Featured News
-

 409Cyber Crime
409Cyber Crime“Cyber‑mercenaries” pose serious new threat, British government warns
Governments around the world are recruiting “cyber-mercenaries” - groups of skilled cyber professionals who target institutions such as banks and energy companies,...
-

 92Malware
92Malware“Bug bounties” are cheap way to keep companies secure, Berkeley study finds
“Bug bounties” paid out for finding and reporting bugs and vulnerabilities are a cheap and effective way for companies to bolster their...
-

 81Malware
81MalwareU.S. Government destroys $170,000 of PCS in malware scare – even mice and keyboards
A U.S. Government department threw away IT components including printers, computer mice and keyboards in an effort to root out a “sophisticated”...
-

 106Scams
106ScamsThe London Scam and the Londonderry Air
My colleagues at ESET Ireland, report that an all-too-familiar scam is currently hitting Irish mailboxes. I’ve talked about it at some length...
-

 101Android
101AndroidDarkleech and the Android Master Key: making a hash of it
I made a comment recently that was subsequently quoted in a recent ESET blog – Android “master key” leaves 900 million devices...
-

 393Cyber Crime
393Cyber CrimeCyber‑threat to London 2012 Olympic opening ceremony revealed
The threat of cyber attack loomed over the opening ceremony for the London Olympics last year, officials have revealed.
-

 410Cyber Crime
410Cyber CrimeNintendo site breached after month‑long brute force assault
A sustained brute force cyber attack battered Nintendo’s defences for a month this summer - and allowed cybercriminals access to private data...
-
 4.3KNews
4.3KNews8 Egyptian Ministry Websites Hacked by Anonymous Jordan, asks Anti-Morsi Protesters Few Questions
An Anonymous hacker going with the handle of Anonymous Jordan has hacked and defaced eight (8) Egyptian Ministry websites against the taking down...
-

 80Cyber Crime
80Cyber CrimeInvestment firm Morningstar admits client credit card numbers leaked in breach
Investment research firm Morningstar says that personal information including credit card numbers for clients, email addresses and passwords may have been compromised...
-

 199News
199NewsAnonymous Group Targets Hawthorne Police Department For Brutally Shooting Dog
The online hackavist from Anonymous group has targeted the Hawthorne Police department in response to police shooting a man’s rottweiler dog. As reported by...
-

 196Data Security
196Data SecurityVulnerabilities in Android will allow NSA to strengthen its grip on users
Just a few days after the reports on vulnerability in the android devices, more shocking news are disclosed. Now, it is believed...
-

 311Cyber Crime
311Cyber CrimeBeware of New Ransomware Scams Targeting Android Devices!
Android phones have now become a source of income for the cyber criminals. The cyber criminals have began a new type of...
-

 258Cyber Events
258Cyber EventsBreaking: Nicaragua and Venezuela offers Asylum To Edward Snowden
Just breaking now that Edward Snowden the man behind leaking NSA’s secret documents and exposing PRISM project has been offered asylum by the Republic...
-

 226Data Security
226Data SecurityCritical Vulnerability In Android, Could Affect 99% Of Devices Out There
When it comes to malwares, often it is android which are most affected. Often in headlines we find some malware found in...
-
 109Cyber Crime
109Cyber CrimeHave you ever wondered how cyber crimes are plotted?
Derby University of mathematics and computing is helping the world to fight from cyber crime in most unusual way. Have you ever...
-

 109Malware
109MalwareAndroid malware attacks skyrocket in China
Mobile malware is growing at an extraordinary rate in China - with 25 times more detections of malicious programs last year than...
-

 424Cyber Crime
424Cyber CrimeSpear‑phishing attacks are “on the rise” warns FBI
Many industries are now being targeted by well-tailored spear-phishing scams, the FBI has warned, with emails containing accurate information about victims, harvested...
-
 297Cyber Crime
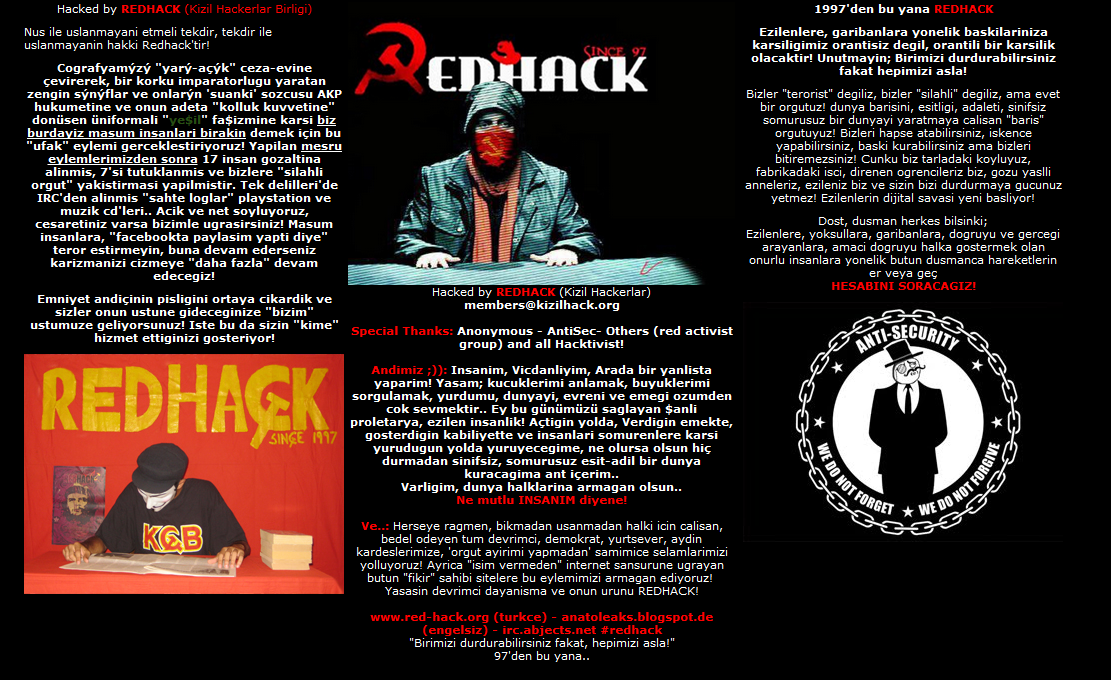
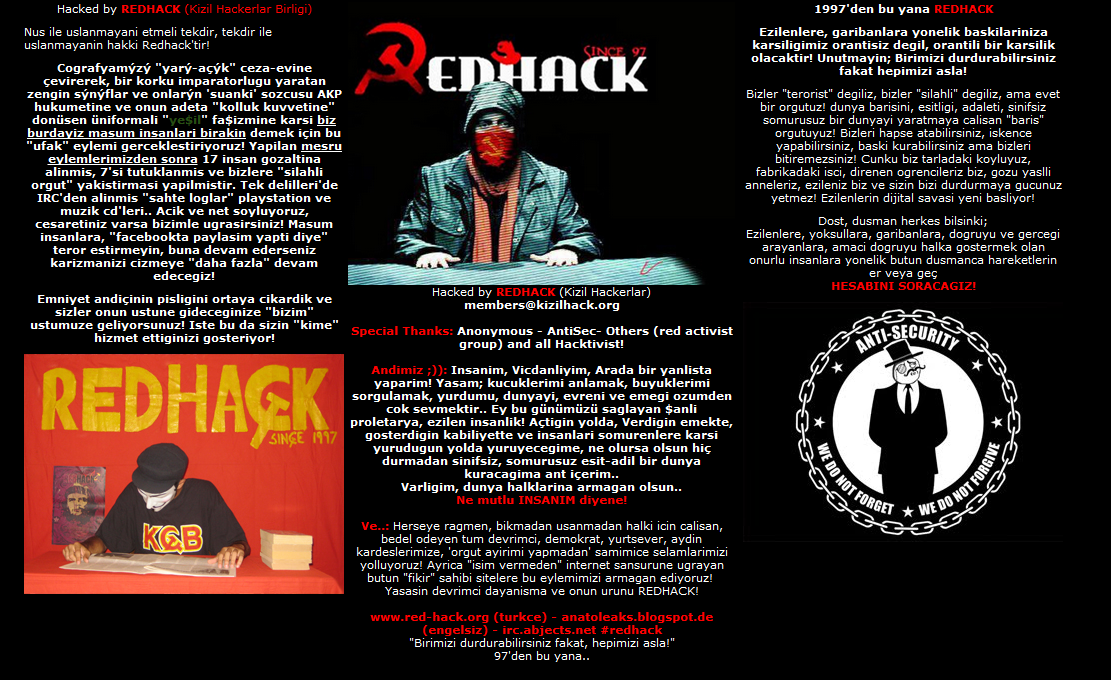
297Cyber CrimeTurkish Police Labels RedHack Hackavists as “Cyber Terrorist Organization”
In a report submitted by the Turkish police in Istanbul Prosecutor’s Office, the famous online hackavist group RedHack has been labed as...
-

 87Cyber Crime
87Cyber CrimeAndroid “master key” leaves 900 million devices vulnerable, researchers claim
Up to 900 million devices running Android could be affected by a new vulnerability which would allow cybercriminals “full control” over affected...
-

 235News
235News33 Chinese Gov sites Hacked by Turkish Hackers against Uyghurs Muslims Massacre
Three Turkish hackers going with the handle of Bozkurt97, De4THBLoW & Bozkurt71 collectively have hacked 33 Chinese government websites from Huojia county (huojia.gov.cn) in...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




