Featured News
-

 340Windows
340WindowsWindows exploitation in 2013
The year 2013 was notable for the appearance of 0-day vulnerabilities that were primarily used in targeted attacks. In this case, criminal...
-
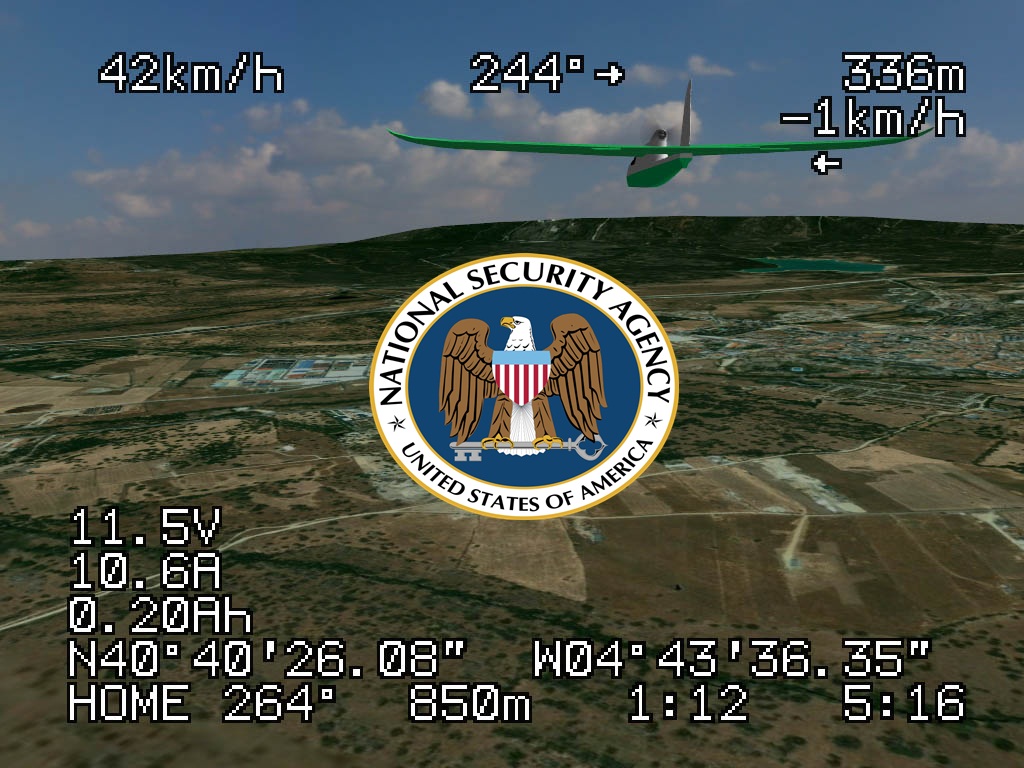
 205Cyber Events
205Cyber EventsAnonymous Whistleblower reveals U.S. uses unreliable NSA cell phone location data to drone civilians.
USA identifies its drone targets based on NSA metadata, a flawed tactic, according to reports published in the Intercept. A former NSA...
-

 386Malware
386MalwareCorkow – the lesser‑known Bitcoin‑curious cousin of the Russian banking Trojan family
A little-known banking trojan, developed in Russia, has managed to infect thousands of victims' computers without the knowledge of their owners. Graham...
-

 559How To
559How ToTwo‑factor authentication: What is it – and why do I need it?
Over the past two years, many online services have started to offer ‘two-factor authentication’ - an extra security measure which often requires...
-

 463Password
463PasswordMicrosoft boosts security for Office 365 users with two‑factor logins
Microsoft’s online Office 365 service has added a new layer of protection to users of the online document-editing service, with two-factor authentication...
-

 200Data Security
200Data SecurityVulnerability that lets hackers hack Snapchat and disable your iPhone
Snapchat app vulnerability is highlighted again, and this time the hackers can temporarily freeze your iPhone and force restart, according to media...
-
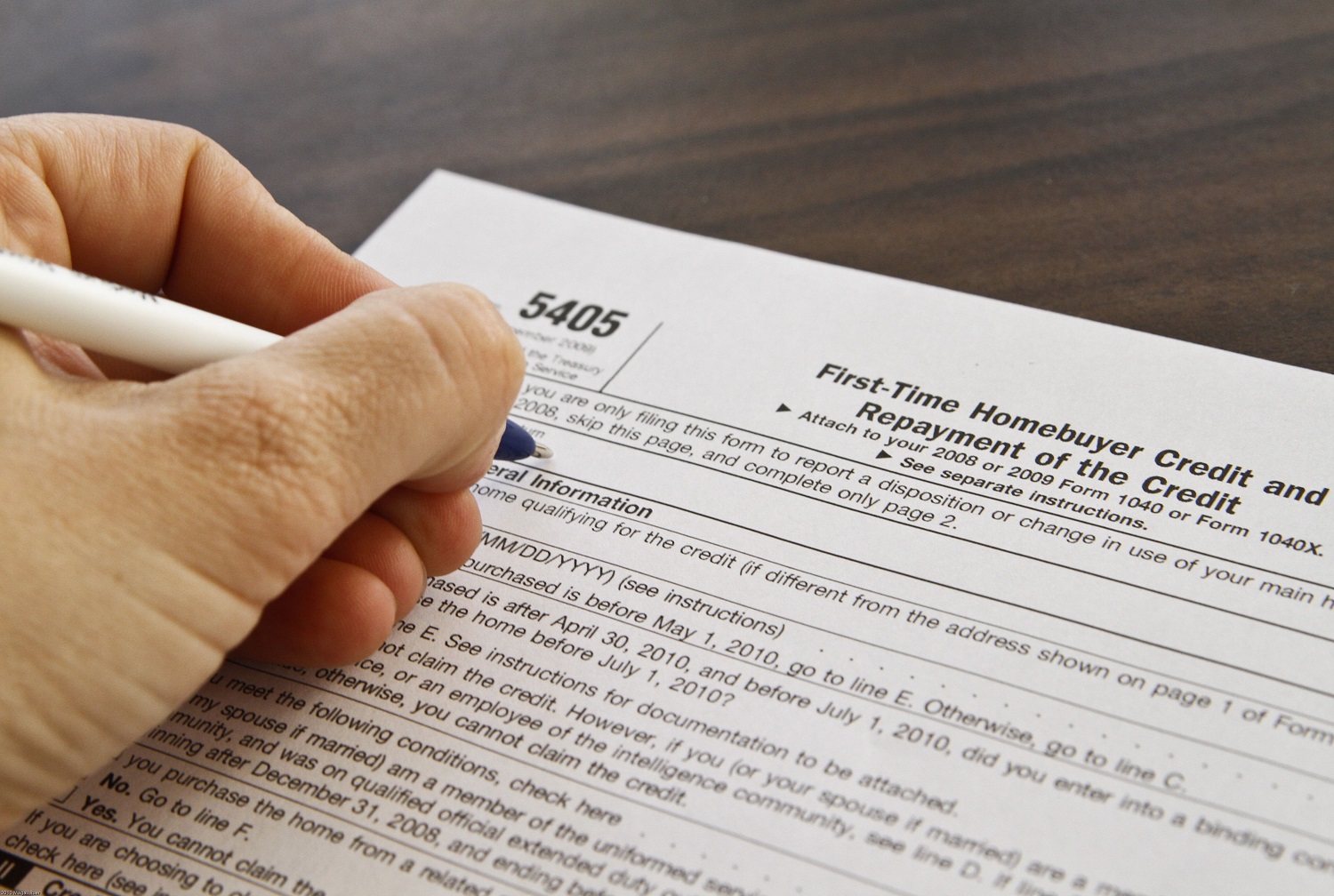
 75Cyber Crime
75Cyber CrimePhishy business: Surge in tax scams as emails rise by nearly 50% in one year
Fraudulent emails offering refunds of overpaid tax have surged by nearly 50% in the past year, according to a report by Accountancy...
-

 180News
180NewsAnother target for Hackers: A small device that can hack a car! (Video Added)
This small sized device could hack a car, let’s see how the researchers demonstrate. Auto makers over the years have paid less...
-

 204Cyber Crime
204Cyber CrimeAmerican law firm admits entire server of legal files fell victim to Cryptolocker
A small American law firm has admitted that every document on a server at the North Carolina company has fallen prey to...
-

 81Cyber Crime
81Cyber CrimeFacebook’s ‘A Look Back’ video used as bait for malware, report claims
A fake version of Facebook’s 10th anniversary celebration video page, ‘A Look Back’ is spreading via the social network, with users directed...
-

 104Scams
104ScamsWangiri Telephone Fraud – One Ring to Scam Them All
Missed a phone call? The Better Business Bureau says answering international telephone fraud calls looking like US calls might cost you more...
-

 251News
251NewsDubai Police Official Twitter, LinkedIn and Pinterest accounts Hacked by Anonymous
An Anonymous hacker going with the handle of @TheHorsemenLulz has hacked 4 official Social Media accounts of UAE‘s Dubai Police. The hacked accounts include LinkedIn,...
-

 233Cyber Events
233Cyber EventsSnowden used a cheap software to gather secret NSA files
Edward Snowden, the American whistleblower, used a very simple ‘Web crawler’ to collect controversial NSA data, according to a senior intelligence official...
-

 167Data Security
167Data SecurityHow to Prevent Your Website from Authentication Hacking Attack? (In Depth Analysis)
Websites though being secured remains at a risk of getting attacked in one or the other way. Internet is coming up with...
-

 188News
188NewsThe President of Nepal has his official website hacked by Iranian hackers
An Iranian hacker going with the handle of Dr.3v1l has hacked and defaced the official website of President of Nepal. Screenshot of the...
-

 74Cyber Crime
74Cyber CrimeU.S. hotel firm ‘knew of credit card breach for two weeks’ before going public
Managers at White Lodging, a hotel management firm that works with various brands including Hilton, Marriott, Westin, Sheraton and Hyatt, may have...
-

 177Password
177PasswordSniffing body odor has ‘enormous potential’ for biometrics, researchers claim
Body odor could be used as a biometric identifier, with high rates of accuracy, due to chemical patterns in the smell that...
-

 215Cyber Events
215Cyber EventsRedHack Hactivists Join hands with activists for a protest against Internet Censorship Laws in Turkey
The Turkish parliament has accepted a highly controversial reversal to a cyber law, granting authorities full power to block certain websites in...
-

 232News
232NewsSyrian Electronic Army Targets Facebook, Google, Yahoo via MarkMonitor Hack
The hardcore supporter of Syrian President Bashar Al Assad and the online hacktavist Syrian Electronic Army has made an attempt to hack...
-
 264News
264NewsInternet Minefield: NBC Reporter was immediately hacked in Sochi! Your Phone & Laptop will be hacked as well.
Devices brought to Sochi get apparently hacked within few moments of being connected to a Wi-Fi network, according to NBC Nightly News’...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




