Featured News
-

 103Cyber Crime
103Cyber CrimeTarget breach optioned as Sony feature film
The Target breach, and in particular the role of respected security blogger Brian Krebs in breaking the story, has been optioned as...
-
 178Geek
178GeekAlert: Tor Browser app in the Apple Store is fake, spreading Malwares and Spywares! Do not download!
Tor Browser app in the Apple app store is fake and have been found spreading adware and spywares. According to the official website...
-

 504Privacy
504PrivacyFacebook’s ‘Deepface’ photo‑matching is nearly as good as human brains
Facebook’s ‘Deepface’ photo-matching software can now ‘recognize’ human faces with an accuracy just a fraction of a percentage point behind human beings...
-

 92Malware
92MalwareGoogle Glass spyware lets snoopers “see through wearer’s eyes”
Spyware which stealthily takes photographs using Google Glass’s built-in camera and uploads them to a remote server without the user being aware...
-

 140Opinion
140OpinionBetter Mac Testing? How OS security can make AV testing harder
As Mac malware increases in prevalence, testing security software that supplements OS X internal security gets more important and more difficult.
-

 197Geek
197GeekPalestinian activists all set to release boycott Israel app for smartphone
Boycott Israel through Smartphones, a higher level of anti-Israel campaign launched by pro-Palestinian activists from Boycott, Divestment and Sanctions movement (BDS). The Boycott...
-
 203News
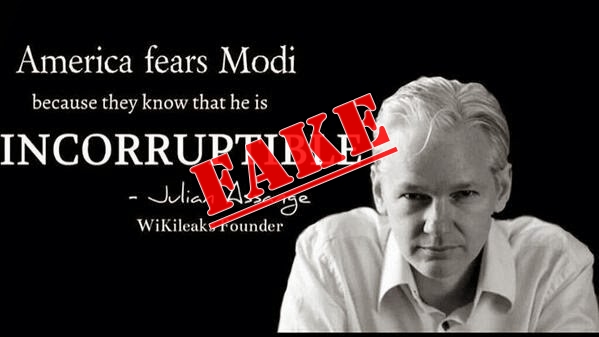
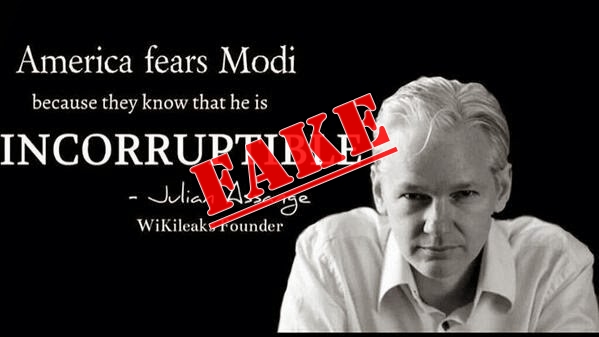
203NewsIndian politician faking WikiLeaks’ Julian Assange words to gain popularity
Indian politicians have taken social media to its greatest height during the coming 16th Lok Sabha elections. A politician’s strength and mass following...
-
 69Cyber Crime
69Cyber CrimeOver 500,000 PCs attacked every day after 25,000 UNIX servers hijacked by Operation Windigo
Malware researchers at ESET have uncovered a widespread cybercriminal operation that has seized control of tens of thousands of Unix servers. Learn...
-

 502Malware
502MalwareOperation Windigo – the vivisection of a large Linux server‑side credential‑stealing malware campaign
Our report titled “Operation Windigo – the vivisection of a large Linux server-side credential-stealing malware campaign" details our analysis of a set...
-

 76Cyber Crime
76Cyber CrimeMore than 80% of business leaders feel “unprepared” for cyber incidents
More than 80% of business leaders do not feel fully prepared for the effects of a major cyber incident, according to a...
-

 182How To
182How ToFive tips to help control your privacy on Mac OS X
Apple’s Mac OS X Mavericks has some very neat privacy features built in - from a “Guest User” account which restricts people...
-
 260News
260NewsOfficial Website of Multi-Hazard Early Warning System for Africa and Asia Hacked
The official website of Regional Integrated Multi-Hazard Early Warning System for Africa and Asia (RIMES) has been hacked and defaced by Indonesian hacking...
-

 218How To
218How ToTips for protecting against sextortion
It seems like every few days there is a new story involving teenaged girls being tricked or blackmailed into sending compromising pictures...
-
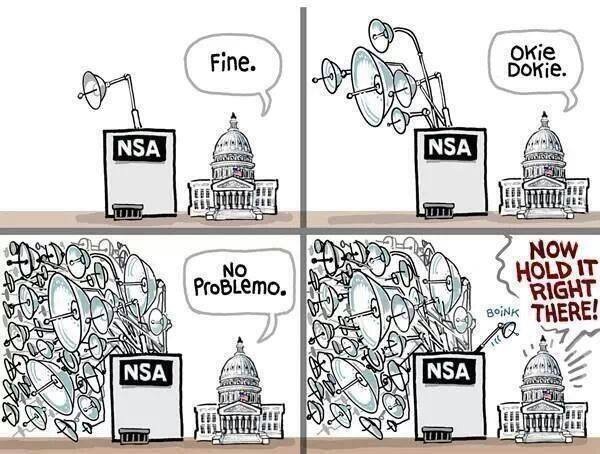
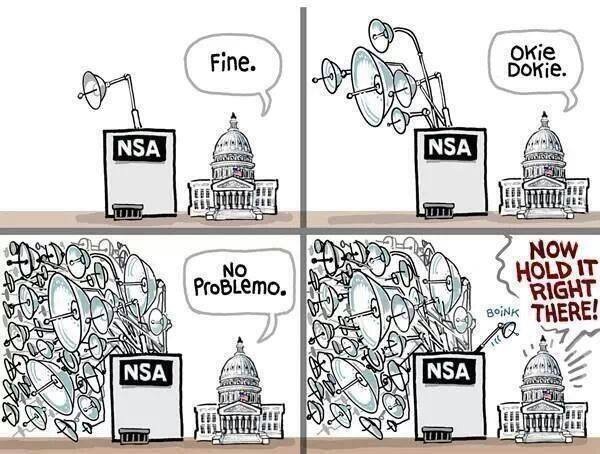 186Cyber Events
186Cyber EventsHypocrisy of Sen. Feinstein and White House over spying best defined in one meme
The CIA and the US senate committee are at loggerheads, according to media reports on Tuesday. This meme describes the Hypocrisy at...
-
 112Malware
112Malware“You have cancer” phishing attack shows how low cybercriminals will go
A “particularly unpleasant” phishing email purporting to be the results of a blood count report showing that the recipient may have cancer...
-

 96Password
96PasswordNew wearable from makers of Pine smartwatch aims to be “key to everything”
A new wearable authenticator built to be the key to “everything” will be designed by some of the hottest new talents in...
-

 410Cyber Crime
410Cyber CrimeScam Alert: Missing Malaysia Jet found in Bermuda Triangle Viral Facebook links are Malicious
The scammers take advantage of every incident to trick people and get some bucks or likes on social media. Same is going...
-

 229News
229NewsPowerful DDoS attack by Ukrainian hackers takes down NATO and its Cyber Defence Centre Server
A group of Ukrainian hackers going with the handle of CyberBerkut has taken down the official website of North Atlantic Treaty Organization (NATO) along with...
-

 230Data Security
230Data SecurityVulnerability in WhatsApp Allows Hackers To Read Your Conversation and View Media
Bad news for WhatsApp users on Android. If you chat on WhatsApp, it’s time to be careful and avoid getting too private. An...
-

 212News
212NewsSyrian Hackers Claim They’ve Compromised US Central Command
Syrian Hackers have stated that they have compromised the central command of the US. Syrian Hackers Claim They’ve Compromised US Central Command...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




