Search results for "Google"
-

 2.1KVulnerabilities
2.1KVulnerabilitiesZero-Day Alert: Google Chrome Under Active Attack, Exploiting New Vulnerability
Google has rolled out security updates to fix seven security issues in its Chrome browser, including a zero-day that has come under...
-
 4.8KData Breach
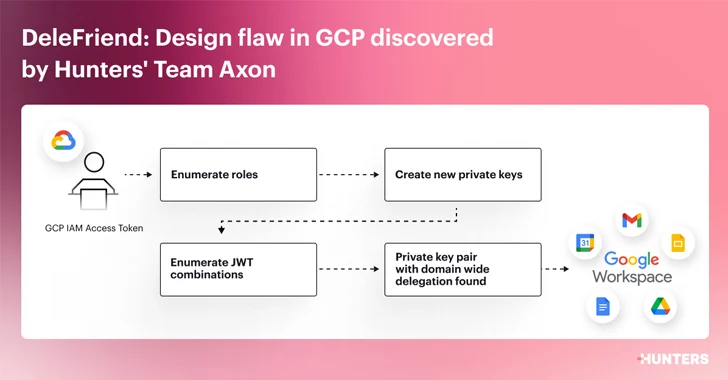
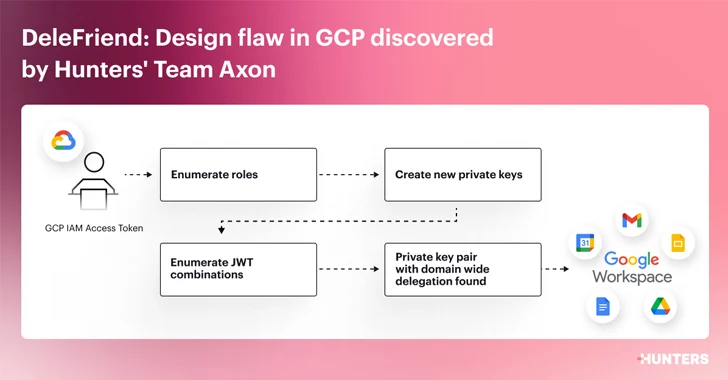
4.8KData BreachDesign Flaw in Google Workspace Could Let Attackers Gain Unauthorized Access
Cybersecurity researchers have detailed a “severe design flaw” in Google Workspace’s domain-wide delegation (DWD) feature that could be exploited by threat actors...
-
 1.4KMalware
1.4KMalwareHow hrserver.dll stealthy webshell can mimic Google’s Web Traffic to hide and compromise networks
In a striking revelation shaking the cybersecurity world, researchers have unearthed a sophisticated web shell, dubbed ‘HrServ,’ hidden within a seemingly innocuous...
-
 3.6KMalware
3.6KMalwareBeware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such...
-

 1.7KData Security
1.7KData SecurityYour Google Cloud Security Might Be at Risk. Hacking GCP via Google Workspace flaw
In a startling revelation, Bitdefender, a leading cybersecurity firm, has disclosed a series of sophisticated attack methods that could significantly impact users...
-

 2.6KMalware
2.6KMalwareSecuriDropper: New Android Dropper-as-a-Service Bypasses Google’s Defenses
Cybersecurity researchers have shed light on a new dropper-as-a-service (DaaS) for Android called SecuriDropper that bypasses new security restrictions imposed by Google...
-

 4.5KMalware
4.5KMalwareGoogle Warns How Hackers Could Abuse Calendar Service as a Covert C2 Channel
Google is warning of multiple threat actors sharing a public proof-of-concept (PoC) exploit that leverages its Calendar service to host command-and-control (C2)...
-
 953Vulnerabilities
953VulnerabilitiesGoogle Expands Its Bug Bounty Program to Tackle Artificial Intelligence Threats
Google has announced that it’s expanding its Vulnerability Rewards Program (VRP) to compensate researchers for finding attack scenarios tailored to generative artificial...
-
 606Cyber Attack
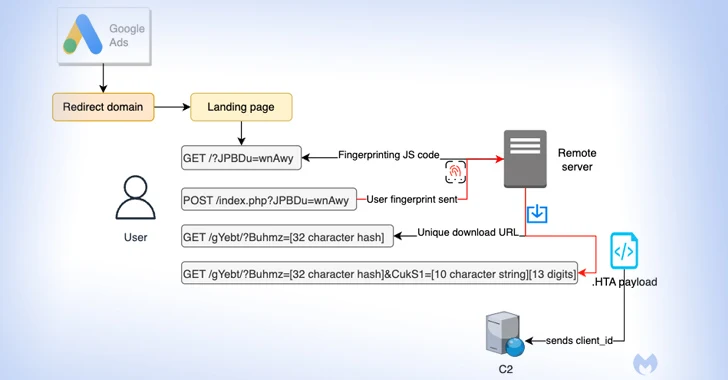
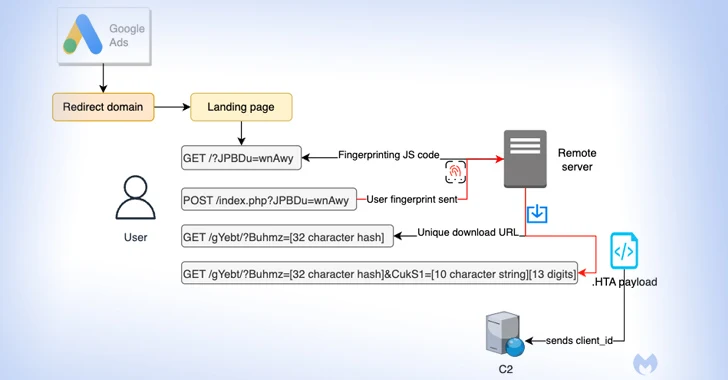
606Cyber AttackMalvertisers Using Google Ads to Target Users Searching for Popular Software
Details have emerged about a malvertising campaign that leverages Google Ads to direct users searching for popular software to fictitious landing pages...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesGoogle TAG Detects State-Backed Threat Actors Exploiting WinRAR Flaw
A number of state-back threat actors from Russia and China have been observed exploiting a recent security flaw in the WinRAR archiver...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesHow Google Chrome Vulnerability can Put Millions of Users in Danger – Safeguard Your Data Now!
In-depth Analysis: Navigating the Perils of CVE-2023-5218 in Google Chrome The digital realm, while offering boundless possibilities, is also a fertile ground...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesUpdate Chrome Now: Google Releases Patch for Actively Exploited Zero-Day Vulnerability
Google on Wednesday rolled out fixes to address a new actively exploited zero-day in the Chrome browser. Tracked as CVE-2023-5217, the high-severity...
-
 672Malware
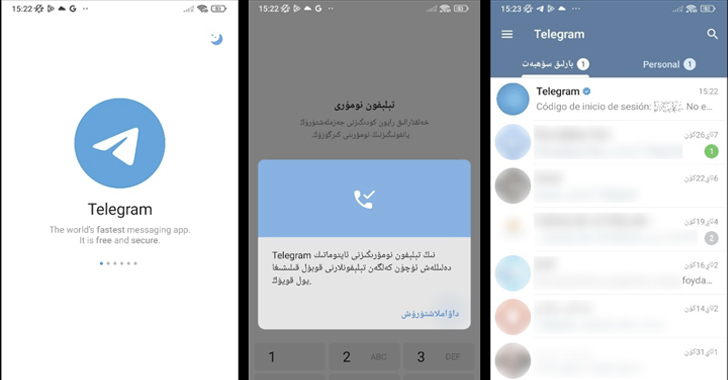
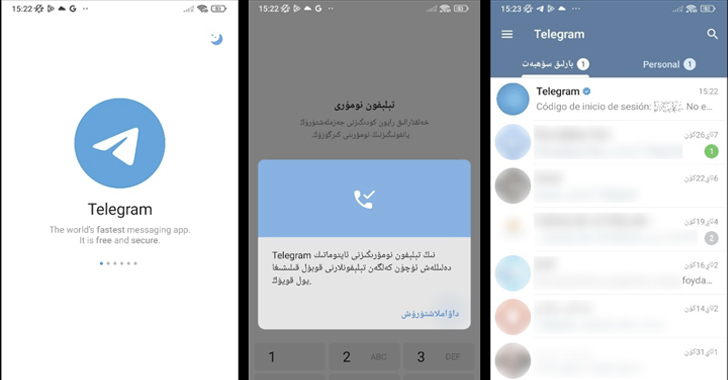
672MalwareMillions Infected by Spyware Hidden in Fake Telegram Apps on Google Play
Spyware masquerading as modified versions of Telegram have been spotted in the Google Play Store that’s designed to harvest sensitive information from...
-
 1.7KMalware
1.7KMalwareMalicious Apps Use Sneaky Versioning Technique to Bypass Google Play Store Scanners
Threat actors are leveraging a technique called versioning to evade Google Play Store’s malware detections and target Android users. “Campaigns using versioning...
-

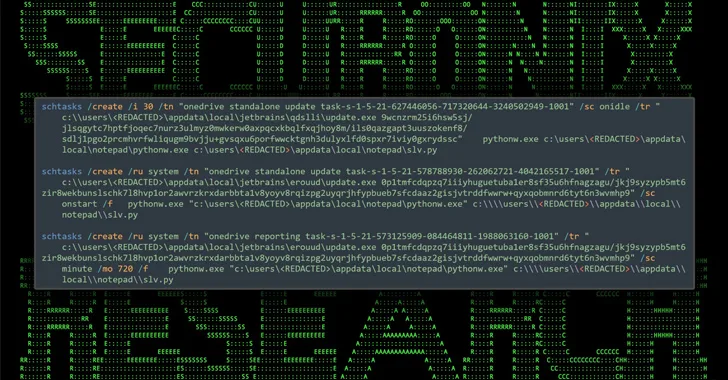
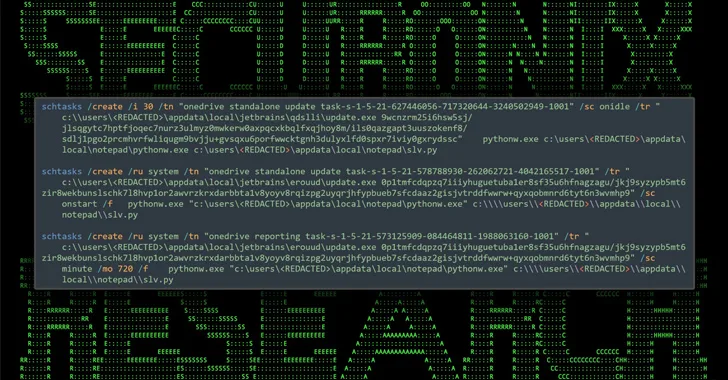
 4.7KMalware
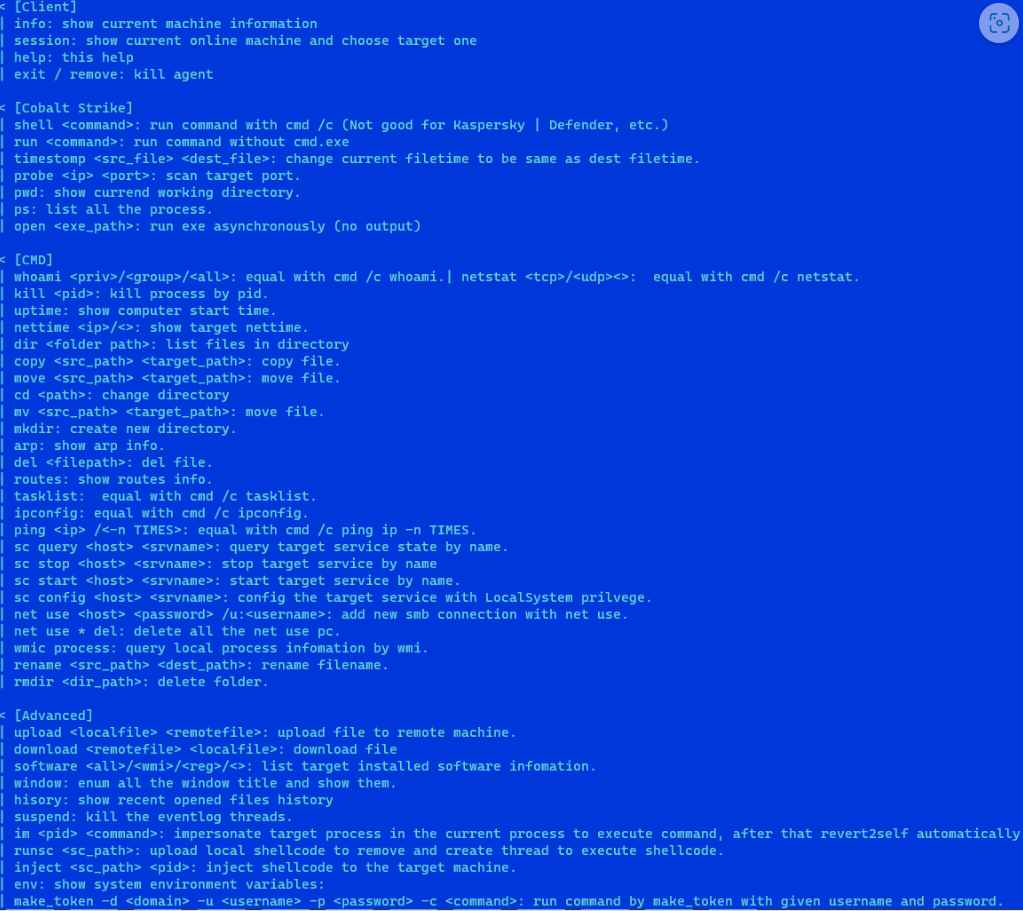
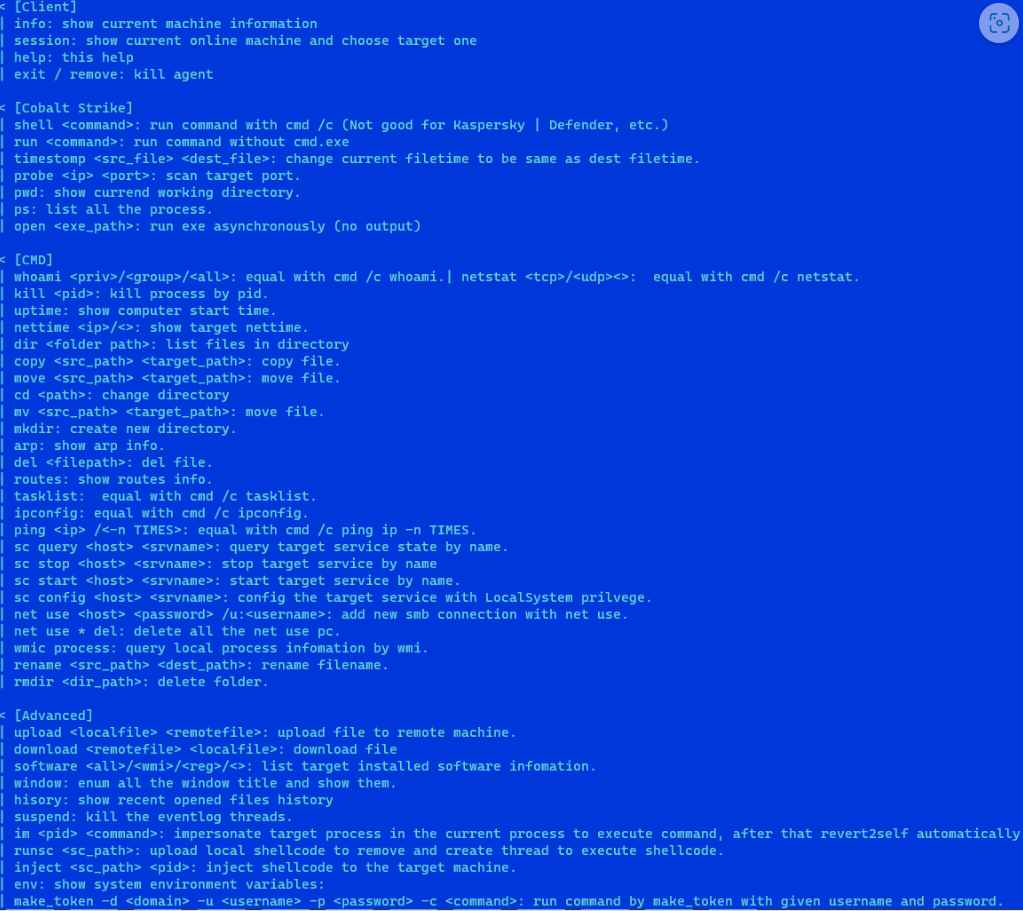
4.7KMalwareHacker Using Google and Bing ads to Deliver Weaponized IT tools
The latest research discovered malvertising campaigns abusing Google and Bing ads to target users seeking certain IT tools and deploying ransomware. This...
-

 347Malware
347MalwareSophisticated BundleBot Malware Disguised as Google AI Chatbot and Utilities
A new malware strain known as BundleBot has been stealthily operating under the radar by taking advantage of .NET single-file deployment techniques,...
-

 4.7KMalware
4.7KMalwareTwo Spyware Apps on Google Play with 1.5 Million Users Sending Data to China
Two file management apps on the Google Play Store have been discovered to be spyware, putting the privacy and security of up...
-

 955Cyber Attack
955Cyber AttackGoogle Releases Android Patch Update for 3 Actively Exploited Vulnerabilities
Google has released its monthly security updates for the Android operating system, addressing 46 new software vulnerabilities. Among these, three vulnerabilities have...
-
 2.8KMalware
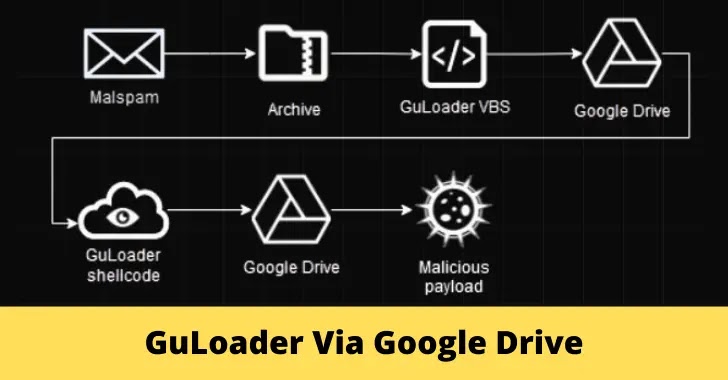
2.8KMalwareFully Encrypted GuLoader Uses Google Drive to Download Payloads
Antivirus products continuously advance to combat evolving threats, prompting malware developers to create new bypassing techniques like “packing” and “crypting,” GuLoader is...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesGUAC 0.1 Beta: Google’s Breakthrough Framework for Secure Software Supply Chains
Google on Wednesday announced the 0.1 Beta version of GUAC (short for Graph for Understanding Artifact Composition) for organizations to secure their...
-
 3.7KData Security
3.7KData SecurityHow to Secure containers images with open source Bazel tool plugin Rules_oci from Google
Rules_oci, an open-sourced Bazel plugin (“ruleset”) that makes it easier and more secure to create container images using Bazel, has been made...






