Featured News
-

 2.3KMalware
2.3KMalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
The Iranian threat actor known as MuddyWater has been attributed to a new command-and-control (C2) infrastructure called DarkBeatC2, becoming the latest such...
-

 1.7KCyber Attack
1.7KCyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
Palo Alto Networks is warning that a critical flaw impacting PAN-OS software used in its GlobalProtect gateways is being actively exploited in...
-

 3.0KMalware
3.0KMalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
Cybersecurity researchers have discovered a credit card skimmer that’s concealed within a fake Meta Pixel tracker script in an attempt to evade...
-

 1.5KData Breach
1.5KData BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday issued an emergency directive (ED 24-02) urging federal agencies to hunt for...
-

 2.6KMalware
2.6KMalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
A threat actor tracked as TA547 has targeted dozens of German organizations with an information stealer called Rhadamanthys as part of an...
-

 637Vulnerabilities
637VulnerabilitiesPython’s PyPI Reveals Its Secrets
GitGuardian is famous for its annual State of Secrets Sprawl report. In their 2023 report, they found over 10 million exposed passwords,...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesFortinet Rolls Out Critical Security Patches for FortiClientLinux Vulnerability
Fortinet has released patches to address a critical security flaw impacting FortiClientLinux that could be exploited to achieve arbitrary code execution. Tracked...
-

 3.7KMalware
3.7KMalware‘eXotic Visit’ Spyware Campaign Targets Android Users in India and Pakistan
An active Android malware campaign dubbed eXotic Visit has been primarily targeting users in South Asia, particularly those in India and Pakistan,...
-

 4.3KMalware
4.3KMalwareRaspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March...
-
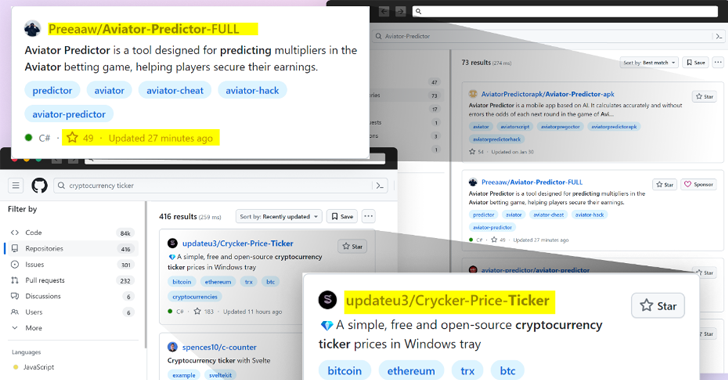
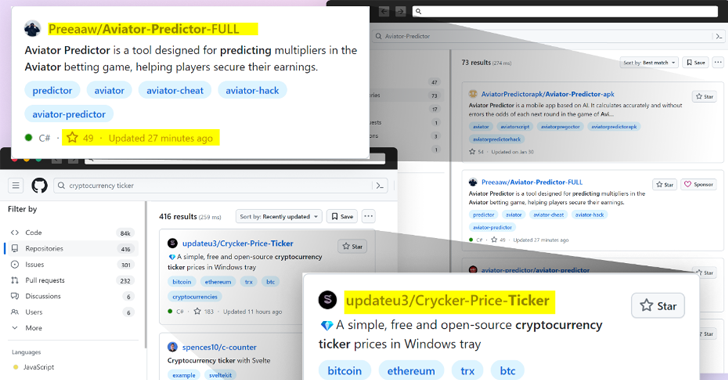 4.9KMalware
4.9KMalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
Threat actors are now taking advantage of GitHub’s search functionality to trick unsuspecting users looking for popular repositories into downloading spurious counterparts...
-
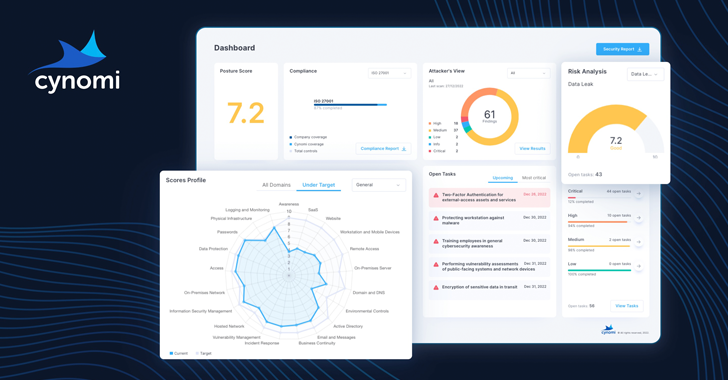
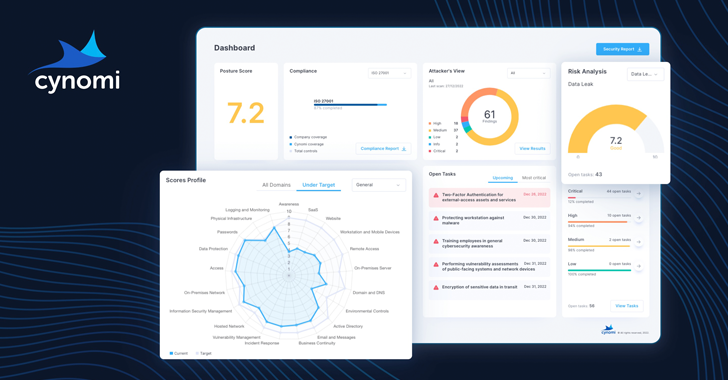 665Vulnerabilities
665VulnerabilitiesHands-on Review: Cynomi AI-powered vCISO Platform
The need for vCISO services is growing. SMBs and SMEs are dealing with more third-party risks, tightening regulatory demands and stringent cyber...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
Microsoft has released security updates for the month of April 2024 to remediate a record 149 flaws, two of which have come...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesCritical ‘BatBadBut’ Rust Vulnerability Exposes Windows Systems to Attacks
A critical security flaw in the Rust standard library could be exploited to target Windows users and stage command injection attacks. The...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesHow to hack a LG Smart TV via vulnerabilities in LG WebOS?
In a recent disclosure, cybersecurity firm Bitdefender has revealed a series of critical vulnerabilities within LG’s WebOS, the operating system used in...
-
 3.4KVulnerabilities
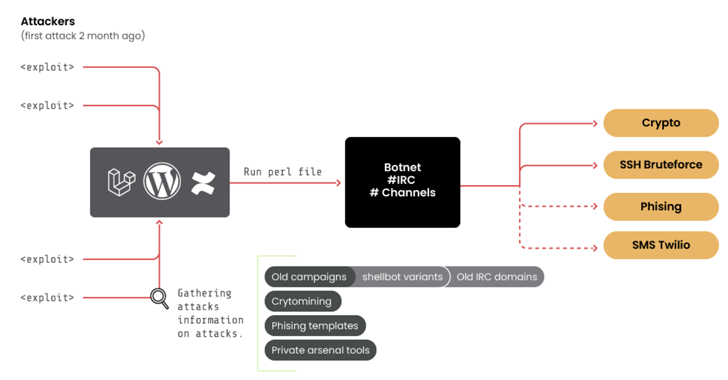
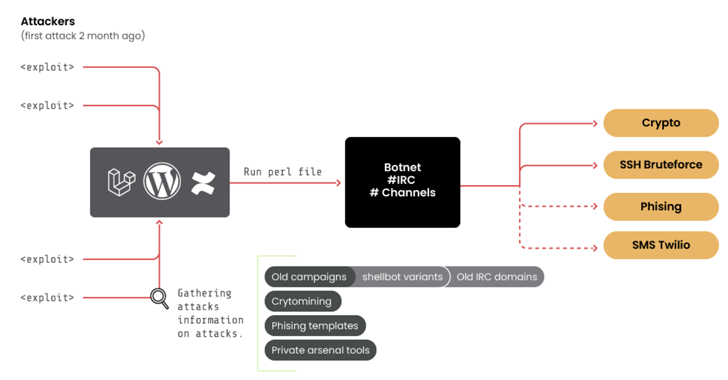
3.4KVulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
A threat group of suspected Romanian origin called RUBYCARP has been observed maintaining a long-running botnet for carrying out crypto mining, distributed...
-

 3.7KMalware
3.7KMalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
Human rights activists in Morocco and the Western Sahara region are the targets of a new threat actor that leverages phishing attacks...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesResearchers Discover LG Smart TV Vulnerabilities Allowing Root Access
Multiple security vulnerabilities have been disclosed in LG webOS running on its smart televisions that could be exploited to bypass authorization and...
-

 3.3KMalware
3.3KMalwareCL0P’s Ransomware Rampage – Security Measures for 2024
2023 CL0P Growth Emerging in early 2019, CL0P was first introduced as a more advanced version of its predecessor the ‘CryptoMix’ ransomware,...
-

 2.5KMalware
2.5KMalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




