Featured News
-
Cyber Crime
Malware Injection Campaign: A Retaliation?
This week there have been several major malware injection campaigns against WordPress blogs and other php-based content management systems. This malware injection...
-
Privacy
Facebook: almost as popular as the Labour Party
[Update: according to Neil Rubenking, FB chat is now working again and it's no longer possible to view friend requests or chat...
-
Privacy
Facebook and privacy in the same sentence…
…but not in a good sense. Clearly there's a lot of confusion about the detail of Facebook's latest changes, as suggested by...
-
Scams
The Juror Scam
I recently received a summons for Jury duty. The date I was supposed to appear on coincides with a date I am...
-
Password
Protecting Against Password Reset Attacks
As I previously blogged today, the hacker who broke into Sarah Palin’s Yahoo account was convicted on two charges. The way that...
-
Cyber Crime
Geek with an edge: Gordon Snow, Asst. Dir. FBI Cyber Division
it’s anyone’s guess whether 24’s Jack Bauer would win in a faceoff against the new FBI Cyber Crimes Top Cop, Gordon Snow....
-
Privacy
Privacy: Lawsuit Alleges School Used Webcams to Lurk in Students’ Homes
Wow. File this under ‘how stupid thoughtless can any one person in a position of absolute power be…’ One school official abuses the built-in...
-
Privacy
Privacy: Can’t We All Just Get Along?
My assessment is that this could be a strong leap forward in support of Community Driven Open Source Privacy. Another assessment is...
-
Malware
European Cybercriminal Gangs Target Middle America SMBs
Better get your CFO to review UCC Article 4A and realign protocols with your business bank – The clear and present danger...
-
Cyber Crime
FBI Cyber Division Warns About Social Networking
In response to questions I heard this weekend from friends of mine about the ‘big picture’ relevance of the 1.5 million Facebook...
-
Cyber Crime
Facebook checked out, 1.5 million accounts overdue for password changes?
The Internet is abuzz with the announcement from Verisign’s iDefense Labs that a criminal hacker on a Russian forum who goes by...
-
Privacy
Community Driven Privacy and Facebook: PC / Mac / iPhone Dependent?
Is online privacy with Facebook technologically agnostic or can different rules apply if you post with your iPhone or other Smartphone? Are...
-
Malware
Another Look at Koobface: How It Infects Facebook Users
Earlier this month, we reported on the massive new Koobface campaign making the rounds through Facebook and how it tricked users into...
-
Malware
There’s Nothing of Value on My Computer
From time to time I hear people who don’t use antivirus software claim that it doesn’t matter, there isn’t anything of value...
-
Cyber Crime
Cybercrime and Cyberwarfare: Warnings Unheeded?
Last week Al Quaeda cyberterrorism attack information was declassified and made public. Today’s New York Times had an applicable editorial to whether...
-
Hacking
Smells Like Teen Spirit
I've just read a news item about a nine year old boy who has been accused of hacking into his school's computer...
-
Password
Good Password Practice: Not the Golden Globe Award
The Boston Globe suggested that changing passwords is a waste of time, based on their interpretation of an article by Herley Cormac. Cormac's...
-
Password
Please do not change your password – The Boston Globe
I find it hard to not be shocked at a headline like this… Then I remembered the recent top cybercrime city survey...
-
Social Engineering
Dangerous Zips + Responsible Disclosure
Mario Vuksan, Tomislav Pericin and Brian Karney have been talking...about vulnerabilities they've found in various compression formats ... as well as their...
-
Privacy
Top Four Privacy Hacks/Tips/Trends Of The Week
Clearly, anything which is posted online should be assumed to be eternal, written in stone tablets, and admissible for all time. For...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
 Data Breach
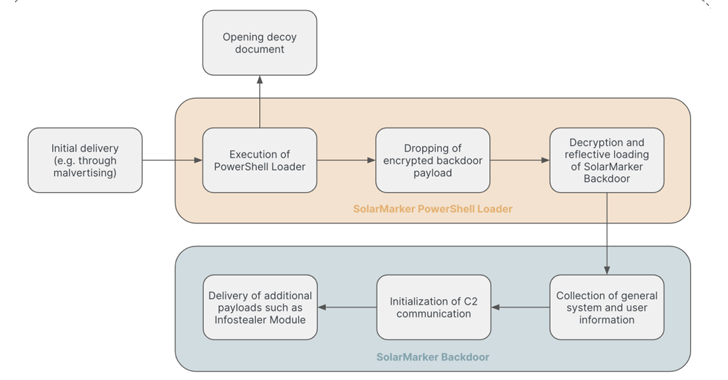
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
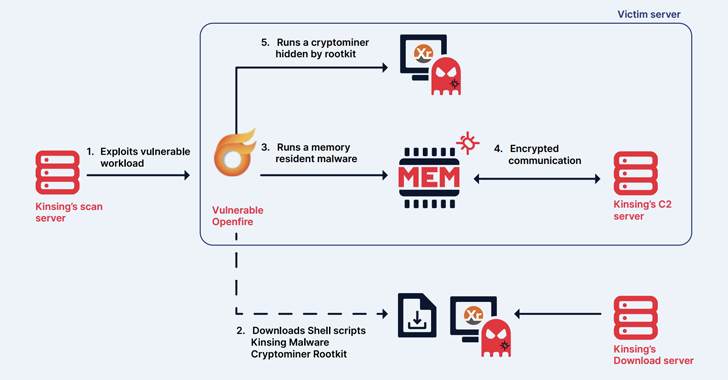
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
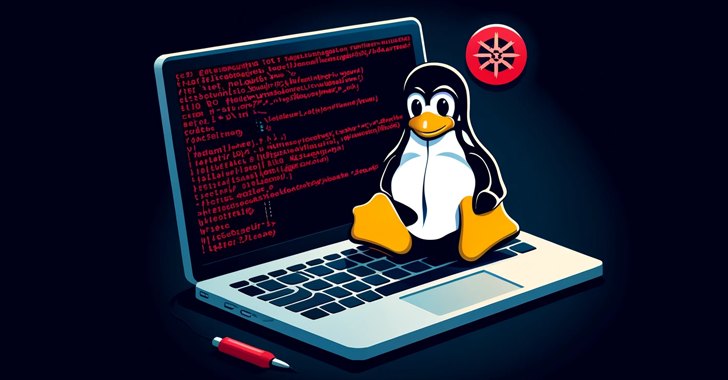
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Tutorials
TutorialsHow to implement Principle of Least Privilege(Cloud Security) in AWS, Azure, and GCP cloud
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
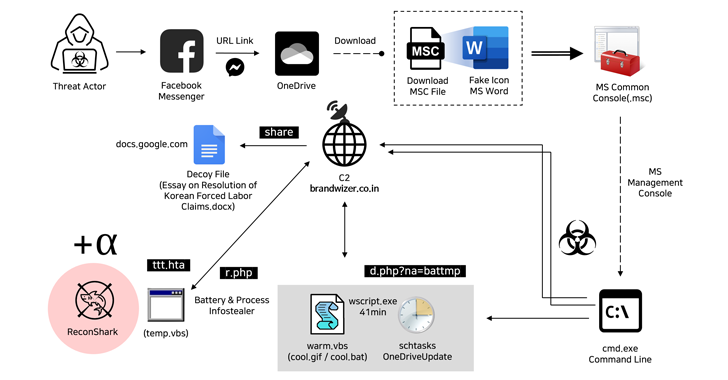
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
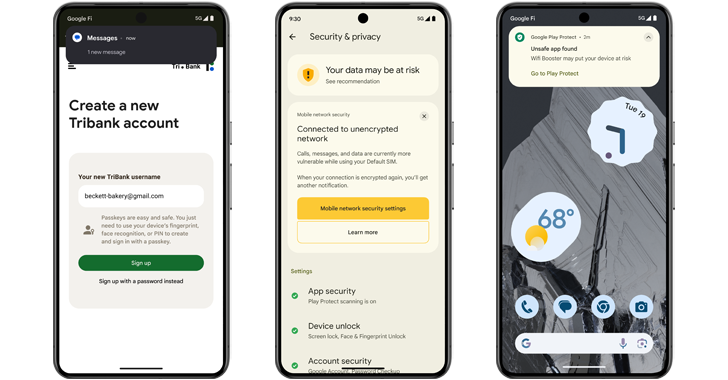
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions




