Featured News
-

 70Cyber Crime
70Cyber CrimeMt Gox site code “posted online” as exchange admits $500m in bitcoin is lost
Bitcoin exchange Mt Gox has admitted that nearly $500 million in bitcoin has “disappeared”, in a new statement posted online - as...
-

 162Scams
162ScamsNetflix phish, tech support scam, same phrying pan
Yet another innovative tech support scam, using Netflix phishing to get remote access to the victim's system.
-

 106Scams
106ScamsCisco offers $300,000 for “visionary” solutions to defend ‘Internet of Things’
Networking giant Cisco has launched a “grand challenge” to invent a security solution for the “internet of things” - a broad term...
-

 215News
215NewsLargest Data Hack in the history! 360mn stolen account credentials found online
It has been reported by a cyber-security firm that huge number of credentials in the form of a cache are being presented...
-
 182News
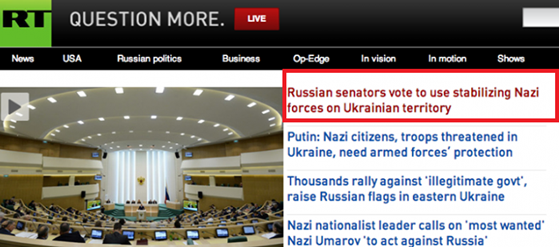
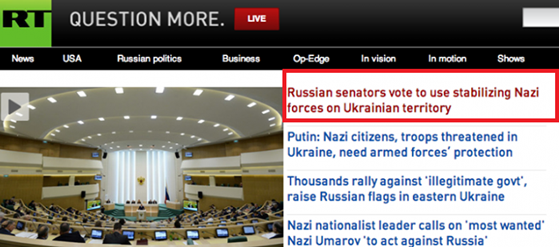
182NewsRussia Today (RT) website hacked, Headline Edited with the word ‘’Nazi’’
Russia Today (RT) website was hacked, Headline Edited with the world ‘’Nazi’’over ongoing Ukrainian unrest. The Russian based news channel RT got...
-
 101Cyber Crime
101Cyber CrimeArrested Anonymous Hacker will serve 12 years in prison for hacking the Federal Reserve
A British individual has been accused of cracking into the servers of the Federal Reserves of U.S, and for stealing and online...
-

 396Cyber Crime
396Cyber CrimeCIA chief says internet‑connected appliances are ‘worrisome’ new threat
CIA Director John Brennan says that connected appliances and networked vehicles will make the agency’s job harder - with more systems to...
-
 126How To
126How ToSmells phishy? New email scams – and why smartphone users need to stay alert
Phishing is unique among cyber attacks - it doesn’t rely on weaknesses in computer software, or new vulnerabilities - it relies, initially...
-

 252News
252NewsAnonymous Declares Cyberwar on Countries Found Disturbing Peace in Ukraine
The online Anonymous Hacktivist has released a video message in which it has declared cyberwar on countries and organizations, posing a threat...
-

 204News
204NewsHackers Threaten Massive Cyber Attack on Brazil Fifa World Cup
SAO PAULO — Brazilian hackers are threatening to disrupt the World Cup with attacks ranging from jamming websites to data theft, adding...
-

 501Android
501AndroidBoeing unveils encrypted ‘Black’ spy phone which self‑destructs when tampered with
Boeing has unveiled a smartphone fit for James Bond - the Boeing Black, which can connect to satellites and secret government telecoms...
-

 366Malware
366MalwareWi‑Fi virus Chameleon infects whole cities ‘like airborne disease’
A virus designed to infect Wi-Fi networks can spread through cities “as efficiently as the common cold spreads between humans”, researchers at...
-

 506Cyber Crime
506Cyber CrimeCorkow: Analysis of a business‑oriented banking Trojan
Win32/Corkow is banking malware with a focus on corporate banking users. We can confirm that several thousand users, mostly in Russia and...
-

 66Cyber Crime
66Cyber CrimeMark Brooks: How to spot an online dating scammer – and why it’s getting tougher
Mark Brooks of OnlinePersonalsWatch works with many online dating sites - and says that all of them are plagued by fake profiles,...
-

 425Cyber Crime
425Cyber CrimeMastercard trials fraud‑busting GPS app to end misery of blocked payments on vacation
Mastercard is piloting a scheme where smartphone GPS systems are used to authenticate purchases for travellers - which could spell an end...
-

 84Malware
84MalwareMac malware spread disguised as cracked versions of Angry Birds, Pixelmator and other top apps
Pirated versions of popular Mac apps, spread via torrent sites, try to infect your computer with malware... and steal Bitcoins.
-

 371Cyber Crime
371Cyber CrimeU.S. businesses boost cyber defenses as they brace for more Target‑style attacks
Businesses in America have increased security spending after the wave of high-profile cyber attacks late last year, including the Target breach -...
-

 209Mobile Security
209Mobile SecurityBlackBerry security revisited: How do the BB10’s stack up?
Following the ground up overhaul of the BlackBerry operating system and accompanying launch of their new flagship smartphones last year, we wondered...
-

 389Malware
389MalwareBritish Airways e‑ticket malware attack launched via email
If you have received an unexpected email, claiming to come from British Airways, about an upcoming flight that you haven’t booked –...
-

 67Cyber Crime
67Cyber CrimeMt Gox exchange ‘disappears’ amid rumors of $350m Bitcoin heist – biggest in history
Trading has been suspended on the Bitcoin exchange Mt Gox and its website has closed, amid rumors that the exchange has lost...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




