Featured News
-
 283News
283NewsFEMA hacked: Anonymous hacks US server in defense of Snowden and against threats from agency
A group of Anonymous hacker has said to hack into a server used by Federal Emergency Management. According to them, the data...
-

 97Kids Online
97Kids OnlineChildren are “the enemy” of good IT security
“Children are a formidable adversary - unlike any other,” says Microsoft security researcher Stuart Schechter, in a paper to be presented at...
-

 92Cyber Crime
92Cyber Crime“Black swan” warning as cybercrime hits half of world stock exchanges
More than half of securities exchanges around the world faced cyber attacks last year, according to a paper released by the International...
-

 207Surveillance
207SurveillanceBlackBerry allows Indian government a direct access to emails and Chats
Government agencies in India are now allowed to access your blackberry devices directly, allowing them to track conversations, emails and attachments sent...
-

 454News
454NewsTrueCaller Phone Directory Hacked, Database with Millions of Facebook, Twitter, Linkedin & Gmail accounts dumped
Syrian hackers known for their hardcore support for President Bashar Ul Assad from Syrian Electronic Army are back in news, this time...
-

 322Password
322PasswordHow to create strong passwords (without driving yourself mad)
There are a few tricks to making passwords that will at least slow down cybercriminals - buying you time to reset your...
-
 92Password
92PasswordTumblr warns users over iPhone app password danger
Micro-blogging site Tumblr has warned users that passwords can be “sniffed” from its iPhone and iPad apps - and issued a “very...
-

 423Cyber Crime
423Cyber CrimeTexas restaurant sues credit card giant after point‑of‑sale hack
A Texas restaurant chain is suing one of its suppliers over a point-of-sale system which allowed hackers to steal customer data -...
-

 347Cyber Crime
347Cyber CrimeHacked signal‑boosters let cybercriminals “listen in” on cellphones
A $250 signal-boosting device for cellphone users can be hacked, two researchers claim - offering total access to phone calls, internet use...
-

 87Malware
87Malware“Warning fatigue” means browser users ignore up to 70% of security alerts
Browser security warnings can work to protect users from phishing and malware sites - but “warning fatigue” means important alerts over site...
-
 105Password
105PasswordFacial recognition system “reads” blood vessels for unbreakable security
A new biometrics system could “read” blood vessels under the skin using thermal imaging cameras - a system which its inventors claim...
-

 304News
304NewsLulzSecPeru defaces, leaks data of Peru’s government portals for using NSA’s backed hosting service
LulzSecPeru known as one of the most skilled online hackavists are back, this time by the hackers have hacked and defaced the...
-

 235News
235NewsOfficial Sony Electronics Italy Website Breached, 40k accounts leaked by Turkish Ajan Hackers
The well known Turkish hackers from Turkish Ajan hacking group have hacked into the official website of Sony Electronics (web.sony.it) designated for...
-

 294Surveillance
294SurveillanceMicrosoft allowed NSA to Spy on Skype and Outlook
Microsoft has collaborated extensively with the intelligence services of the United States to allow users’ communications details. The company even helped the...
-

 388Cyber Crime
388Cyber CrimeCyber threats are now the third‑biggest worry for CEOs, Lloyds survey reveals
Cyber risk has shot up in importance for company CEOs and senior executives, according to an Ipsos survey for Lloyds Risk Index...
-

 405Cyber Crime
405Cyber CrimeOld‑school security? Kremlin orders $15,000‑worth of electric typewriters
A Kremlin security agency has ordered $15,000 of electric typewriters - sparking international gossip about a return to “old school” security measures.
-

 297Surveillance
297SurveillanceRussia uses typewriters to prevent Spying by US
The Russian newspaper “Izvestia” reported on Thursday that the Federal Protective Service of the country bought 20 typewriters to prevent sensitive information...
-
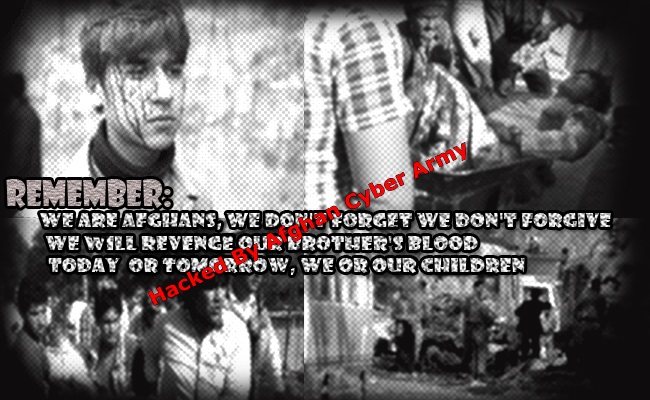
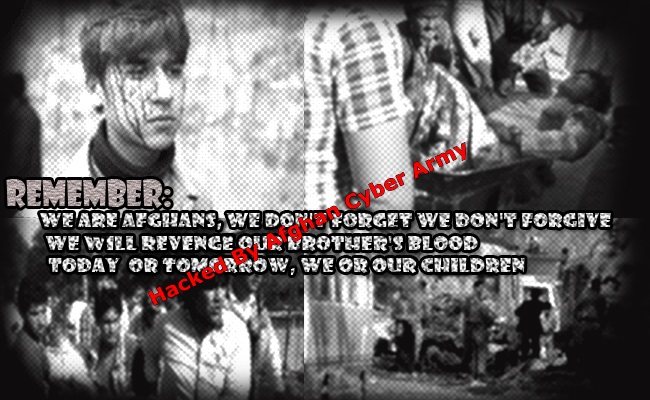 98News
98News6 Pakistani Ministry Websites Hacked by Afghan Cyber Army
A group of hackers claiming to have roots in Afghanistan going with the handle of Afghan Cyber Army has hacked and defaced six...
-

 422Cyber Crime
422Cyber Crime“Cyber‑mercenaries” pose serious new threat, British government warns
Governments around the world are recruiting “cyber-mercenaries” - groups of skilled cyber professionals who target institutions such as banks and energy companies,...
-

 101Malware
101Malware“Bug bounties” are cheap way to keep companies secure, Berkeley study finds
“Bug bounties” paid out for finding and reporting bugs and vulnerabilities are a cheap and effective way for companies to bolster their...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




