Featured News
-

 234News
234NewsParaguay Embassy in Argentina, 200 Mexican, 177 Pakistani Websites Hacked by Islamic Ghost Team
A hacking group going with the handle of Islamic Ghost Team from Morocco has hacked and defaced hundreds of websites including the official...
-

 179News
179NewsSky News Android apps on Google Play Hacked by Syrian Electronic Army
After making its name in hacking websites, Facebook and Twitter handles of major media outlets, Syrian Electronic Army has moved one level...
-

 185Cyber Crime
185Cyber CrimeLiberty Reserve Payment Processor Busted, Owner arrested for Money Laundering
The official website of Liberty Reserve (), known for its services such as payment processing and transfer has been shutdown by the...
-

 245News
245News#usaOPERATION1: Akron Canton Airport Hacked, 15,000 credentials leaked by Turkish Ajan Hacking Group
Online hackavists from Turkish Ajan hacking group have hacked and defaced the official website of Akron Canton Airport (http://www.akroncantonairport.com), as a result information of...
-

 121News
121NewsPetitions Website Change.org Hacked and Edited by Terminal hacker
A hacker going with the handle of Terminal Hacker has hacked famous petition site Change.org, as a result the hacker successfully changed and at some...
-
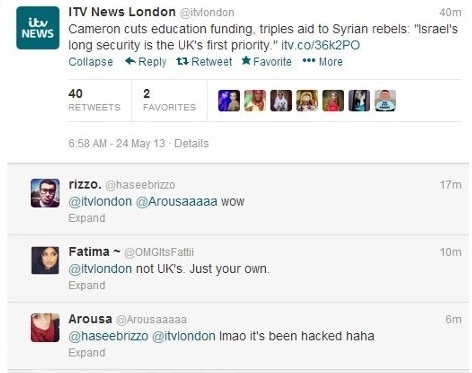
 382News
382NewsITV News London Twitter account Hacked by Syrian Electronic Army
The Pro Syrian President Bashar al-Assad hackers from Syrian Electronic Army has hacked the official Twitter account of British broadcaster ITV News,...
-

 251News
251NewsUnited Nations Information Center Jakarta Websites Hacked by Dr.SHA6H
Famous hackavist Dr.SHA6H who is known for his high profile is back with another one, this time by hacking and defacing 3 official...
-
 97Malware
97MalwareTax returns: Slovakian spyware campaign
ESET’s Security Research Lab details a malware-spreading campaign leveraging the deadline for tax returns in Slovakia and examines a case of infection...
-

 227News
227News50 Israeli Websites Hacked by CapoO_TunisiAnoO
Israeli cyber space is always under attack by hackers from all aver the world, one of those hackers is known as World...
-

 72Cyber Crime
72Cyber Crime“Stronger action” urged in face of IP theft from American companies
American companies are facing an “unprecedented” onslaught of data theft, costing “hundreds of billions”, according to a report by a private group...
-

 247News
247NewsOfficial UNICEF and UNDP Croatia Websites Hacked by Turkish Hackers
Three Turkish hackers going with the handles of eboz , flowchart and Vezir.04, collectively have hacked and defaced the official websites of United Nations...
-

 91Cyber Crime
91Cyber CrimeElectrical grids “woefully prepared” for cyber attacks, warns analyst
Electrical grids worldwide have become more susceptible to cyber attacks, due to the use of industrial control systems, according to market analysts...
-

 230News
230News49 Israeli Websites Hacked by The key40 from Algeria
An Algerian hacker going with the handle of ‘the key40’ has hacked and defaced total 49 Israeli websites. The sites were left...
-

 245Surveillance
245SurveillanceChinese Hackers who breached Google in 2010, gained access to massive Spy Data: US officials
Back in the year 2010, the Breach performed by Chinese hackers that was a part of the operation termed as Operation Aurora...
-

 75Cyber Crime
75Cyber CrimeTwitter beefs up security after wave of attacks on media sites
Twitter has introduced a new two-factor security system - an optional "extra layer" of security which should help to prevent unauthorised access...
-

 77Cyber Crime
77Cyber CrimeSmall business cybercrime costs $6,000 a year, says British group
Cybercrime is costing small businesses an average of £4,000 ($6000) a year, according to the British Federation of Small Businesses (FSB). A...
-

 95Privacy
95PrivacyXbox One Kinect microphone “always on” security fears
The Xbox One Kinect microphone – one of the hi-tech new features of Microsoft’s new Xbox One console – has raised security...
-

 239News
239NewsOfficial United Nation Pacific Website Hacked by Pakistani Hacker
H4x0r HuSsY from Pakistan who was in news for his high profile hacks against India and Sri Lankan is back with another one, this...
-
 146News
146NewsMicrosoft Warns of New Trojan Hijacking Facebook Accounts
Microsoft has released a warning of a new malware disguised extension for Google Chrome and Firefox add-on, began circulating on Facebook, targeting...
-

 175Surveillance
175SurveillanceHow Brazilian Government is Spying on its Citizens
The federal government of Brazil may indeed have access to private data that citizens may have provided to any private company. More...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




