Featured News
-

 153Scams
153ScamsHow cybercriminals ‘market’ email attacks – and why LinkedIn lures are today’s prize phish
Cybercriminals ‘manage’ phishing emails using techniques similar to those used by marketing agencies, including the use of ‘test audiences’ to see how...
-

 170Privacy
170Privacy‘Secure’ web browsing can leak private data to employers and ISPs, researchers warn
University of Berkeley researchers have revealed a technique for identifying individual web pages visited ‘securely’ by users, with up to 89% accuracy,...
-

 251News
251NewsSnowden’s Latest Leak has fake UFO Images: Claims expert
A document among the trove leaked by Edward Snowden contains slides showing images of flying saucer as reported by Yahoo News Following...
-
 330News
330NewsCyberwar Heating Up: Ukraine hit by massive cyber attack from Russia, mobile networks blocked
The telecommunication system of Ukraine has got hit by cyber-attacks through the equipment which have been installed in the Russian-influenced Crimea. These...
-
 158Opinion
158OpinionCourier Scams – don’t give away your bank card
If someone rings you up to tell you that your bank card has been compromised, it may be because they want to...
-

 395Malware
395MalwareAndroid phones and tablets ship “pre‑infected” with malware
Android phones and tablets from four different manufacturers are arriving with malware “pre-installed” - a bogus version of Netflix which sends password...
-

 290News
290NewsMysterious UFO Photos Found in Documents Leaked by Snowden
Ex-NSA tech Snowden leaked documents had yet another element of surprise; it has a set of slides depicting mysterious spacecrafts referring to Flying...
-

 93Cyber Crime
93Cyber CrimeWWF warns of ‘arms race’ with ‘cyberpoachers’ targeting endangered species
Criminals seeking to kill endangered species and sell trophies online are turning to increasingly hi-tech methods to target their prey - including...
-

 72Cyber Crime
72Cyber CrimeBitcoin bank Flexcoin shuts down after attackers loot $570,000 from “hot wallet”
The attackers were able to steal all the bitcoins stored in the bank’s “hot wallet” - the portion of its funds on...
-

 106How To
106How ToHow can we as patients secure our medical data?
When someone says “data privacy” most people think about the information that is available on sites like Google and Facebook, or stored...
-

 101Password
101PasswordDon’t panic! Twitter mass password reset was ‘mistake’ company admits
An emailed warning and enforced password reset sent out to Twitter users on Monday due to a supposed compromise of their accounts...
-
 338Surveillance
338SurveillanceIts not just the NSA! Facebook also collects data: Says White House
It is not just the NSA, the infamous snooping authority of the US, that has been collecting data of millions of Americans,...
-

 98Cyber Crime
98Cyber CrimeMore than 300,000 wireless routers hijacked by criminals in global attack
More than 300,000 wireless routers worldwide are under the control of an unknown group of cybercriminals, who have made malicious changes to...
-

 73Cyber Crime
73Cyber CrimeMt Gox site code “posted online” as exchange admits $500m in bitcoin is lost
Bitcoin exchange Mt Gox has admitted that nearly $500 million in bitcoin has “disappeared”, in a new statement posted online - as...
-

 166Scams
166ScamsNetflix phish, tech support scam, same phrying pan
Yet another innovative tech support scam, using Netflix phishing to get remote access to the victim's system.
-

 109Scams
109ScamsCisco offers $300,000 for “visionary” solutions to defend ‘Internet of Things’
Networking giant Cisco has launched a “grand challenge” to invent a security solution for the “internet of things” - a broad term...
-

 218News
218NewsLargest Data Hack in the history! 360mn stolen account credentials found online
It has been reported by a cyber-security firm that huge number of credentials in the form of a cache are being presented...
-
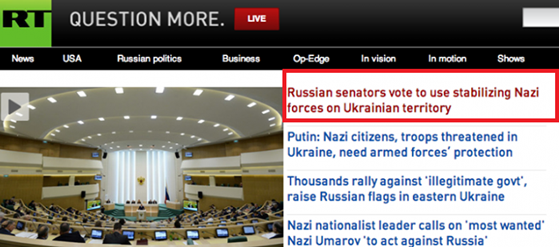
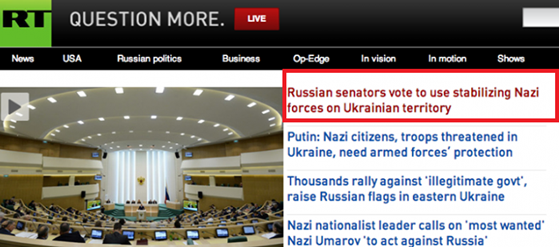 184News
184NewsRussia Today (RT) website hacked, Headline Edited with the word ‘’Nazi’’
Russia Today (RT) website was hacked, Headline Edited with the world ‘’Nazi’’over ongoing Ukrainian unrest. The Russian based news channel RT got...
-
 105Cyber Crime
105Cyber CrimeArrested Anonymous Hacker will serve 12 years in prison for hacking the Federal Reserve
A British individual has been accused of cracking into the servers of the Federal Reserves of U.S, and for stealing and online...
-

 401Cyber Crime
401Cyber CrimeCIA chief says internet‑connected appliances are ‘worrisome’ new threat
CIA Director John Brennan says that connected appliances and networked vehicles will make the agency’s job harder - with more systems to...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




