activities are changing online behavior for many Americans...
-

 474Password
474PasswordCredit cards are dead, long live fingerprints? Samsung S5 first of ‘many’ scan‑to‑pay phones
Samsung's Galaxy S5 offers a cutting-edge component that will change m-commerce forever - a fingerprint-scanner which offers instant authentication with one finger-swipe...
-
 310News
310NewsSnowden Document Reveals NSA spied on 122 world leaders
Documents leaked by the ex-NSA contractor and the whistleblower, Edward Snowden, indicate GCHQ and NSA along with the US government were hand...
-

 323News
323NewsKuwait’ Ministry of Internal Affairs Website Hacked, hacker demands interference in Syria
The official website belonging to the Ministry of Internal Affairs of Kuwait was hacked and defaced on 26th March, 2014 by unknown...
-
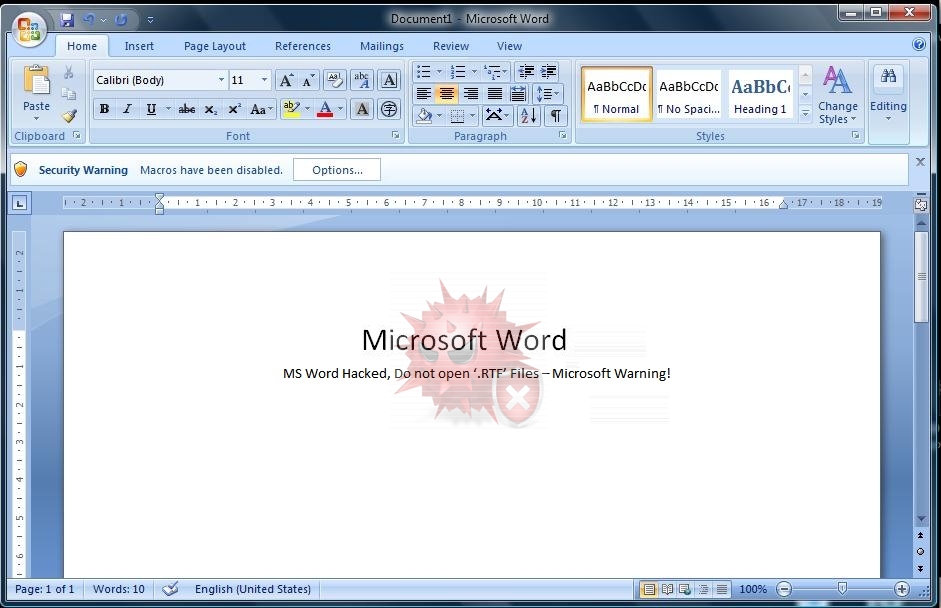
 288Data Security
288Data SecurityMicrosoft Warning: MS Word Has Been Hacked, Do not open ‘.RTF’ Files
Microsoft has issued a warning about a possible hacking attempt through an RTF exploit code, according to its official blog. The latest...
-
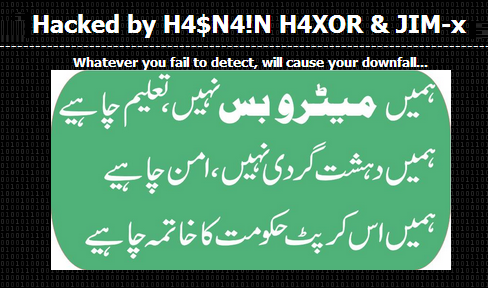
 133News
133NewsPakistani Consulate in Jeddah Website Hacked against Corrupt Government
A Pakistani hacker going with the handle Hasnain Haxor from Pakistan Haxor Crew has hacked and defaced the official website of Pakistani consulate in...
-

 204Data Security
204Data SecuritySpammers using “No War on Syria” petitions to steal personal information
Spammers are taking advantage of the various online petitions against the recent news about the alleged arming of the Syrian rebels by...
-

 175News
175NewsAnonymous Ecuador Hacks Official Twitter Account of Ecuador President
The official Twitter account of Ecuadoran president Rafael Correa was hacked last Thursday with several anti-government tweets spammed over the social media. The hacked Twitter...
-
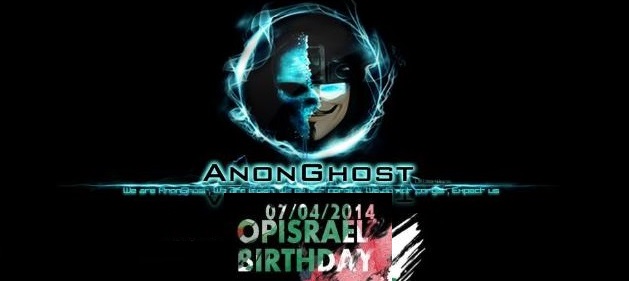
 267News
267NewsIsraeli Ministry of Agriculture and Rural Development Domain Hacked by AnonGhost
The pro-Palestinian hacktivist AnonGhost has hacked and defaced the official website of Israeli Agricultural Research Organization, which is ran by Israeli Ministry of...
-

 326How To
326How To5 Tips for protecting Windows XP machines after April 8, 2014
Microsoft will cease providing security updates for the Windows XP operating system on April 8, 2014. If you cannot get away from...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




