Featured News
-
 245News
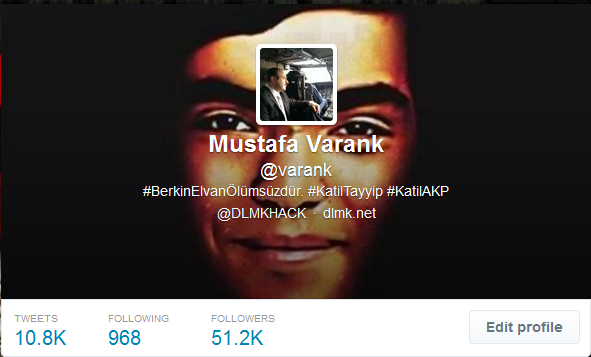
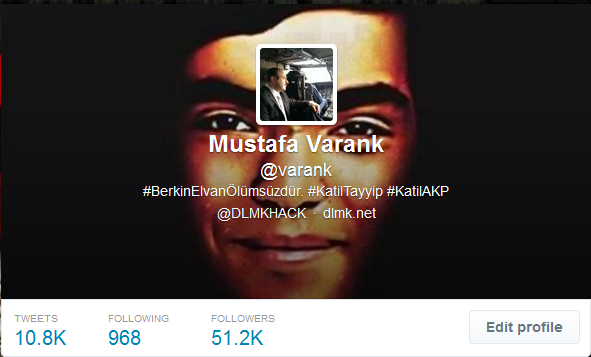
245NewsTwitter account of Turkish PM’s top adviser hacked, messages left against Berkin Elvan’s death
A group of Turkish hackers have hacked the official Twitter account of Mustafa Varank, who is a top political advisers of Prime...
-
 474Malware
474MalwareCritical Internet Explorer zero‑day vulnerability patched by Microsoft
Microsoft releases a fix for a zero-day vulnerability that has already been exploited by hackers in targeted attacks against some organisations. Don't...
-

 299Surveillance
299SurveillanceApp Controlled Drone That Will Shoot You With an 80,000 Volt Taser (Video Added)
A tech-firm has amazed the world with its proof-of-demonstration of a remote-controlled “stun copter” that can deliver 80,000 volts of electricity to...
-

 371Password
371PasswordSmartphones with fingerprint‑scanning screens ‘on sale by summer’
Smartphones such as iPhone 5S rely on buttons to scan fingerprints - but the CEO of biometrics firm CrucialTec says that smartphones...
-

 81Cyber Crime
81Cyber CrimeGoogle Glass app offers new level of security for ATM users
A futuristic app uses Google Glass to add an extra layer of privacy for users withdrawing cash from ATM machines - by...
-

 198Geek
198GeekBoeing to release self destructing black phone to aid spies and diplomats
Boeing is set to launch a self-destructing smartphone that would aid the spies, diplomats and others keep their data secure, according to...
-

 84Cyber Crime
84Cyber CrimeFinancial files from Mt Gox supposedly ‘leak online’ after CEO targeted
A file of material purporting to include detailed information on trades at the Bitcoin exchange Mt Gox, has surfaced online, after attackers...
-

 134Scams
134ScamsThe Billgate Foundation – the fall for money, eh many…
Recently it was announced that Satya Nadella will be Steve Ballmer’s successor as CEO of Microsoft. Of course for the cybercriminals this...
-

 270Scams
270ScamsFive ‘new friends’ to avoid like the plague on social networks
Befriending the wrong person on Facebook can hand a criminal the tools for an identity theft attack - and on LinkedIn, talking...
-
 231Cyber Crime
231Cyber CrimeJustin Bieber is the latest celebrity to have his Twitter account hacked
Maybe it's time to think twice before rushing to click on a link, next time your favourite celebrity says something bizarre on...
-

 146Scams
146ScamsHow cybercriminals ‘market’ email attacks – and why LinkedIn lures are today’s prize phish
Cybercriminals ‘manage’ phishing emails using techniques similar to those used by marketing agencies, including the use of ‘test audiences’ to see how...
-

 164Privacy
164Privacy‘Secure’ web browsing can leak private data to employers and ISPs, researchers warn
University of Berkeley researchers have revealed a technique for identifying individual web pages visited ‘securely’ by users, with up to 89% accuracy,...
-

 247News
247NewsSnowden’s Latest Leak has fake UFO Images: Claims expert
A document among the trove leaked by Edward Snowden contains slides showing images of flying saucer as reported by Yahoo News Following...
-
 322News
322NewsCyberwar Heating Up: Ukraine hit by massive cyber attack from Russia, mobile networks blocked
The telecommunication system of Ukraine has got hit by cyber-attacks through the equipment which have been installed in the Russian-influenced Crimea. These...
-
 151Opinion
151OpinionCourier Scams – don’t give away your bank card
If someone rings you up to tell you that your bank card has been compromised, it may be because they want to...
-

 391Malware
391MalwareAndroid phones and tablets ship “pre‑infected” with malware
Android phones and tablets from four different manufacturers are arriving with malware “pre-installed” - a bogus version of Netflix which sends password...
-

 284News
284NewsMysterious UFO Photos Found in Documents Leaked by Snowden
Ex-NSA tech Snowden leaked documents had yet another element of surprise; it has a set of slides depicting mysterious spacecrafts referring to Flying...
-

 88Cyber Crime
88Cyber CrimeWWF warns of ‘arms race’ with ‘cyberpoachers’ targeting endangered species
Criminals seeking to kill endangered species and sell trophies online are turning to increasingly hi-tech methods to target their prey - including...
-

 69Cyber Crime
69Cyber CrimeBitcoin bank Flexcoin shuts down after attackers loot $570,000 from “hot wallet”
The attackers were able to steal all the bitcoins stored in the bank’s “hot wallet” - the portion of its funds on...
-

 100How To
100How ToHow can we as patients secure our medical data?
When someone says “data privacy” most people think about the information that is available on sites like Google and Facebook, or stored...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




