Featured News
-

 342Malware
342MalwareFake Grand Theft Auto V tempts thousands of PC users to download “malware”
Grand Theft Auto V sold more than $1 billion worth of units in a week - no wonder cybercriminals are tempted to...
-

 161Cyber Crime
161Cyber CrimeIs this how Indonesia topped the malicious traffic charts?
Indonesia as a major source of malicious traffic? That's what a recent infographic from content delivery network provider Akamai seemed to say....
-

 203News
203NewsU.S. Department of State’s Domain Hacked and Defaced by Dbuzz Indonesian Hacker
An Indonesian Hacker known with the handle of Dbuzz has hacked and defaced the official sub-domain of U.S. Department of State (http://ourplanet.infocentral.state.gov). Defaced domain...
-

 379Malware
379MalwareWarning overload? Half of PC users ignore virus alerts – and middle‑aged are “worst culprits”
Middle aged PC users routinely ignore warnings that sites may harm their computers - and that figure has doubled since 2011, according...
-

 201News
201NewsWebsite of U.S. (US Embassy.gov) Embassies, Consulates, and Diplomatic Missions Hacked by Indonesian Hackers
In an extremely high profile hack, An Indonesian hacker going with the handle of Dbuzz has hacked and defaced the official blog...
-

 417Cyber Crime
417Cyber CrimeMillions at risk as guest information from hotel Wi‑Fi provider “goes on sale” in China
A huge amount of private information harvested via hotel Wi-Fi networks is on sale in China - including phone numbers, dates of...
-
 296Cyber Events
296Cyber Events#OpDirenis: Anonymous and RedHack Join Hands for November 5 Protests in Turkey
November 5 will be a day when people from around the world will gather to march and protest for several causes. World’s most...
-

 348Kids Online
348Kids OnlineWarning over “risky behavior” of under‑12s online – and parents need to take action
Children indulge in highly risky behavior online - with nearly one in five 9-11 year olds having physically met strangers they encountered...
-

 85Cyber Crime
85Cyber CrimeCyberattacks against major firms “double in one year”, report warns
Cyber attacks have doubled in the year 2012-2013, according to a fraud report released by investigators Kroll - and the target is...
-

 258News
258NewsDaily Mail UK Newspaper Discussion Forum Hacked and Defaced by TeaM MADLEETS
Newly emerging Pakistan based hacking group TeaM MADLEETS has done a high profile defacement in which the official forum of world renowned UK...
-
 213News
213NewsQatari Domain Registrar Hacked, Government and Military Websites Defaced by Syria Electronic Army
The hackers from Syrian Electronic Army known for their hardcore support for Syrian President Bashar Ul Assad are back in news with...
-

 214News
214NewsAzerbaijan Hacker Team Hacks National Security Service of Armenia, Claims to leak Secret Documents
A group of Azerbaijani hackers from Azerbaijan Hacker Team has hacked several Armenian websites including the website of Armenian National Security Service....
-

 177Geek
177GeekCouple in China ‘Sell’ Their Baby Daughter to Buy iPhone
A couple in Shanghai city of China is facing criminal charges for selling their infant daughter on an online forum in order...
-
 113Malware
113MalwareSolutions to current antivirus challenges
The detection and blocking of malicious code employed by modern threats, whether targeted attacks or mass-spreading campaigns, has been a game of...
-

 284Geek
284GeekIsraeli Think Tank Acknowledges Iran as Major Cyber Power, Iran Claims its 4th Biggest Cyber Army in World
Iran is now the world’s fourth biggest cyber army, claims an official of the Islamic Revolution Guards Corps stressing that the IRGC’s...
-

 123Android
123AndroidNew IBM system adds “robust” security to smartphone banking and shopping
Cybercriminals are already targeting mobile banking apps as a “way in” to customer accounts – as witnessed in ESET’s discovery of a...
-

 89Cyber Crime
89Cyber CrimeAdobe hackers behind breach at PR Newswire – but company claims “no fake releases” have gone out
The global press release distribution firm PR Newswire has admitted to a large-scale breach, in which usernames and passwords were stolen -...
-

 270News
270NewsRed Bull Energy Drink Server Hacked, Domains of 09 Countries Defaced by Oxer-X
A famous Algerian hacker Over-X has hacked into the server of world renowned Red Bull energy drink, as a result company’s blog and...
-

 170How To
170How ToClean up, speed up: How to make your PC run faster
On average, Windows PC users spend five days a year waiting for their machines to load - and the culprit for slow...
-
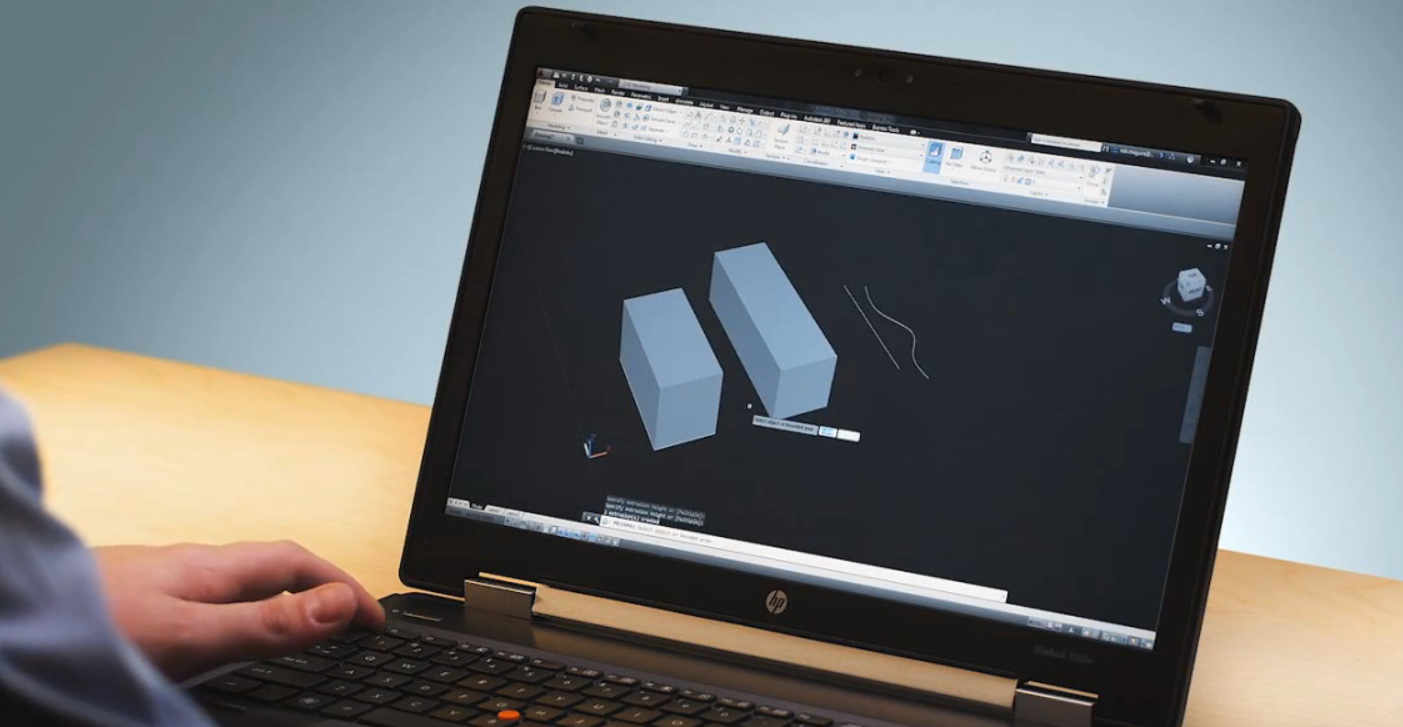
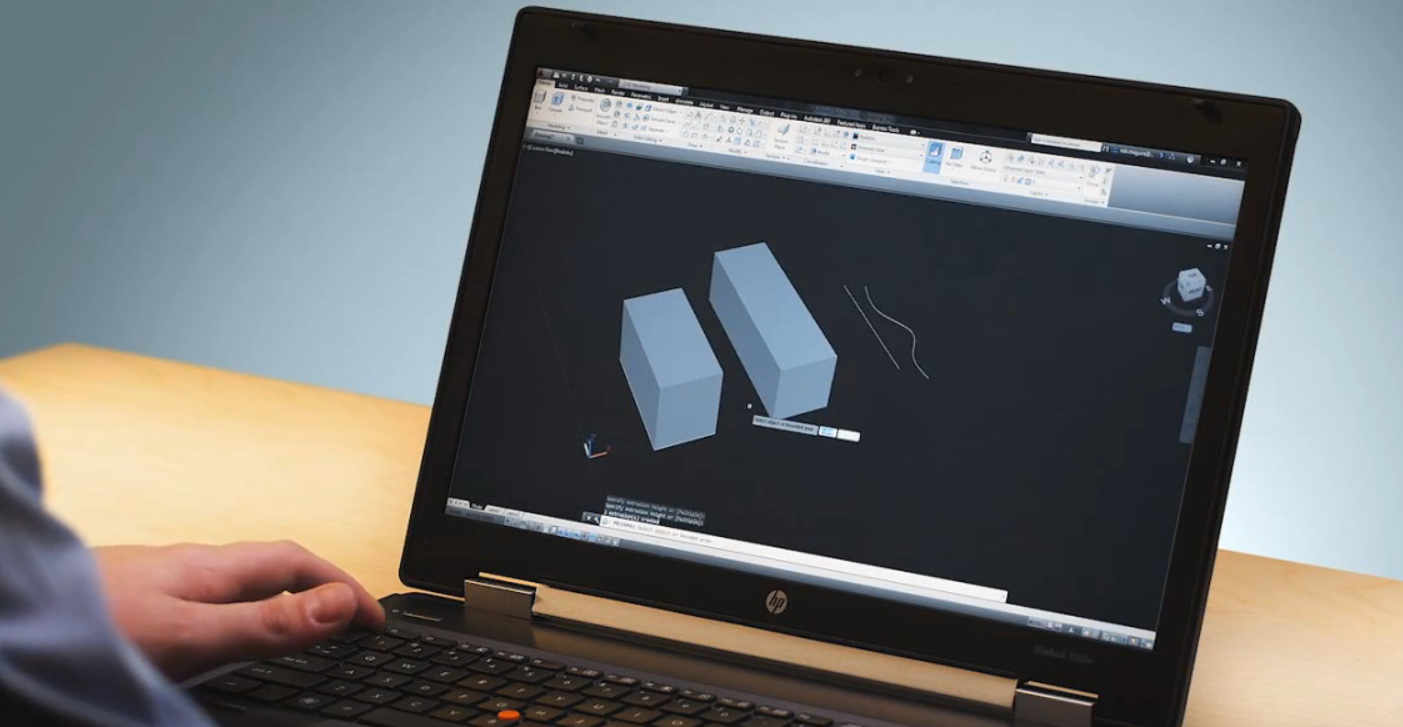 88Malware
88MalwareA prompt to save the world: new security features against malware in AutoCAD
Security researchers from Autodesk, along with Microsoft, announced new features in AutoCAD to prevent malware in a presentation at Virus Bulletin 2013...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




