Featured News
-

 4.9KVulnerabilities
4.9KVulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
Threat actors are actively scanning and exploiting a pair of security flaws that are said to affect as many as 92,000 internet-exposed...
-
 3.1KMalware
3.1KMalwareWatch Out for ‘Latrodectus’ – This Malware Could Be In Your Inbox
Threat hunters have discovered a new malware called Latrodectus that has been distributed as part of email phishing campaigns since at least...
-

 287Data Breach
287Data BreachThe Drop in Ransomware Attacks in 2024 and What it Means
The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 5,070. But 2024...
-

 3.8KMalware
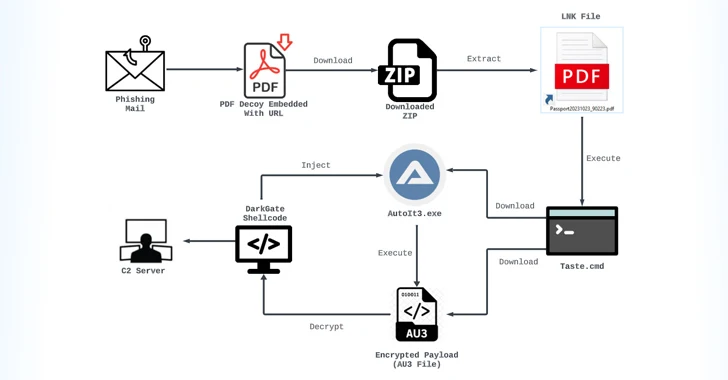
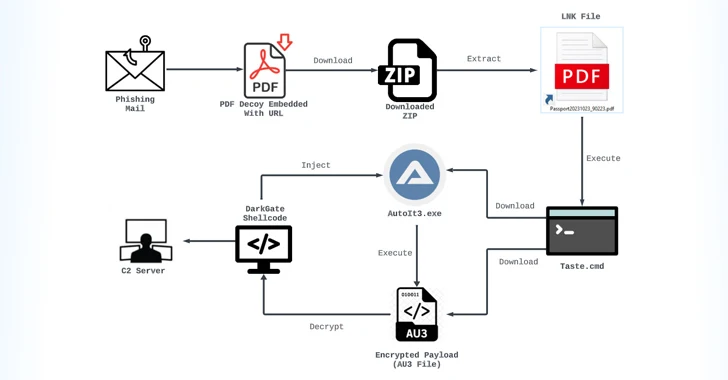
3.8KMalwareCybercriminals Targeting Latin America with Sophisticated Phishing Scheme
A new phishing campaign has set its eyes on the Latin American region to deliver malicious payloads to Windows systems. “The phishing...
-

 1.2KMalware
1.2KMalwareGoogle Sues App Developers Over Fake Crypto Investment App Scam
Google has filed a lawsuit in the U.S. against two app developers for allegedly engaging in an “international online consumer investment fraud...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesHackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites. The attack leverages...
-
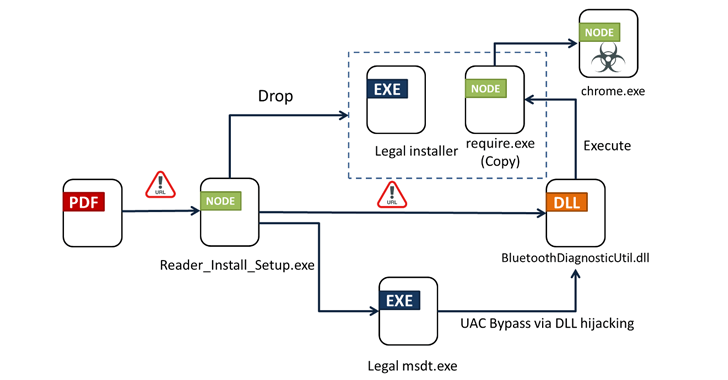
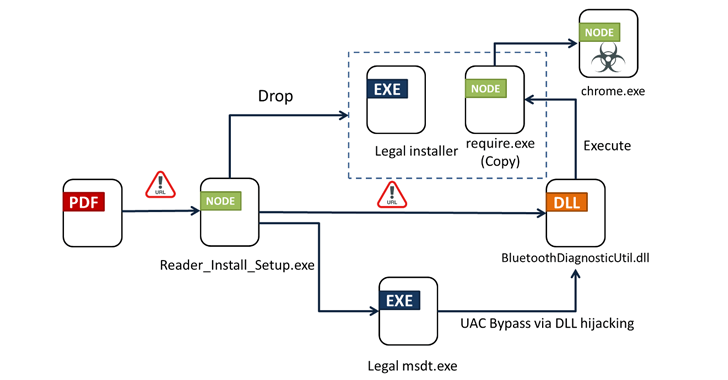 3.1KMalware
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
-

 1.8KMalware
1.8KMalwareVietnam-Based Hackers Steal Financial Data Across Asia with Malware
A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest...
-

 137Malware
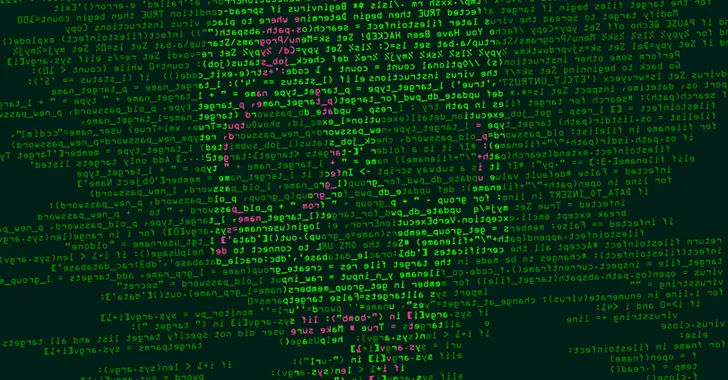
137MalwareNew Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. “The...
-

 780Vulnerabilities
780VulnerabilitiesConsiderations for Operational Technology Cybersecurity
Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events....
-

 1.4KVulnerabilities
1.4KVulnerabilitiesNew HTTP/2 Vulnerability Exposes Web Servers to DoS Attacks
New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesU.S. Cyber Safety Board Slams Microsoft Over Breach by China-Based Hackers
The U.S. Cyber Safety Review Board (CSRB) has criticized Microsoft for a series of security lapses that led to the breach of...
-

 3.1KMalware
3.1KMalwareGoogle Chrome Beta Tests New DBSC Protection Against Cookie-Stealing Attacks
Google on Tuesday said it’s piloting a new feature in Chrome called Device Bound Session Credentials (DBSC) to help protect users against...
-
 3.8KMalware
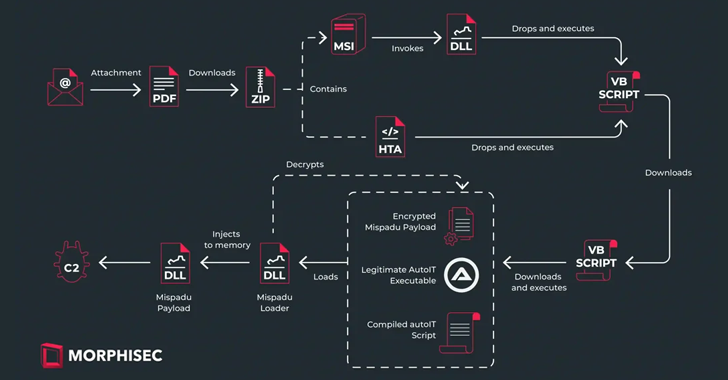
3.8KMalwareMispadu Trojan Targets Europe, Thousands of Credentials Compromised
The banking trojan known as Mispadu has expanded its focus beyond Latin America (LATAM) and Spanish-speaking individuals to target users in Italy,...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesCritical Security Flaw Found in Popular LayerSlider WordPress Plugin
A critical security flaw impacting the LayerSlider plugin for WordPress could be abused to extract sensitive information from databases, such as password...
-

 597Data Security
597Data SecurityHow to Check if a Linux Distribution is Compromised by the XZ Utils Backdoor in 6 Steps
In an unsettling development that emerged late last week, the open-source community was thrust into a state of high alert following the...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesMalicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
The malicious code inserted into the open-source library XZ Utils, a widely used package present in major Linux distributions, is also capable...
-
 4.2KMalware
4.2KMalwareChina-linked Hackers Deploy New ‘UNAPIMON’ Malware for Stealthy Operations
A threat activity cluster tracked as Earth Freybug has been observed using a new malware called UNAPIMON to fly under the radar....
-
 894Malware
894MalwareMassive Phishing Campaign Strikes Latin America: Venom RAT Targeting Multiple Sectors
The threat actor known as TA558 has been attributed to a new massive phishing campaign that targets a wide range of sectors...
-

 4.9KMalware
4.9KMalwareDetecting Windows-based Malware Through Better Visibility
Despite a plethora of available security solutions, more and more organizations fall victim to Ransomware and other threats. These continued threats aren’t...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




