Featured News
-

 325News
325NewsOfficial websites of WWF and Earth Hour Philippines Hacked by Indonesian hackers
The official websites of World Wildlife Fund (WWF) and Earth Hour Philippines have been hacked and defaced by Indonesian based hacking group Gantengers Crew. Hackers...
-

 376Malware
376MalwareAttack ‘bypasses’ Microsoft’s zero‑day protection tool
Researchers have demonstrated an attack that completely bypasses the protections offered by EMET - a Microsoft toolkit used to provide safeguards against...
-

 91Password
91PasswordSamsung Galaxy S5 offers fingerprint security for safe shopping with PayPal
Samsung has introduced fingerprint-scanning security as standard into its new flagship Galaxy S5 handset - with Finger Scanner offering secure shopping via...
-

 101Password
101PasswordThe perils of passwords – and how to avoid them
There are lots of ways that hackers can steal your passwords, and use them against you. So what can you do to...
-
 222News
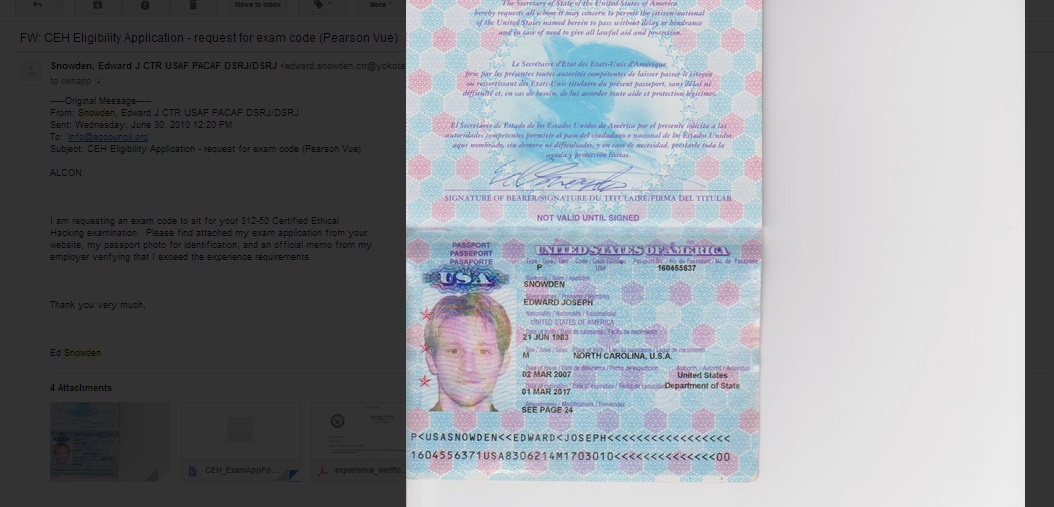
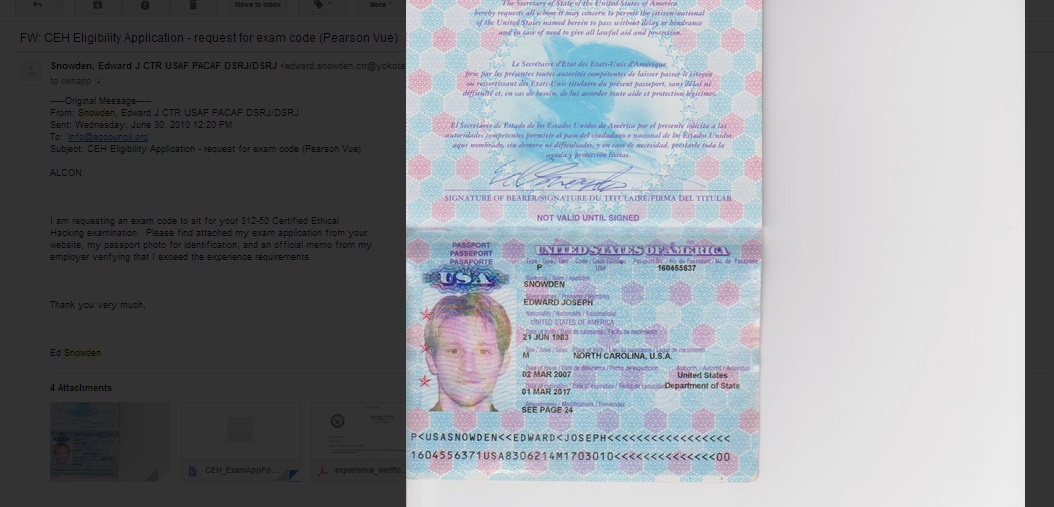
222NewsEthical Hacking Organization Website Hacked, Defaced with Snowden’ Passport
Screenshot of the deface page left by the hackers EC- Council Website of the Security Certification Group got defaced with passport of...
-

 444Cyber Crime
444Cyber CrimeMost small‑office routers have ‘critical’ vulnerabilities as mysterious ‘Moon’ worm spreads
A large majority of routers used in small offices are plagued with security vulnerabilities - with up to 80% of small office/home...
-

 70Cyber Crime
70Cyber CrimeNeiman Marcus attackers set off 60,000 alerts – but went unnoticed
Hackers who stole hundreds of thousands of card details from upscale retailer Neiman Marcus set off more than 60,000 security alerts -...
-

 311Cyber Crime
311Cyber CrimeSouth Korea will develop Stuxnet-like cyberweapons to destroy North Korean nuclear facilities
In order to demolish North Korean nuclear facilities, South Korea has decided to develop its own cyber attack tools. Stuxnet kind of weapons have...
-

 443Malware
443MalwareAn In‑depth Analysis of Linux/Ebury
In this blog post, we provide an in-depth analysis of Linux/Ebury - the most sophisticated Linux backdoor ever seen by our researchers....
-

 278News
278NewsUniversity of Maryland Hacked, Personal Information of 300,000 Staff and Students Stolen
More than 300,000 records of faculty, staff, students, and affiliates of the Maryland University were breached, according to the University’s president. In...
-
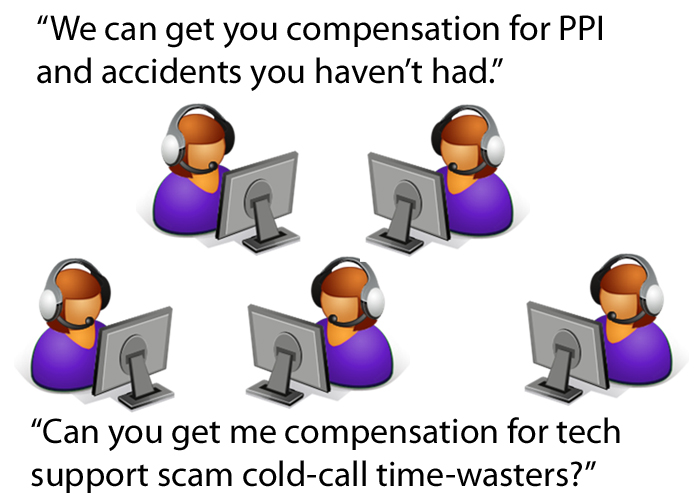
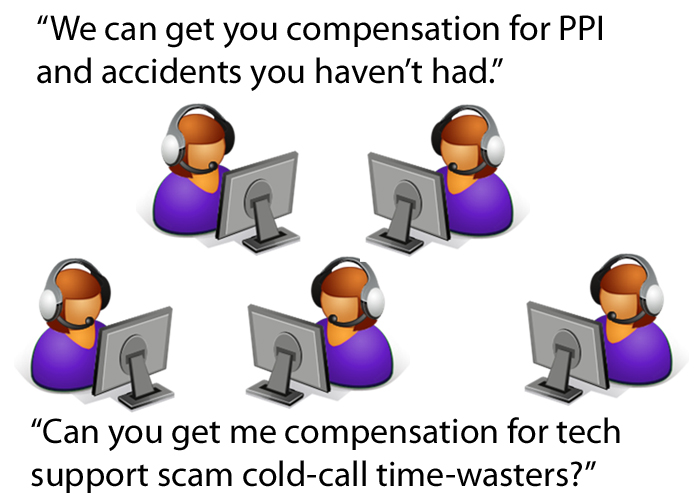 217Scams
217ScamsScams: Tech Support, Accident Insurance, PPI, Oh My My
It's not just fake tech support: call centre cold-callers are operating various kinds of insurance scams, too.
-

 191Cyber Crime
191Cyber CrimeTinder dating app gave away exact locations of users for months
Smartphone dating app Tinder revealed more about its users than they might have wished over a period of several months last year...
-

 215Privacy
215PrivacyHow can doctors practice better health information security?
Did you know that medical data on 20,000 people may be exposed to abuse today? As a healthcare practitioner, you may not...
-

 103Malware
103MalwareQR codes pose hidden danger to smartphone users, researchers claim
The increasing use of QR codes as a way to add interactive elements, apps and websites to display advertising, competitions or print...
-

 272News
272NewsSyrian Electronic Army Hacks Official Twitter Accounts of FC Barcelona
Syrian Electronic Army, the pro- Bashar Al Assad Syrian hackers, hacked the official twitter accounts of Futbol Club Barcelona (FC Barcelona) and sent...
-

 77Cyber Crime
77Cyber CrimeBelkin’s ‘Smart Home’ system has security flaws which could ‘black out’ homes – or start fires
Belkin’s WeMo home automation systems contain multiple vulnerabilities which could allow attackers to remotely control devices attached to a WeMo system -...
-

 241News
241NewsNational Portal of India Hacked by Z Company Hacking Crew in Support of Kashmir
The online hacktivists from Z Company Hacking Crew (ZHC) have hacked two official domains of National portal of India and left messages against Indian...
-

 195News
195NewsHacking of US Navy Computers by Iranian Hackers will Test new NSA Commander Rogers
In 2012, we reported that US NAVY faces 110,000 cyber attacks every hour. Now a report has gone viral that Iran’s penetration into...
-

 318News
318NewsSilk Road 2.0 Hacked: $2.5 million in Bitcoins Stolen! Administrator makes an emotional appeal
An emotional appeal posted on the dark market’s official forum clearly stated that “We have been hacked” and nearly $2.4 to $2.7...
-
 453Password
453PasswordGoogle buys firm with password‑busting “silent sound” authentication system
Google has bought a company offering a new form of two-factor authentication - using “silent” sounds played via PC and smartphone speakers...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




