Featured News
-

 91Cyber Crime
91Cyber CrimeMassive ‘war game’ batters London’s banking system with simulated cyber onslaught
One of the largest cyber 'war games' ever created tested thousands of banking staff across London’s investment banks against the ‘worst case...
-
 110Malware
110MalwareESET response to Bits of Freedom open letter on detection of government malware
A coalition of digital rights organizations and academics recently published an ‘open letter’ to the Anti-Malware/Anti-Virus industry asking for clarification on vendor...
-

 113Malware
113MalwareBack up now! Warning over new wave of Filecoder infections hitting U.S.
American PC users are being hit with a new wave of Filecoder ransomware, which locks access to computers and demands $300 -...
-

 281Surveillance
281SurveillanceBrazil demands answer over Google Street View Car spying on its citizens
Brazilian authorities have accused Google of spying over their country’s streets. According to the authorities, Google since the launch of it’s street...
-

 132News
132NewsBMPoC Hacking Group Hacks and Defaces 21 Brazilian Military Domains
The hackers behind NASA hack from BMPoC hacking group have now hacked and defaced total 21 sub-domains of Brazilian Military. The domains...
-

 329News
329NewsSingapore Prime Minister: We Will Track Anonymous Down, In return Anonymous Hacks His Official Website
The official website of Singapore Prime Minister Lee Hsien Loong (http://www.pmo.gov.sg/) was hacked and defaced by Anonymous Singapore after receiving a warning directly from PM’s...
-
 187News
187NewsOfficial Website of Maharashtra Police Academy, India Defaced by Pak Cyber Pyrates
A Pakistani hacker going with the handle of Gujjar (PCP) from Pak Cyber Pyrates had hacked and defaced the official website of Maharashtra...
-
 162News
162NewsPalestinian Broadcasting Corporation Website Hacked, Left with Bible Verses
The official website of Palestinian Broadcasting Corporation (PBS) has been hacked and defaced by a hacker going with the handle of gOx....
-

 248News
248NewsSyrian Electronic Army Hacks Vice Magazine Website, Deletes Article About Members’ Identities
The pro-Syrian President hackers from Syrian Electronic Army has hacked the official website of Vice Magazine (vice.com) for publishing article, revealing the identities...
-

 70Cyber Crime
70Cyber CrimeBitcoin heist nets thieves $1.2 million – and site warns “don’t store your coins on the net”
A cyberheist targeting a bitcoin "bank" website has netted thieves more than 4,100 bitcoins, worth $1.2 million. The hack is among the...
-
 93Password
93PasswordNew ‘inkblot’ passwords could be safe – even AFTER a big breach, researchers claim
The system relies on users describing patterns of blots, then matching descriptions to patterns - and should be foil the automated programs...
-

 291Privacy
291PrivacyHow can domestic violence survivors protect their privacy?
Domestic violence is not something that gets discussed much in information security circles, but there are few people that need advice on...
-

 73Cyber Crime
73Cyber Crime‘Drug market’ Silk Road 2.0 launches on Tor – with new security in place
Only weeks after the closure of Silk Road, a “drug market” which authorities claim shipped $1.2 billion of drugs including heroin around...
-
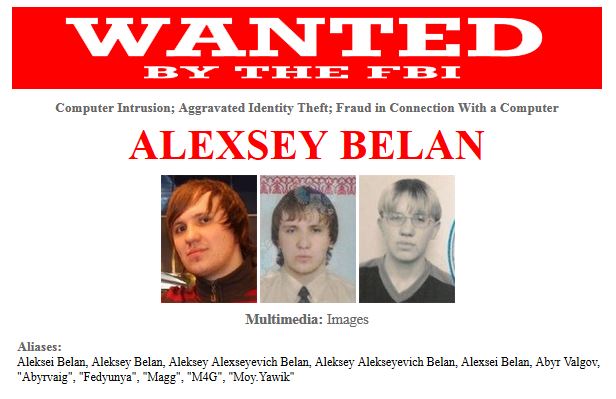
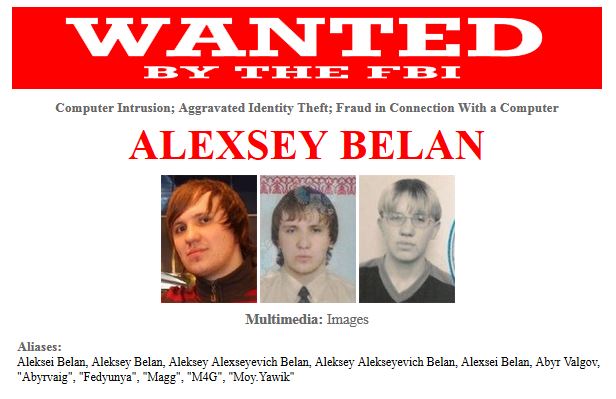 174Cyber Crime
174Cyber CrimeFBI adds five new targets to its Cyber’s Most Wanted list – with bounties up to $100,000
The FBI added five new cybercriminals to its Most Wanted list - including a new entry at number one, Alexsey Belan. The...
-

 100Malware
100MalwareFive interesting facts about the Morris worm (for its 25th anniversary)
On November 2nd, 1988, the Morris worm was released by its author, and within 24 hours had caused damage across the world....
-

 84Password
84PasswordKnock, knock, unlock: New app unlocks Macs with two taps on your iPhone
A new app lets you unlock Mac computers without entering a password - users simply tap on a paired iPhone with the...
-

 161Cyber Crime
161Cyber CrimeAdobe breach reveals really terrible passwords are still popular – 2 million used “123456”
Adobe’s security breach laid bare 38 million passwords to the world - and a security researcher claims that 1.9 million of these...
-

 81Cyber Crime
81Cyber CrimeTom Hanks and Donald Trump among 850,000 victims as limo firm hack leaks addresses and AmEx numbers
Tom Hanks and Donald Trump are among a client list of 850,000 users of limousines and town cars to become the latest...
-

 388Password
388PasswordGoogle testing new way to keep passwords snooper‑proof in Chrome
Google may soon offer Chrome users a little extra protection for their passwords - which could previously be accessed in “one click”...
-

 91Malware
91MalwareGhost in the machine: Mysterious malware “jumps” between disconnected PCs, researcher claims
A three-year-battle with a mysterious new strain of malware has led researcher Dragos Ruiu to conclude that the BadBIOS malware infesting his...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




