Featured News
-
 217News
217NewsFamous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data
Famous South Korean Search Portal NAVER Hacked, 25 Million accounts Hacked Using Stolen Data. A hacker going with the handle of ‘Seo’...
-
 386Windows
386WindowsTime to Move On From Windows XP
Windows XP comes to an end of sorts on April 8, 2014. After this, Microsoft will cease providing security updates or support...
-
 291Opinion
291OpinionBetter Mac Testing: Static versus Dynamic Testing
Dynamic or on-access Mac testing of AV products is problematical with samples for which Apple has implemented signature detection.
-
 249News
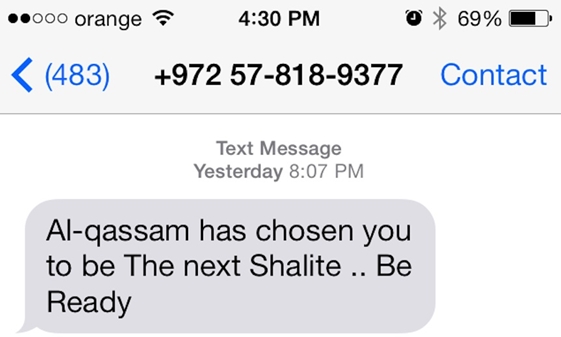
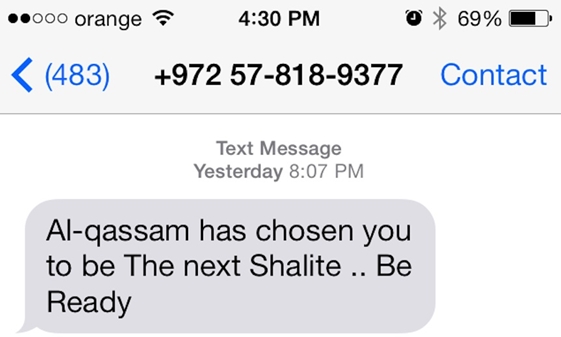
249NewsHackers Breached Israeli Defence Forum, gathered info, sent threatening SMS to Israeli journalists
A possibility that Muslim hackers could have compromised the IsraelDefense magazine (www.israeldefense.com) database and its website, to launch the recent SMS attack on...
-

 225Surveillance
225SurveillanceJimmy Carter Believes the NSA Spies on Him
In an exclusive interview with NBC, the ex-American president Mr. Jimmy Carter expressed his views on the NSA; according to which Mr. Carter believes...
-
 412Password
412PasswordMark Zuckerberg invests in CAPTCHA‑crushing AI which “thinks like a human”
Mark Zuckerberg, Paypal founder Elon Musk and Ashton Kutcher have invested $40 million in an artificial-intelligence start-up, Vicarious, which can already 'read'...
-

 252News
252NewsDocuments Leaked by Snowden show NSA Spied on Chinese Government and Huawei Telecom
NSA hacked into servers of Huawei Technologies, a Chinese network manufacturer, and collected information to plant ‘backdoors’ on their equipment, according to...
-

 77Cyber Crime
77Cyber CrimeBitcoin fixes Mt Gox theft bug – as exchange staff find 200,000 BTC in ‘forgotten’ wallet
Bitcoin’s developers have released a new version of the software, which includes a long-awaited fix for the “transaction malleability” bug which is...
-
 239News
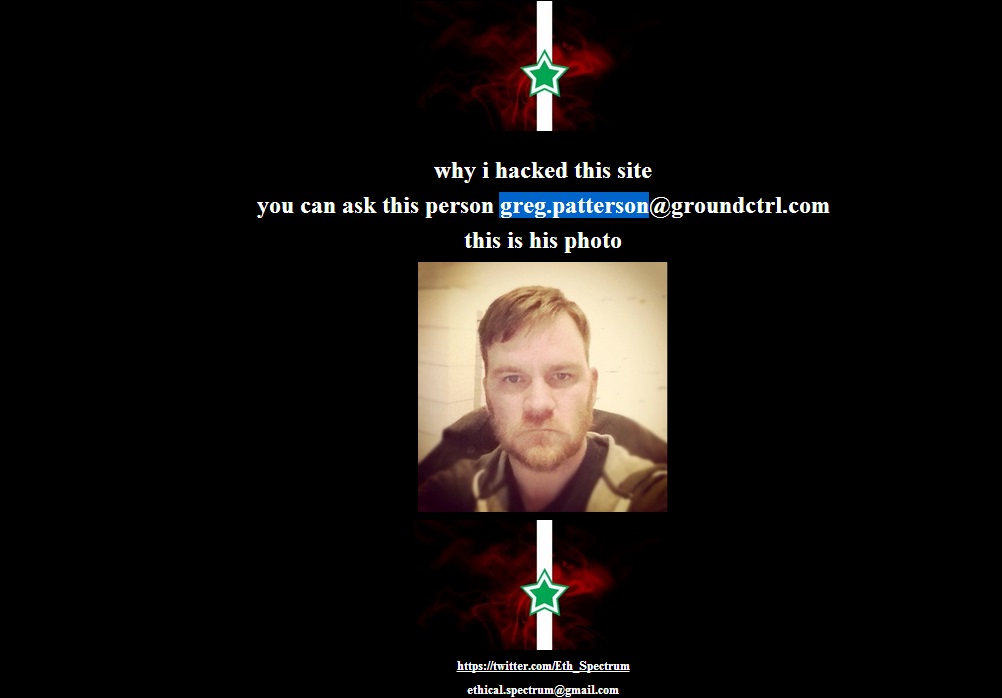
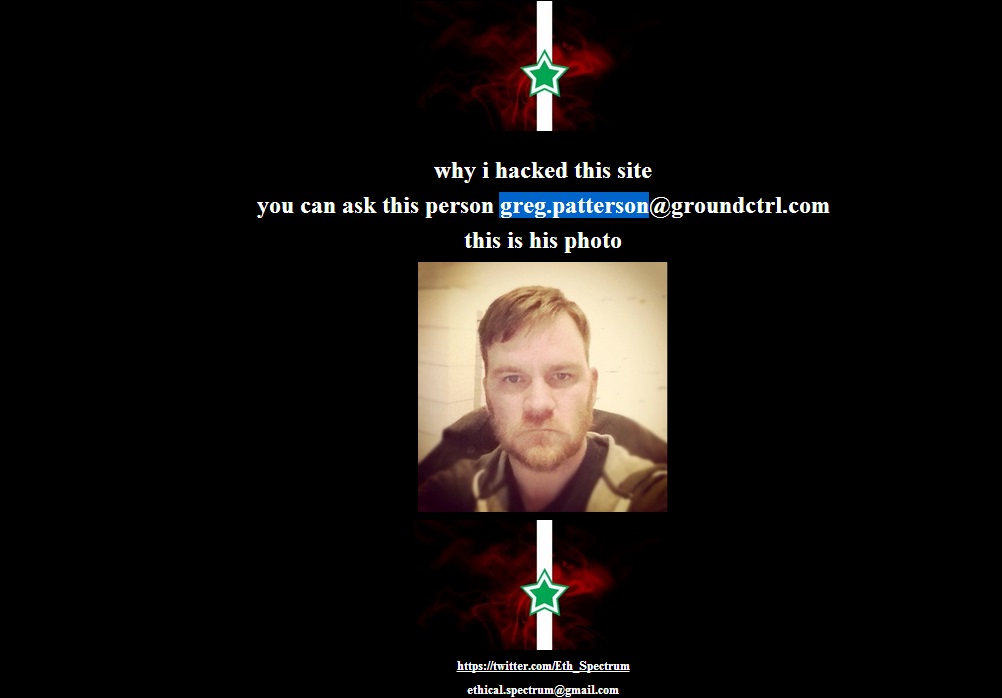
239NewsOfficial website of Miley Cyrus, Taylor Swift, Britney Spears, Selena Gomez and Nicki Minaj Hacked
A hacker going with the handle of Eth_Spectrum had hacked and defaced the official websites of top Hollywood celebrities including Miley Cyrus, Taylor Swift,...
-
 125News
125NewsHacked Emails Show How Much Microsoft Charges FBI for Selling Your Personal Data
According to documents leaked by the Syrian Electronic Army, Microsoft have been charging the FBI with millions of Dollars a year for giving them...
-

 124Privacy
124PrivacyGoogle encrypts ALL Gmail to keep snoopers out
Starting today, Gmail will use an encrypted HTTPS connection to check or send email, regardless of what platform users employ to access...
-

 232Surveillance
232SurveillanceWhy The NSA is Trying to Keep Its Water Usage a Secret?
The list of secrets held by the NSA is a never-ending one. Latest in the list includes its refusal to disclose the amount...
-

 157Malware
157Malware10 years of Mac OS X malware
The malware problem on Mac OS X is nothing like as bad as it is on Windows, but that doesn't mean it...
-

 100How To
100How ToMaster of Mavericks: How to secure your Mac using Apple’s latest update
Apple’s Mavericks update was the first free update to Mac OS X – itself a big step forward for security, as all...
-
 208Android
208AndroidStealth malware sneaks onto Android phones, then “turns evil” when OS upgrades
A new form of Android malware could bypass one of the main warning systems built into Google’s smartphone and tablet OS -...
-

 104Cyber Crime
104Cyber CrimeTarget breach optioned as Sony feature film
The Target breach, and in particular the role of respected security blogger Brian Krebs in breaking the story, has been optioned as...
-
 181Geek
181GeekAlert: Tor Browser app in the Apple Store is fake, spreading Malwares and Spywares! Do not download!
Tor Browser app in the Apple app store is fake and have been found spreading adware and spywares. According to the official website...
-

 508Privacy
508PrivacyFacebook’s ‘Deepface’ photo‑matching is nearly as good as human brains
Facebook’s ‘Deepface’ photo-matching software can now ‘recognize’ human faces with an accuracy just a fraction of a percentage point behind human beings...
-

 97Malware
97MalwareGoogle Glass spyware lets snoopers “see through wearer’s eyes”
Spyware which stealthily takes photographs using Google Glass’s built-in camera and uploads them to a remote server without the user being aware...
-

 143Opinion
143OpinionBetter Mac Testing? How OS security can make AV testing harder
As Mac malware increases in prevalence, testing security software that supplements OS X internal security gets more important and more difficult.
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




