Search results for "IBM"
-

 332Vulnerabilities
332VulnerabilitiesMultiple Vulnerabilities in IBM QRadar SIEM Allows Attackers to Escalate Privileges and to Execute Arbitrary Commands
Multiple Vulnerabilities found in IBM QRadar chained together allows a remote attacker to bypass authentication and to execute arbitrary commands with root...
-

 332Data Security
332Data SecurityIBM improves its security and prohibits the use of USB drives throughout the company
IBM recently banned all removable storage, throughout the company; this is a new policy that aims to avoid financial and reputational damage...
-

 299Geek
299GeekIBM Developing World’s Tiniest Computer Smaller than a Grain of Salt
At Think 2018, IBM has announced developing world’s tiniest computer that will cost less than ten cents to manufacture and can monitor,...
-
 461Vulnerabilities
461Vulnerabilities6 Critical RCE and Buffer Overflow Vulnerabilities in IBM Informix Dynamic Server and Informix Open Admin Tool
IBM Informix Dynamic Server and Informix Open Admin Tool contains 6 Critical Vulnerabilities including RCE and a Buffer overflow in HEAP. IBM Informix...
-

 167Malware
167MalwareIBM Warns Customers That Some of Its USB Flash Drives May Contain Malware
IBM has issued a security alert last week, warning customers that some USB flash drives shipped with IBM Storwize products may contain...
-

 369Data Security
369Data SecurityIBM Sent Off USB Sticks Infected with Malware
A new warning has been issued by IBM and the situation seems to be rather serious. According to the firm, there are...
-

 275Data Security
275Data SecurityAndroid Malware Developer Contacts IBM; Demands Blog Post Correction
IBM contacted by Bilal Bot Developer for Publishing Incorrect Details about his Malware. It’s definitely one crazy turn of events. The supposed...
-

 185Geek
185GeekTanmay, World’s Youngest IBM Watson Programmer, Started Coding At The Age Of Five
Short Bytes: Today, I’m going to tell you about 12-year-old app developer Tanmay Bakshi, who is making headlines after his recent talk...
-
 321Geek
321GeekHere’s Your Chance to Use IBM’s Remotely Accessible Quantum Computer
Quantum Computing- No More a Thing of Distant Future — IBM wants us all to use it remotely accessible Quantum Computer… for free!...
-
 162Geek
162GeekIndian Coder Shows How To Make IBM’s $1.4 million Randomized App In 4 Minutes
Short Bytes: An Indian techie, Sandesh Suvarna, has shown how to make IBM’s $1.4 million Randomizer app within 4 minutes. IBM made...
-

 105Data Security
105Data SecurityIBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...
-

 279Geek
279GeekIBM’s New Open Source OMR Project Will Boost Python, Ruby, And Other Languages
Short Bytes: IBM is taking the parts from its JVM project by separating it from Java and making them usable for any...
-
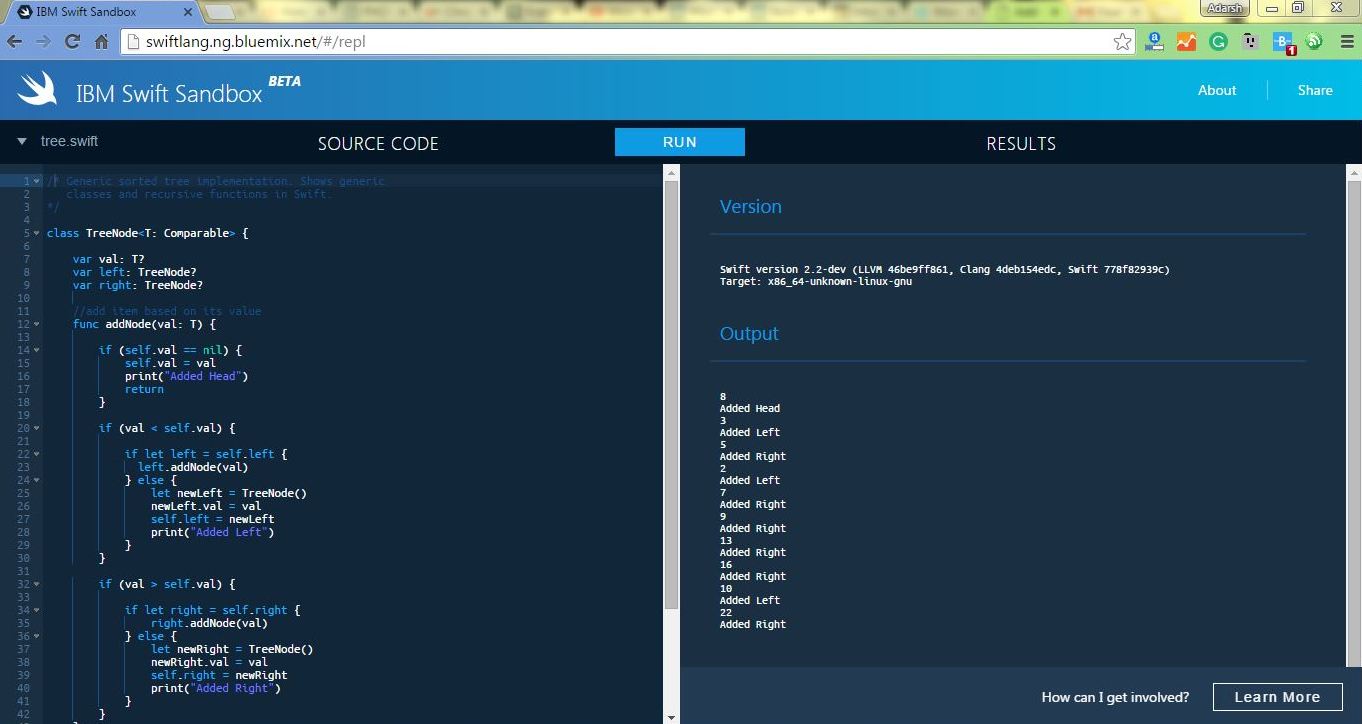
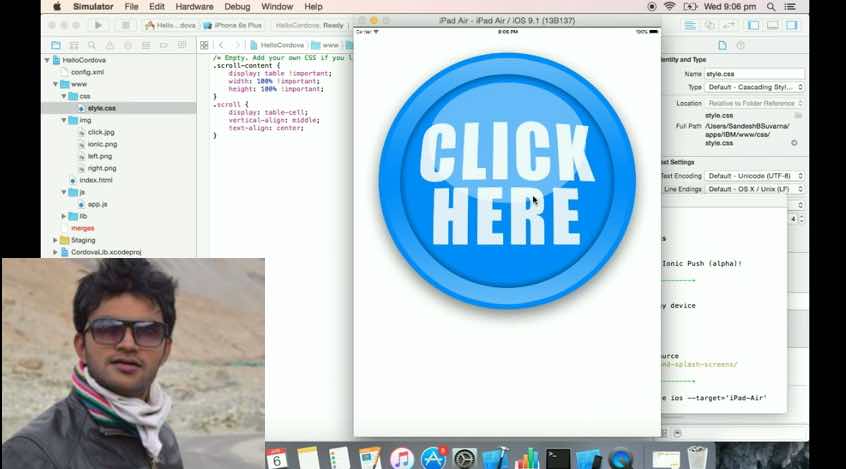
 260Geek
260GeekNow Run Apple’s Swift Programming Language Online In IBM Swift Sandbox
Short Bytes: To make learning Apple’s programming language Swift easier, IBM has launched an online Swift Sandbox. Here, you can write and...
-

 307Data Security
307Data SecurityHackers Use Malware To Steal Cisco, IBM and Oracle Certification Manager
A certification tracking system (Credential Manager System) used by companies like Cisco, F5, IBM and Oracle has faced a data breach and...
-

 168News
168NewsIBM’s Security Report Suggests Users To Avoid TOR
Security researchers have suggested that corporations and enterprises should block all of the encrypted and anonymised traffic that they are receiving through...
-
 276Hacked
276HackedIBM: Hackers are Using Tor Network More Frequently For Launching Hacking Attacks
Short Bytes: A report from IBM researchers has shown that the use of Tor network is on the rise. As a result, the growth...
-
 205Geek
205GeekIBM Open Sources 50 Projects, Launches developerWorks Open
Short Bytes: Technology pioneer IBM has open sourced 50 tools and apps. These tools cover a large interest area varying from Cloud, Analytics, IoT,...
-

 125Mobile Security
125Mobile SecurityMobile security: IBM/Ponemon study finds enterprise app security weaknesses
Nearly 40 percent of large companies - including a significant number in the Fortune 500 - are not taking necessary precautions to...
-

 96Cyber Crime
96Cyber CrimeThe ‘Digital Guardian’: IBM’s security expert explains why ‘Steve’ might watch your eating habits to keep you secure
Here, J.R. Rao, IBM Director for Security Research, explains why the idea of a digital guardian who watches for unusual behavior is...
-

 134News
134NewsIBM Sued by Its Own Shareholder for Cooperating with the NSA
It seems as if those business which bowed down in front of NSA are now facing a backlash. That’s what we can...
-

 126Android
126AndroidNew IBM system adds “robust” security to smartphone banking and shopping
Cybercriminals are already targeting mobile banking apps as a “way in” to customer accounts – as witnessed in ESET’s discovery of a...






