Featured News
-

 244News
244News#OpTurkey Takes Height as Turkish Government Mufti Websites Hacked, Database Leaked by TurkHackTeam
It seems as #OpTurkey is taking heights as more hackers are joining in as in latest hack the Turkish hackavists from Turk Hack Team...
-

 223News
223News135 Indian Websites Hacked by Kurdish Hacker
Yet another day, yet another hack where a Kurdish hacker going with the handle of ‘SA3D HaCk3D has hacked and defaced total...
-

 291News
291NewsShalom Hartman Institute of Israel Hacked, 200 login accounts leaked by China Blue Army
A group of hackers from China Blue Army are claiming to breach the official website of Shalom Hartman Institute of Israel (hartman.org.il), ending up...
-

 295News
295NewsVirgin Radio Dubai Website Hacked, Database Left for Sale
A hacker going with the handle of OxAlien has hacked the official website of Virgin Radio Dubai (virginradiodubai.com) yesterday, as a result the database has...
-

 119Malware
119MalwareOperation Hangover: more links to the Oslo Freedom Forum incident
In our previous post on Operation Hangover, we revealed the existence of an attack group, apparently operating from within India, who were...
-
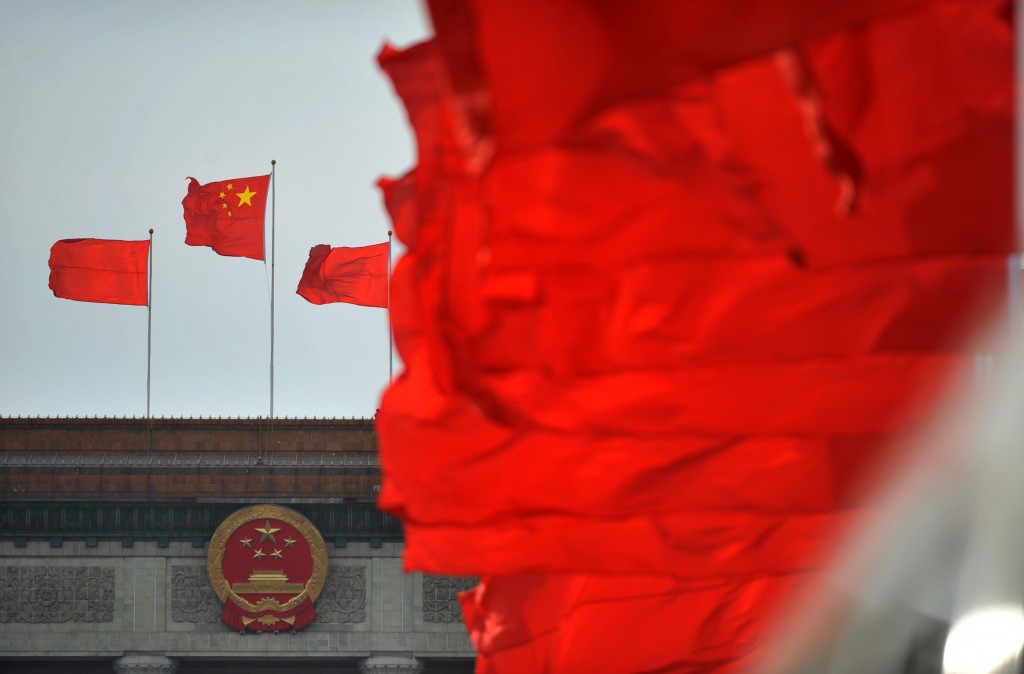
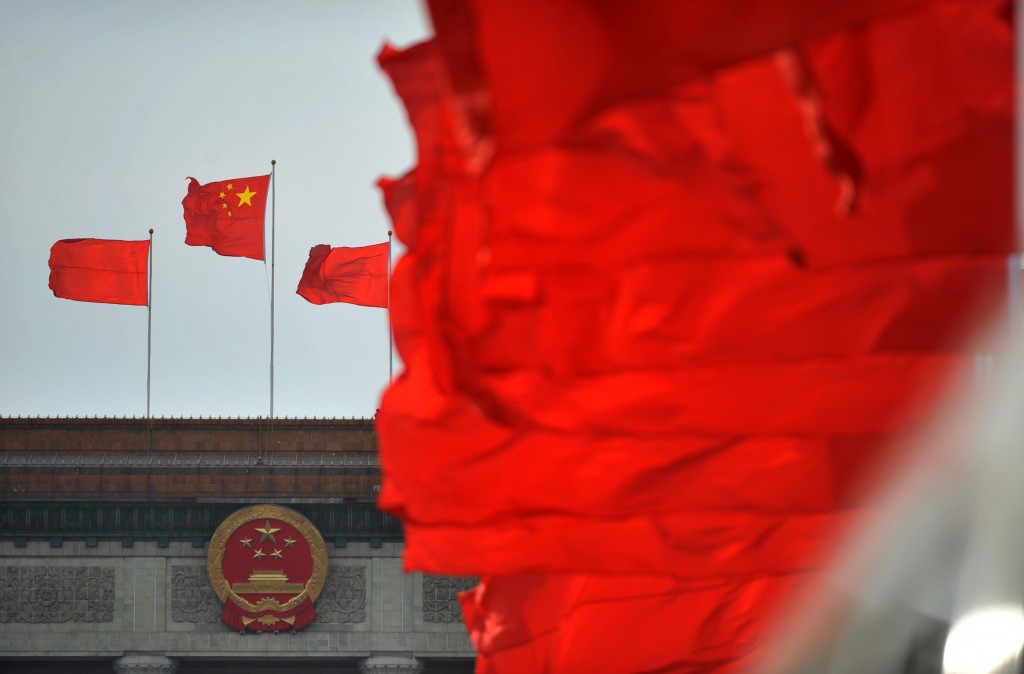 216Hacking
216HackingChina has “mountains of data” on U.S. cyber attacks, top official claims
A top internet security official in China has said that his organization has “mountains of data” on U.S. cyber attacks against the...
-

 260News
260News#OpTurkey: Turkish Prime Minister and Government Websites Hacked by Hacktivists
Online hackavists from Syrian Electronic Army (SEA) and Anonymous hackers have conducted a massive cyber attack on high profile Turkish government websites...
-

 353Windows
353WindowsLock folders with fingerprint security in Windows 8.1 as biometrics becomes “integral”
The upcoming 8.1 update to Windows 8 will offer improved fingerprint security - including the option to secure folders using a fingertip,...
-

 428Cyber Crime
428Cyber CrimeSilicon Valley “needs to lead” battle against cyber attacks, says ex‑Homeland Security chief
Silicon Valley technology firms should take the lead in defending the private sector against cyber attacks, says Paul Rosenzweig, a former Department...
-

 177News
177NewsMore 145 Turkish Websites Hacked by Tunisian Hackers
Anti-government protests are raising in Turkey, so as the protest on Turkish cyber space where 145 Turkish websites have been hacked and...
-
 286News
286News#OpTurkey: 4 Turkish Government Websites Hacked & Defaced by Security Dr@Gon
A Syrian hacker going with the handle of Security Dr@Gon has hacked and defaced 34 Turkish websites out of which 4 belongs to...
-

 196Data Security
196Data SecurityHack any iOS Device within One Minute by a Modified Charger
A team of security researchers at Georgia Institute of Technology have found a way by which any iOS device can be hacked within...
-
 216News
216NewsGovernment of Karnataka Websites hacked and defaced by Pakistani Hackers
Two Pakistani hackers going with the handle of Dr.FreaK & Xploiter, today have hacked and defaced two official websites of India’s government of...
-

 126Mobile Security
126Mobile SecurityFake iPhone charger can hack iOS in under 60 seconds
A fake iPhone charger could be used to bypass the defenses of Apple's smartphone, three researchers from Georgia Tech have claimed. In...
-

 380Cyber Crime
380Cyber CrimeCybercriminals use photo‑sharing to snare victims in auction scams, FBI warns
Cybercriminals are using online car auctions and photo-sharing services to dupe victims into downloading malware, the FBI has warned. Once infected, the...
-
 402Password
402PasswordEvernote and LinkedIn boost security with two‑factor authentication
Evernote and LinkedIn have both added an option for two-factor authentication in the past few days - days after Twitter announced its...
-

 99Password
99PasswordMotorola predicts passwords could be replaced by arm tattoos and “authentication pills”
Motorola has revealed plans for hi-tech authentication systems that could make accessing data faster and easier - including a “tattoo” with embedded...
-

 285News
285News#OpEDL: English Defence League Website Hacked and Defaced by Muslim Hackers
A hacker going with the handle of Cyber-Jihadi had hacked and defaced the official website English Defence League (englishdefenceleague.org). The site’s home page...
-

 98Cyber Crime
98Cyber CrimeDrupal.org resets passwords after hack exposes usernames, email addresses
The free open-source content management system Drupal has reset all Drupal.org passwords after unknown attackers gained access to user account data including...
-

 182Surveillance
182SurveillanceSurveillance Drones Now Being Deployed on German Railway Stations
The drones which fly at the height of 150 yards will be utilized at the graffiti “hotspots” such as the big German...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




