Featured News
-
Malware
Stock Manipulation Botnets Gain Ground
The attacks from cybercriminals are now occurring in the online stock and equity trading world. Instead of simply emptying out compromised brokerage...
-
Password
Keylogging taken seriously: Security upgrades in the new Hotmail
Microsoft Hotmail has a new feature: Out of Band Authentication via cell phone SMS Text. They call it ‘single-use codes’: Single-use codes...
-
Scams
Truly Touching
I was greeted with the most charming email this morning. A young lady is so impressed with me that she wants to...
-
Scams
Ohhhh Free Money!!!
I received the following email recently: Greetings, Please forgive me for the unofficial way of reaching you via email Contacting you is...
-
Cyber Crime
Will Free Wi‑Fi at Starbucks and McDonalds Spread Malware?
Reports that Starbucks (NASD: SBUX) will be offering free 802.11 wireless access at all US locations starting July 1st raised some speculative...
-
Cyber Crime
IEEE eCrime Researchers Summit 2010 Call for Papers
The fifth IEEE eCrime Researchers Summit 2010 once again will be held in conjunction with the 2010 APWG General Meeting between October...
-
Malware
Cross‑platform Security Advisory for Flash Player, Adobe Reader and Acrobat
Ouch. This affects virtually everyone including Mac, Linux, and Windows users. More can be found here at the PSIRT site. And yes,...
-
Mac
Mac Malware OSX/OpinionSpy
A spyware application Intego calls OSX/OpinionSpy is being spread as part of the installation process for a number of screensavers and other...
-
Cyber Crime
Please Rob Me: Blippy
Blippy recently had a small data breach which merely underscored the risks of a growing segment of social networks which showcases your...
-
Malware
Banking Fraud? Tell me and tell me quick!
In the survey, banks that were notifying consumers as quickly as possible or immediately across multiple channels performed well [and] they also...
-
Privacy
New Facebook Privacy Controls Arrive on Wednesday
Mashable reports a halt to the insanity over privacy may be only a day away… On Sunday, Facebook CEO Mark Zuckerberg promised...
-
Cyber Crime
Carr’s Four Cyber Trends That Must Be Reversed Now
I’m not always in alignment with Jeffrey Carr’s point of view but in this he is spot on. Succinct and to the...
-
Malware
Library of Congress Acquires Entire Twitter Archive
Since the feed will be public and historic, there is a potential to research trends over the timeline, particularly as twitter is...
-
Cyber Crime
Cyber‑crimefighters pwn Carders.cc
Brian Krebs, source of a lot of key research on the banking trojan focus on small to medium sized business, has reported...
-
Malware
Bricking your cell phone: Mayhem on a Massive Scale
What would happen if every single one of the four BILLION cell phones on this planet just went dark? Or most likely,...
-
Cyber Crime
Debate Heating Up: Cybersecurity Act of 2010 S. 773
Forbes contributor Richard Stennion doesn’t like the Cybersecurity Act of 2010 very much. We know it around here as S. 773 and...
-
Cyber Crime
Cybercrime: Illegal Seizure Applicable or Not?
During a recent illness I was doing some research into rendition and the Fourth Amendment evidentiary issues which may come up more...
-
Privacy
Best Facebook Security Setting Infographic: NYTimes
At least it’s easier to understand than the prompt from Facebook asking me to accept and open my connections which I saw...
-
Scams
A New Scam?
David Harley sent me a link to an article about a scam I wasn’t familiar with. I wouldn’t really call it a...
-
Cyber Crime
Continued Malware Hijinks with Mass Webserver Compromises
While the jury’s still out about whether the intent of the past month’s mass webserver breaches are fully criminal, Dancho reports new...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
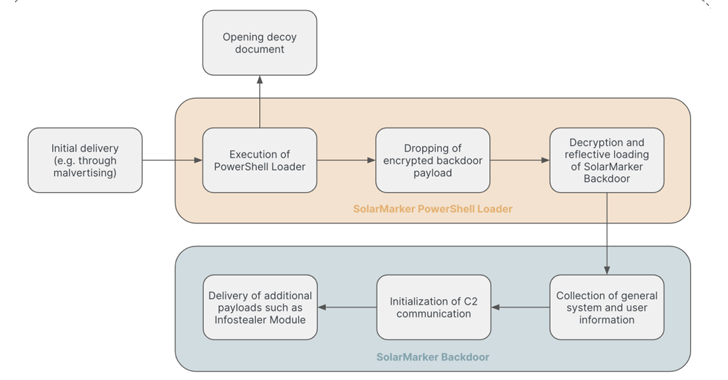 Data Breach
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
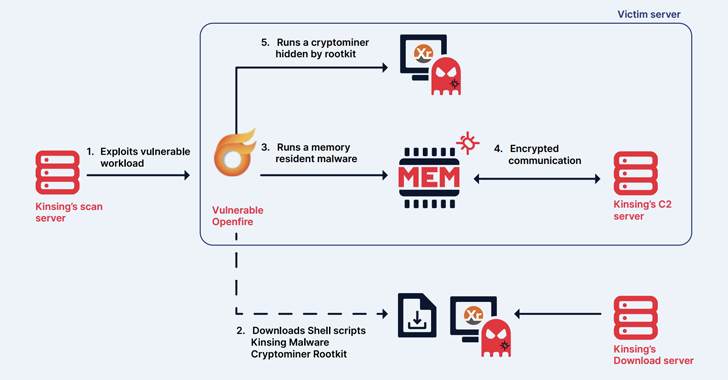 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Tutorials
TutorialsHow to implement Principle of Least Privilege(Cloud Security) in AWS, Azure, and GCP cloud
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
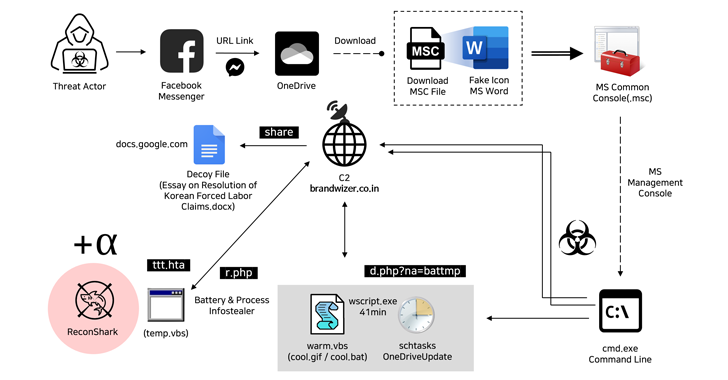
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
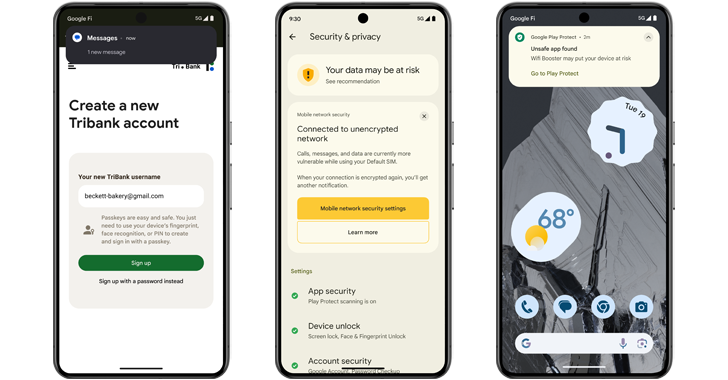
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions




