Featured News
-

 89Cyber Crime
89Cyber CrimeFinancial files from Mt Gox supposedly ‘leak online’ after CEO targeted
A file of material purporting to include detailed information on trades at the Bitcoin exchange Mt Gox, has surfaced online, after attackers...
-

 139Scams
139ScamsThe Billgate Foundation – the fall for money, eh many…
Recently it was announced that Satya Nadella will be Steve Ballmer’s successor as CEO of Microsoft. Of course for the cybercriminals this...
-

 277Scams
277ScamsFive ‘new friends’ to avoid like the plague on social networks
Befriending the wrong person on Facebook can hand a criminal the tools for an identity theft attack - and on LinkedIn, talking...
-
 236Cyber Crime
236Cyber CrimeJustin Bieber is the latest celebrity to have his Twitter account hacked
Maybe it's time to think twice before rushing to click on a link, next time your favourite celebrity says something bizarre on...
-

 154Scams
154ScamsHow cybercriminals ‘market’ email attacks – and why LinkedIn lures are today’s prize phish
Cybercriminals ‘manage’ phishing emails using techniques similar to those used by marketing agencies, including the use of ‘test audiences’ to see how...
-

 172Privacy
172Privacy‘Secure’ web browsing can leak private data to employers and ISPs, researchers warn
University of Berkeley researchers have revealed a technique for identifying individual web pages visited ‘securely’ by users, with up to 89% accuracy,...
-

 253News
253NewsSnowden’s Latest Leak has fake UFO Images: Claims expert
A document among the trove leaked by Edward Snowden contains slides showing images of flying saucer as reported by Yahoo News Following...
-
 335News
335NewsCyberwar Heating Up: Ukraine hit by massive cyber attack from Russia, mobile networks blocked
The telecommunication system of Ukraine has got hit by cyber-attacks through the equipment which have been installed in the Russian-influenced Crimea. These...
-
 160Opinion
160OpinionCourier Scams – don’t give away your bank card
If someone rings you up to tell you that your bank card has been compromised, it may be because they want to...
-

 397Malware
397MalwareAndroid phones and tablets ship “pre‑infected” with malware
Android phones and tablets from four different manufacturers are arriving with malware “pre-installed” - a bogus version of Netflix which sends password...
-

 291News
291NewsMysterious UFO Photos Found in Documents Leaked by Snowden
Ex-NSA tech Snowden leaked documents had yet another element of surprise; it has a set of slides depicting mysterious spacecrafts referring to Flying...
-

 95Cyber Crime
95Cyber CrimeWWF warns of ‘arms race’ with ‘cyberpoachers’ targeting endangered species
Criminals seeking to kill endangered species and sell trophies online are turning to increasingly hi-tech methods to target their prey - including...
-

 74Cyber Crime
74Cyber CrimeBitcoin bank Flexcoin shuts down after attackers loot $570,000 from “hot wallet”
The attackers were able to steal all the bitcoins stored in the bank’s “hot wallet” - the portion of its funds on...
-

 108How To
108How ToHow can we as patients secure our medical data?
When someone says “data privacy” most people think about the information that is available on sites like Google and Facebook, or stored...
-

 102Password
102PasswordDon’t panic! Twitter mass password reset was ‘mistake’ company admits
An emailed warning and enforced password reset sent out to Twitter users on Monday due to a supposed compromise of their accounts...
-
 340Surveillance
340SurveillanceIts not just the NSA! Facebook also collects data: Says White House
It is not just the NSA, the infamous snooping authority of the US, that has been collecting data of millions of Americans,...
-

 101Cyber Crime
101Cyber CrimeMore than 300,000 wireless routers hijacked by criminals in global attack
More than 300,000 wireless routers worldwide are under the control of an unknown group of cybercriminals, who have made malicious changes to...
-

 74Cyber Crime
74Cyber CrimeMt Gox site code “posted online” as exchange admits $500m in bitcoin is lost
Bitcoin exchange Mt Gox has admitted that nearly $500 million in bitcoin has “disappeared”, in a new statement posted online - as...
-

 167Scams
167ScamsNetflix phish, tech support scam, same phrying pan
Yet another innovative tech support scam, using Netflix phishing to get remote access to the victim's system.
-

 110Scams
110ScamsCisco offers $300,000 for “visionary” solutions to defend ‘Internet of Things’
Networking giant Cisco has launched a “grand challenge” to invent a security solution for the “internet of things” - a broad term...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
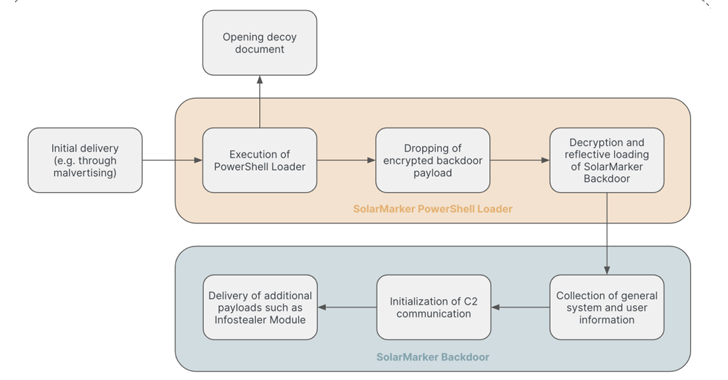 Data Breach
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
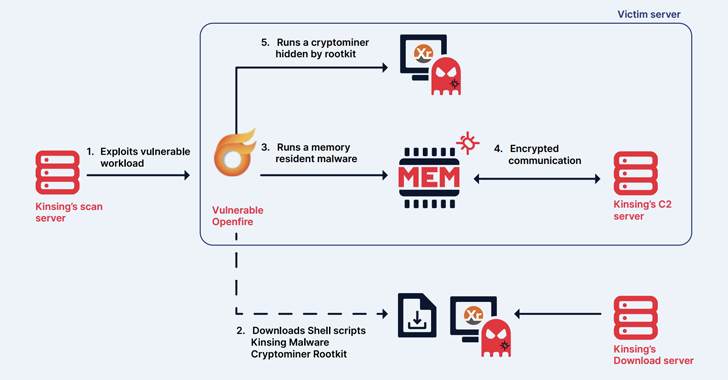 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
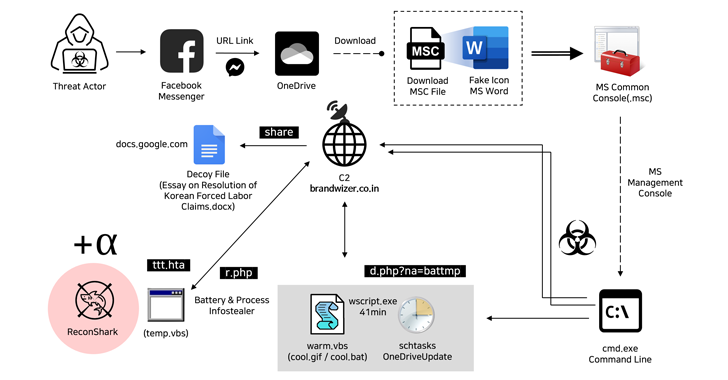 Malware
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
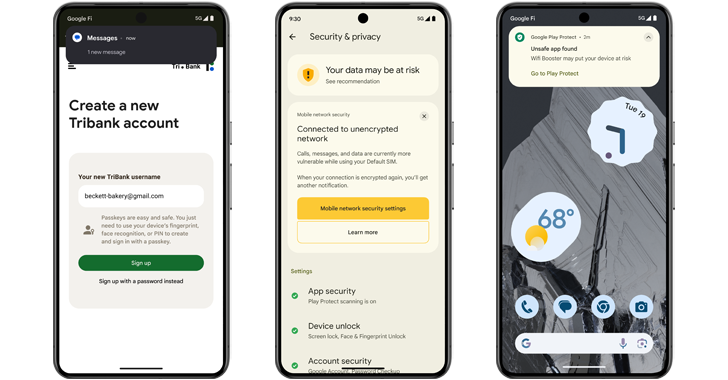
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage




