Featured News
-

 60Cyber Crime
60Cyber CrimeVietnamese malware : ‘Single post’ enough to trigger spyware attacks against U.S. bloggers, EFF claims
A Californian blogger was among victims of a malware attack which targeted critics of the communist state in Vietnam, as well as...
-

 166Cyber Crime
166Cyber CrimeAmerican Spies Want Snowden Dead
Although Snowden is held in high esteem by ordinary citizens of America, as a whistle-blower, there are quite a few who swear...
-

 68Cyber Crime
68Cyber CrimePush to replace “hugely insecure” credit card system in U.S after rash of retailer breaches
The ‘magnetic stripe’ credit cards used by American banks should be replaced with the more secure chip-and-PIN systems standard in Europe and...
-

 384News
384News#OpIsraelBirthday: Hackers of the World Uniting Forces for a Massive Cyber Attack against Israel on 7 April 2014
The online hacktivist AnonGhost along with a group of hackers has decided to attack Israeli cyber space on 7th April, 2014 when...
-

 148News
148News#OpFullerton: Anonymous takes down Fullerton police website against protesters arrest and Kelly Thomas tribute
The online hacktivist Anonymous has taken down the official website of Fullerton police department in retaliation for the arrest of protesters and citizen journalists....
-

 161Cyber Events
161Cyber EventsNSA Reforms: Obama to End Government Storage of Cell Data and Snooping on Friendly Neighbors
Delivering a speech on NSA reforms after seven months since the first revelations on NSA by Edward Snowden, President Obama remained unapologetic...
-

 102Malware
102MalwareBoaxxe adware: ‘A good advert sells the product without drawing attention to itself’ Part 2
In this post, we examine the complex it fits into a larger click fraud ecosystem, where users can be redirected either automatically,...
-

 395Cyber Crime
395Cyber CrimeHuge shortage of cyber‑defenders as threat levels ‘highest since records began’, Cisco report warns
Cisco claims in its report that cybercrime is now a global, professional industry - and there is a worldwide shortage of professionals...
-
 273News
273NewsAnti-NSA Blackphone: Encrypted smartphone designed to rescue users from surveillance
Post-Snowden revelations about NSA snooping on private data of almost every individual, Silent Circle, a Switzerland based encryption firm, has partnered with...
-
 144Cyber Crime
144Cyber CrimeMicrosoft offers brief reprieve to Windows XP users – with antimalware updates until July 2015
The computer giant announced the change of policy in an official blog post in which it said that although XP was no...
-

 84Cyber Crime
84Cyber CrimeThousands of hotels under attack as Google Maps and Google+ listings hijacked
Thousands of hotels have found that their listings on Google Maps and Google+ have been ‘hijacked’ - pointing instead to different sites,...
-

 282News
282NewsRedHack Leaks 4,000 Turkcell numbers against providing Ministers with new numbers
RedHack Leaks 4k Turkcell numbers against facilitating Ministers with new numbers. The famous hacktivist group RedHack has leaked phone numbers of more...
-

 77Password
77PasswordBetter latte than never? Starbucks adds extra shot of security after app blunder
Starbucks has promised to update its mobile app - the most-used mobile payment app in America - after a security researcher found...
-

 277News
277NewsAVG in trouble: Gets 19 official domains hacked by Indonesian and Pakistani hackers
The internet security software company AVG is in trouble, this time the company has been attacked by hackers from Indonesia and Pakistan who have...
-

 109Malware
109MalwareFridge raiders: Will 2014 REALLY be the year your Smart Home gets hacked?
At CES 2014, the app was king - and more importantly, the appcessory - fridges, lights, appliances and gadgets built for app...
-
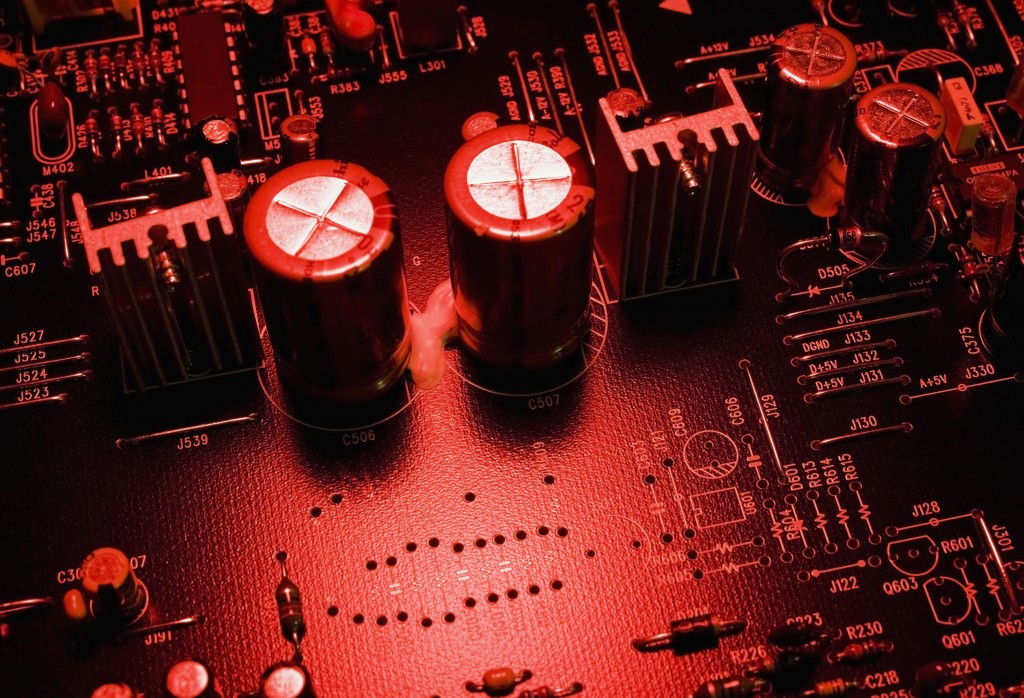
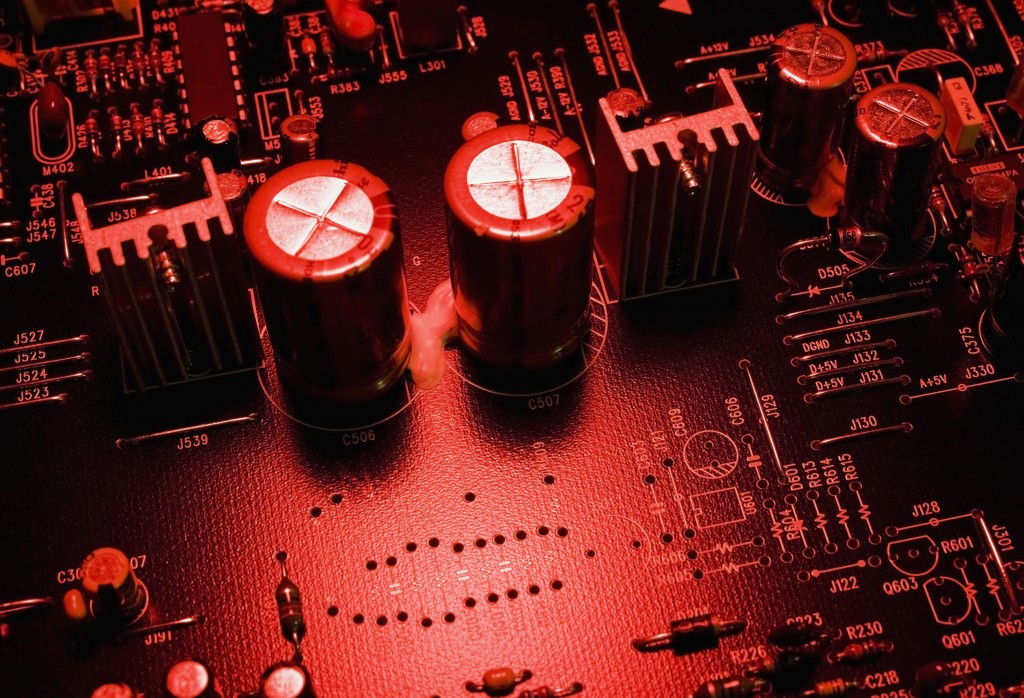 72Cyber Crime
72Cyber CrimeSecret radio technology allowed NSA to spy on PCs disconnected from the Internet
A secret technology which relied on radio transmissions has allowed the National Security Agency to spy on computers disconnected from the internet...
-

 79Cyber Crime
79Cyber CrimeBorrowing tricks from cybercriminals can ‘scare’ web users into safe browsing, Cambridge researchers claim
Computer users often feel bombarded by warnings about malware - particularly in internet browsers, which often repeatedly warn about risky sites -...
-

 233News
233NewsSyrian Electronic Army’s official website hacked and defaced by Turkish Hackers
A group of Turkish hackers going with the handle of @Turkguvenligi on Twitter has hacked and defaced the official website (http://leaks.sea.sy/) of high...
-
 105Surveillance
105SurveillanceNSA Surveillance Fails to Prevent Terrorist Attacks: Report
The US government’s extensive dragnet across the country keeping track of almost everything that travels across the internet and following every single...
-

 64Cyber Crime
64Cyber CrimeMajor cyber attacks ‘can be predicted’ using computer model, researchers claim
Major international cyber attacks follow a pattern - and attacks such as Stuxnet, which targeted Iran's nuclear plant can be predicted by...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




