Featured News
-

 205Mobile Security
205Mobile SecurityBlackBerry security revisited: How do the BB10’s stack up?
Following the ground up overhaul of the BlackBerry operating system and accompanying launch of their new flagship smartphones last year, we wondered...
-

 386Malware
386MalwareBritish Airways e‑ticket malware attack launched via email
If you have received an unexpected email, claiming to come from British Airways, about an upcoming flight that you haven’t booked –...
-

 66Cyber Crime
66Cyber CrimeMt Gox exchange ‘disappears’ amid rumors of $350m Bitcoin heist – biggest in history
Trading has been suspended on the Bitcoin exchange Mt Gox and its website has closed, amid rumors that the exchange has lost...
-

 323News
323NewsOfficial websites of WWF and Earth Hour Philippines Hacked by Indonesian hackers
The official websites of World Wildlife Fund (WWF) and Earth Hour Philippines have been hacked and defaced by Indonesian based hacking group Gantengers Crew. Hackers...
-

 374Malware
374MalwareAttack ‘bypasses’ Microsoft’s zero‑day protection tool
Researchers have demonstrated an attack that completely bypasses the protections offered by EMET - a Microsoft toolkit used to provide safeguards against...
-

 90Password
90PasswordSamsung Galaxy S5 offers fingerprint security for safe shopping with PayPal
Samsung has introduced fingerprint-scanning security as standard into its new flagship Galaxy S5 handset - with Finger Scanner offering secure shopping via...
-

 99Password
99PasswordThe perils of passwords – and how to avoid them
There are lots of ways that hackers can steal your passwords, and use them against you. So what can you do to...
-
 219News
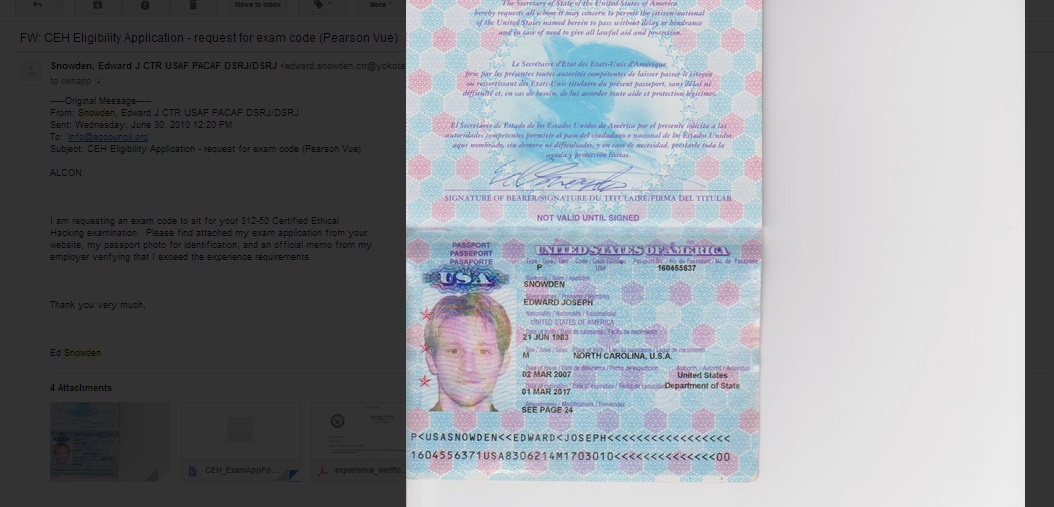
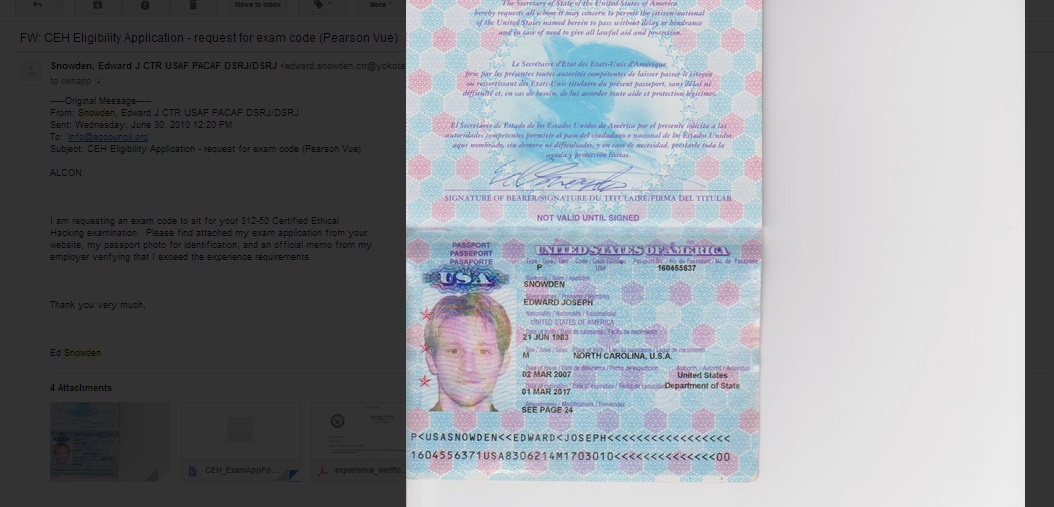
219NewsEthical Hacking Organization Website Hacked, Defaced with Snowden’ Passport
Screenshot of the deface page left by the hackers EC- Council Website of the Security Certification Group got defaced with passport of...
-

 442Cyber Crime
442Cyber CrimeMost small‑office routers have ‘critical’ vulnerabilities as mysterious ‘Moon’ worm spreads
A large majority of routers used in small offices are plagued with security vulnerabilities - with up to 80% of small office/home...
-

 69Cyber Crime
69Cyber CrimeNeiman Marcus attackers set off 60,000 alerts – but went unnoticed
Hackers who stole hundreds of thousands of card details from upscale retailer Neiman Marcus set off more than 60,000 security alerts -...
-

 308Cyber Crime
308Cyber CrimeSouth Korea will develop Stuxnet-like cyberweapons to destroy North Korean nuclear facilities
In order to demolish North Korean nuclear facilities, South Korea has decided to develop its own cyber attack tools. Stuxnet kind of weapons have...
-

 441Malware
441MalwareAn In‑depth Analysis of Linux/Ebury
In this blog post, we provide an in-depth analysis of Linux/Ebury - the most sophisticated Linux backdoor ever seen by our researchers....
-

 276News
276NewsUniversity of Maryland Hacked, Personal Information of 300,000 Staff and Students Stolen
More than 300,000 records of faculty, staff, students, and affiliates of the Maryland University were breached, according to the University’s president. In...
-
 216Scams
216ScamsScams: Tech Support, Accident Insurance, PPI, Oh My My
It's not just fake tech support: call centre cold-callers are operating various kinds of insurance scams, too.
-

 186Cyber Crime
186Cyber CrimeTinder dating app gave away exact locations of users for months
Smartphone dating app Tinder revealed more about its users than they might have wished over a period of several months last year...
-

 213Privacy
213PrivacyHow can doctors practice better health information security?
Did you know that medical data on 20,000 people may be exposed to abuse today? As a healthcare practitioner, you may not...
-

 102Malware
102MalwareQR codes pose hidden danger to smartphone users, researchers claim
The increasing use of QR codes as a way to add interactive elements, apps and websites to display advertising, competitions or print...
-

 270News
270NewsSyrian Electronic Army Hacks Official Twitter Accounts of FC Barcelona
Syrian Electronic Army, the pro- Bashar Al Assad Syrian hackers, hacked the official twitter accounts of Futbol Club Barcelona (FC Barcelona) and sent...
-

 77Cyber Crime
77Cyber CrimeBelkin’s ‘Smart Home’ system has security flaws which could ‘black out’ homes – or start fires
Belkin’s WeMo home automation systems contain multiple vulnerabilities which could allow attackers to remotely control devices attached to a WeMo system -...
-

 239News
239NewsNational Portal of India Hacked by Z Company Hacking Crew in Support of Kashmir
The online hacktivists from Z Company Hacking Crew (ZHC) have hacked two official domains of National portal of India and left messages against Indian...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




