Featured News
-
 176Geek
176GeekIncapsula – New DDoS Study: Who Needs a Botnet when you have a 4 Gbps DDoS Cannon?
Who Needs a Botnet when you have a 4 Gbps DDoS Cannon? In recent months the DDoS world has shifted from complex...
-

 219News
219News33 Israeli Websites Hacked by CapoO_TunisiAnoO
33 Israeli Websites Hacked by CapoO_TunisiAnoO The hardcore anti-Israeli hacker from Tunisia going with the handle of CapoO_TunisiAnoO is back, this time after...
-

 227Geek
227GeekGoogle Maps ‘Murder Scene’ In Almere, Netherlands Is Water Trail From Golden Retriever
A recent image from Google earth took everyone by surprise as it showed rare images of a person’s murder. The image clearly...
-

 270Malware
270MalwareLinux/Cdorked.A: New Apache backdoor being used in the wild to serve Blackhole
Analysis of a malicious backdoor serving Blackhole exploit pack found on Linux Apache webserver compromised by malware dubbed Linux/Cdorked.A, together with remediation...
-

 219News
219NewsGovernment of SriLanka’s Top News Portal Hacked by Kurdish Elite Security Team
A hacker going with the handle Sultan Brain from Kurdish Elite Security Team has hacked and defaced three top SriLankan government owned news...
-

 564Surveillance
564SurveillanceIsrael Airport Security is now Allowed to Read Tourists Emails
Israel Airport Security is now Allowed to Read Tourists Emails The officials at Ben Gurion airport of Israel have announced that from...
-
 174News
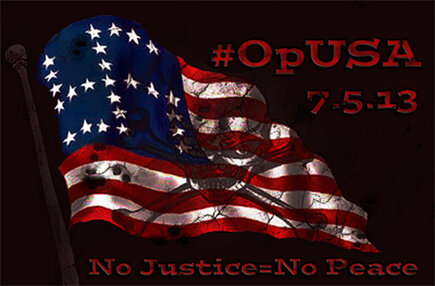
174News#OpUSA: Hackers Claim to Leak 40,000 Facebook accounts for #OpUSA
#OpUSA Hackers Claim to Leak 40,000 Facebook accounts for #OpUSA Different hackers from all over the world are conducting operation against the...
-

 110Cyber Crime
110Cyber CrimeGovernments need to spend billions more on data protection, says British security chief
Adrian Price, Head of Information Security at Britain's Ministry of Defence, suggested that governments should devote 20% of their budget to protecting...
-
 328News
328NewsHartford City, Indiana and Jefferson County, Wisconsin Websites Hacked by Nob0dy Hacker
Hartford City and Jefferson County, Wisconsin Websites Hacked & Defaced by Nob0dy Hacker A hacker going with the handle of NobOdy has hacked...
-

 358News
358NewsPakistani Security Researcher Founds XSS Vulnerability in IndiaTimes and Ask.com
An independent security researcher from Pakistan, going with the name of Danish Tariq has claimed to found cross site scripting vulnerability (XSS)...
-

 116Cyber Crime
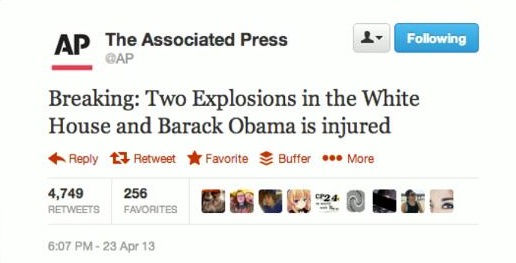
116Cyber CrimeTwitter security under spotlight after phishing blamed for disastrous AP Tweet
Twitter is said to be testing new security systems in the wake of a false Tweet from an official Associated Press account...
-
 303News
303NewsHackers Hijack Twitter accounts of The Associated Press Claiming Obama’s Injury in White House Blast
World renowned hackers from Syrian Electronic Army have hacked two official Twitter accounts of The Associated Press, which is a multinational non-profit news...
-
 108Cyber Crime
108Cyber CrimeHalf of British adults use the same password across all websites
Half of British adults use the same password across all the websites they access, according to telecoms regulator Ofcom. The data comes...
-

 100Cyber Crime
100Cyber CrimePreventable errors are behind most security breaches, says Verizon report
Most cyber attacks are simple and predictable, relying on basic tactics and preventable employee errors, according to Verizon’s annual Data Breach Investigations...
-
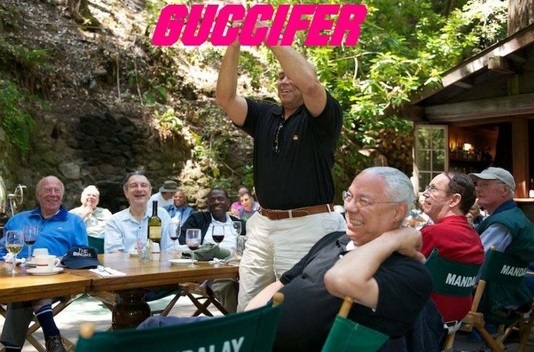
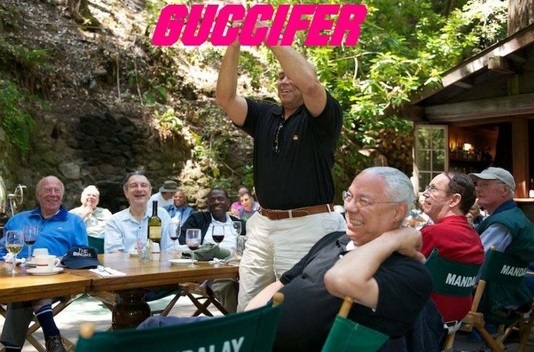 418News
418NewsHacked Photos Show Colin Powell At Bohemian Grove
On 15th April 2013, hacker going with the handle of Guccifer leaked hacked photos from Colin Powell’s personal email account showing the retired...
-

 269News
269NewsMinistry of National Defense – Polish Army, Websites Hacked and Defaced by Over-X
Ministry of National Defense – Polish Army, Websites Hacked and Defaced by Over-X Famous Algerian hacker Over-X has hacked and defaced six...
-

 408Malware
408MalwareHacked CBS Twitter accounts present followers with malware‑tainted “news”
Twitter accounts used by CBS News were compromised on Saturday - and began serving up bogus news stories with links to malware.
-

 124Malware
124MalwareU.S. Air Force team wins virtual “cyber war” against veteran hackers
A three-day “cyber war” ended in victory for a team from the U.S. Air Force Academy, who beat off attacks from hackers...
-

 269News
269NewsWebsite of Bangladesh Prime Minister’s Office Hacked & Defaced by Indian Hackers
Two Indian hackers, going with the handles of Yamraaj & 404 !-!@!2$!-!@ have hacked and defaced the official website of Bangladesh’s Prime...
-
 309News
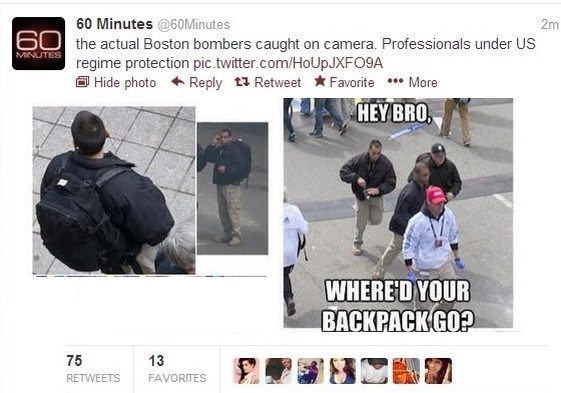
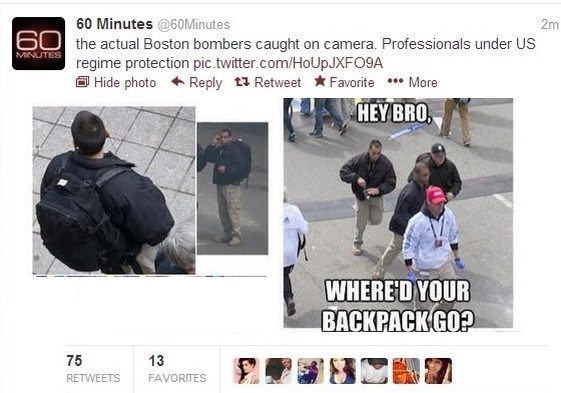
309NewsSyrian Electronic Army Hacks CBS Twitter To Claim Obama Involvement in Boston Bombings
Hacktivists expose media’s refusal to report on private operatives at Boston bombings The mainstream media’s refusal to report on images showing private...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




