Search results for "malware"
-
 3.1KMalware
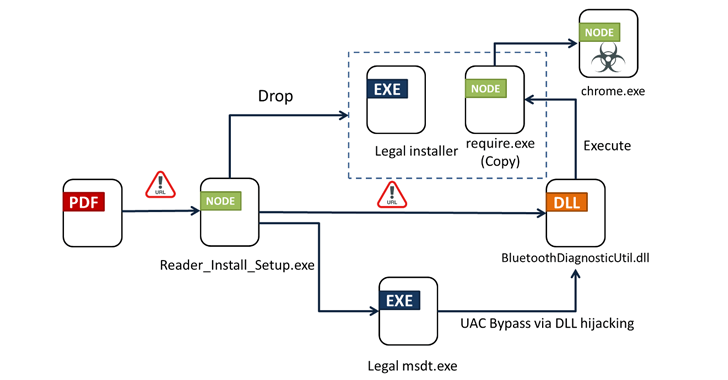
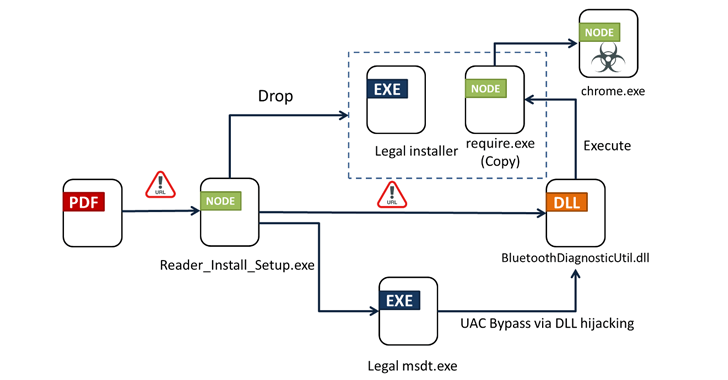
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
-

 1.8KMalware
1.8KMalwareVietnam-Based Hackers Steal Financial Data Across Asia with Malware
A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest...
-

 165Malware
165MalwareNew Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. “The...
-
 4.3KMalware
4.3KMalwareChina-linked Hackers Deploy New ‘UNAPIMON’ Malware for Stealthy Operations
A threat activity cluster tracked as Earth Freybug has been observed using a new malware called UNAPIMON to fly under the radar....
-

 4.9KMalware
4.9KMalwareDetecting Windows-based Malware Through Better Visibility
Despite a plethora of available security solutions, more and more organizations fall victim to Ransomware and other threats. These continued threats aren’t...
-

 4.6KMalware
4.6KMalwareHackers Target macOS Users with Malicious Ads Spreading Stealer Malware
Malicious ads and bogus websites are acting as a conduit to deliver two different stealer malware, including Atomic Stealer, targeting Apple macOS...
-

 4.1KMalware
4.1KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesAndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that’s used to target Laravel applications and steal sensitive data....
-
 1.6KMalware
1.6KMalwareFrom Deepfakes to Malware: AI’s Expanding Role in Cyber Attacks
Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules....
-

 2.1KMalware
2.1KMalwareSuspected Russian Data-Wiping ‘AcidPour’ Malware Targeting Linux x86 Devices
A new variant of a data wiping malware called AcidRain has been detected in the wild that’s specifically designed for targeting Linux...
-
 2.8KMalware
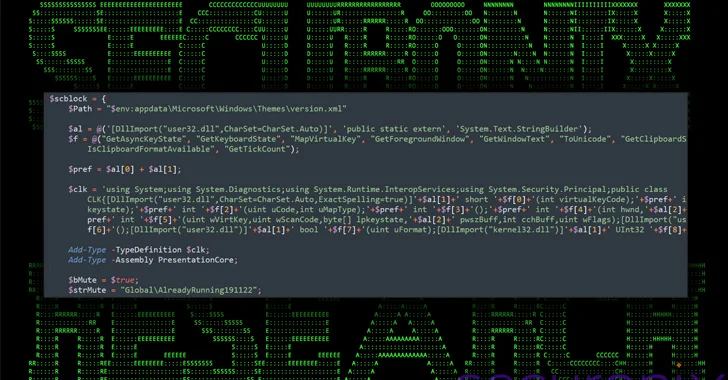
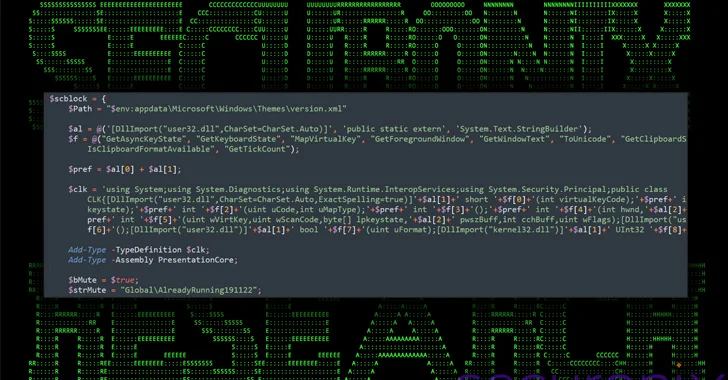
2.8KMalwareNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...
-
 4.2KMalware
4.2KMalwareHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-

 2.2KMalware
2.2KMalwareAnde Loader Malware Targets Manufacturing Sector in North America
The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans...
-
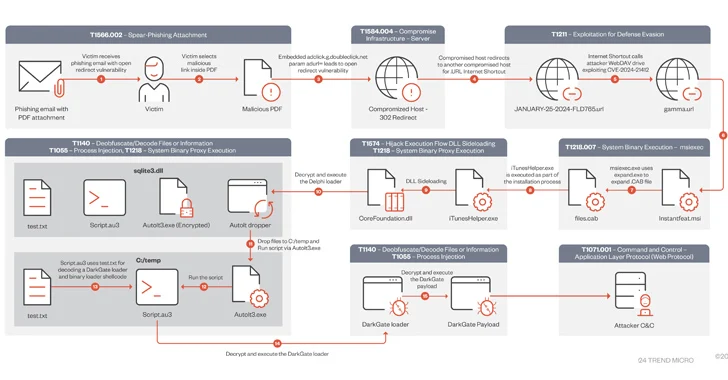
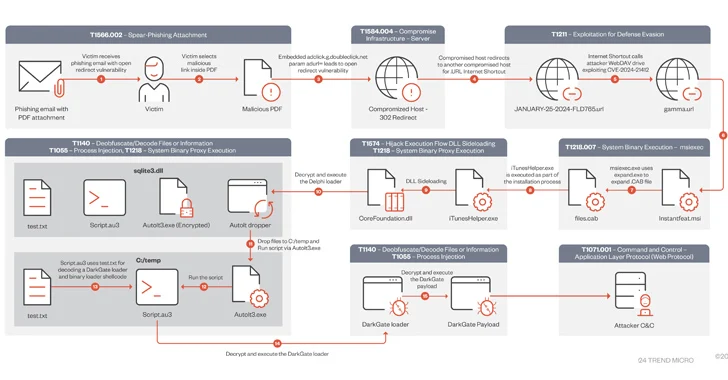 4.5KVulnerabilities
4.5KVulnerabilitiesDarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack
A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus...
-
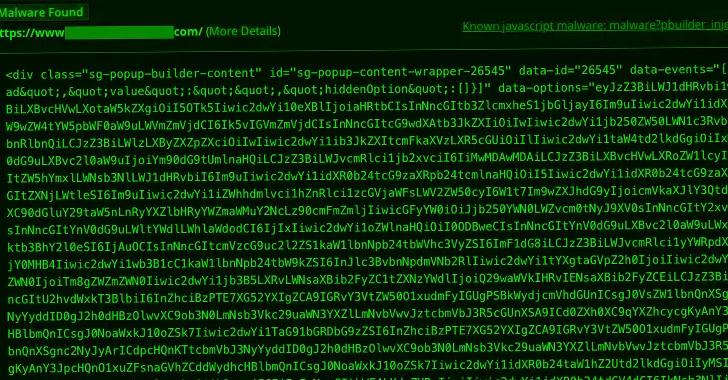
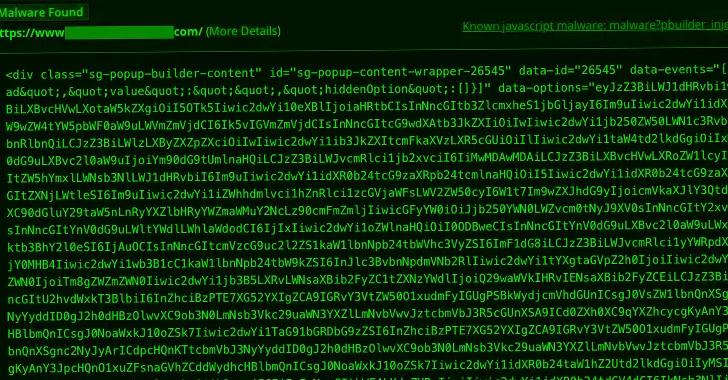 580Cyber Attack
580Cyber AttackMalware Campaign Exploits Popup Builder WordPress Plugin to Infect 3,900+ Sites
A new malware campaign is leveraging a high-severity security flaw in the Popup Builder plugin for WordPress to inject malicious JavaScript code....
-
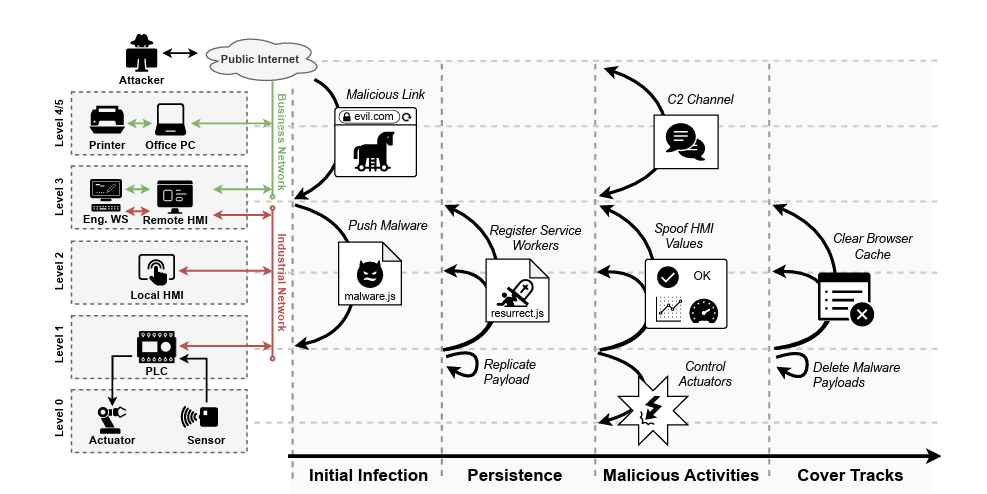
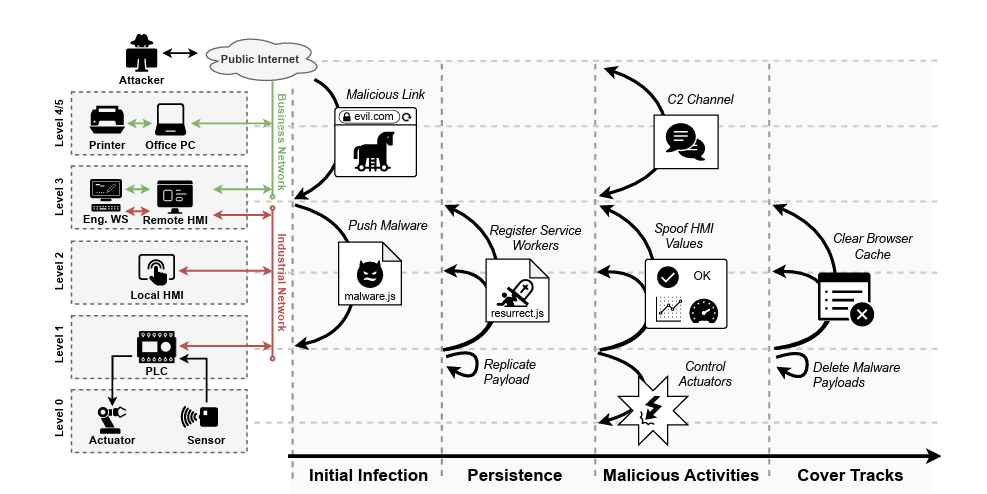 4.4KTutorials
4.4KTutorialsWeb-Based PLC Malware: A New Technique to Hack Industrial Control Systems
In a significant development that could reshape the cybersecurity landscape of industrial control systems (ICS), a team of researchers from the Georgia...
-
 4.2KMalware
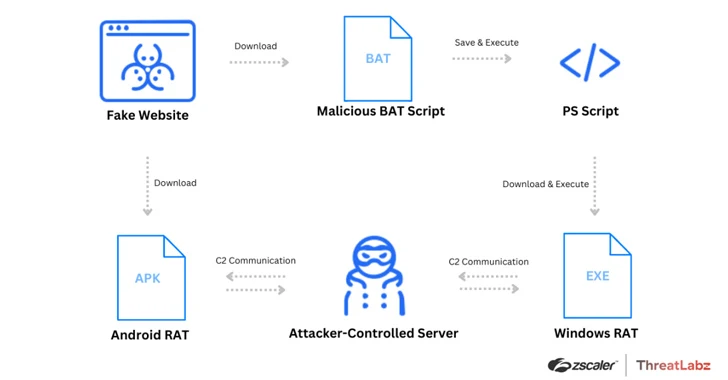
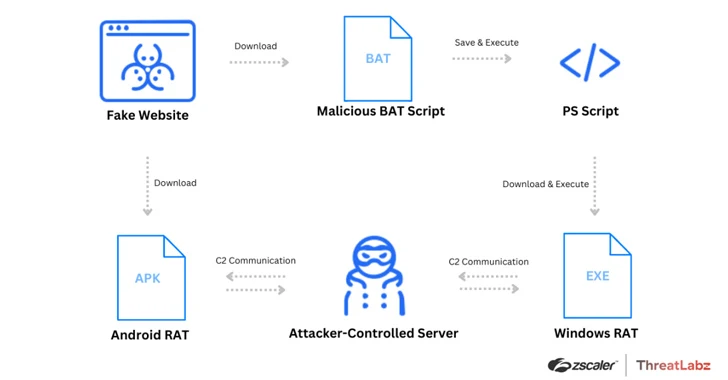
4.2KMalwareWatch Out for Spoofed Zoom, Skype, Google Meet Sites Delivering Malware
Threat actors have been leveraging fake websites advertising popular video conferencing software such as Google Meet, Skype, and Zoom to deliver a...
-

 3.4KMalware
3.4KMalwareHackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK. According...
-

 5.0KMalware
5.0KMalwareNew BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive...
-
 169Malware
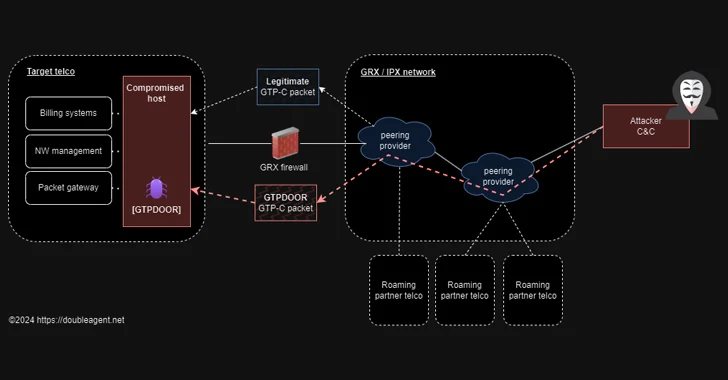
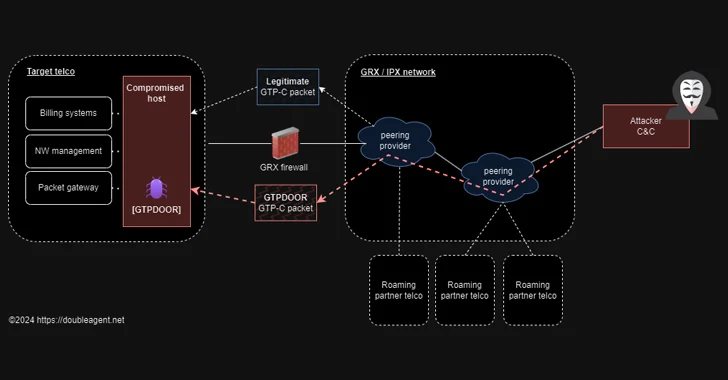
169MalwareGTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to...






