Featured News
-

 161How To
161How ToFive bad PC habits many of us STILL have – and how to stop today
Tiny things such as using an admin account on your PC when you don’t need to can give cybercriminals their “way in”....
-
 87Password
87PasswordSmartphone users want more protection – and don’t mind being fingerprinted, says Paypal
Smartphone users want more protection for the data on their cellphone - and are perfectly comfortable being fingerprinted if that’s the best...
-
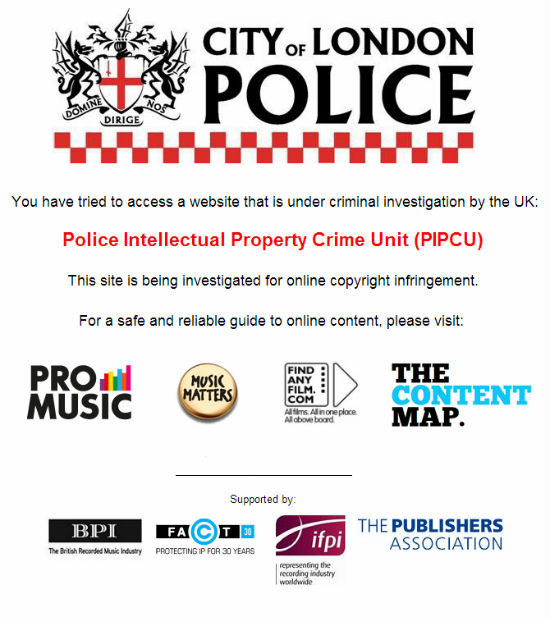
 209Cyber Crime
209Cyber CrimeUK Police Orders Registrars to Shutdown Major Torrent Sites
The newly formed Intellectual Property Crime Unit of the City of London Police (IPCU) is in action. In its first operation the...
-

 267News
267NewsSyrian Hacker Dr.SHA6H Hacks and Defaces City of Mansfield, OH Website for Free Syria
Famous Syrian Hacker Dr.SHA6H has hacked and defaced the official website of U.S. City of Mansfield, OH earlier today in support of a...
-

 70Cyber Crime
70Cyber CrimeEU cyber agency warns of “outdated” systems in power plants – and suggests new safety measures
Cyber attacks against Industrial Control Systems pose a risk to power plants and other critical infrastructure - and action is needed to...
-
 72Cyber Crime
72Cyber CrimePonemon study shows costs of cybercrime still rising – each attack now costs $1 million
The costs of cybercrime have continued to rise for victims, for the fourth consecutive year, according to a survey conducted by the...
-

 271News
271NewsAlexa Internet Search Domains Defaced by Anonymous Palestine – KDMS Team
The official domains of Alexa internet search have been hacked and defaced by Anonymous Palestine affiliated group KDMS Team. KDMS hackers left...
-
 304News
304NewsWhatsapp, Avira and AVG Anti-Virus Websites Hacked and Defaced by Anonymous Palestine
The official website of world’s most famous mobile messaging app Whatsapp, anti-virus giant Avira and AVG were defaced by newly emerging group of hackers...
-

 417Password
417PasswordAndroid users to get Apple‑baiting fingerprint protection “by next year”
Apple’s fingerprint sensor has drawn a huge amount of attention (and hack attempts) ever since it launched on iPhone 5S - but...
-

 112Cyber Crime
112Cyber CrimeWaking Shark: Banks to face biggest cyber war game ever in UK
A cyber “war game” will test Britain’s financial system to its limits in a virtual attack which will test the defenses of...
-
 373Password
373PasswordWho goes there? Voice‑recognizing biometrics are set to take off, claims Nuance exec
The human voice can be used as a secure, quick way to identify people, claims Bretislav Beranek of voice-recognition software company Nuance....
-

 103Malware
103MalwareSkorpion smartphone charger lights up if your phone contains malware
Plugging your smartphone in to charge up could soon offer an alert that you’ve contracted malware - with a new charger that...
-

 300News
300NewsSyrian Hacker Hacks Avast Anti-Virus Serbia Website, Demands Free Syria
Dr.SHA6H, a hacker who claims to be from Syria who apposes President Bashar Ul Assad has hacked and defaced the official website...
-

 73Cyber Crime
73Cyber CrimeInternet Explorer vulnerability will finally be patched on Tuesday after “months” of attacks
Internet Explorer users will be a great deal safer from Tuesday onwards, after Microsoft announced a patch for a vulnerability that has...
-

 70Cyber Crime
70Cyber CrimeAcrobat in hands of hackers, millions of customer details stolen, as Adobe admits to “unprecedented” breach
Adobe Systems, makers of popular software such as Acrobat, admitted on Thursday that hackers had penetrated its systems and stolen source code...
-

 197News
197NewsAdobe System Hacked and Breached, login information of 2.9 Million Customer Accessed
The multinational computer software company Adobe Systems, Inc has notified its users via their blog that the company has been hit by...
-
 176News
176NewsVote Wisely Says Anonymous Hacker after Hacking United Nations Honduras Website
The official website of United Nations Honduras has been hacked and defaced by a hacker going with the handle of Ch4FeR, which...
-
 131News
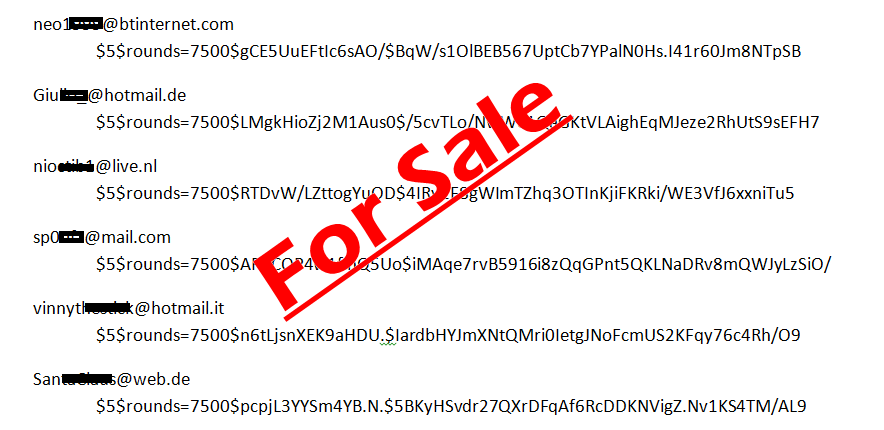
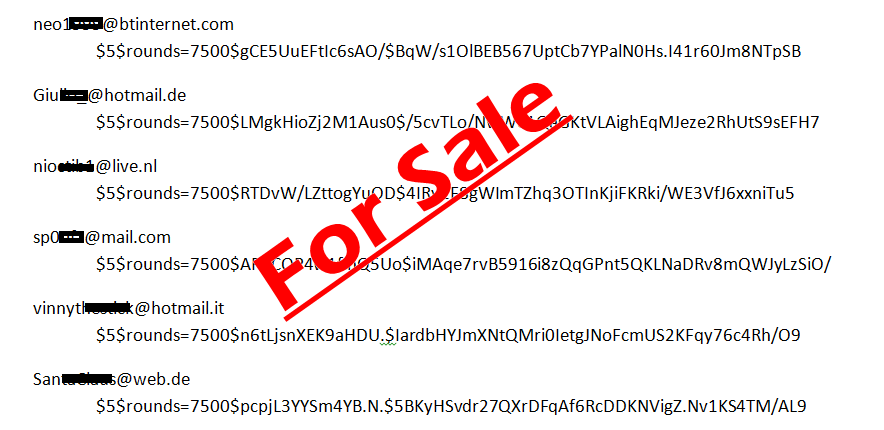
131NewsBitcoinTalk.org Website Defaced, 150,000 Emails and Passwords for Sale
A group of hackers going with the handle of “The Hole Seekers” have hacked and defaced a famous Bitcoin discussion forum on...
-

 200Surveillance
200SurveillanceFISA Court in action: USA to Google, Facebook, Microsoft: No, you can’t tell users we’re spying on them
A motion has been filed today with the Foreign Intelligence Surveillance Court by the U.S Department of Justice. This motion is basically...
-

 274Cyber Crime
274Cyber CrimeIranian Cyber Warfare Commander Assassinated
The head of the cyber warfare program of Iran has been shot dead. This act will further boost the allegations that the...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




