Featured News
-
 125How To
125How ToSmells phishy? New email scams – and why smartphone users need to stay alert
Phishing is unique among cyber attacks - it doesn’t rely on weaknesses in computer software, or new vulnerabilities - it relies, initially...
-

 252News
252NewsAnonymous Declares Cyberwar on Countries Found Disturbing Peace in Ukraine
The online Anonymous Hacktivist has released a video message in which it has declared cyberwar on countries and organizations, posing a threat...
-

 204News
204NewsHackers Threaten Massive Cyber Attack on Brazil Fifa World Cup
SAO PAULO — Brazilian hackers are threatening to disrupt the World Cup with attacks ranging from jamming websites to data theft, adding...
-

 500Android
500AndroidBoeing unveils encrypted ‘Black’ spy phone which self‑destructs when tampered with
Boeing has unveiled a smartphone fit for James Bond - the Boeing Black, which can connect to satellites and secret government telecoms...
-

 366Malware
366MalwareWi‑Fi virus Chameleon infects whole cities ‘like airborne disease’
A virus designed to infect Wi-Fi networks can spread through cities “as efficiently as the common cold spreads between humans”, researchers at...
-

 506Cyber Crime
506Cyber CrimeCorkow: Analysis of a business‑oriented banking Trojan
Win32/Corkow is banking malware with a focus on corporate banking users. We can confirm that several thousand users, mostly in Russia and...
-

 66Cyber Crime
66Cyber CrimeMark Brooks: How to spot an online dating scammer – and why it’s getting tougher
Mark Brooks of OnlinePersonalsWatch works with many online dating sites - and says that all of them are plagued by fake profiles,...
-

 424Cyber Crime
424Cyber CrimeMastercard trials fraud‑busting GPS app to end misery of blocked payments on vacation
Mastercard is piloting a scheme where smartphone GPS systems are used to authenticate purchases for travellers - which could spell an end...
-

 84Malware
84MalwareMac malware spread disguised as cracked versions of Angry Birds, Pixelmator and other top apps
Pirated versions of popular Mac apps, spread via torrent sites, try to infect your computer with malware... and steal Bitcoins.
-

 370Cyber Crime
370Cyber CrimeU.S. businesses boost cyber defenses as they brace for more Target‑style attacks
Businesses in America have increased security spending after the wave of high-profile cyber attacks late last year, including the Target breach -...
-

 207Mobile Security
207Mobile SecurityBlackBerry security revisited: How do the BB10’s stack up?
Following the ground up overhaul of the BlackBerry operating system and accompanying launch of their new flagship smartphones last year, we wondered...
-

 389Malware
389MalwareBritish Airways e‑ticket malware attack launched via email
If you have received an unexpected email, claiming to come from British Airways, about an upcoming flight that you haven’t booked –...
-

 67Cyber Crime
67Cyber CrimeMt Gox exchange ‘disappears’ amid rumors of $350m Bitcoin heist – biggest in history
Trading has been suspended on the Bitcoin exchange Mt Gox and its website has closed, amid rumors that the exchange has lost...
-

 325News
325NewsOfficial websites of WWF and Earth Hour Philippines Hacked by Indonesian hackers
The official websites of World Wildlife Fund (WWF) and Earth Hour Philippines have been hacked and defaced by Indonesian based hacking group Gantengers Crew. Hackers...
-

 376Malware
376MalwareAttack ‘bypasses’ Microsoft’s zero‑day protection tool
Researchers have demonstrated an attack that completely bypasses the protections offered by EMET - a Microsoft toolkit used to provide safeguards against...
-

 91Password
91PasswordSamsung Galaxy S5 offers fingerprint security for safe shopping with PayPal
Samsung has introduced fingerprint-scanning security as standard into its new flagship Galaxy S5 handset - with Finger Scanner offering secure shopping via...
-

 101Password
101PasswordThe perils of passwords – and how to avoid them
There are lots of ways that hackers can steal your passwords, and use them against you. So what can you do to...
-
 222News
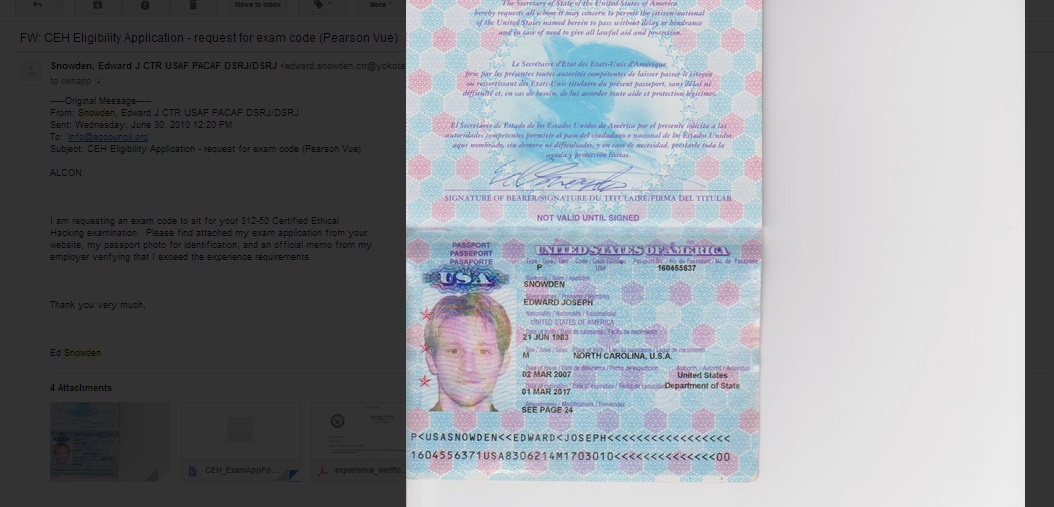
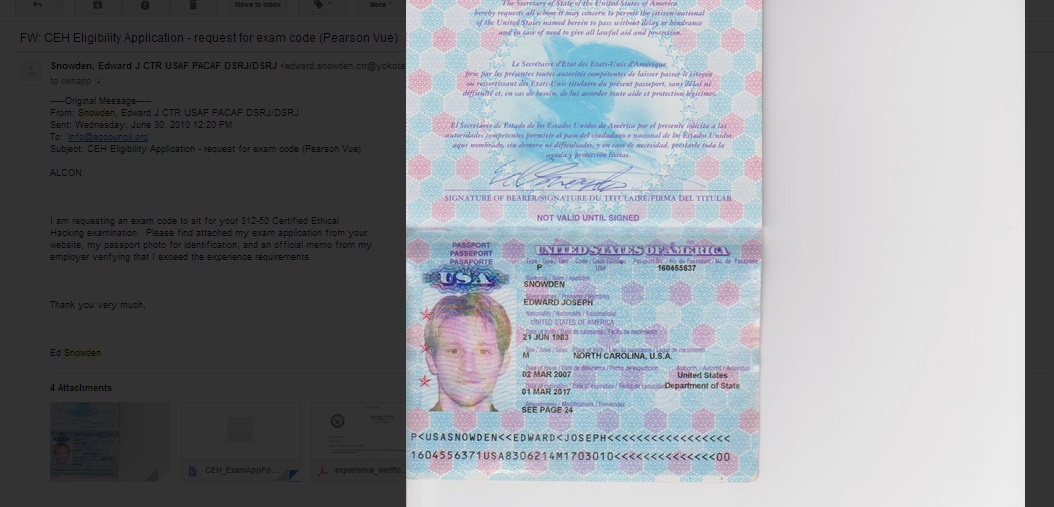
222NewsEthical Hacking Organization Website Hacked, Defaced with Snowden’ Passport
Screenshot of the deface page left by the hackers EC- Council Website of the Security Certification Group got defaced with passport of...
-

 444Cyber Crime
444Cyber CrimeMost small‑office routers have ‘critical’ vulnerabilities as mysterious ‘Moon’ worm spreads
A large majority of routers used in small offices are plagued with security vulnerabilities - with up to 80% of small office/home...
-

 70Cyber Crime
70Cyber CrimeNeiman Marcus attackers set off 60,000 alerts – but went unnoticed
Hackers who stole hundreds of thousands of card details from upscale retailer Neiman Marcus set off more than 60,000 security alerts -...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




