Featured News
-
 252Scams
252ScamsTech Support Scammers: Talking to a Real Support Team
It so happens that I live over 5,000 miles from the ESET North America office in San Diego, and so tend not...
-

 204News
204NewsCode-Newbie Team from Indonesia and Malaysia Hacks 44 Chinese Government Domains
A group of Indonesian and Malaysian hacker going with the handle of Code-Newbie has hacked and defaced 44 Chinese government sub-domains belonging to Fifth...
-

 262News
262News#OpNSA: Australian Federal Police and Reserve Bank websites taken down amid spying row with Indonesia
Thursday: An Indonesian hacker going with the handle of ./BCT_48 has claimed responsibility for taking down the official website of Australian Federal Police and Reserve Bank amid an...
-

 387Malware
387MalwarePC gaming service fined $1m for serving up Bitcoin‑mining malware
The company, E-Sports Entertainment, served up malware which used PCs to mine Bitcoins, an attack which earned $3,602. The malware was delivered...
-
 210News
210NewsAnonymous Declares Global Cyber War on U.S. Government against Hammond’s Sentence and NSA Spying
The online hacktivist group Anonymous has released a video, according to which the group has declared global cyber war on the government of United...
-
 233News
233NewsPakistani Hackers Hacks All India Radio Allahabad Website, Greets Iranian and Syrian Hackers
The official website of All India Radio Allahabad has been hacked and defaced by Pakistani Hacker going with the handle of BLACK H3ART. Hacker has...
-

 134Cyber Crime
134Cyber CrimeWhat becomes of the broken hearted? Dating website leaked 42 million usernames and passwords
Dating site Cupid Media left personal details and plain text passwords for 42 million users exposed after an attack earlier this year....
-
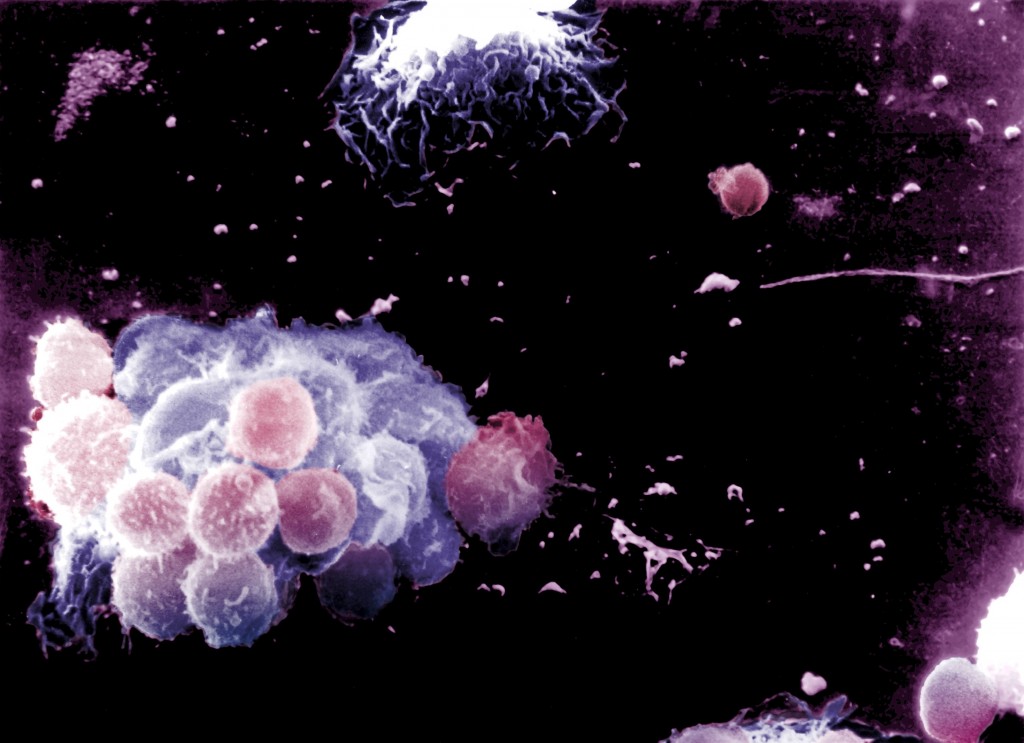
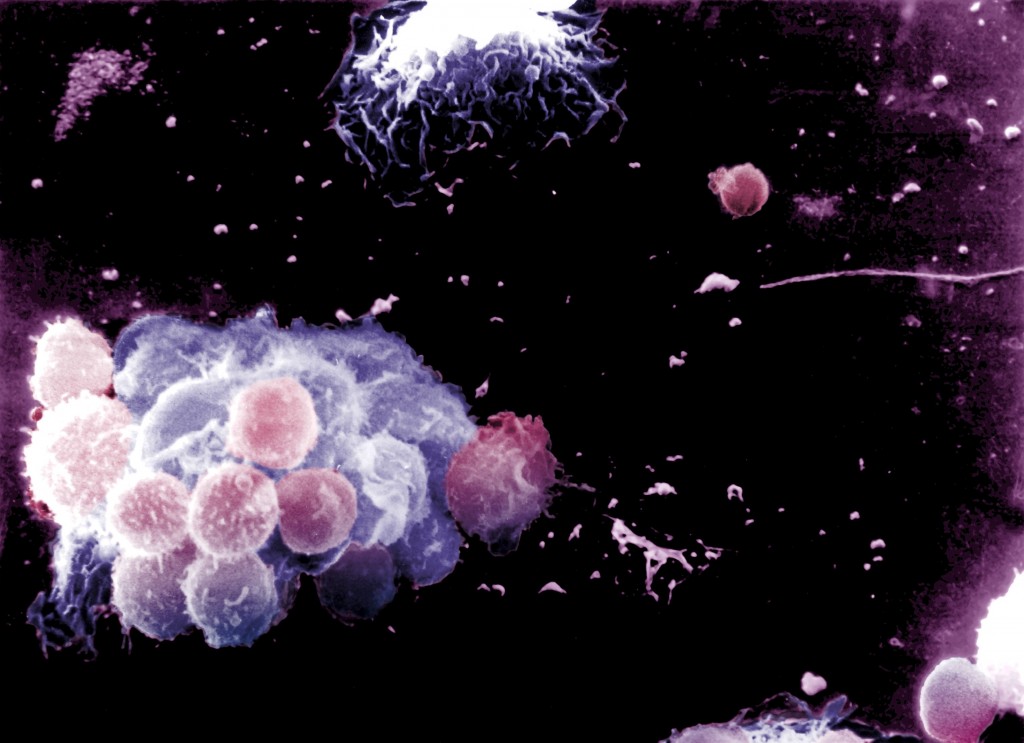 88Malware
88MalwareGraham Cluley: AV shouldn’t just be something on your hard drive – it should be part of a global immune system
In the first of a series of guest blog posts AV industry veteran Graham Cluley voices his opinion on how security has...
-

 88Password
88PasswordDoes your mouse know it’s you? Researchers claim patterns can “fingerprint” users – and lock out imposters
When any computer user types on a keyboard, the pattern of keystrokes is unique - like a fingerprint. When using a mouse,...
-

 131Malware
131MalwareChronology of a Skype attack
By the middle of May, users around the world started to receive messages from their contacts through different instant-messaging applications, such as...
-

 249News
249NewsSyrian Ministry of Electricity Website Hacked and Defaced by Bangladesh Grey Hat Hackers
A hacker going with the handle of Albaze Ever from Bangladesh Grey Hat Hackers has hacked and defaced the official website of Syrian Arab Republic’s...
-

 207News
207NewsOfficial Website of Peru’s President and National Police Defaced by LulzSec Peru
The online hacktivists from Lulz Security Peru have hacked and defaced the official website of Peruvian President and Peruvian National Police. The website of Peruvian President...
-

 296Surveillance
296SurveillancePrivacy Breach by Google as Father Finds Son’s Dead Image and Crime Scene on Google Maps
Kevin Barrera was murdered at age 14 in 2009 in Richmond, California. In 2013, however, his death took on new proportions after...
-

 74Cyber Crime
74Cyber CrimeDerivatives trader admits to “cyber intrusion” which leaked customer information
CME, described by Bloomberg as the world’s largest futures trader, said in a statement that “to date” there was no evidence that...
-

 186Cyber Crime
186Cyber CrimeMore woes for BlackBerry after “serious” security bug alert
Embattled handset maker BlackBerry has faced another blow, after the company warned users of a security bug affecting the software used to...
-

 204News
204NewsOfficial Franklin County, Ohio Website/Portal Hacked and Defaced by Nullroot
A hacker going with the handle of /Nullroot has hacked and defaced the official website of Franklin County, Ohio State on 17th Nov,...
-

 362Android
362AndroidAndroids destroyed: Hacking contest pays out $50,000 “bug bounties” for successful attacks on Nexus 4 and Galaxy S4
“Pinkie Pie”, an under-21 hacker won $50,000 at the Pwn2Own contest, as he used drive-by attacks to take over a Samsung Galaxy...
-

 144Malware
144Malware“Tens of millions” at risk from Filecoder due to “mass email spam event” targeting small businesses, British police agency warns
Tens of millions of computer users are at risk from Filecoder due to a “mass spamming event”, detailed in an alert from...
-

 281News
281News8 NASA Domains Hacked and Defaced by Italian Hackers Team
A newly emerging hacking group going with the handle of M4ST£R 1T4L!4N H@CK£RS T£4M (Master Italian Hackers Team) has hacked and defaced...
-
 301News
301NewsAnonGhost Hacks Hillside Illinois Police Department website against NATO Strikes
The official website of State of Illinois’ Hillside Police Department has been hacked and defaced by online hactivist group AnonGhost. Hillside Police Department...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




