Featured News
-

 169News
169News#OpMaryville: Anonymous Threatens To Go After Alleged Rapists, Prepares Twitter Storm for #JusticeforDaisy
The online hacktivists from Anonymous group has started an new operation under the banner of OpMaryville. The operation is planned when authorities at Maryville set...
-

 73Cyber Crime
73Cyber CrimeLaw “may need longer arm” to tackle international cyber gangs, British police chief admits
Bringing the international gang lords of cybercrime to justice is a “challenge”, the interim head of Britain’s new National Cyber Crime Unit...
-

 239News
239NewsIranian Hacker Hacks Israeli Job Portal, Leaks 3349 Login Accounts of Israeli Users
An Iranian hacker going with the handle of Dr.3v1l from Black_Devils B0ys hacking group has breached to an Israeli based job search portal, as...
-

 111Malware
111MalwareStop, thief! Five new tricks used by cybercriminals – and how to stay safe
From legitimate companies delivering software with a “side-order” of malware, to PC attacks that persuade you to infect your own phone, here...
-

 116Android
116AndroidSecurity alert over sensors in smartphones – is your accelerometer selling you out?
Most smartphones today contain an accelerometer - without them, the latest fitness apps don’t work - but a Stanford researchers has shown...
-

 278Surveillance
278SurveillanceBitTorrent Bashes NSA In Stunning Billboard Campaign
If you live in New York or San Francisco, you will know the importance of its billboards and strange messages mentioned on...
-

 391Cyber Crime
391Cyber CrimeSome D‑Link routers contain “backdoor” which allows remote access, researcher warns
Some models of the popular routers made by D-Link contain a “backdoor” which could allow a remote attacker access to settings and...
-

 269News
269News#OpTrollIsrael: 65 Israel Websites Hacked by AnonGhost
The Moroccan based online hacktivist going with the handle of AnonGhost has hacked and defaced 65 Israeli websites under the banner of...
-
 209News
209NewsBSNL Telecom India Domain Hacked and Defaced by P4K-M4D-HUNT3R-Z
A Pakistani hacker going with the handle of Ch3rn0by1 from P4K-M4D-HUNT3R-Z has hacked and defaced the official domain of India’s Bharat Sanchar Nigam Limited (BSNL) Telecom yesterday....
-

 291News
291NewsPakistani Hacker Defaces official Google, Google Images and Google Plus Malaysia Domains
In a high profile hack, a famous Pakistani hacker going with the handle of H4x0r HuSsY from MadLeets hacking crew has...
-
 128News
128NewsBMPoC Hacker Defaces another NASA Domain but not against NSA or Syrian War
The world renowned BMPoC hacker who got fame by defacing 14 official NASA domains against NSA’s spying over Brazil and Syrian war has now defaced...
-

 423News
423NewsAnonymous Palestine – KDMS Team Defaces Websites Anti-Virus ESET, BitFinder, Penetration Software Metasploit and Rapid7
The online hacktivists from Anonymous Palestine – KDMS Team has hacked and defaced the official websites of anti-virus giant ESET, BitFinder along with...
-

 243Malware
243MalwareWin32/KanKan – Chinese drama
In this blog post, we will describe software detected by ESET products as Win32/Kankan, and explain why its discovery shocked many Chinese...
-

 80Cyber Crime
80Cyber CrimeThe wrong cable guys: Card skimmers install bogus wires into cash registers in Nordstrom store
A trio of men plugged keyloggers disguised as ordinary connectors into cash registers in a Nordstrom department store in Florida, and returned...
-

 382Password
382PasswordSupercar security? Porsche and Lacie unveil “ultra‑secure” encrypted USB stick
For many PC users USB keys must seem like a relic of a bygone age - but for security-conscious workers, keys can...
-

 158How To
158How ToFive bad PC habits many of us STILL have – and how to stop today
Tiny things such as using an admin account on your PC when you don’t need to can give cybercriminals their “way in”....
-
 82Password
82PasswordSmartphone users want more protection – and don’t mind being fingerprinted, says Paypal
Smartphone users want more protection for the data on their cellphone - and are perfectly comfortable being fingerprinted if that’s the best...
-
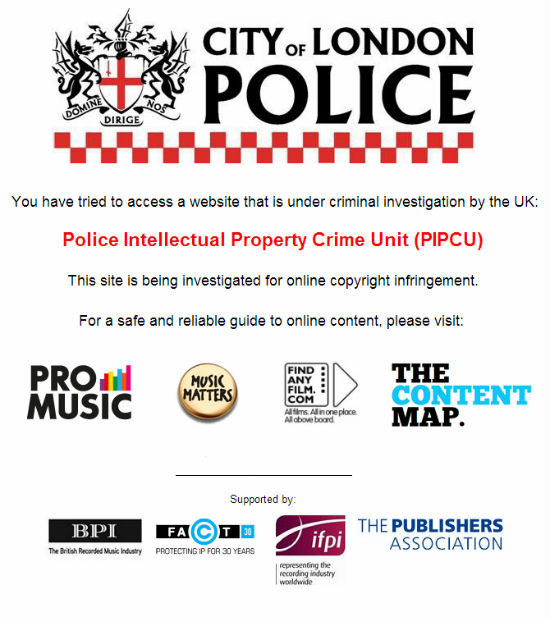
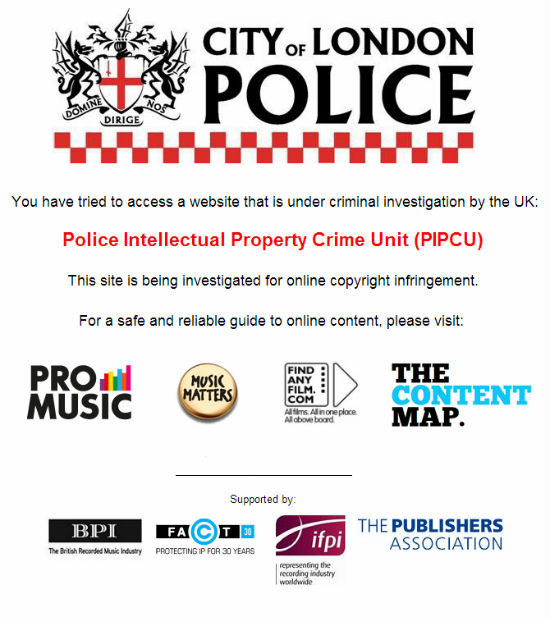 205Cyber Crime
205Cyber CrimeUK Police Orders Registrars to Shutdown Major Torrent Sites
The newly formed Intellectual Property Crime Unit of the City of London Police (IPCU) is in action. In its first operation the...
-

 257News
257NewsSyrian Hacker Dr.SHA6H Hacks and Defaces City of Mansfield, OH Website for Free Syria
Famous Syrian Hacker Dr.SHA6H has hacked and defaced the official website of U.S. City of Mansfield, OH earlier today in support of a...
-

 66Cyber Crime
66Cyber CrimeEU cyber agency warns of “outdated” systems in power plants – and suggests new safety measures
Cyber attacks against Industrial Control Systems pose a risk to power plants and other critical infrastructure - and action is needed to...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




