Featured News
-

 119Malware
119MalwareMicrosoft Word users urged to apply urgent fix after targeted attacks
Microsoft Word users have been urged to update their software after attacks against users of MS Word 2010, where opening a “specially...
-
 137Privacy
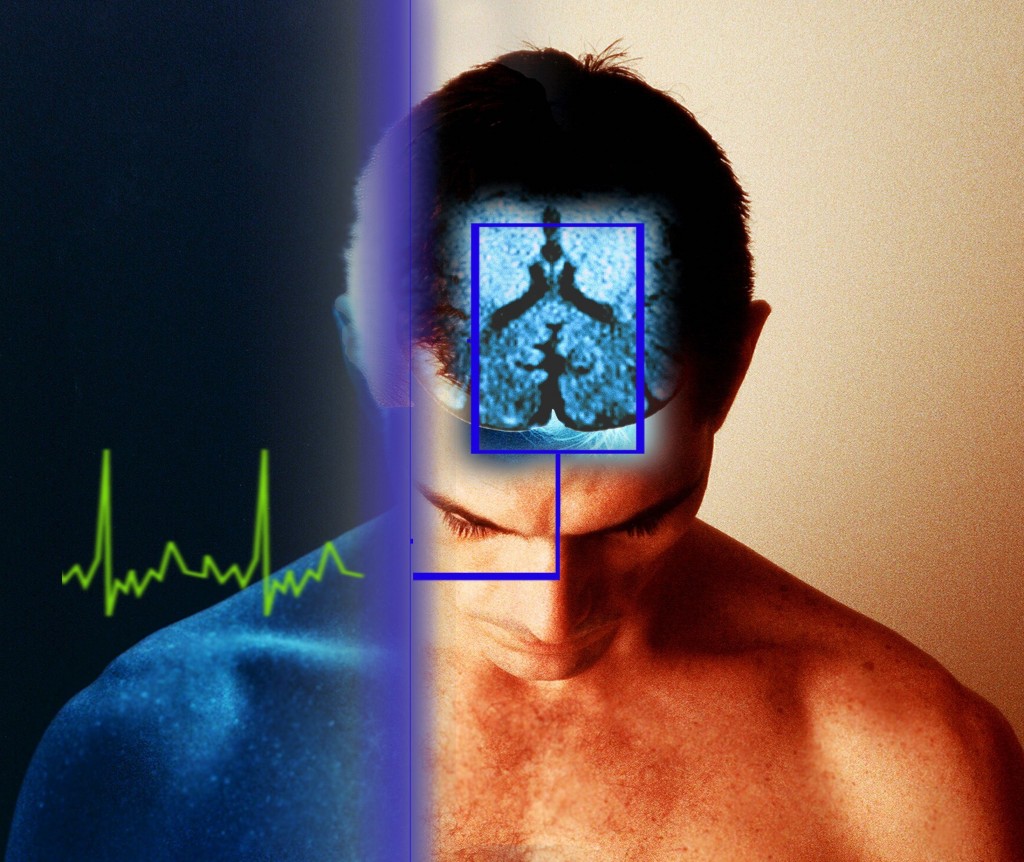
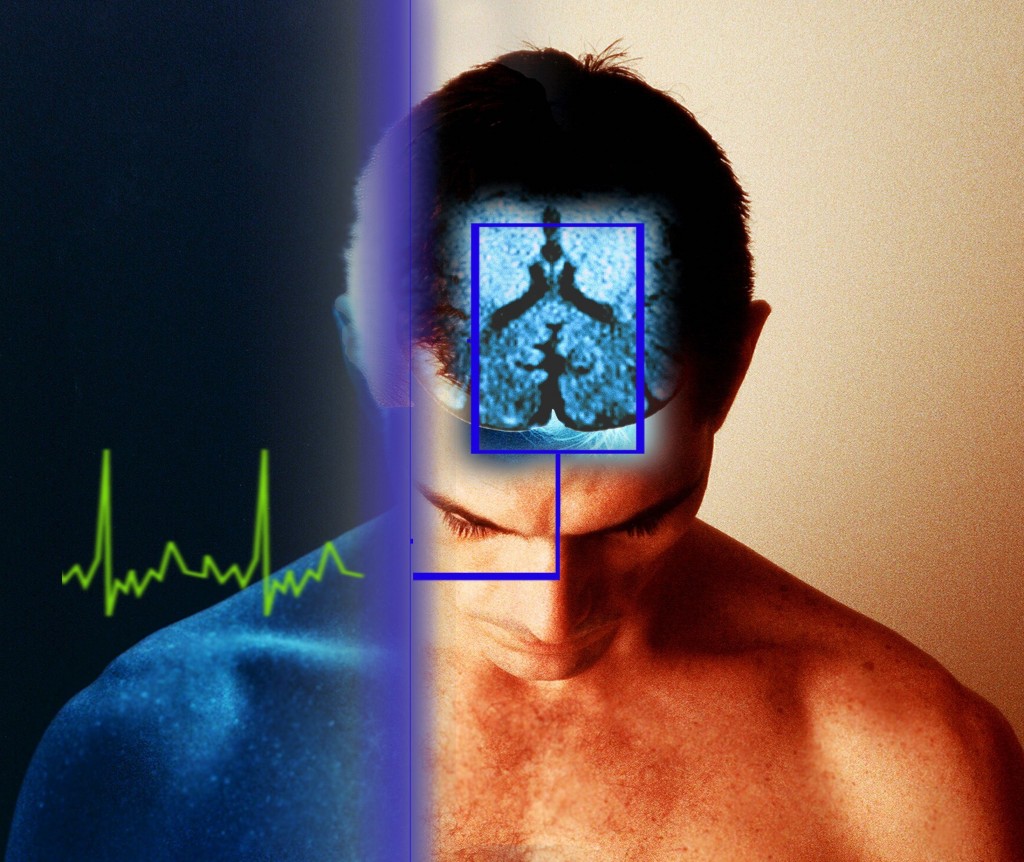
137PrivacyBrainwave privacy standard “is needed” to prevent spying on EEG scan data, researchers warn
Smartphone apps and home equipment for scanning brainwaves could lead to a future in which governments or companies misuse such data as...
-

 406Data Security
406Data SecuritySnowden Leaks: NSA Posed as Facebook to infect computers with malware
According to one of the recent report, NSA is believed to be spying many Facebook users since 2010. NSA used a number...
-

 194Cyber Crime
194Cyber CrimeFake video of Malaysia Airlines flight MH370 rescue is ‘callous’ cyber scam
A post promising a video of a plane landing on water has been circulating on Facebook, with a title suggesting that it...
-

 117Scams
117ScamsMore Mystery Shopper Misery
'Highly-paid' mystery shopper assignments where you're sent cashier's checks upfront can end up costing you a lot of money.
-

 220Android
220AndroidHidden backdoor in top Samsung Galaxy models ‘allows remote spying on users’
A hidden backdoor in the modified version of Android run by nine Samsung Galaxy models could allow attackers to spy remotely on...
-

 120Surveillance
120SurveillanceSnowden at SXSW Conference: They’re “setting fire to the future of the Internet”
Edward Snowden, the NSA whistleblower made his longest public appearance at the SXSW conference since his surveillance act. This was done through...
-

 324Cyber Crime
324Cyber CrimeRomanian Man Kills 4 Year Old Son, commits Suicide After Police Ransomware Tells Him He Must Pay Fine
A man from Romania has committed suicide after his computer got infected with “police ransomware,” according to a local media report. Police...
-

 399Password
399PasswordTop e‑commerce sites still fail to warn users who choose “password”
Two-thirds of top e-commerce sites still accept the weakest passwords, such as “123456” and “password” without warning users that these are the...
-

 87Cyber Crime
87Cyber CrimeFridge attacks “raise big questions” says Microsoft security chief
The emerging ‘internet of things’ raises big security questions, and vulnerabilities in connected devices such as ‘smart’ fridges may force companies to...
-
 251News
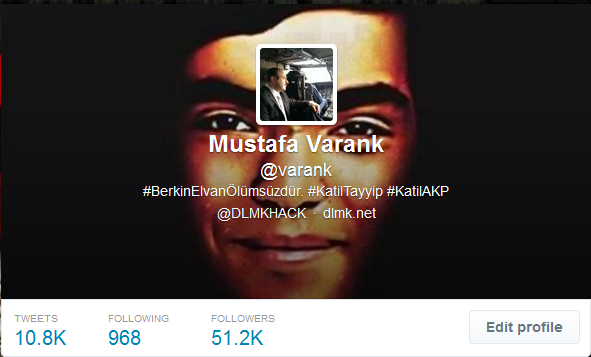
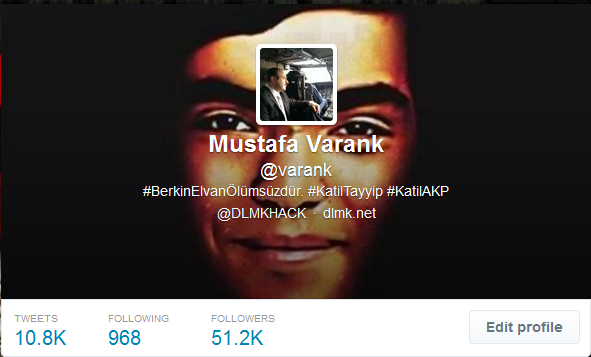
251NewsTwitter account of Turkish PM’s top adviser hacked, messages left against Berkin Elvan’s death
A group of Turkish hackers have hacked the official Twitter account of Mustafa Varank, who is a top political advisers of Prime...
-
 480Malware
480MalwareCritical Internet Explorer zero‑day vulnerability patched by Microsoft
Microsoft releases a fix for a zero-day vulnerability that has already been exploited by hackers in targeted attacks against some organisations. Don't...
-

 304Surveillance
304SurveillanceApp Controlled Drone That Will Shoot You With an 80,000 Volt Taser (Video Added)
A tech-firm has amazed the world with its proof-of-demonstration of a remote-controlled “stun copter” that can deliver 80,000 volts of electricity to...
-

 379Password
379PasswordSmartphones with fingerprint‑scanning screens ‘on sale by summer’
Smartphones such as iPhone 5S rely on buttons to scan fingerprints - but the CEO of biometrics firm CrucialTec says that smartphones...
-

 87Cyber Crime
87Cyber CrimeGoogle Glass app offers new level of security for ATM users
A futuristic app uses Google Glass to add an extra layer of privacy for users withdrawing cash from ATM machines - by...
-

 204Geek
204GeekBoeing to release self destructing black phone to aid spies and diplomats
Boeing is set to launch a self-destructing smartphone that would aid the spies, diplomats and others keep their data secure, according to...
-

 88Cyber Crime
88Cyber CrimeFinancial files from Mt Gox supposedly ‘leak online’ after CEO targeted
A file of material purporting to include detailed information on trades at the Bitcoin exchange Mt Gox, has surfaced online, after attackers...
-

 139Scams
139ScamsThe Billgate Foundation – the fall for money, eh many…
Recently it was announced that Satya Nadella will be Steve Ballmer’s successor as CEO of Microsoft. Of course for the cybercriminals this...
-

 276Scams
276ScamsFive ‘new friends’ to avoid like the plague on social networks
Befriending the wrong person on Facebook can hand a criminal the tools for an identity theft attack - and on LinkedIn, talking...
-
 235Cyber Crime
235Cyber CrimeJustin Bieber is the latest celebrity to have his Twitter account hacked
Maybe it's time to think twice before rushing to click on a link, next time your favourite celebrity says something bizarre on...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




