Featured News
-
Malware
September’s Global Threat Report
ESET released its Global Threat Report for the month of September, 2009, identifying the top ten threats seen during the month by...
-
Cyber Crime
Cybersecurity Awareness Month – Awareness for the Next Generation
“Now may I suggest some of the things we must do if we are to make the American dream a reality. First,...
-
Cyber Crime
Genial Geneva and a note for Francophones
Bonjour mes amis! Well, I am in Switzerland, and very close to the French border, for the Virus Bulletin conference – perhaps...
-
Malware
Do You Wear a Seatbelt?
Modern cars are designed with crumple zones. These crumple zones help to decrease the risk of death in a severe car accident....
-
Malware
CFET paper added to White Papers Page
We’ve just added my paper “The Game of the Name: Malware Naming, Shape Shifters and Sympathetic Magic” to the White Papers page. This...
-
Scams
Fake ICE and Hot ICE
Randy’s post yesterday about putting an “In Case of Emergency” (ICE) prefix in front of one or more entries in the contact...
-
Mobile Security
Got ICE?
ICE stands for “In Case of Emergency”. The idea is that you put ICE in front of the contact(s) on your phone...
-
Mac
Not all Mac users are naive about security
I’m often exasperated by blinkered mindsets in the Mac community, of the security-related kind that Randy highlighted in a recent blog. You might have...
-
Malware
Is Apple’s Snow Leopard Immune to Malware?
There is an interesting and humorous work of fiction at http://www.appleinsider.com/articles/09/09/07/inside_mac_os_x_snow_leopard_malware_protection.html. Humorous as long as you don’t believe it! The article starts...
-
Privacy
Armor for Social Butterflies
I was speaking with our friend David Perry at Trend Micro about the insecurity of social networking services and what steps users...
-
Mac
Mac Malware (again)
An interesting comment was made to my last blog on Snow Leopard, Mac malware and all that. I’ve approved the comment, but...
-
Scams
419 and Mac scams
I forwarded this to myself from another account yesterday because I thought it was one of the laziest 419 scam messages I’d...
-
Mac
Snow Leopard and Malware
Mac User has reported in a little more detail than I’ve seen elsewhere so far on the Trojan detection in Snow Leopard,...
-
Mac
Mad Macs: Beyond Blunderdome
I really ought to be working towards some really urgent deadlines, but I can’t resist a quick comment on the antimalware detection...
-
Social Engineering
Web Searches and Dangerous Ladies
I feel like the learned judge in the ’60s who asked, in the course of a trial, “What is a Beatle?” since...
-
Cyber Crime
M(b)ac(k) to the future
Mac security firm Intego blogged about Apple’s decision to include an antimalware component in Mac OS X 10.6 "Snow Leopard" and we...
-
Password
New White Papers
A number of new papers have been added to the white papers page: Cristian Borghello’s “Playing Dirty” is a translation of his...
-
Interview
Turkish Delight (2)
This is part two of a recent email interview with a Turkish web site, with part one made available here for the...
-
Social Engineering
(User) Education, Education, Education
Regular readers will be aware that, unlike many people in the security industry, people in this research team tend to be enthusiastic...
-
Interview
Turkish Delight
So, back in harness. I’ve been away for a couple of weeks: not on holiday as such, though I did take some...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
 Data Breach
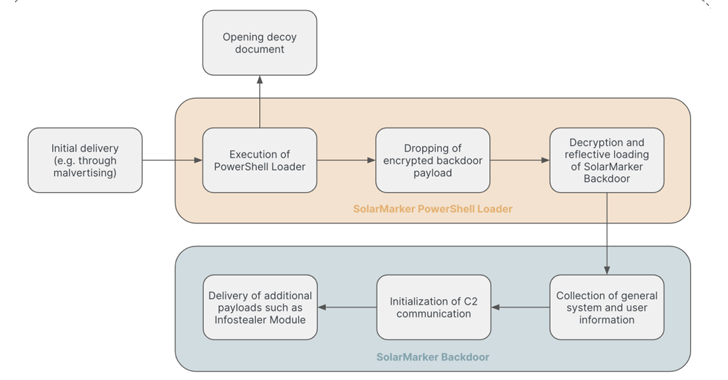
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
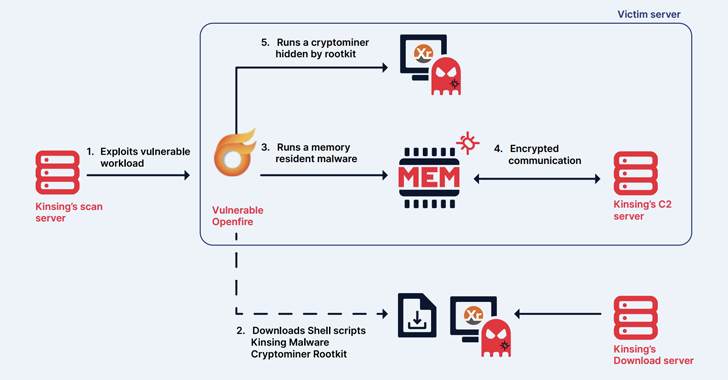
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Tutorials
TutorialsHow to implement Principle of Least Privilege(Cloud Security) in AWS, Azure, and GCP cloud
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
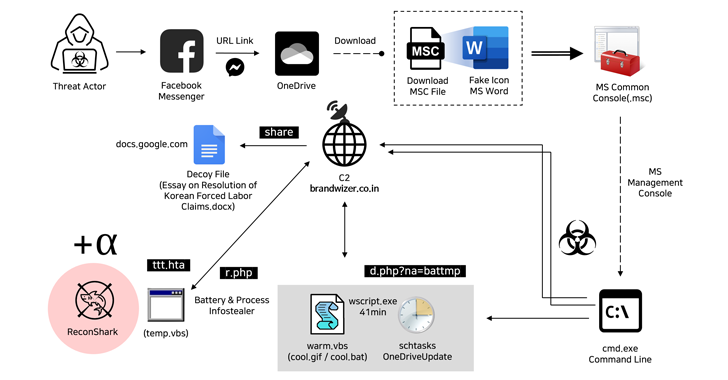
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
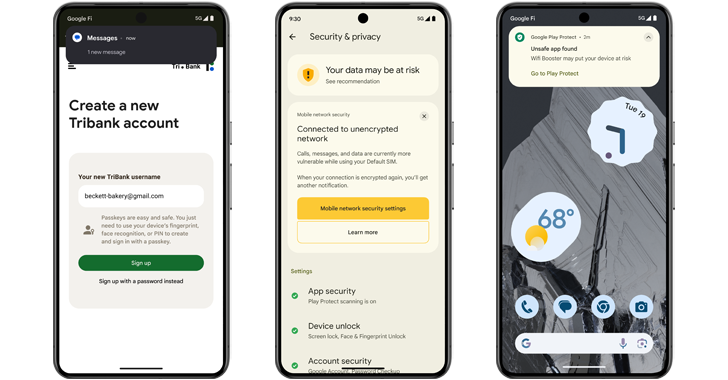
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions




