Featured News
-
 212Cyber Events
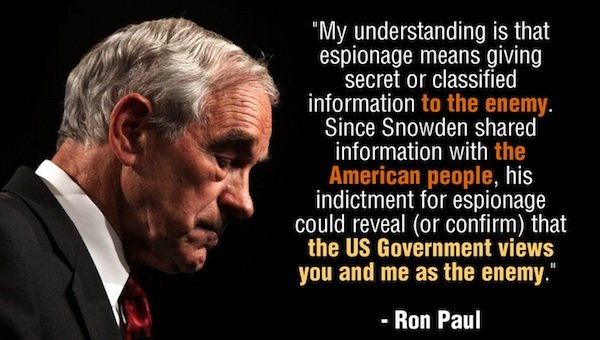
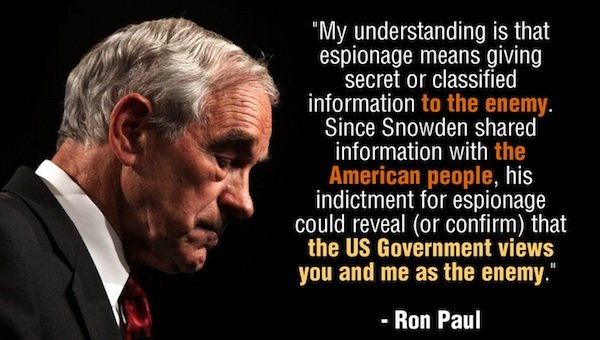
212Cyber EventsRon Paul Launches Clemency Petition for Snowden!
Ron Paul, a former Texas congressman, has launched a petition seeking clemency for Edward Snowden, the whistleblower who leaked data about the NSA surveillance...
-
 178Geek
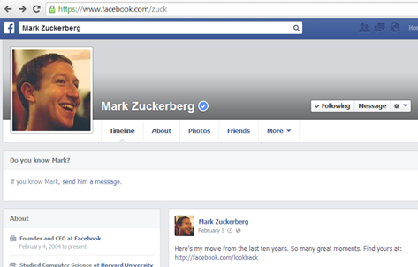
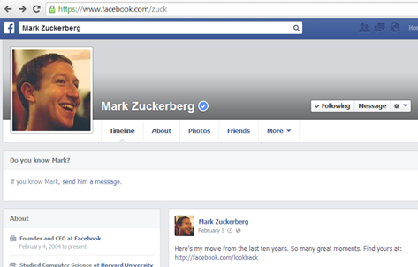
178GeekEgyptian hacker removes Mark Zuckerberg’s Facebook Timeline Photo
An Egyptian hacker removed Mark Zuckerberg’s Facebook timeline cover photo from his account using a private exploit, according to a latest hacker...
-

 228Cyber Events
228Cyber EventsBrazil is spying on social media accounts of protesters, hoping to protect World Cup
According to the officials, the security forces of Brazil are constantly using secret agents and thoroughly supervising the social media in order...
-

 212News
212NewsLulzSec Peru hacks Twitter account of Venezuela’s Ruling Party against Twitter Cencorship
World renowned hacktivists from LulzSec Peru have hacked a verified Twitter account of United Socialist Party of Venezuela (PSUV). After taking over the Twitter account, the hacktivists...
-

 276News
276NewsRedHack Leaks Contact Details of US Embassy staff in Turkey
Turkish based RedHack hacktivist claims to leak personal information and contact details of US embassy’ staff in Turkey. The dumped data shows...
-

 278News
278NewsSyrian Electronic Army hacks Forbes Website and Twitter account for spreading hate against Syria
The hardcore supporters of Syrian President Bashar-Al-Assad from Syrian Electronic Army have hacked the American business magazine Forbes. As a result of hack, a...
-
 75Cyber Crime
75Cyber CrimeSilk Road 2.0 drug market hit, millions stolen from bitcoin reserve
A large scale cyber-theft has drained the relaunched ‘online drug bazaar’ Silk Road 2.0 of nearly all of its Bitcoin reserves -...
-
 289News
289NewsAnonymous Ukraine Claims to hack and leak secret email conversations of Vitali Klitschko’s UDAR party
Activists in Ukraine are fighting a battle on ground, while hacktavists are putting their share online. The Anonymous Ukraine, in an email...
-

 381Password
381PasswordTwo‑thirds of couples ‘share passwords to online accounts’, Pew research finds
Couples who have been in a long-term relationship indulge in risky online behaviour, such as sharing passwords for online accounts, with two-thirds...
-
 175Cyber Crime
175Cyber CrimeThe 400Gbps largest DDoS attack has hit Europe using NTP Amplification
For temporary abandoning the services of the host that is connected to some internet, the most widely used and favorite method that...
-
 90Cyber Crime
90Cyber CrimeKaspersky Uncovers sophisticated Spying operation ‘The Mask’ targeted diplomats, govts for 7 years
Kaspersky Lab, the Moscow-based computer security software firm, has unearthed a cyber-spying campaign apparently started by a Spanish-speaking country. The campaign targeted...
-

 103Malware
103MalwareCritical IE and other flaws discovered. Patch your systems now, says Microsoft
If your system administrator looks a little frazzled this week, be nice to him or her and don't grumble too much about...
-

 96Cyber Crime
96Cyber CrimePersonal email and cloud storage pose ‘biggest threat’ to corporate data, report claims
Nearly two-thirds of employees - 63% - use personal email to transfer work files, potentially leaving workplaces exposed to hacks against their...
-

 79Cyber Crime
79Cyber CrimeWorldwide cost of identity theft could be $5 billion per year, Microsoft survey finds
A Microsoft survey of 10,000 consumers found that the worldwide annual cost of identity theft and phishing could be as high as...
-

 367Cyber Crime
367Cyber CrimeHalf of children left exposed to online threats as parents fail to use built‑in controls
Less than half of parents use parental controls on internet-enabled devices bought for their children - leaving millions of youngsters potentially exposed...
-

 339Windows
339WindowsWindows exploitation in 2013
The year 2013 was notable for the appearance of 0-day vulnerabilities that were primarily used in targeted attacks. In this case, criminal...
-
 205Cyber Events
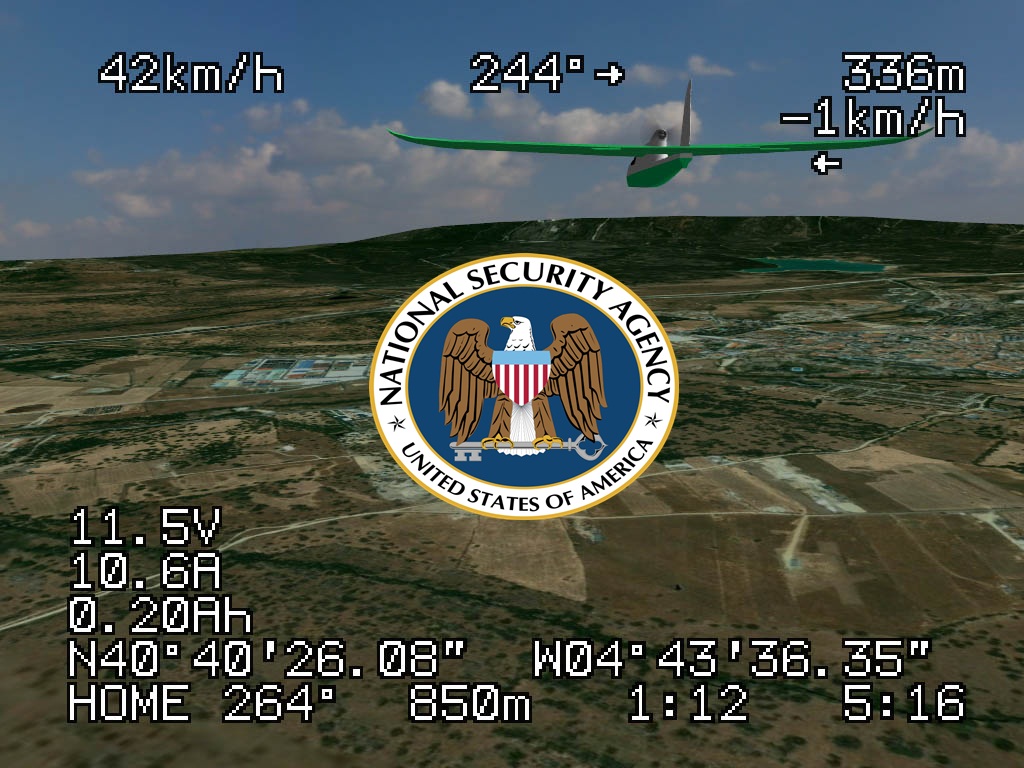
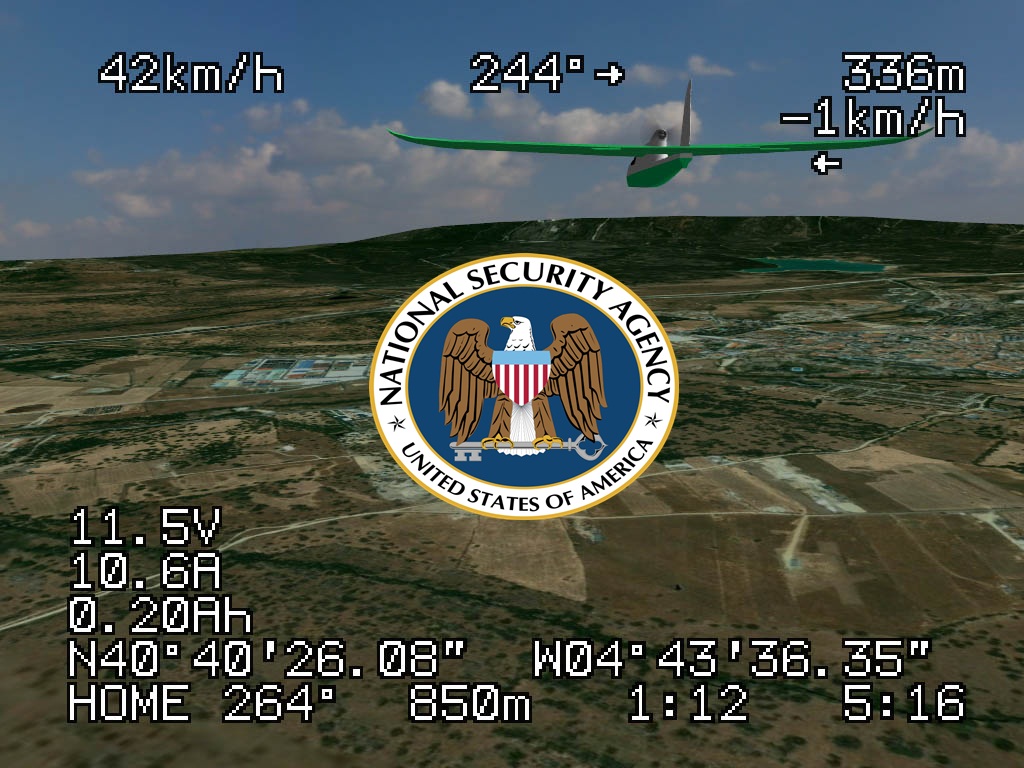
205Cyber EventsAnonymous Whistleblower reveals U.S. uses unreliable NSA cell phone location data to drone civilians.
USA identifies its drone targets based on NSA metadata, a flawed tactic, according to reports published in the Intercept. A former NSA...
-

 386Malware
386MalwareCorkow – the lesser‑known Bitcoin‑curious cousin of the Russian banking Trojan family
A little-known banking trojan, developed in Russia, has managed to infect thousands of victims' computers without the knowledge of their owners. Graham...
-

 557How To
557How ToTwo‑factor authentication: What is it – and why do I need it?
Over the past two years, many online services have started to offer ‘two-factor authentication’ - an extra security measure which often requires...
-

 461Password
461PasswordMicrosoft boosts security for Office 365 users with two‑factor logins
Microsoft’s online Office 365 service has added a new layer of protection to users of the online document-editing service, with two-factor authentication...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




