Featured News
-

 2.6KMalware
2.6KMalwareDirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in the country have been infected by...
-

 2.4KData Breach
2.4KData BreachFormer CIA Engineer Sentenced to 40 Years for Leaking Classified Documents
A former software engineer with the U.S. Central Intelligence Agency (CIA) has been sentenced to 40 years in prison by the Southern...
-

 1.9KMalware
1.9KMalwareCloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security
Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in its cybersecurity landscape. This breakthrough has been achieved through a...
-

 424Malware
424MalwareINTERPOL Arrests 31 in Global Operation, Identifies 1,900+ Ransomware-Linked IPs
An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the identification of 1,300 suspicious IP addresses and...
-

 2.5KData Breach
2.5KData BreachCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-
 3.2KData Security
3.2KData SecurityHacking Debian, Ubuntu, Redhat& Fedora servers using a single vulnerability in 2024
The recent discovery of a significant flaw in the GNU C Library (glibc), a fundamental component of major Linux distributions, has raised...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...
-

 193Cyber Attack
193Cyber AttackU.S. Feds Shut Down China-Linked “KV-Botnet” Targeting SOHO Routers
The U.S. government on Wednesday said it took steps to neutralize a botnet comprising hundreds of U.S.-based small office and home office...
-

 3.6KMalware
3.6KMalwareHeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since...
-
 2.0KMalware
2.0KMalwareWarning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during...
-
 1.1KVulnerabilities
1.1KVulnerabilitiesCISA Warns of Active Exploitation Apple iOS and macOS Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a high-severity flaw impacting iOS, iPadOS, macOS, tvOS, and watchOS to...
-

 945Vulnerabilities
945VulnerabilitiesAlert: Ivanti Discloses 2 New Zero-Day Flaws, One Under Active Exploitation
Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure products, one of which is said to...
-
 3.7KMalware
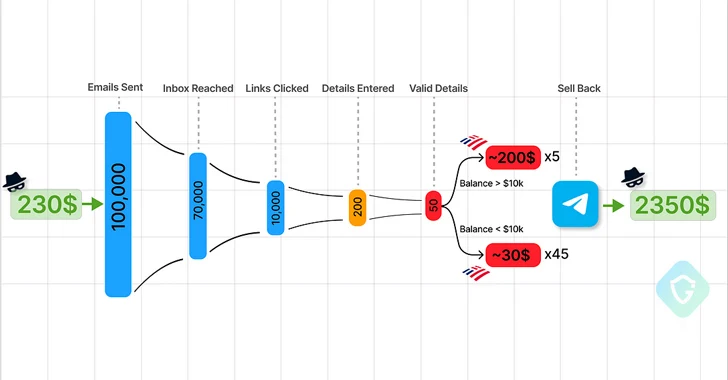
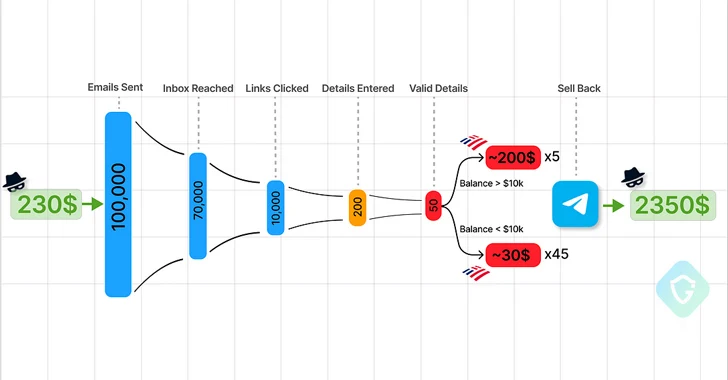
3.7KMalwareTelegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for...
-

 2.4KData Breach
2.4KData BreachThe SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules
The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure and...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesHackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver...
-

 4.4KMalware
4.4KMalwareBrazilian Feds Dismantle Grandoreiro Banking Trojan, Arresting Top Operatives
A Brazilian law enforcement operation has led to the arrest of several Brazilian operators in charge of the Grandoreiro malware. The Federal...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesURGENT: Upgrade GitLab – Critical Workspace Creation Flaw Allows File Overwrite
GitLab once again released fixes to address a critical security flaw in its Community Edition (CE) and Enterprise Edition (EE) that could...
-
 594Malware
594MalwareChina-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz
The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry of Defence and Foreign Affairs as part...
-

 553Data Breach
553Data BreachTop Security Posture Vulnerabilities Revealed
Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the field...
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




