Featured News
-

 119How To
119How ToCan you hear us now? ESET researchers podcast every week
Have you checked out the weekly podcast by ESET security researchers? It's called the ESET Malware Report and it covers many security...
-

 88Cyber Crime
88Cyber CrimePhantom menace? A guide to APTs – and why most of us have little to fear from these ‘cyberweapons’
APTs - or Advanced Persistent Threats - are the most menacing cyber attack there is, some say. Built to be stealthy, they...
-

 379Cyber Crime
379Cyber CrimeWill car‑hacking be the “next global cybercrime”? Senator’s letter inspires debate
As wireless technologies and electronic controls are increasingly built into cars, vehicles could become vulnerable to hackers - either stealing information, or...
-

 101Password
101PasswordMicrosoft uses “telepathy” to warn users off weak passwords
Microsoft's telepathic power, of course, comes from AI, not magic, and illustrates very clearly which passwords are easy for a computer to...
-

 190How To
190How ToWhy “crypto” isn’t just for spies: A beginner’s guide to keeping secrets
For years, "encryption" has sounded like James Bond technology to many PC users - but new systems have made "crypto" technology easier...
-

 390Cyber Crime
390Cyber CrimeMicrosoft’s new crime‑fighting super‑team strikes blow against million‑strong “zombie army”
Only weeks after Microsoft unveiled a global Cybercrime Center armed with new, hi-tech tools to combat crime, it announced it had carried...
-

 195Malware
195MalwareDid you say “Advanced” Persistent Threats?
Once in a while we get to spend time analyzing malicious code that is not as widespread as other threats we've encountered....
-

 335Malware
335MalwareHas‑bean? Old Androids still on Jelly Bean can be “lock‑picked” by malware
A vulnerability in Android could allow attackers to “unlock” phones without cracking PIN codes - using malware to deactivate Google’s locks on...
-
 172Surveillance
172SurveillanceObama: I am not allowed to use iPhone for ‘security reasons’
Wednesday: I am not allowed to use iPhone for security reason: President Barak Obama. President Barak Obama has given an unusual statement during...
-
 122Cyber Crime
122Cyber CrimeJP Morgan warns 465,000 cardholders of data leak after hackers breach defenses
Personal information for up to 465,000 customers of JP Morgan, Chase & Co. may be at risk after hackers breached its network...
-

 103Privacy
103PrivacyOh look, a hacked package delivery drone
News of Amazon's plans to use aerial drones to deliver packages raises the prospect of clashing values in areas like use of...
-

 261News
261NewsHackers Steal 2 Million Facebook, Gmail and Twitter Passwords in a Massive Hack
An InfoSec company TrustWave has reported that unknown hackers have stolen usernames and passwords of two million accounts at Google, Facebook, Twitter, Yahoo and...
-

 268How To
268How ToWhy your small business needs an information security policy and a WISP
Information security policy can make a big difference for small business. Here we offer advice, resources, and a free recorded webinar on...
-

 391Malware
391MalwareUltrasonic cyber‑attack can “steal information” even from high‑security systems, researchers warn
An audio communication system designed for ultrasonic underwater communications can be used to steal data - even from disconnected PCs in secure...
-

 255News
255NewsOregon State’s City of Amity and Sutherlin City Websites Hacked by Iranian hackers
An Iranian hacker going with the handle of ‘hossein19123’ from Ashiyane Digital Security Team has hacked and defaced the official websites of City of...
-
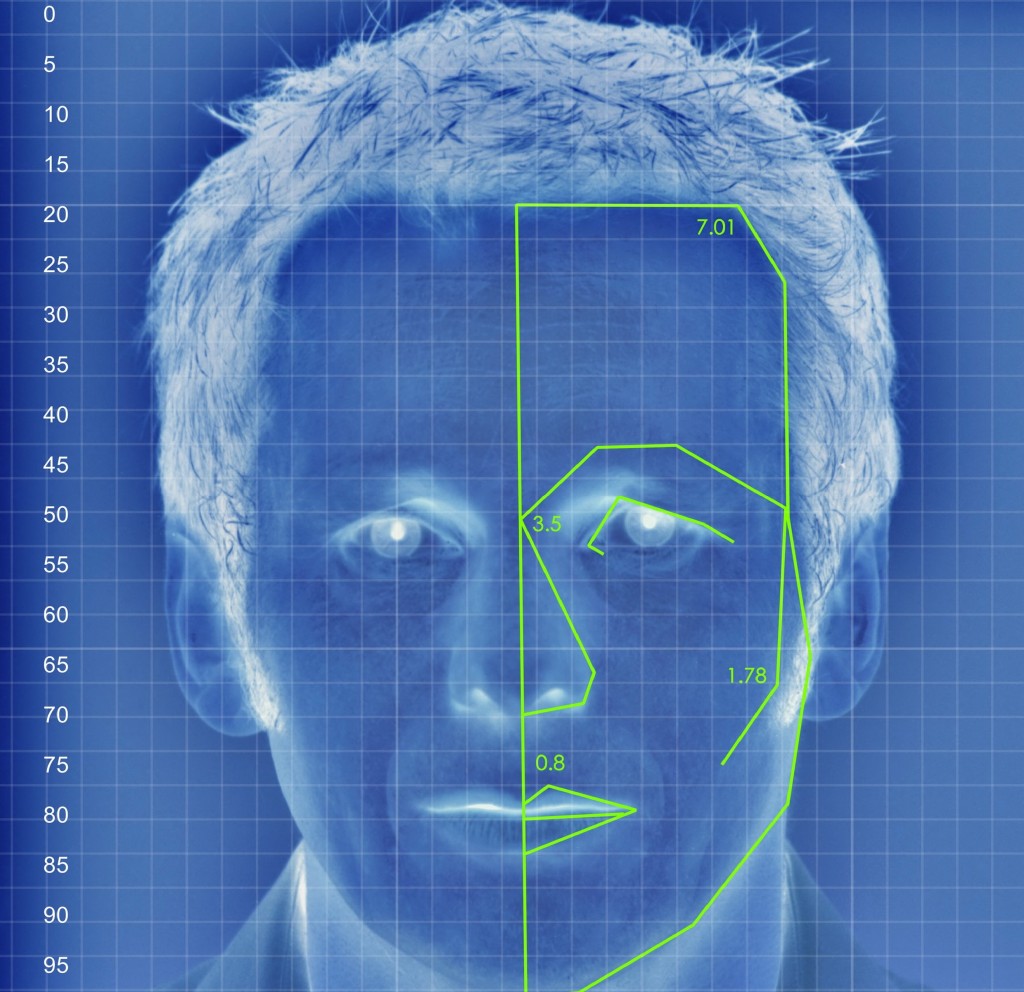
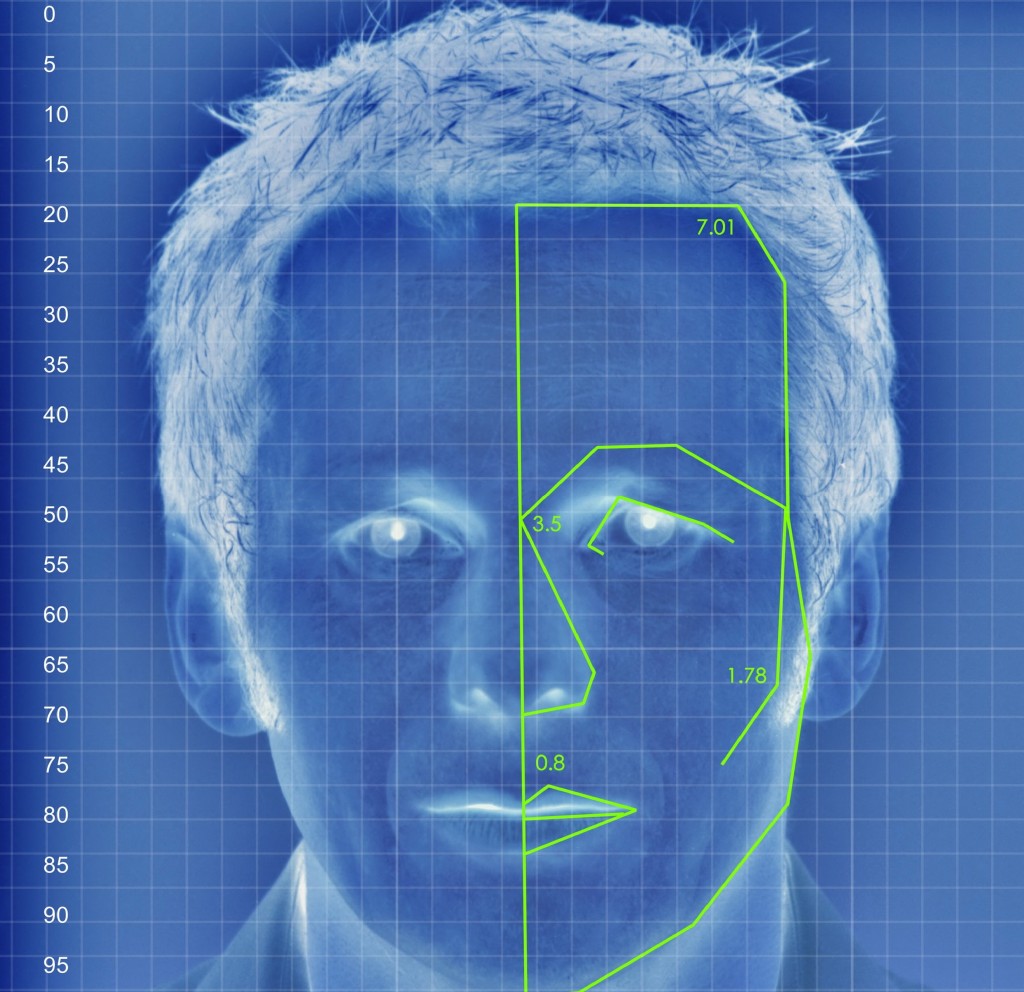 402Password
402PasswordNew Apple face‑recognizing system could prevent snoopers reading your alerts
Apple users may soon be able not only to unlock their devices simply by showing their face - they may be able...
-

 247News
247NewsProtest against election fraud continues as Anonymous hacks more Honduras government portals
Yesterday, we reported how “ Anonymous Honduras ” hacked and defaced high profile Honduras government websites including Interpol and State Police websites against electoral fraud in...
-

 196Malware
196MalwareSpy agencies working on cyberweapon “more powerful than Stuxnet”, claims Iran
An Iranian news agency has said that “malware worse than Stuxnet” may soon be unleashed, to “spy on and destroy the software...
-

 86Cyber Crime
86Cyber CrimeMillions in Bitcoin stolen from Sheep dark market as user flees
One of the ‘dark marketplaces’ offering illegal and semi-legal services via the anonymized web browser Tor has shut down, according to reports...
-
 273News
273NewsAnonymous hacks and defaces Interpol Honduras and State Police websites against electoral fraud
The online hacktivist group ‘Anonymous Honduras‘ has hacked and defaced 6 high profile Honduras government ministries websites against the alleged fraud in...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




