Featured News
-
 186Cyber Events
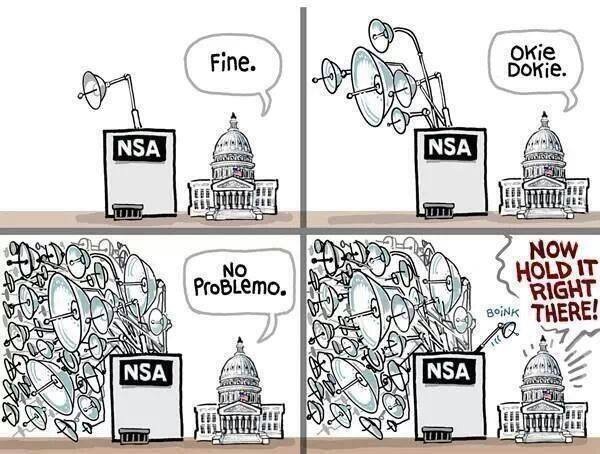
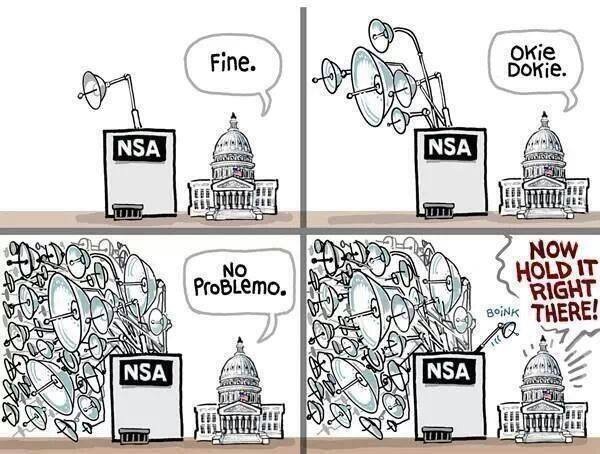
186Cyber EventsHypocrisy of Sen. Feinstein and White House over spying best defined in one meme
The CIA and the US senate committee are at loggerheads, according to media reports on Tuesday. This meme describes the Hypocrisy at...
-
 112Malware
112Malware“You have cancer” phishing attack shows how low cybercriminals will go
A “particularly unpleasant” phishing email purporting to be the results of a blood count report showing that the recipient may have cancer...
-

 96Password
96PasswordNew wearable from makers of Pine smartwatch aims to be “key to everything”
A new wearable authenticator built to be the key to “everything” will be designed by some of the hottest new talents in...
-

 410Cyber Crime
410Cyber CrimeScam Alert: Missing Malaysia Jet found in Bermuda Triangle Viral Facebook links are Malicious
The scammers take advantage of every incident to trick people and get some bucks or likes on social media. Same is going...
-

 229News
229NewsPowerful DDoS attack by Ukrainian hackers takes down NATO and its Cyber Defence Centre Server
A group of Ukrainian hackers going with the handle of CyberBerkut has taken down the official website of North Atlantic Treaty Organization (NATO) along with...
-

 230Data Security
230Data SecurityVulnerability in WhatsApp Allows Hackers To Read Your Conversation and View Media
Bad news for WhatsApp users on Android. If you chat on WhatsApp, it’s time to be careful and avoid getting too private. An...
-

 212News
212NewsSyrian Hackers Claim They’ve Compromised US Central Command
Syrian Hackers have stated that they have compromised the central command of the US. Syrian Hackers Claim They’ve Compromised US Central Command...
-

 115Malware
115MalwareMicrosoft Word users urged to apply urgent fix after targeted attacks
Microsoft Word users have been urged to update their software after attacks against users of MS Word 2010, where opening a “specially...
-
 133Privacy
133PrivacyBrainwave privacy standard “is needed” to prevent spying on EEG scan data, researchers warn
Smartphone apps and home equipment for scanning brainwaves could lead to a future in which governments or companies misuse such data as...
-

 400Data Security
400Data SecuritySnowden Leaks: NSA Posed as Facebook to infect computers with malware
According to one of the recent report, NSA is believed to be spying many Facebook users since 2010. NSA used a number...
-

 191Cyber Crime
191Cyber CrimeFake video of Malaysia Airlines flight MH370 rescue is ‘callous’ cyber scam
A post promising a video of a plane landing on water has been circulating on Facebook, with a title suggesting that it...
-

 113Scams
113ScamsMore Mystery Shopper Misery
'Highly-paid' mystery shopper assignments where you're sent cashier's checks upfront can end up costing you a lot of money.
-

 218Android
218AndroidHidden backdoor in top Samsung Galaxy models ‘allows remote spying on users’
A hidden backdoor in the modified version of Android run by nine Samsung Galaxy models could allow attackers to spy remotely on...
-

 117Surveillance
117SurveillanceSnowden at SXSW Conference: They’re “setting fire to the future of the Internet”
Edward Snowden, the NSA whistleblower made his longest public appearance at the SXSW conference since his surveillance act. This was done through...
-

 321Cyber Crime
321Cyber CrimeRomanian Man Kills 4 Year Old Son, commits Suicide After Police Ransomware Tells Him He Must Pay Fine
A man from Romania has committed suicide after his computer got infected with “police ransomware,” according to a local media report. Police...
-

 396Password
396PasswordTop e‑commerce sites still fail to warn users who choose “password”
Two-thirds of top e-commerce sites still accept the weakest passwords, such as “123456” and “password” without warning users that these are the...
-

 84Cyber Crime
84Cyber CrimeFridge attacks “raise big questions” says Microsoft security chief
The emerging ‘internet of things’ raises big security questions, and vulnerabilities in connected devices such as ‘smart’ fridges may force companies to...
-
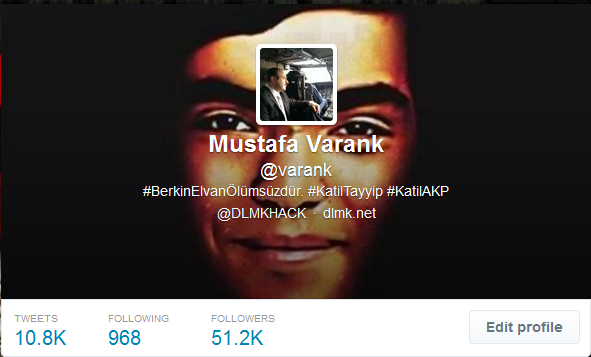
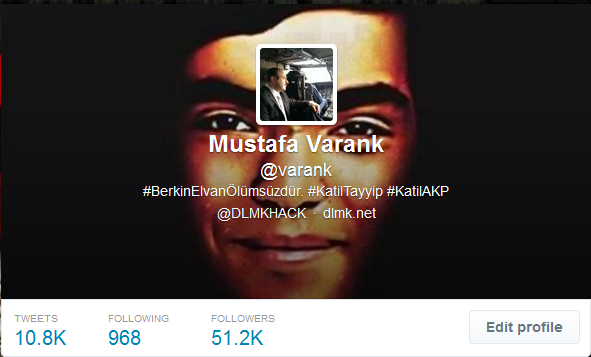 247News
247NewsTwitter account of Turkish PM’s top adviser hacked, messages left against Berkin Elvan’s death
A group of Turkish hackers have hacked the official Twitter account of Mustafa Varank, who is a top political advisers of Prime...
-
 476Malware
476MalwareCritical Internet Explorer zero‑day vulnerability patched by Microsoft
Microsoft releases a fix for a zero-day vulnerability that has already been exploited by hackers in targeted attacks against some organisations. Don't...
-

 301Surveillance
301SurveillanceApp Controlled Drone That Will Shoot You With an 80,000 Volt Taser (Video Added)
A tech-firm has amazed the world with its proof-of-demonstration of a remote-controlled “stun copter” that can deliver 80,000 volts of electricity to...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




