Featured News
-

 3.6KVulnerabilities
3.6KVulnerabilitiesGitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials
GitHub has revealed that it has rotated some keys in response to a security vulnerability that could be potentially exploited to gain...
-

 944Vulnerabilities
944VulnerabilitiesCitrix, VMware, and Atlassian Hit with Critical Flaws — Patch ASAP!
Citrix is warning of two zero-day security vulnerabilities in NetScaler ADC (formerly Citrix ADC) and NetScaler Gateway (formerly Citrix Gateway) that are...
-
 3.2KVulnerabilities
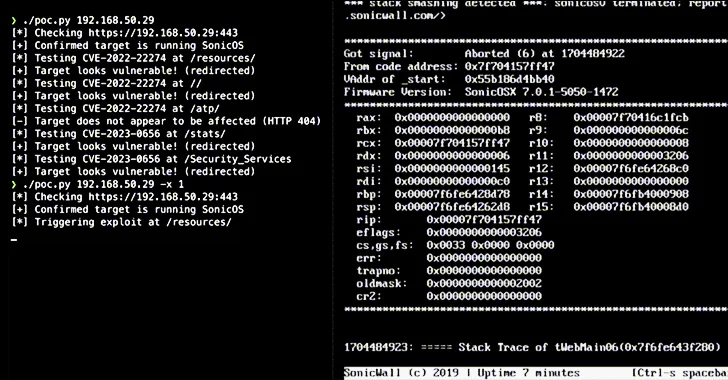
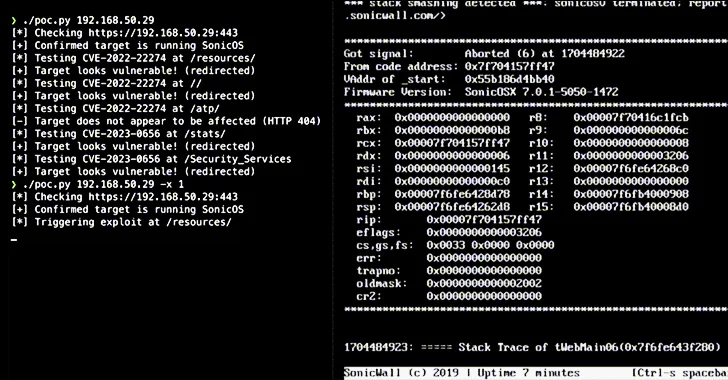
3.2KVulnerabilitiesAlert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now
Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCase Study: The Cookie Privacy Monster in Big Global Retail
Explore how an advanced exposure management solution saved a major retail industry client from ending up on the naughty step due to...
-

 1.1KMalware
1.1KMalwareRemcos RAT Spreading Through Adult Games in New Attack Wave
The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games...
-

 807Malware
807MalwareHackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer
Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy an open-source information stealer called Phemedrone Stealer....
-

 4.0KIncidents
4.0KIncidentsHow to exploit Windows Defender Antivirus to infect a device with malware
Trend Micro’s recent threat hunting efforts have uncovered active exploitation of CVE-2023-36025, a vulnerability in Microsoft Windows Defender SmartScreen, by a new...
-
 1.8KVulnerabilities
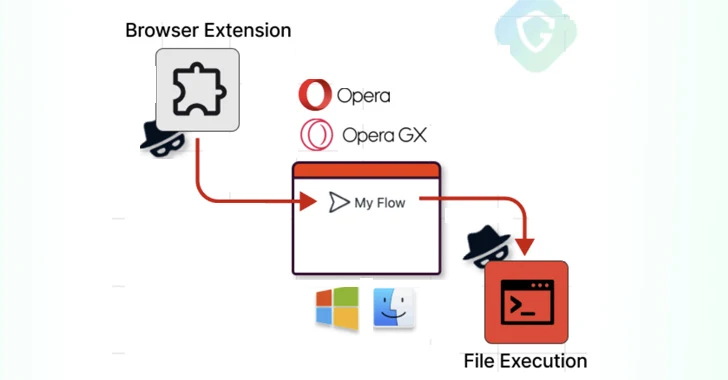
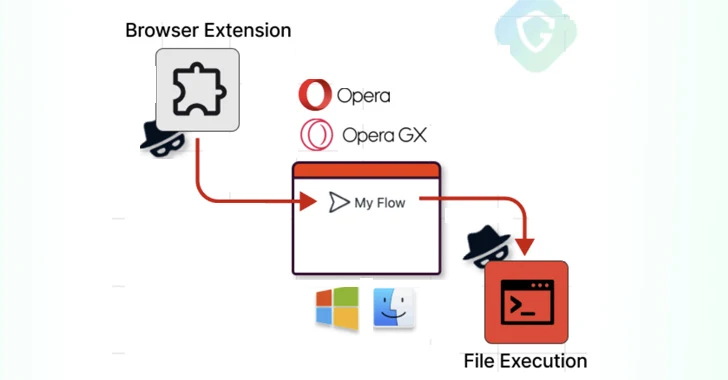
1.8KVulnerabilitiesOpera MyFlaw Bug Could Let Hackers Run ANY File on Your Mac or Windows
Cybersecurity researchers have disclosed a now-patched security flaw in the Opera web browser for Microsoft Windows and Apple macOS that could be...
-

 802Vulnerabilities
802VulnerabilitiesHigh-Severity Flaws Uncovered in Bosch Thermostats and Smart Nutrunners
Multiple security vulnerabilities have been disclosed in Bosch BCC100 thermostats and Rexroth NXA015S-36V-B smart nutrunners that, if successfully exploited, could allow attackers...
-
 1.4KVulnerabilities
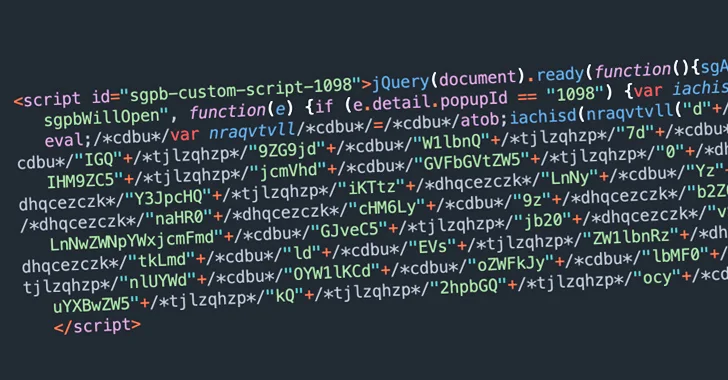
1.4KVulnerabilitiesBalada Injector Infects Over 7,100 WordPress Sites Using Plugin Vulnerability
Thousands of WordPress sites using a vulnerable version of the Popup Builder plugin have been compromised with a malware called Balada Injector....
-
 4.2KCyber Attack
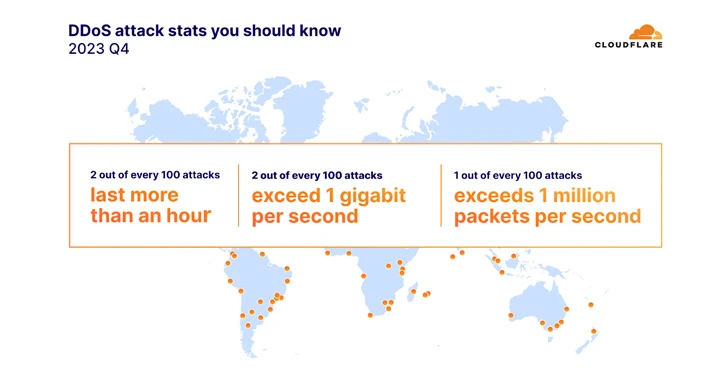
4.2KCyber AttackDDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023
The environmental services industry witnessed an “unprecedented surge” in HTTP-based distributed denial-of-service (DDoS) attacks, accounting for half of all its HTTP traffic....
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have had the involvement of the Russia-linked Sandworm hacking...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesCritical RCE Vulnerability Uncovered in Juniper SRX Firewalls and EX Switches
Juniper Networks has released updates to fix a critical remote code execution (RCE) vulnerability in its SRX Series firewalls and EX Series...
-
 2.2KData Breach
2.2KData Breach29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services
A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,” netting them over $2 million (€1.8 million)...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesNation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families
As many as five different malware families were deployed by suspected nation-state actors as part of post-exploitation activities leveraging two zero-day vulnerabilities...
-
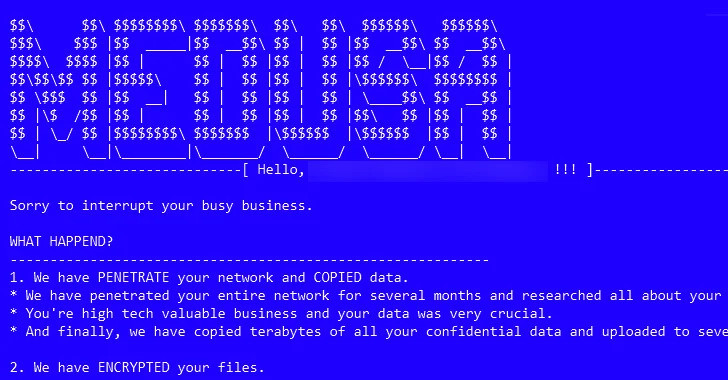
 3.4KMalware
3.4KMalwareMedusa Ransomware on the Rise: From Data Leaks to Multi-Extortion
The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak site...
-

 2.8KMalware
2.8KMalwareCryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks
Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners within targeted environments....
-
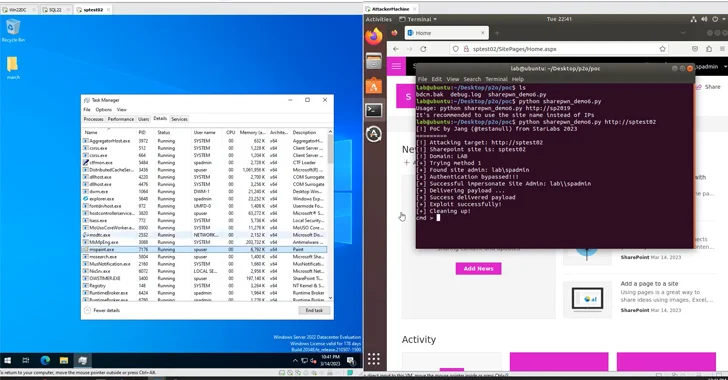
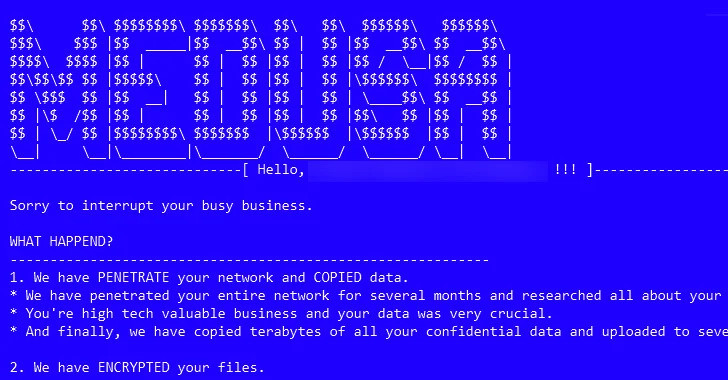
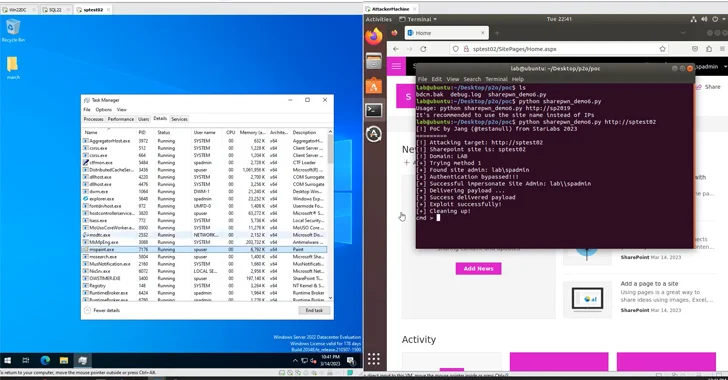 1.5KVulnerabilities
1.5KVulnerabilitiesAct Now: CISA Flags Active Exploitation of Microsoft SharePoint Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security vulnerability impacting Microsoft SharePoint Server to its Known Exploited...
-
 2.7KLeaks
2.7KLeaksYouTube Not Working on iPhone? Here’s How to Fix It
If the YouTube app on your iPhone is crashing or will not open, there are various fixes you can try, such as...
-

 5.0KLeaks
5.0KLeaksWhy is the iPhone Force Restart Not Working?
If the iPhone force restart does not work as intended, there may be an issue with the iOS system. To address this,...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




