Featured News
-
 129How To
129How ToSmells phishy? New email scams – and why smartphone users need to stay alert
Phishing is unique among cyber attacks - it doesn’t rely on weaknesses in computer software, or new vulnerabilities - it relies, initially...
-

 256News
256NewsAnonymous Declares Cyberwar on Countries Found Disturbing Peace in Ukraine
The online Anonymous Hacktivist has released a video message in which it has declared cyberwar on countries and organizations, posing a threat...
-

 207News
207NewsHackers Threaten Massive Cyber Attack on Brazil Fifa World Cup
SAO PAULO — Brazilian hackers are threatening to disrupt the World Cup with attacks ranging from jamming websites to data theft, adding...
-

 505Android
505AndroidBoeing unveils encrypted ‘Black’ spy phone which self‑destructs when tampered with
Boeing has unveiled a smartphone fit for James Bond - the Boeing Black, which can connect to satellites and secret government telecoms...
-

 370Malware
370MalwareWi‑Fi virus Chameleon infects whole cities ‘like airborne disease’
A virus designed to infect Wi-Fi networks can spread through cities “as efficiently as the common cold spreads between humans”, researchers at...
-

 510Cyber Crime
510Cyber CrimeCorkow: Analysis of a business‑oriented banking Trojan
Win32/Corkow is banking malware with a focus on corporate banking users. We can confirm that several thousand users, mostly in Russia and...
-

 70Cyber Crime
70Cyber CrimeMark Brooks: How to spot an online dating scammer – and why it’s getting tougher
Mark Brooks of OnlinePersonalsWatch works with many online dating sites - and says that all of them are plagued by fake profiles,...
-

 430Cyber Crime
430Cyber CrimeMastercard trials fraud‑busting GPS app to end misery of blocked payments on vacation
Mastercard is piloting a scheme where smartphone GPS systems are used to authenticate purchases for travellers - which could spell an end...
-

 89Malware
89MalwareMac malware spread disguised as cracked versions of Angry Birds, Pixelmator and other top apps
Pirated versions of popular Mac apps, spread via torrent sites, try to infect your computer with malware... and steal Bitcoins.
-

 376Cyber Crime
376Cyber CrimeU.S. businesses boost cyber defenses as they brace for more Target‑style attacks
Businesses in America have increased security spending after the wave of high-profile cyber attacks late last year, including the Target breach -...
-

 211Mobile Security
211Mobile SecurityBlackBerry security revisited: How do the BB10’s stack up?
Following the ground up overhaul of the BlackBerry operating system and accompanying launch of their new flagship smartphones last year, we wondered...
-

 397Malware
397MalwareBritish Airways e‑ticket malware attack launched via email
If you have received an unexpected email, claiming to come from British Airways, about an upcoming flight that you haven’t booked –...
-

 70Cyber Crime
70Cyber CrimeMt Gox exchange ‘disappears’ amid rumors of $350m Bitcoin heist – biggest in history
Trading has been suspended on the Bitcoin exchange Mt Gox and its website has closed, amid rumors that the exchange has lost...
-

 330News
330NewsOfficial websites of WWF and Earth Hour Philippines Hacked by Indonesian hackers
The official websites of World Wildlife Fund (WWF) and Earth Hour Philippines have been hacked and defaced by Indonesian based hacking group Gantengers Crew. Hackers...
-

 379Malware
379MalwareAttack ‘bypasses’ Microsoft’s zero‑day protection tool
Researchers have demonstrated an attack that completely bypasses the protections offered by EMET - a Microsoft toolkit used to provide safeguards against...
-

 95Password
95PasswordSamsung Galaxy S5 offers fingerprint security for safe shopping with PayPal
Samsung has introduced fingerprint-scanning security as standard into its new flagship Galaxy S5 handset - with Finger Scanner offering secure shopping via...
-

 104Password
104PasswordThe perils of passwords – and how to avoid them
There are lots of ways that hackers can steal your passwords, and use them against you. So what can you do to...
-
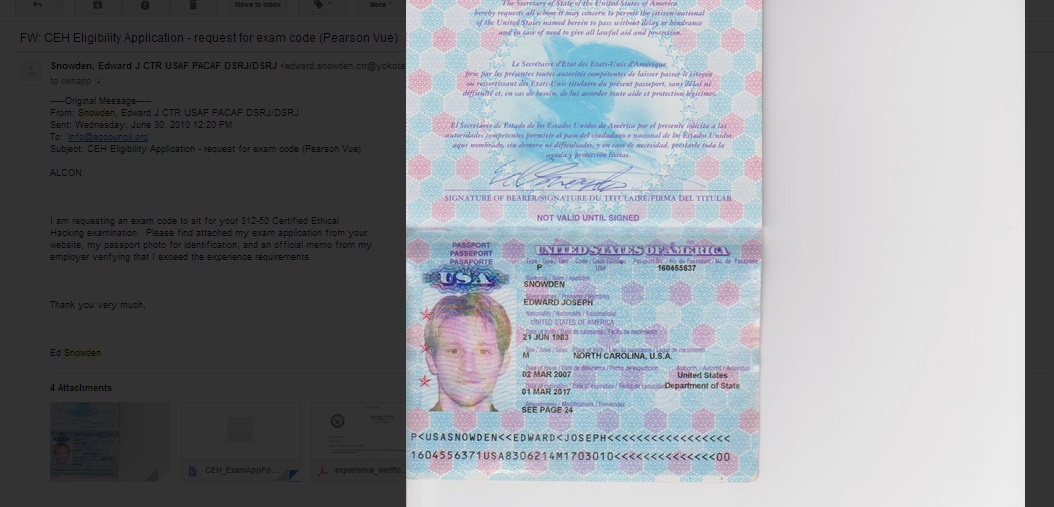
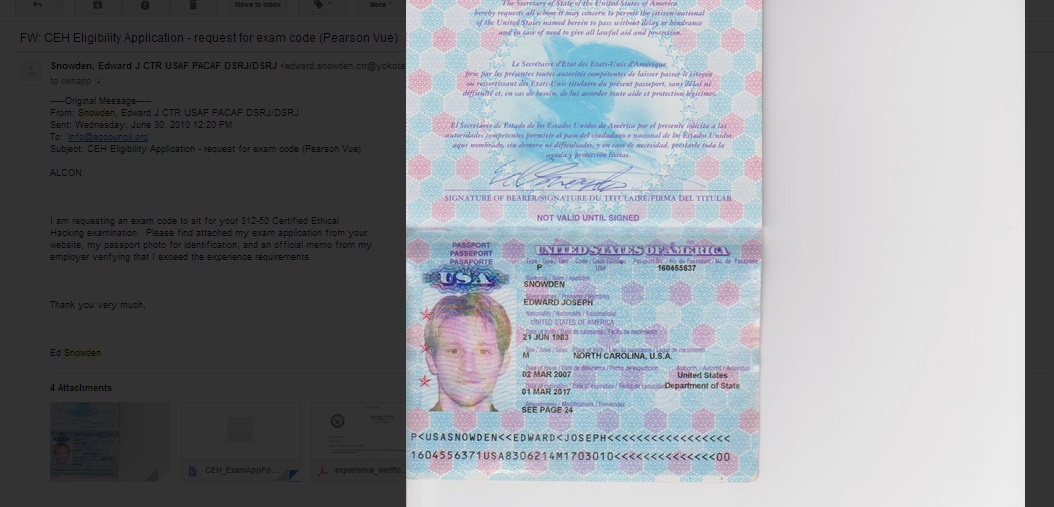 224News
224NewsEthical Hacking Organization Website Hacked, Defaced with Snowden’ Passport
Screenshot of the deface page left by the hackers EC- Council Website of the Security Certification Group got defaced with passport of...
-

 449Cyber Crime
449Cyber CrimeMost small‑office routers have ‘critical’ vulnerabilities as mysterious ‘Moon’ worm spreads
A large majority of routers used in small offices are plagued with security vulnerabilities - with up to 80% of small office/home...
-

 75Cyber Crime
75Cyber CrimeNeiman Marcus attackers set off 60,000 alerts – but went unnoticed
Hackers who stole hundreds of thousands of card details from upscale retailer Neiman Marcus set off more than 60,000 security alerts -...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




